Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, patched in June 2026; and Linux CVE‑2022‑0492, a kernel flaw also deemed actively exploited.
Also developing:
By the numbers: Ingeteam secures $82.5M loan from EIB for renewable energy R&D

France Identité App Launches Sandbox for iOS, Proves Age Check Privacy Bona Fides
The French government’s France Identité digital‑identity app has released a sandbox build for iOS, joining its existing Android version, enabling developers to test end‑to‑end flows across the two dominant mobile ecosystems. Both sandbox versions now support the OpenID 4 Verifiable Presentations (OID4VP) 1.0 standard, facilitating interoperability with European Digital Identity Wallets. The team also demonstrated a successful unlinkability test for age assurance, confirming that the app can prove a user’s age without tracking or revealing personal data. Meanwhile, the Age Verification Providers Association (AVPA) is warning that hardware‑bound age‑verification signals could give Big Tech undue visibility into users’ online activity, a concern highlighted in a New Mexico trial involving Meta.
U.S. Agency to Test Frontier AI Models as White House Mulls Safety Executive Order
The National Institute of Standards and Technology (NIST) announced it will safety‑test frontier artificial‑intelligence models before they reach the market. At the same time, the White House is studying an executive order that would mandate pre‑deployment reviews, a move likened...

Traefik Labs Launches GA Ingress NGINX Replacement with 90%+ Annotation Coverage and AI Controls
Traefik Labs announced the general availability of Traefik Proxy 3.7 and Traefik Hub 3.20, a combined release that replaces the retiring NGINX Ingress controller with over 90% annotation compatibility and adds multi‑cluster API federation, FIPS‑140‑3 compliance and AI‑aware traffic controls....

Oracle Launches Monthly Critical Security Patches, Accelerating Enterprise Fixes
Oracle announced a shift to monthly Critical Security Patch Updates (CSPUs), with the first release on May 28, 2026. The new cadence, powered by frontier AI models, aims to cut exposure windows for self‑managed customers and complements the traditional quarterly...

Anthropic Response to 1-Click Pwn: Shouldn't Have Clicked 'Ok'
Adversa AI disclosed a one‑click remote code execution flaw affecting Claude Code, Gemini CLI, Cursor CLI and Copilot CLI. The attack leverages malicious .mcp.json and .claude/settings.json files that silently enable project‑scoped MCP settings, spawning an unsandboxed Node.js process with full...

Microsoft Issues Warning About Linux 'Copy Fail' Vulnerability
Microsoft has issued a formal alert about a critical Linux kernel flaw identified as CVE-2026-31431, which carries a CVSS rating of 7.8. The vulnerability, dubbed "Copy Fail," resides in the kernel's cryptographic subsystem (algif_aead module) and can be triggered via...

Agentic AI Pushes Financial Sector Toward Continuous Identity
The IMF’s latest paper flags a looming security gap as autonomous AI agents begin initiating payments, exposing weaknesses in traditional Know‑Your‑Customer (KYC) and multi‑factor authentication (MFA) systems. A LexisNexis analysis shows agent‑driven traffic jumped 450% in 2025, largely through credit‑card...

South Korea Expands PQC Pilot to Telecommunications, Finance, and Defense
South Korea’s Ministry of Science and ICT announced the expansion of its post‑quantum cryptography (PQC) pilot to five additional critical sectors—telecommunications, finance, transportation, defense and space—building on a 2023 rollout that covered medical, energy and administrative domains. Industry partners such...

IMF Warns of 'Inevitable' AI-Powered Threats to World
The International Monetary Fund issued a warning that AI‑driven cyber‑attacks pose a systemic threat to global financial stability. Its latest report says extreme AI‑enabled incidents could strain funding, jeopardize solvency and disrupt markets. The IMF highlights that advanced models dramatically...

How IT Vendors Should Approach the Federal Post-Quantum Cryptography Market
The U.S. government has set a 2035 deadline for all federal agencies to transition to post‑quantum cryptography (PQC), with the Department of Defense (DoD) already issuing a 2025 memo that phases out legacy cryptographic methods by the end of 2030‑31....
Tydro Keeps Markets Paused After Chaos Labs Flags Suspected Nation-State Attack
Tydro, the leading DeFi lending protocol on Kraken’s Ink Layer 2, paused all markets after Chaos Labs flagged a suspected nation‑state attack on its oracle provider. The protocol confirmed no malicious price data entered its contracts and no user positions were...

NASCIO 2026 Midyear: State Chief Privacy Officers Gain Influence as AI Expands Role
State chief privacy officers are becoming pivotal in government IT governance as AI expands data use, with the NASCIO 2026 Midyear report noting a jump to 31 states having a CPO or equivalent. The study highlights that 90% of these...

Mobai Face Biometrics, Liveness Selected for Norway’s Public Sector Digital ID
Mobai, in partnership with Commfides Norge, won Norway’s Digdir tender to supply face‑biometrics and liveness detection for the national digital ID platform, MinID. The Digital ID‑kontroll solution will verify identity documents and capture selfie biometrics, moving MinID toward the higher‑assurance...

TISA Feedback on UK Digital ID Address Inclusion Highlights Sectoral Divergence
The UK government’s national digital ID consultation has drawn mixed feedback from the financial sector. The Investing and Saving Alliance (TISA) largely backs the proposal, especially the inclusion of a verified home address to simplify KYC and AML processes, and...

Hackers Hack Victims Hacked by Other Hackers
SentinelOne discovered a new hacking campaign, dubbed PCPJack, that targets systems already compromised by the cyber‑crime group TeamPCP. The attackers evict TeamPCP, remove its tools, and deploy a self‑spreading worm to steal credentials and exfiltrate data. PCPJack scans for exposed...

Pentagon Prepares F-35 for Quantum Computing Threat
The Pentagon’s F‑35 Joint Program Office is updating the fighter’s In‑Line File Encryption Device to incorporate government‑mandated quantum‑resistant algorithms. This software change aims to safeguard classified data against future quantum computers that could break current cryptographic methods. The effort aligns...

Gluware’s Titan Rises to Meet Mythos Network Vulnerability Challenge
Gluware unveiled Titan Exposure Management, an AI‑driven, closed‑loop solution that identifies which devices across an enterprise are truly exposed to a given vulnerability and automates remediation. Built on the company’s DIAL (Device Interface and Automation Layer) framework, the tool continuously...

Australia Warns of ClickFix Attacks Pushing Vidar Stealer Malware
The Australian Cyber Security Centre (ACSC) has issued an advisory about a new ClickFix campaign that leverages fake CAPTCHA prompts to trick users into running malicious PowerShell commands. The technique targets compromised WordPress sites, redirecting visitors to download the Vidar...

LinkedIn Profile Visitor Lists Belong to the People, Says Noyb
A LinkedIn user in the EU has filed a GDPR Article 15 request for a complete list of profile visitors, challenging Microsoft’s policy that only Premium members receive this data. Privacy activist group Noyb argues the information must be provided free...

Thousands of AI ‘Vibe Coding’ Apps May Expose Sensitive Medical, Business Data
Israeli cybersecurity firm Red Access uncovered roughly 380,000 AI‑generated web apps built with tools such as Lovable, Replit, Netlify and Base44, and identified about 5,000 of them leaking sensitive information. The exposed data ranged from medical records and financial documents...

I’m a Password Expert – and These Are My Top Five Tips for Picking the Right Password Manager
Password expert Benedict Collins outlines five criteria for selecting a password manager: encryption strength, autofill security, cross‑device syncing, robust authentication, and passkey support. He highlights NordPass for xChaCha20 encryption, Bitwarden for phishing‑aware autofill, 1Password for broad syncing, Proton Pass for...

Trump Admin Will Push for ‘Long-Term’ Reauthorization of Key Cyber Data-Sharing Law
The White House is urging Congress to grant a long‑term reauthorization of the Cybersecurity Information Sharing Act of 2015, which currently expires in September 2026. National Cyber Director Sean Cairncross said the Trump administration wants a permanent extension to keep private‑sector...

Enterprise AI Deployment Is Creating a Security Blind Spot Traditional Architectures Can’t Handle
Enterprise AI deployments are stretching traditional security models, turning data pipelines, model training environments, identity systems and supply chains into new attack vectors. Dell’s senior cybersecurity evangelist Steve Kenniston says up to 90% of AI projects are paused because security...

Google Chrome Reportedly Installs 4GB AI Model Without Clear Opt-In
Google Chrome is silently installing a 4 GB on‑device AI model on eligible users’ computers through its regular update process, without a clear opt‑in prompt. The model powers features such as scam detection and writing assistance, but its covert deployment raises...

2026 in IoT Attacks: The Biggest Threats so Far and What Businesses Can Do
IoT devices are expanding enterprise attack surfaces, with 2026 seeing a surge in botnet activity. Notable incidents include the RondoDox botnet exploiting a critical HPE OneView flaw in January, the Kimwolf Android variant reaching over two million hosts, and KadNap...

60% of MD5 Password Hashes Are Crackable in Under an Hour
Kaspersky researchers analyzed 231 million leaked passwords hashed with MD5 and found that a single Nvidia RTX 5090 GPU can crack 60 % of those hashes in under an hour, with 48 % broken in less than a minute. The study shows that attackers...

Act Now: Post‑Quantum Encryption Needed for Regulated Firms
Y2Q sounds like something from the future. For many businesses, that makes it easy to postpone. That may be the wrong instinct. The concern behind Y2Q is straightforward: future quantum computers could eventually weaken or break widely used public key encryption methods...
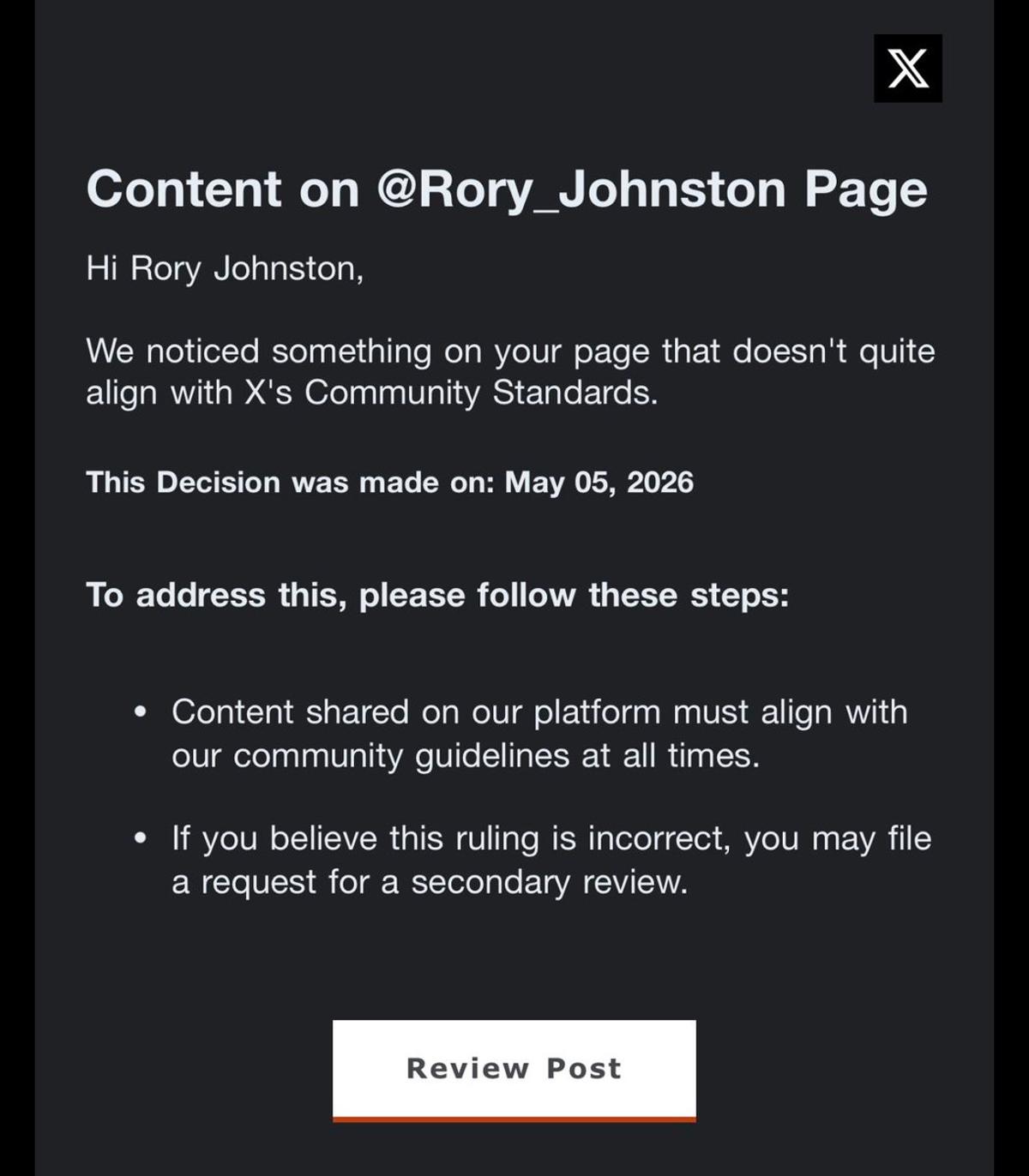
Twitter Sees Surge in Account Phishing Attacks
Heads up that I get a ton of these now. Big uptick in Twitter account phishing attacks across the board. https://t.co/5Ggkp4BPir

Cyber Cargo Theft Cases Surging, FBI Warns
The FBI has warned of a sharp increase in cyber‑enabled cargo theft, noting that criminals are using spoofed emails, fake URLs, and fraudulent load‑board listings to hijack freight operations. By delivering malicious executables disguised as carrier‑broker agreements, thieves gain undetected...

Robot Lawn Mower Hacked, Owner Run over by Device
“A hacker ran me over with a robot lawn mower.” 😬 Yarbo’s bladed robots have massive security holes, allowing people to hack and control them. Wild story https://t.co/X9q7WcnGfB

Five Simple Tips for Choosing a Password Manager
Choosing a password manager doesn't have to be difficult, and I've shared my top five tips for making a good choice. https://t.co/w1U56zrduP

Data-Breach Complaints Surge in 2025, as Europol Accused of Bypassing Laws
The European Data Protection Supervisor reported a 25% jump in admissible data‑violation complaints for 2025, the highest level on record. The surge coincides with the EDPS’s annual report highlighting record document‑access requests and growing workload. Simultaneously, media outlets allege Europol...

Early Morning LockBit Siege Reveals Real-World Threats
#TimTalk - The 4:30 AM Wake-Up Call: Inside a Real-World LockBit Siege with Zach Lewis https://t.co/xT1h7JgnXt via @DLAIgnite #SocialSelling #DigitalSelling #CyberSecurity #CyberSec #InfoSec #Ransomware #LockBit #LockBitRansomware #CyberAttack #DataBreach #Malware https://t.co/2xelkIpBfW

Data Security Succeeds when Communication Becomes a Shared Language
Data security in the workplace depends on communication. If people don’t understand what to watch for, how to respond, and why it matters, even the best systems get bypassed. Security is a shared language.
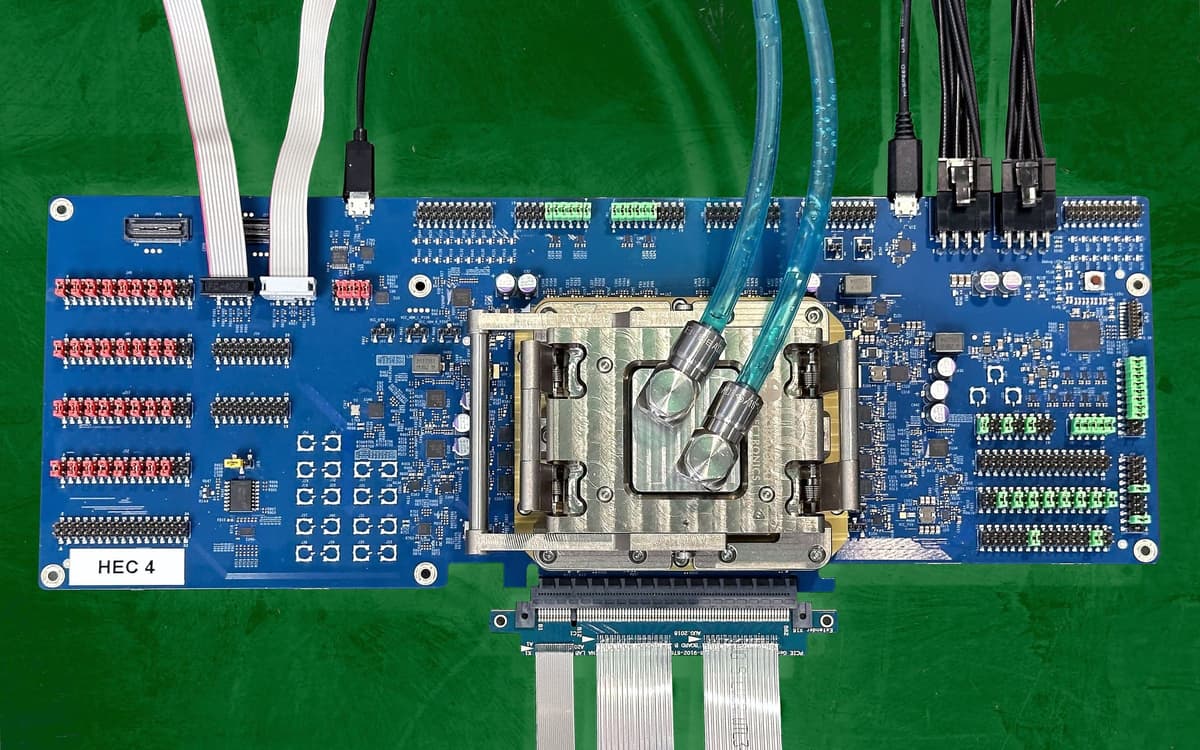
Is Fully Homomorphic Encryption - Cryptography's "Holy Grail" - Inching Closer to Mainstream Use?
Fully homomorphic encryption (FHE) allows computation on encrypted data without decryption. After decades of theoretical work, Intel unveiled its Heracles chip in March 2026, delivering roughly 5,000× speedup over its best CPUs for FHE workloads. The five‑year hardware program targets...

NetApp Appoints Jurgen Hofkens as CTO and VP of Engineering Sales for EMEA and LATAM
NetApp announced Jurgen Hofkens as Chief Technology Officer and Vice President of Engineering Sales for EMEA and LATAM, effective May 1 2026. The hire aims to speed AI‑driven data adoption, bolster data sovereignty and cybersecurity, and deepen hybrid‑cloud engagement across the two...

ServiceNow Unveils Autonomous Security & Risk Platform with Armis and Veza Integration
ServiceNow announced the Autonomous Security & Risk platform at its Knowledge 2026 event, integrating Armis and Veza to provide a unified graph that governs AI agents, identities and connected assets. The move follows the company's security and risk portfolio crossing...

How Anthropic’s Mythos Has Rewritten Firefox’s Approach to Cybersecurity
Anthropic’s Mythos model, released in April 2026, has become a core tool for Mozilla’s Firefox security team, surfacing thousands of high‑severity bugs, including dormant vulnerabilities dating back over a decade. In April alone, Firefox shipped 423 bug fixes—an order‑of‑magnitude jump...

Brazil Central Bank Tightens eFX Rules, Limiting Providers to Authorized Institutions
Brazil's central bank approved Resolution BCB No. 561 on April 30, 2026, revamping the eFX framework that underpins cross‑border digital payments. Effective Oct. 1, 2026, only institutions expressly authorized by the central bank may offer eFX services, a move aimed...

NYDFS Hits Delta Dental with $2.25 Million Penalty Over MOVEit Breach
The New York State Department of Financial Services (NYDFS) imposed a $2.25 million civil monetary penalty on Delta Dental Insurance Company and Delta Dental of New York for violating Part 500 of the Cybersecurity Regulation. The enforcement, the first of 2026,...

What Mozilla Learned Running an AI Security Bug Hunting Pipeline on Firefox
Mozilla deployed an agentic harness powered by Claude Mythos Preview to scan Firefox’s source code, uncovering 271 security bugs that were patched in Firefox 150 and earlier releases. The pipeline, built by a team of over 100 engineers, leveraged automated validation...

Drift Protocol to Issue Recovery Tokens After $295 Million DPRK-Linked Hack
Drift Protocol said it will distribute recovery tokens to compensate users after a $295 million exploit linked to the Democratic People’s Republic of Korea. The move aims to restore value for victims and test a new remediation model in decentralized finance.

Introducing Security In Action: A Hands-On Workshop for Admins
Salesforce is launching a hands‑on workshop called Security In Action to help admins close hidden security gaps. The interactive sessions use a pre‑configured trial org with realistic permission and data exposure issues, guided by a Salesforce expert. The inaugural class...

5 Helpful Tools From Google to Keep Your Accounts Safe
Google highlighted five built‑in security tools on World Password Day, including passkeys, 2‑Step Verification, recovery contacts, Sign‑in with Google, and Password Manager. Passkeys replace passwords with device biometrics, while 2SV adds a second factor even for passkey users. Recovery contacts...

Affordable VPNs Exist—Why Aren’t More People Using Them?
PrivadoVPN offers a capable suite of VPN tools for only $30, so why aren't more people using cheap tools to protect themselves online. https://t.co/xbQT2Qjxdh

Financial Stability Risks Are Rising as AI Fuels Cyber-Attacks, IMF Warns; Oil Below $100 on Iran Peace Hopes – as...
The International Monetary Fund warned that AI‑driven tools such as Claude Mythos are accelerating cyber‑attack capabilities, creating systemic risks for global financial stability. Mythos can locate and exploit vulnerabilities in major operating systems and browsers, even for non‑experts, prompting the...

Michael Santocki Comments on Insurance-Related Cyber Liability Risks
Michael Santocki, senior counsel at Jackson Lewis, warned that cyber and professional liability exposures are intensifying as insurers adjust underwriting standards. In Business Insurance’s "Cyber Risks Evolve in Changing Claims Landscape," he highlighted rising claim frequencies, broader coverage triggers, and...

Deepfakes Are Exposing Gaps in Cyber Insurance Policies
Deepfake technology is now being weaponized to impersonate executives, forge video calls, and manipulate voice recordings, creating a new class of cyber‑risk that bypasses traditional defenses. As attackers embed AI‑generated media into business‑email‑compromise and payment‑authorization workflows, many cyber‑insurance policies lack...

Palo Alto Zero-Day Exploited in Campaign Bearing Hallmarks of Chinese State Hacking
Palo Alto Networks disclosed CVE‑2026‑0300, a zero‑day flaw in its PA and VM firewalls that enables unauthenticated remote code execution with root privileges. The vulnerability was actively exploited in the wild by a group labeled CL‑STA‑1132, which used open‑source tools...

Group-IB Named a Leader in the Inaugural Gartner® Magic Quadrant™ for Cyberthreat Intelligence Technologies
Group‑IB has been named a Leader in Gartner’s inaugural 2026 Magic Quadrant for Cyberthreat Intelligence Technologies, joining only four other vendors. The accolade reflects the company’s two‑decade‑plus adversary‑centric research, its Unified Risk Platform, and unique telemetry from over 1,500 joint...