Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB
AI Adoption Is Moving Faster Than Security Controls, Increasing Risk
Hospitality operators are racing to embed AI agents while security controls lag, leading to massive data breaches. In March 2026, attackers stole 527 credentials from Spanish and Austrian platforms, exposing personal data of more than 5 million guests. The article highlights how AI agents often operate with plain‑text passwords and insufficient authentication, amplifying the scale of attacks. It warns that without robust audit trails and vendor transparency, hotels face multi‑million‑dollar losses and eroded guest trust.

10 Data Breaches to Know About (April 2026)
In April 2026, Security magazine cataloged ten high‑profile data breaches spanning AI startups, government agencies, and consumer brands. Notable incidents include Mercur’s 4 TB loss via a LiteLLM supply‑chain flaw, a breach of an FBI surveillance system allegedly tied to Chinese hackers,...

Wits Restores Learning Platform After Cyber Attack
The University of Witwatersrand (Wits) has restored its Ulwazi learning management system after it was taken offline by a cyber‑extortion attack linked to the ShinyHunters group. The breach originated from a vulnerability in Instructure’s Canvas platform, which affected roughly 8,800...

Fiber Optic Cables Can Eavesdrop on Nearby Conversations
Scientists demonstrated that distributed acoustic sensing (DAS) on fiber‑optic cables can capture nearby speech and convert it into real‑time transcripts using free AI software. The method works best on surface‑coiled fibers within five metres of the sound source, while burial...

The Cyber Express Weekly Roundup: EU AI Act Updates, Malware Expansion, Critical Vulnerabilities, and Rising Cybercrime Trends
The European Union has revised its AI Act, streamlining compliance rules while imposing stricter bans on harmful AI‑generated content. Microsoft‑confirmed ClickFix malware has expanded its campaign to target macOS users with fake troubleshooting pages. A critical PAN‑OS vulnerability (CVE‑2026‑0300) with...

R1.6 Billion Missing After Hackers Ran Free Inside Major South African Metro’s Systems
The City of Ekurhuleni disclosed a massive cyberattack that left R1.19 billion missing, with only R891 million recovered through back‑billing. Hackers exploited an unsecured municipal Wi‑Fi and VPN to infiltrate billing systems, manipulate invoices and erase debts. An internal investigation revealed insider...

DOJ Spotlights Cyber Insider Threats and Terrorism With Two High-Stakes Prosecutions
The Department of Justice this week announced two high‑profile prosecutions: a Virginia jury conviction of Sohaib Akhter for deliberately deleting U.S. government databases, and a guilty plea by Muhammad Shahzeb Khan for an ISIS‑inspired plot against a Brooklyn Jewish center....

Druva Expands Cyber Resilience to Microsoft Power Platform
Druva announced native support for Microsoft Power Platform, beginning with Power BI, to extend its cyber‑resilience portfolio to AI‑driven analytics workloads. The solution backs up workspaces, reports, dashboards and underlying metadata with immutable, air‑gapped copies that can be restored at a...

How Dangerous Is Anthropic’s Mythos AI? | Bruce Schneier
Anthropic announced Claude Mythos Preview, a generative‑AI model so adept at spotting software flaws that it will be limited to a handful of enterprise partners. The UK AI Security Institute and independent tests show OpenAI’s GPT‑5.5 and smaller, cheaper models...

Modular RAT Campaign Steals Credentials and Captures Screenshots
Seqrite Labs uncovered Operation GriefLure, a spear‑phishing campaign aimed at senior executives of Vietnam’s Viettel Group and the Philippines’ St. Luke’s Medical Center. The attackers delivered a malicious LNK file that leverages the native ftp.exe utility to assemble a modular remote‑access trojan...

Google Ads To Require Passkey For Certain Sensitive Actions After July 15
Google announced that, beginning July 15, 2026, Google Ads will require advertisers to use passkeys for certain sensitive actions. The policy shift follows a recent spike in account hijacks targeting the platform. Passkeys are password‑free credentials that rely on device‑based cryptography, making...

Fake Moustache Trick Raises Questions Over UK Online Safety Act Age Checks
The UK’s Online Safety Act, launched in July 2025, introduced stricter age‑verification and content‑moderation rules to protect children online. Early testing shows simple tricks—such as a 12‑year‑old drawing a fake moustache—can fool AI‑driven facial age checks, exposing a critical vulnerability....

Fake OpenClaw Installer Targets Crypto Wallets and Password Managers
A fake OpenClaw installer is being used to deliver a Rust‑based infostealer called Hologram, which targets over 250 crypto‑wallet and password‑manager browser extensions. The 130 MB dropper evades detection with layered anti‑VM checks, a mouse‑gate, and a PowerShell payload that disables...

68% of Passwords Can Be Cracked Within a Day
Kaspersky’s analysis of 231 million leaked passwords reveals that 68 % can be cracked within a day using AI‑driven brute‑force tools. Predictable structures dominate: 53 % end with digits, 10 % use the “@” symbol, and even 15‑character passwords are broken in under a...

Zara Data Breach Exposed Personal Information of 197,000 People
Spanish fast‑fashion retailer Zara, part of Inditex, suffered a data breach affecting over 197,000 customers. Hackers accessed databases hosted by a former technology provider, extracting email addresses, geographic data, purchase histories, and support tickets, but not names, phone numbers, or...

Canvas Cyberattack Disrupts 9,000 Schools, Exposes 275 Million Records
Instructure confirmed that a ransomware attack by the ShinyHunters group forced a shutdown of its Canvas learning platform, affecting roughly 9,000 schools worldwide. The hackers claim to have stolen data on 275 million users, prompting emergency responses from universities and K‑12...
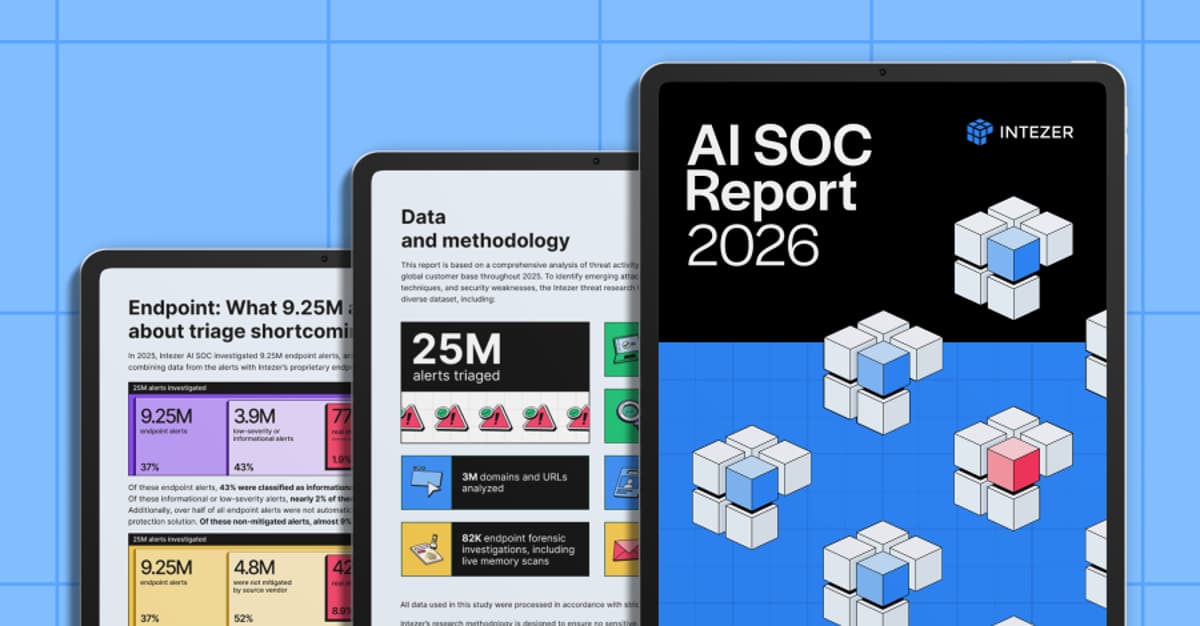
One Missed Threat Per Week: What 25M Alerts Reveal About Low-Severity Risk
The new Intezer AI SOC report analyzed more than 25 million security alerts across 10 million endpoints and identities. It found that roughly 1 % of alerts classified as low‑severity or informational correspond to real breaches—about one missed incident per week for a...

Pentest-Tools.com Releases Free Scanner for CVE-2026-41940 as cPanel Authentication Bypass Enters Its Third Week of Active Exploitation
Pentest‑Tools.com has launched a free, no‑login scanner that actively probes cPanel and WHM servers for the critical CVE‑2026‑41940 authentication bypass. The flaw, rated CVSS 9.8, lets attackers inject a crafted CRLF payload to hijack the whostmgrsession cookie and gain full...

AI LLMs Threaten and Bolster Enterprise Cybersecurity, Frontier AI Report Warns
Frontier AI’s new report flags Anthropic’s Claude Mythos as capable of uncovering tens of thousands of high‑severity software flaws in hours, a capability already being leveraged by firms like Mozilla to patch Firefox. The rapid scale of AI‑driven bug hunting...

ShinyHunters Breach Hits Canvas, Shutting Down UCSD, SDSU and Hundreds of Campuses
The hacking group ShinyHunters forced Instructure's Canvas learning platform into maintenance mode, locking out students at UC San Diego, San Diego State and dozens of other institutions. The attackers say they have exfiltrated up to 280 million records from roughly 9,000...

Google Is Turning Android Studio Into a Policy Watchdog
Google is embedding Play Policy Insights into Android Studio, giving developers real‑time warnings about policy violations and SDK compliance. The upgraded Play Integrity API and post‑quantum support boost fraud detection and cryptographic security. New privacy widgets, developer verification, and AI‑driven...

Microsoft Launches Azure Kubernetes Fleet Manager to Automate Governance of Thousands of Clusters
Microsoft announced Azure Kubernetes Fleet Manager, a new service that automates governance across thousands of Kubernetes clusters spanning cloud, on‑premises and edge. The platform extends GitOps with fleet‑scale controls, aiming to simplify compliance, security and rollout for SaaS operators.
Circle CEO Jeremy Allaire Tightens USDC Auditability to Counter Crypto Fraud
Circle chief executive Jeremy Allaire announced a suite of new auditability measures for USDC, including monthly attestations, regulated reserve composition and real‑time reporting. The move targets crypto’s fraud problem and aligns the stablecoin with growing institutional demands for transparency.

Your CTEM Program Is Probably Ignoring MCP. Here’s How to Fix It
The piece highlights Model Context Protocol (MCP) as a hidden vulnerability in modern AI toolchains, warning that many security programs overlook it. It details real‑world breaches—such as a malicious npm MCP package that infected 300 firms and high‑severity CVEs that...
I Analyzed the 5 Best Incident Response Tools in 2026
The article reviews the five top incident‑response platforms for 2026—KnowBe4 PhishER, Datadog, Tines, Torq, and Dynatrace—based on G2 ratings, user feedback, and feature depth. Each tool is matched to a specific use case, from phishing triage to AI‑driven root‑cause analysis, and...

ZiChatBot Malware Abuses Zulip APIs for Stealthy C2 Operations
Security researchers have uncovered ZiChatBot, a cross‑platform malware family that hijacks legitimate Python Package Index (PyPI) wheel packages to deliver malicious code to Windows and Linux developers. The payloads are dropped via DLL or SO files, achieve persistence through Run‑registry...

A New Frontier: Identity Stack Evolves for Agentic Systems
Current IAM solutions are built for human users and static applications, relying on RBAC and MFA. Agentic AI systems introduce autonomous, non‑human identities that act at machine speed, creating ambiguous credentials and expanded attack surfaces. To secure these agents, a...

VoidStealer Trojan Steals Chrome Master Key via Debugger
The new VoidStealer Trojan has learned to bypass Chrome's stored data protection: the infostealer attaches to the browser process as a debugger, and intercepts the master key from RAM. Cookies, sessions, and passwords in Chrome and other browsers – Microsoft...

Disruptions to Digital Services and a Surge in Phishing Emails
In April, Estonia’s Information System Authority logged 1,138 cyber incidents that disrupted a range of public digital services, from health‑insurance prescriptions to digital signature platforms. A software error halted the Health Insurance Fund’s e‑prescription system for about 30 minutes, while...

Global Data Leaks up 22% in Early 2026, 259.4k Irish Accounts Exposed
Surfshark’s Q1 2026 data‑breach report shows global leaks jumped 22% year‑over‑year, with 210.3 million accounts compromised. The United States accounts for 29% of those breaches, while Ireland contributed 260 thousand exposed accounts, ranking 39th worldwide and fourth in Northern Europe since 2004....

Windows 11 Can Block Google Chrome's 4GB AI Model From Reinstalling Itself on Your PC — A Simple Registry Tweak...
Google Chrome and Microsoft Edge now download a 4 GB on‑device Gemini Nano AI model by default, prompting privacy and storage concerns. Windows 11 Pro introduces a Registry policy, GenAILocalFoundationalModelSettings, that lets administrators block or remove the model for both browsers. The setting...

ASIC Urges Financial Firms to Boost Cyber Defences
The Australian Securities and Investments Commission (ASIC) has issued an open letter urging all licensed financial firms to urgently strengthen cyber resilience in light of frontier artificial intelligence threats. ASIC stresses that AI‑driven attacks can expose vulnerabilities faster and at...
BT Cyber Threat Protection Offers Norton to Protect up to 15 Devices
BT has launched a Cyber Threat Protection service for its broadband customers, powered by Norton. The complimentary package covers up to 15 devices across Windows, macOS, iOS, and Android, and includes antivirus, scam assistant, dark web monitoring, safe web, social...

Pen Tests Show AI Security Flaws Far More Severe than Legacy Software Bugs
Penetration testing of AI and large language model (LLM) applications reveals a disproportionate share of high‑risk flaws. Cobalt’s 2026 State of Pentesting Report finds 32% of AI/LLM findings are high risk—about 2.5 times the 13% rate in traditional enterprise software—yet...

Your Refresh Plan Has a CVE Blind Spot
A healthcare client bought servers in 2017 and, due to COVID‑driven supply‑chain delays, extended the vendor’s end‑of‑life timeline to 2026 for software updates and 2028 for security patches. With new hardware now unavailable for up to a year and costs...

PCPJack Campaign Boots TeamPCP Off Compromised Machines
Security researchers have uncovered PCPJack, a new credential‑theft framework that first wipes traces of the notorious TeamPCP group before worming through exposed cloud environments. The worm targets Docker, Kubernetes, Redis, MongoDB, RayML and vulnerable web applications, stealing credentials for later...

Your Databases Are Being Watched – Just Not by You
The article warns that most enterprises leave databases unmonitored, allowing attackers to linger for an average 241 days before detection. This governance deficit fuels costly breaches and exposes firms to South African POPIA penalties of up to R10 million (≈$540 k) and average...

Snyk Integrates Claude to Advance AI-Native Application Security
Snyk has integrated Anthropic’s Claude large‑language model into its AI Security Platform, enabling automated discovery, prioritization, and developer‑ready remediation of vulnerabilities across code, dependencies, containers, and AI‑generated artifacts. The platform, called Evo, extends protection to AI models, agents, datasets, and...

City of London Calls for Tech-Led Fraud Fight
The City of London Corporation is urging technology firms to create stronger digital identity‑verification services to curb financial‑sector fraud. It proposes a voluntary, secure network that lets users verify once with a trusted provider and reuse that proof across multiple...

Securonix Launches AI Threat Research Agent and ThreatWatch Validation Tool
Securonix unveiled two new capabilities – the AI‑driven Threat Research Agent and the ThreatWatch validation tool – built on its ThreatQ platform. The Research Agent transforms raw threat intelligence into structured, role‑specific findings with source attribution, while ThreatWatch automatically generates...

OpenAI Tunes GPT-5.5-Cyber for More Permissive Security Workflows
OpenAI has begun a limited preview of GPT‑5.5‑Cyber, a more permissive variant of its latest GPT‑5.5 model, available only to verified cybersecurity professionals through the Trusted Access for Cyber program. The new tier relaxes restrictions on security‑related prompts, enabling authorized...

Does Shein Send Data to China? Irish Watchdog Investigates
The Irish Data Protection Commission has opened an investigation into Shein Ireland, the European hub of the fast‑fashion e‑commerce giant. Regulators suspect the retailer may have illegally transferred personal data of EU users to China, breaching GDPR rules. The probe...
AI-Driven Threats Make Cyber Resilience Essential for Survival
Cybersecurity is entering a different era. Frontier AI models can now discover and exploit vulnerabilities continuously and at scale, shrinking attack timelines and expanding risks far beyond traditional defenses. The priority is changing fast. Cyber resilience is no longer optional infrastructure, it...

Ransomware Group Takes Credit for Trellix Hack
RansomHouse, a ransomware‑as‑a‑service group, has claimed responsibility for the recent breach of Trellix’s source‑code repository. Trellix confirmed the intrusion but said its code release process appears untouched and no exploitation has been detected. The attackers posted screenshots of internal dashboards,...

How Slack Keeps a Team of AI Agents From Losing the Plot
Slack’s security investigation service orchestrates a team of large‑language‑model agents—Director, multiple Experts, and a Critic—to analyze alerts without sharing a single monolithic context. The Director records every decision, observation, and hypothesis in a structured journal that feeds into the other...

Transilience AI Unveils Security Operating System for Cloud Remediation
Transilience AI announced the general availability of its Full Stack Security Operating System for cloud environments, aiming to close the gap between detection and remediation. The platform replaces fragmented CSPM, CNAPP, and CWPP tools with LLM‑powered agents that continuously collect,...

Enrique Salem on Founder Leadership, Trust, and Scaling Technology Companies
In this episode, Enrique Salem—partner at Bain Capital Ventures and former Symantec CEO—shares how his journey from software developer to corporate leader shapes his investment lens, emphasizing a customer‑first perspective and founder empathy. He discusses the challenges of building globally‑ready...

Vulnerability in Claude Extension for Chrome Exposes AI Agent to Takeover
Security firm LayerX has identified a critical flaw, dubbed ClaudeBleed, in Anthropic’s Claude extension for Chrome that lets any zero‑permission extension issue privileged commands to the AI agent. By exploiting lax origin verification, attackers can inject prompts, bypass user confirmations,...

70 Out of 100 South Africans Hit by Data Breaches
Surfshark’s Q1 2026 data‑breach monitor shows 70 percent of South Africans have been affected by breaches since 2004, with 45.7 million compromised accounts placing the country 38th globally and second in Africa. The most exposed data points are passwords (22.9 million) and usernames (12 million),...
Real‑Time Threat Detection Keeps Businesses Ahead
OpenClaw Security offers innovative protection solutions that focus on real-time threat detection and response, ensuring businesses can stay ahead of cyber threats. Learn more here: https://t.co/xD7sxwrMiz @handvantage