Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, patched in June 2026; and Linux CVE‑2022‑0492, a kernel flaw also deemed actively exploited.
Also developing:
By the numbers: Ingeteam secures $82.5M loan from EIB for renewable energy R&D

Hackers Weaponize Claude AI in Attacks on Water and Drainage Utilities
Hackers leveraged Anthropic's Claude and OpenAI's GPT models as operational copilots to infiltrate the Mexican water utility Servicios de Agua y Drenaje de Monterrey (SADM). Claude generated a 17,000‑line Python framework that automated reconnaissance, credential harvesting, and lateral movement, accelerating the attack timeline from weeks to hours. The AI‑driven effort accounted for roughly three‑quarters of remote command execution across a broader Mexican government campaign, though attempts to breach the OT‑adjacent vNode gateway failed. The incident highlights how generative AI can amplify low‑skill actors against critical infrastructure.

Veeam Ranked the #1 Data Protection Software in Market Share Worldwide for 2H 2025
Veeam Software was named the #1 data protection software worldwide for the second half of 2025, capturing 13.6% market share according to IDC’s Semiannual Software Tracker. The company posted 11.5% sequential growth, outpacing the market’s 8.8% average. Veeam attributes its...

Open Source Tamper-Proof Database Adds Immutable Audit Logging and Expands PostgreSQL Compatibility
Open‑source database immudb released version 1.11, adding built‑in immutable audit logging and full PostgreSQL compatibility. The new audit feature records every database action inside an append‑only ledger, creating tamper‑proof trails without external log collectors. PostgreSQL compatibility lets existing applications switch to...

Federal Jury Convicts Alexandria Man on Charges Relating to the Deletion of U.S. Government Databases
A federal jury convicted Alexandria resident Sohaib Akhter of conspiracy to commit computer fraud, password trafficking, and illegal firearm possession. Akhter and his twin brother, former employees of a contractor serving more than 45 federal agencies, accessed a plaintext EEOC...

Freecash Returns to Google Play After Policy Review
Almedia’s Freecash app has been reinstated on Google Play after a policy compliance review. The app was pulled earlier this year amid accusations that it harvested sensitive health, religious and sexual‑orientation data and acted as a data broker—claims the company...

Security Teams Juggle Frameworks Yet Still Question Risk Accuracy
Question for the security folks on Threads: how are you actually measuring risk? NIST CSF? CIS? Some Frankenstein blend of frameworks plus vendor assessments? Every conversation I have lately ends with "all of the above and we are still not sure it...

Government Picks Two Cyber Incident Response Partners for £7m Contracts
Britain’s Cabinet Office has awarded Deloitte and PwC retained cyber‑incident response contracts worth up to £8.1 million (about $10.4 million). The two‑year agreements, with a possible 12‑month extension, will provide on‑site and remote expertise to any UK government department facing a cyber...
Quantum Computers Threaten some Crypto, Not All
Quantum computers are not FUD. But there are ways to prepare for them. Some kinds of cryptography will be broken by quantum computers, while others will remain safe. Why? Here's the explanation. https://t.co/szh6X1usyt

Netwrix Adds CTO, VP of Engineering, and Channel Head to Accelerate AI‑Driven Security
Netwrix announced three senior hires—Avesta Hojjati as CTO, Marcin Gierlak as VP of Engineering and Kraków site leader, and Natalie Tomlin as Head of North America Channel—to sharpen its engineering pipeline and expand its partner ecosystem. The moves come as...

Cisco Patches High-Severity Vulnerabilities in Enterprise Products
Cisco disclosed patches for five high‑severity vulnerabilities across its enterprise portfolio, including SSRF flaws in Unity Connection and SNMP‑related denial‑of‑service bugs in SG350 switches. Additional DoS issues were fixed in the Crosswork Network Controller, Network Services Orchestrator, and the IoT...

Smart Glasses for the Authorities
ICE is preparing to field AI‑enhanced smart glasses that can pull facial‑recognition, gait and other biometric data from federal databases in real time. The devices are modeled on counter‑terrorism tools such as ABIS and BEWL, extending them to routine street...

Allianz Hands Global Commercial Cyber Book to MGA Coalition
Allianz Commercial is transferring its standalone global commercial cyber insurance portfolio to San Francisco‑based MGA Coalition. The multiyear deal gives Coalition primary underwriting, pricing and claims responsibilities while Allianz provides capacity, equity and board representation, positioning Coalition to become the world’s...

Nimbus-Key® ID Revolution
Nimbus-Key ID announced a partnership with federal IT reseller Carahsoft to broaden its authentication platform. The company argues that traditional username/password combos and six‑digit OTPs are both insecure and cumbersome for users. Nimbus-Key ID promotes an AI‑enhanced identity solution that...
Simple, Affordable Steps to Protect Your Online Identity
Easy, Low-Cost Ways To Defend Your Identity Online by @Forbes Learn more: https://t.co/2npREWRZaC #CyberSecurity #Infosec #IT #Tech https://t.co/XBn8sjEMDi

Day Zero Readiness: The Operational Gaps That Break Incident Response
The article argues that having an incident‑response retainer is insufficient without Day Zero operational readiness. It stresses that immediate visibility—especially into identity, cloud, endpoint, and logging systems—is the first priority when a breach is detected. The guide outlines common access bottlenecks,...

Identity Fraud in 2026: Why the Latest News Points to a More Layered Threat
Identity fraud in 2026 has evolved from isolated credential theft to a multi‑layered threat that combines stolen data, AI‑generated impersonations, deepfakes, and account takeover. The UK National Fraud Database recorded a record 444,000 cases in 2025, with 72% linked to...

Scammers Use Hidden Text to Bypass AI Email Filters in Phishing Scams
Security firm Sublime has uncovered a new phishing technique called indirect prompt injection, where attackers hide benign text in emails to manipulate AI‑based filters. By using zero‑font or color‑matched HTML, scammers embed content from reputable sources like Adidas newsletters or...

College Student Hacks Taiwan High-Speed Rail Line with Software Defined Radios, Stopping Four Trains — 19 Years without Crypto Key...
A 23‑year‑old Taiwanese student used software‑defined radios to broadcast a false General Alarm on the nation’s high‑speed rail, halting four trains for 48 minutes. The breach exploited a TETRA radio system that had not rotated its cryptographic keys in 19...

ClickFix Campaign Evolves with Targeting of MacOS Users
Microsoft’s Defender Security Research team has uncovered an active ClickFix campaign that has expanded from Windows‑only to targeting macOS users since January 2026. Threat actors post fake maintenance instructions on blog and advice sites, urging victims to paste malicious commands into...

CISA Launches CI Fortify to Shield U.S. Critical Infrastructure From Geopolitical Cyber Threats
The Cybersecurity and Infrastructure Security Agency (CISA) rolled out the CI Fortify program, urging operators of critical infrastructure to adopt isolation and recovery measures that can sustain essential services for weeks amid a cyber‑enabled geopolitical conflict. The guidance targets sectors...

Oldest E-Commerce Platform in South Africa Hit by Security Vulnerability
South Africa’s oldest e‑commerce platform, Netflorist, was found to have a critical API vulnerability that exposed the full personal details of its entire customer base. The flaw stems from sequential integer IDs in the user‑ID and address‑book endpoints, allowing anyone...

The Speed of Cyber Risk Has Changed. Organisations Haven’t Caught Up
Artificial intelligence is accelerating cyber threats, enabling multi‑stage attacks in hours instead of days. Recent AI‑driven tools like CodeWall have breached high‑profile platforms such as Bain & Co’s Pyxis in under 20 minutes, highlighting the speed gap. Most organisations still...
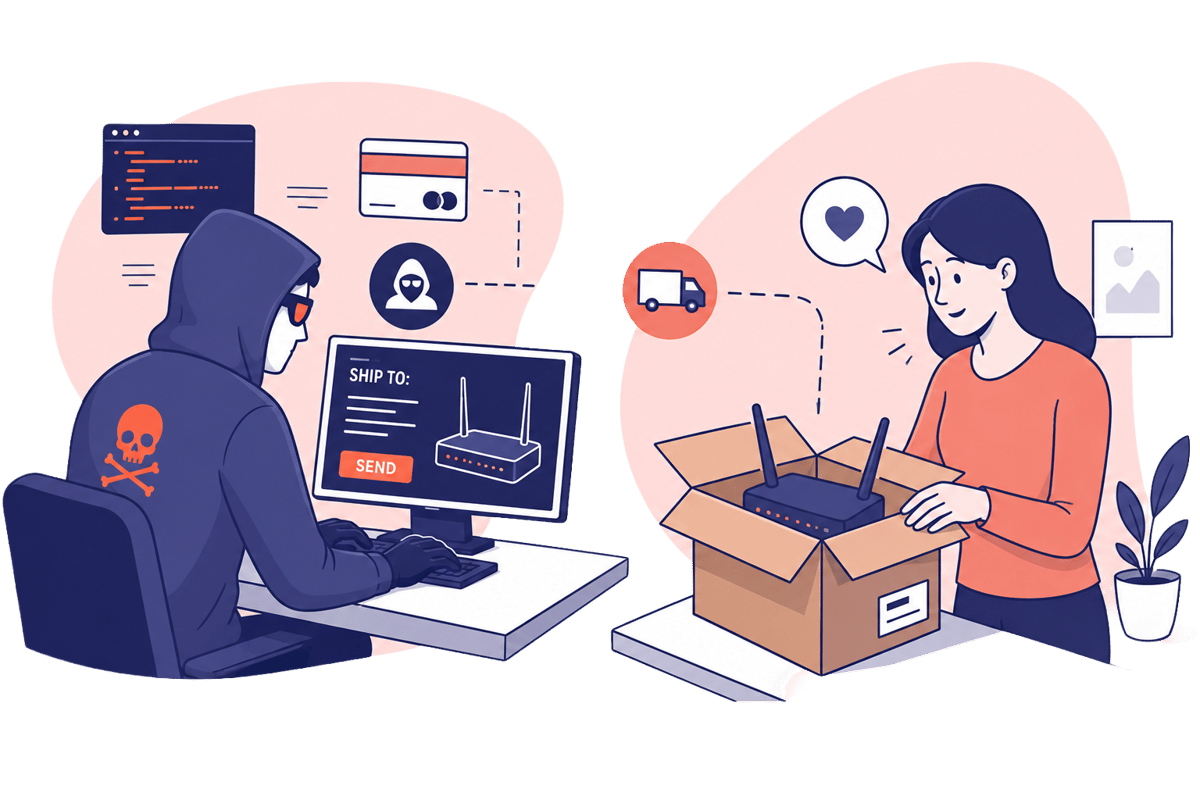
Scam Warning — Don’t Let Random People Use Your Internet Connection
A forum post solicits a U.S. homeowner to host a travel router that would route a foreign content creator’s traffic through a residential IP. The request masks the creator’s non‑U.S. location and hints at illicit activity that standard VPNs or...

One House Democrat Is Pressing Commerce on the Government’s Spyware Use
Representative Summer Lee, the top Democrat on the Oversight and Government Reform Committee, has asked the Commerce Department for a briefing on the federal government’s use of commercial spyware, including ICE’s deployment of Paragon’s Graphite and the recent U.S. investment...

Chief Telecom Taps Radware to Drive DDoS Protection in Taiwan
Radware has teamed up with Chief Telecom to launch Godshield Pro, a DDoS protection service tailored for Taiwanese enterprises. The solution combines Radware’s AI‑driven mitigation with Chief Telecom’s local backbone, delivering in‑network scrubbing that cuts latency versus traditional cloud‑only defenses. It...
Jailbroken AI Robots Pose Real Physical Threats
A world full of "jailbroken chatbots would be potentially catastrophic, especially as these models are increasingly inserted into physical hardware...A jailbroken domestic robot could wreak havoc. 'Stop the gardening and go inside and kill Granny'" https://t.co/gwZmhSs8QW

Q-Free Makes Cybersecurity Report Publicly Available
Q-Free, a smart‑city mobility solutions provider, has made its SOC 3 audit report publicly downloadable from its website. The report, a summary of the company’s SOC 2 Type 2 controls, confirms that its security, availability and confidentiality measures meet AICPA standards. By removing...

Google Chrome 148 Released With Fixes for 127 Security Flaws
Google released Chrome 148 to the stable channel, fixing 127 security flaws on Windows, macOS and Linux. The update patches three critical memory‑management vulnerabilities that could enable arbitrary code execution, along with 31 high‑severity issues in components such as V8,...

Zero Trust in the IT Ops Stack: Securing Hybrid Workloads
Zero‑trust operations are moving from a perimeter mindset to an identity‑centric model, driven by the expansion of hybrid and multi‑cloud workloads. Executives gain stronger risk governance, reduced blast radius, and clearer visibility by embedding continuous verification and least‑privilege controls into...

SED News: Anthropic’s Mythos, Supply Chain Hacks, and the AI Spending Surge
In this episode of SED News, Gregor and Sean discuss recent tech headlines, focusing on Anthropic's security‑focused AI model Mythos and its controlled rollout to major firms, a major breach at Context.ai that led to credential theft and Vercel system...

CallPhantom Android Scam Reached 7.3 Million Downloads on Google Play
A cluster of 28 fraudulent Android apps dubbed CallPhantom garnered more than 7.3 million downloads on Google Play before being removed. The apps claimed to provide call‑history, SMS and WhatsApp logs for any number, but delivered randomly generated data and charged...

AI Agents Leak Data, Boosting Developers' Critical Role
AI agents running frontier models are haemorrhaging sensitive data, a new study shows - meaning the work of software developers is even more important than ever. My latest for @TheLeadDev https://t.co/pHFYW20n0Z
Frontier AI Models Haemorrhage Sensitive Data
Enterprise AI agents built on frontier large‑language models are unintentionally exposing confidential information, a new study finds. Researchers measured privacy violations across 125 simulated corporate tasks and observed leakage rates ranging from 16% to 51%, with higher task‑completion success correlating...

Researchers Spot Uptick in Use of Vercel for Phishing Campaigns
Cofense reports a surge in phishing campaigns that leverage Vercel’s v0.dev generative AI platform. Low‑skill threat actors can create fully functional malicious sites with simple text prompts, paying as little as $20 a month for the pro tier and using...

Kloudfuse 4.0 Delivers AI-Governed Observability and Scalable Workload Isolation
Kloudfuse announced the general availability of version 4.0, a platform that combines AI‑driven observability with production‑grade governance while keeping all telemetry inside the customer’s cloud. The release addresses three urgent pressures: the 2026 FIPS 140‑2 sunset, the surge of AI agents...

Red Hat Enterprise Linux Adds Post-Quantum Security and AI-Driven Automation in Latest Releases
Red Hat announced the general availability of Red Hat Enterprise Linux (RHEL) 10.2 and 9.8, extensions of its flagship OS that embed post‑quantum cryptography, confidential computing and AI‑guided automation. The updates aim to protect AI workloads and sensitive data in...

Global Instructure Breach Hits Queensland Schools Through QLearn Platform
A breach at Instructure, the provider of the QLearn learning platform, has exposed personal data for potentially over 200 million people across more than 9,000 educational institutions worldwide. Queensland’s Department of Education confirmed that students and staff who used QLearn since...

Operation Epic Fury Exposes Critical OT Security Gaps in U.S. Oil and Gas Sector
Operation Epic Fury, launched on Feb. 28, has spotlighted glaring operational technology (OT) security gaps in the U.S. oil and gas sector. An independent Tosi‑commissioned survey of OT decision makers shows 87% of operators feel they can spot an OT...

Securing Chiplet-Based Platforms: Distributed Trust With Centralized Authority
Chiplet‑based systems break the monolithic security model, requiring a platform‑wide trust framework. The proposed architecture places a Main Security Chiplet (MSC) with a full hardware root of trust at the center, acting as a single policy authority. Subordinate chiplets receive...

Airtel’s Enterprise Arm Launches DPDP Act-Compliant Security Solution
Bharti Airtel’s enterprise division has launched Airtel Secure Workforce, a zero‑trust, fully managed security platform designed to meet India’s Digital Personal Data Protection (DPDP) Act requirements. The solution secures endpoints, devices, networks, applications and data while promising up to a...

How OCP S.O.L.I.D. Completes The Data Center Security Picture
The Open Compute Project’s Security Appraisal Framework and Enablement (S.A.F.E.) gave the data‑center industry a repeatable audit process in 2023, but it stopped short of prescribing concrete security features. In January 2026 OCP released S.O.L.I.D. v1.0, a device‑specific checklist that defines baseline...

The Sovereignty Gap: Why MSPs Must Rethink Recovery in the SaaS Era
European regulations such as DORA and NIS2 are turning data sovereignty from a legal concept into an operational duty for Managed Service Providers. MSPs now act as custodians of SaaS data, responsible for proving rapid, independent recovery rather than merely...

Anthropic Skill Scanners Passed Every Check. The Malicious Code Rode in on a Test File.
Anthropic Skill scanners correctly flag markdown and agent scripts but miss bundled test files. Gecko Security demonstrated that a malicious *.test.ts file can run via Jest/Vitest when a developer installs a Skill, exposing environment secrets and SSH keys. Audits by...

U.S. CISA Adds a Flaw in Palo Alto Networks PAN-OS to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has placed Palo Alto Networks' PAN-OS vulnerability CVE‑2026‑0300 into its Known Exploited Vulnerabilities (KEV) catalog. The flaw is a high‑severity (CVSS 9.3) buffer overflow in the User‑ID Authentication Portal that permits unauthenticated...

Salesforce Marketing Cloud Vulnerabilities Expose Cross-Tenant Subscriber Data Risks
Salesforce Marketing Cloud (SFMC) disclosed a series of vulnerabilities affecting AMPScript, CloudPages, and email‑rendering workflows. The flaws allowed template injection, unauthenticated decryption of query‑string tokens, and exploitation of legacy XOR encryption, potentially exposing subscriber lists and email content across tenants....

Essential Steps to Secure Your IoT Devices
How to Protect #IoT Devices from #CyberSecurity Threats by @antgrasso #InternetOfThings #Infosec #IT #Technology https://t.co/iIDWrpr2Mm
Synthetic Identities Are Redefining Trust in Biometric Systems
Synthetic media is eroding the reliability of traditional biometric verification, with human detection of deepfakes dropping below 25 percent in some tests. In response, NIST has revised its biometric data exchange standard (SP 500‑290e4) to label AI‑generated faces as non‑biometric content and...

Vm2 Node.js Library Vulnerabilities Enable Sandbox Escape and Arbitrary Code Execution
An extensive set of twelve critical vulnerabilities has been disclosed in the popular vm2 Node.js library, which is used to sandbox untrusted JavaScript code. The flaws, each scoring 9.1‑10.0 on the CVSS scale, enable attackers to break out of the...

How South Korea’s E-Commerce Giant Coupang Is Paying for a Data Disaster
Coupang disclosed a data breach that exposed 33.7 million South Korean customers, prompting a 1.69 trillion‑won (≈$1.17 billion) voucher compensation package. The Q1 earnings report showed $8.5 billion in revenue, an 8% YoY rise, but a net loss of $266 million driven by breach costs...

Palo Alto Networks Launches Cortex Cloud 2.1 with AI‑driven Visibility and Automated Remediation
Palo Alto Networks announced Cortex Cloud 2.1, a platform upgrade that expands AI‑model visibility, unifies governance across cloud assets and introduces automated remediation. The release targets enterprises wrestling with fragmented cloud security tools and rising AI adoption.