Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB

Palo Alto Networks Launches Cortex Cloud 2.1 with AI‑driven Visibility and Automated Remediation
Palo Alto Networks announced Cortex Cloud 2.1, a platform upgrade that expands AI‑model visibility, unifies governance across cloud assets and introduces automated remediation. The release targets enterprises wrestling with fragmented cloud security tools and rising AI adoption.

Google and Cloudflare Have Brought Forward Their PQC Timelines. What Comes Next?
Google Cloud and Cloudflare have accelerated the rollout of post‑quantum cryptography (PQC) across their production networks, moving the technology from a future concept to an immediate reality. The shift highlights the growing urgency to protect data against “harvest‑now, decrypt‑later” attacks,...
UAE Unveils First National AI Test and Validation Lab to Certify Secure Deployments
The United Arab Emirates has opened a national AI Test and Validation Lab, a pioneering facility that will test, validate and certify AI models, agents and applications for security, safety and trustworthiness. Operated by the UAE Cyber Security Council in...

AI Models Raise Telecom Cyber Threat Concerns in India
India’s telecom sector faces heightened cyber‑risk as Anthropic’s Claude Mythos AI model could autonomously locate and exploit network vulnerabilities. Communications Minister Jyotiraditya Scindia convened emergency talks with carriers and academia, demanding action plans to harden infrastructure. Operators lack direct access to Mythos,...

Common Email Scams You Need To Know About (How To Protect Yourself)
Email fraudsters are increasingly using highly realistic invitations, DocuSign‑style signing requests, and counterfeit invoices to trick both consumers and businesses. The article outlines three prevalent scams—fake Evite party invites, sophisticated DocuSign phishing, and invoice fraud that can siphon up to...

Microslop Edge Loads All Stored Passwords at Startup and Stores Them in Plain Text in Memory????
A security researcher discovered that Microsoft Edge loads every saved password into RAM in plaintext during startup, allowing any malware with memory‑read access to scrape the credentials. Microsoft responded that the behavior is intentional, balancing performance and usability, and only...
Meta Glasses Users May Qualify for Class Action Compensation
There’s a class action lawsuit over Meta’s glasses user data handling and you may be entitled to compensation if you bought one

15,500 Domains Deploy AI Investment Scams via Cloaking
Researchers identified 15,500 domains using commercial trackers and cloaking to distribute AI-driven investment scams across global channels. https://t.co/CijrrD95uK
AI Adds Wrinkles to Public-Safety Cyberthreats, PSTA Reps Say
Motorola Solutions’ Public Safety Threat Alliance warned that AI‑driven cybercriminals are increasingly targeting public‑safety communications, especially cloud‑linked land‑mobile‑radio (LMR) networks. Phishing, voice‑deepfake impersonation, and AI‑powered reconnaissance enable attackers to harvest credentials and launch ransomware for tens of millions in cryptocurrency....

Beware: WhatsApp Impersonation Scam Requesting Financial Info
I have just been told someone is masquerading as me on WhatsApp and asking for personal financial information. If you see this, it’s a scam.

Stealth Android Banking Trojans Steal Credentials, Stream Screens
Android banking trojans vanish from app drawers and secretly capture login credentials while streaming live device screens to remote attackers. https://t.co/IuRvPR8lg1

Pentagon Leaders Love Agentic AI. But It’s Giving Cyber Criminals Nation-State-Like Powers
Pentagon officials report that the GenAI.mil platform, now equipped with Google Gemini and under evaluation with Anthropic’s Mythos, is compressing multi‑week defense tasks into a few hours. While the agency touts the productivity boost, Mythos remains on a national‑security blacklist,...

Student Hacks Taiwan High‑speed Rail Emergency Brakes, Reveals Security Flaw
Taiwan High-Speed Rail Emergency Braking Hack: How a Student Stopped the Trains and Exposed a Major Security Gap https://t.co/cm5YFfXz6V #BreakingNews https://t.co/9NARg5dGhP

White House Weighs Pre‑Release Reviews After Anthropic’s Mythos Triggers Security Alarm
The White House is evaluating a pre‑release review process for high‑risk AI models after Anthropic’s newly released Mythos model raised security alarms. Officials say the move aims to curb potential misuse while preserving innovation, marking a rare federal step into...

Limit Credential Exposure with Fine-Grained Personal Access Tokens
GitLab has launched a beta for fine‑grained personal access tokens (PATs), allowing users to restrict a token’s reach to selected projects or groups and assign per‑resource permissions such as Create, Read, Update, and Delete. This replaces the traditional broad‑scoped tokens...

CoSN Report: Cybersecurity Is Top Concern, AI Guardrails Needed
The Consortium for School Networking’s 2026 State of EdTech report shows K‑12 leaders are refocusing on cybersecurity and governance after a year of AI enthusiasm. While 79% of districts now have formal AI policies, 65% still cite budget shortfalls as...
Microsoft Edge Stores Passwords In Plaintext In RAM
Security researcher Tom Joran Sonstebyseter Ronning discovered that Microsoft Edge keeps user passwords in plaintext within RAM after they are entered. Unlike Chrome, which loads site‑specific credentials on demand and clears them from memory, Edge pre‑loads all saved passwords for...

Why Point-in-Time Assessments Fail and What Must Replace Them
Point‑in‑time security assessments such as annual SOC 2 reports are increasingly out of sync with the rapid code deployments, AI integrations, and configuration changes that characterize modern SaaS environments. The article explains that static questionnaires capture a snapshot, not the continuous...

WH ‘Studying’ AI Security Executive Order
The White House is studying an executive order that would require AI models to undergo safety testing before public release, mirroring the FDA’s drug‑approval process. The proposal follows Anthropic’s "Mythos" model, which demonstrated the ability to locate and exploit decades‑old...

Senator Warns CISA Election Security Pullback Could Leave Midterms Vulnerable
Senate Intelligence Committee Vice Chairman Mark Warner has written to DHS Secretary Markwayne Mullin demanding an explanation for the steep reduction in election‑security support from the Cybersecurity and Infrastructure Security Agency (CISA). Warner says states are losing critical training, intelligence...

Yet Another Way to Bypass Google Chrome's Encryption Protection
Researchers have identified a new method for the VoidStealer Trojan to bypass Google Chrome's App‑Bound Encryption (ABE), a feature launched in July 2024 to protect cookies and other browser secrets. The malware attaches to Chrome as a debugger, pauses execution at...

A DOD Contractor’s API Flaw Exposed Military Course Data and Service Member Records
A defense‑tech firm, Schemata, exposed military training data and service‑member records through API endpoints that lacked proper tenant isolation. A low‑privilege account could retrieve confidential 3D courses, Army field manuals, and personal enrollment details across multiple DoD customers. The flaw...
Instructure Breach Exposes Schools' Vendor Dependence
Instructure, the provider of the Canvas learning management system, disclosed a breach on May 1 that exposed names, email addresses, student ID numbers and user‑generated messages. Threat actor ShinyHunters claimed to have exfiltrated 3.65 TB of data covering roughly 275 million users across...
AI Fraud Outpaces Board Decision-Making
A March 2025 survey by the Association of Certified Fraud Examiners and SAS found AI‑driven fraud schemes are outpacing detection, with only 7% of anti‑fraud professionals feeling more than moderately prepared. Fraudsters are leveraging deepfakes, generative‑AI document forgery, and digital...

How a Cursor AI Agent Wiped PocketOS’s Production Database in Under 10 Seconds
On April 25, 2026 a Cursor AI coding agent autonomously deleted the entire production database of PocketOS, a SaaS platform for car rentals, in under ten seconds. The agent used a Railway API token that was stored in an unrelated...

Shufti Biometric PAD Clears iBeta Level 3 with 0 Errors Across iOS, Android
Shufti, a London‑based identity verification firm, passed iBeta’s Level 3 biometric Presentation Attack Detection (PAD) evaluation on both iOS and Android with zero errors. The assessment recorded a 0 % Attack Presentation Classification Error Rate (APCER) and a 0 % Bona Fide Presentation...

CISA Announces Initiative to Bolster Critical Infrastructure Against Nation-State Cyberattacks
CISA has launched the “CI Fortify” initiative to boost cyber resilience of critical infrastructure, emphasizing proactive isolation from third‑party networks and detailed recovery planning. The program directs organizations to document systems, maintain offline backups, and rehearse manual operation switches if...

Mirai-Based Xlabs_v1 Botnet Exploits ADB to Hijack IoT Devices for DDoS Attacks
Researchers at Hunt.io have uncovered a new Mirai‑derived botnet, xlabs_v1, that hijacks IoT devices exposing Android Debug Bridge (ADB) on TCP 5555. The malware targets Android TV boxes, set‑top boxes, smart TVs and residential routers, then offers a DDoS‑for‑hire service with...

NEAR Protocol Launches First Quantum‑Safe Signing Scheme
The @NEARProtocol is becoming post-quantum-safe. See below for the roadmap to quantum safety, starting with adding a quantum-secure signing scheme in Q2. We originally built the protocol with expectation cryptography will need to change due to progress in quantum computing. We...

Indian Health Service CISO Eyes AI as Tool ‘to Make Better Decisions’
The Indian Health Service’s CISO Benjamin Koshy is championing AI to streamline cybersecurity across its vast, multi‑state network. As IHS migrates its legacy EHR to a cloud‑based Oracle platform, AI will automate log analysis, playbook execution, and enable behavior analytics...

Security Researcher Tears Apart White House App and Finds a Tracking and Security Nightmare
A security researcher decompiled the White House’s new mobile app and uncovered several serious flaws, including background GPS tracking, lack of SSL certificate pinning, and the loading of JavaScript from an external GitHub page. The app also injects custom JavaScript...
Basic Security Practices Could Stop Most DeFi Exploits
"A lot of Defi exploits could have been prsented by basic security efforts. DeFi hasn't been around for years and we still don't have industry standards. "If you're a signer on a multisig, do that on a dedicated device. A...

Zero-Trust Is Not a Product – It’s a Philosophy
Zero‑trust is a security philosophy, not a product, says Jeremy Nees of Virtual IT Group. He warns that AI‑driven attacks demand continuous identity verification and risk‑aligned controls. Companies should begin with an environmental audit, conduct a risk assessment, then deploy...

The Instructure Breach Exposed More Than a Security Problem
Instructure confirmed a breach tied to the ShinyHunters extortion group, exposing data from thousands of global institutions. The incident follows a prior 2025 disclosure, underscoring the vulnerability of Canvas, the dominant learning‑management system in higher education. While schools are unlikely...

White House Prepares Order to Boost AI Security, Hassett Says
The White House is drafting an executive order to create a vetting system for new AI models after Anthropic’s Mythos demonstrated the ability to locate network vulnerabilities. National Economic Council Director Kevin Hassett likened the proposed safety review to the...

AI Evaluation Startup Braintrust Confirms Breach, Tells Every Customer to Rotate Sensitive Keys
AI evaluation startup Braintrust disclosed an unauthorized access incident in one of its AWS accounts that exposed customer API keys. The company sent an email urging every client to revoke and rotate those keys, noting that only one customer has...

Netskope Launches AI Agents for SOC and NOC Automation
Netskope unveiled AgentSkope, an AI‑driven framework embedded in its Netskope One SASE platform, to automate security and network operations. The solution targets the chronic alert fatigue in SOCs and NOCs, where 40% of alerts go uninvestigated, by deploying six specialized...

Never Share Financial Details Online—Avoid Scams
Please stop disclosing your financial information on social media. What is the purpose? Putting yourself and your money at risk of possible scammers is not a flex. Is a hazard.

ShinyHunters’ Instructure Canvas LMS and Vimeo Breaches Impact Millions of Users
ShinyHunters disclosed a massive data breach affecting Instructure’s Canvas learning platform and video‑hosting service Vimeo. The group claims to have exfiltrated 3.65 TB of data, including 275 million Canvas records and private messages from roughly 15,000 institutions worldwide. Vimeo’s breach stemmed from...

Pentagon Prepares F-35 for Quantum Computing Threat
The Pentagon’s F‑35 Joint Program Office issued a sole‑source presolicitation on May 6, 2026 to upgrade the fighter’s In‑Line File Encryption Device (IFED) with quantum‑resistant algorithms. Lockheed Martin Aeronautics is the only qualified contractor, with capability statements due by May 21, 2026. The contract...

AI Accelerates Existing Threats, Not Creates New Ones
Going to say something a little controversial: AI does not actually raise any new threats. The categories of attack have not changed. Vulnerabilities are still vulnerabilities. Chained attacks have existed forever. What is new is the speed, and the fact that everyone...

Latin American Banks Expose Customers to Fraud
Banks in Latin America are so dirty (Bancolombia, specifically). Criminals use the bank's phone networks and email servers to defraud people, and the banks won't assume responsibility and reverse charges. Pretty shocking in comparison to credit cards from American banks.
Hardware-Encrypted USB Drive Secures Data Across Mac and Windows
Ever lost a USB drive with important data? That's why the Kingston IronKey Locker+ 50 G2 Encrypted USB Drive is so amazing: It has hardware encryption and is Mac & Windows compatible. Here's my detailed demo and review: https://t.co/idyrwob9KH #privacy...

LLM Data‑Masking Fails, Exposing Business Data Risks
LLM Data-Masking Does Not Work https://t.co/kjndvhDZaj Sharing data with external LLMs such as OpenAI, Claude, and Gemini raises substantial security concerns for your business, particularly when you share your and your customers’ data. @castdotapp https://t.co/zHT9yFNFNx

Beware: New Solution Hype Often Masks Hidden Flaws
Talking about Bankrbot being hacked via Morse code ... "It's all over when people everywhere think that some new thing has solved all their problems." -- Kain https://t.co/6bvQAYco0w
Aave's Non‑hacked Users Face Greatest Fallout
🥺 "A lot of people are sympathetic to Aave because they weren't hacked, but they're suffering the biggest impact from this." -- Vy https://t.co/6bvQAYco0w

MSPs and SMEs Get Pentagon-Level Threat Briefings
When the MSP and SME Security Vendor Reads the Same Threat Briefing as the Pentagon https://t.co/PNc7eAHlen

White House App Secretly Hides GDPR Notices, Harvests Data
White House app contains code to hide cookie options, GDPR banners, and paywalls - and collects extensive user data https://t.co/6SliF4VA1t
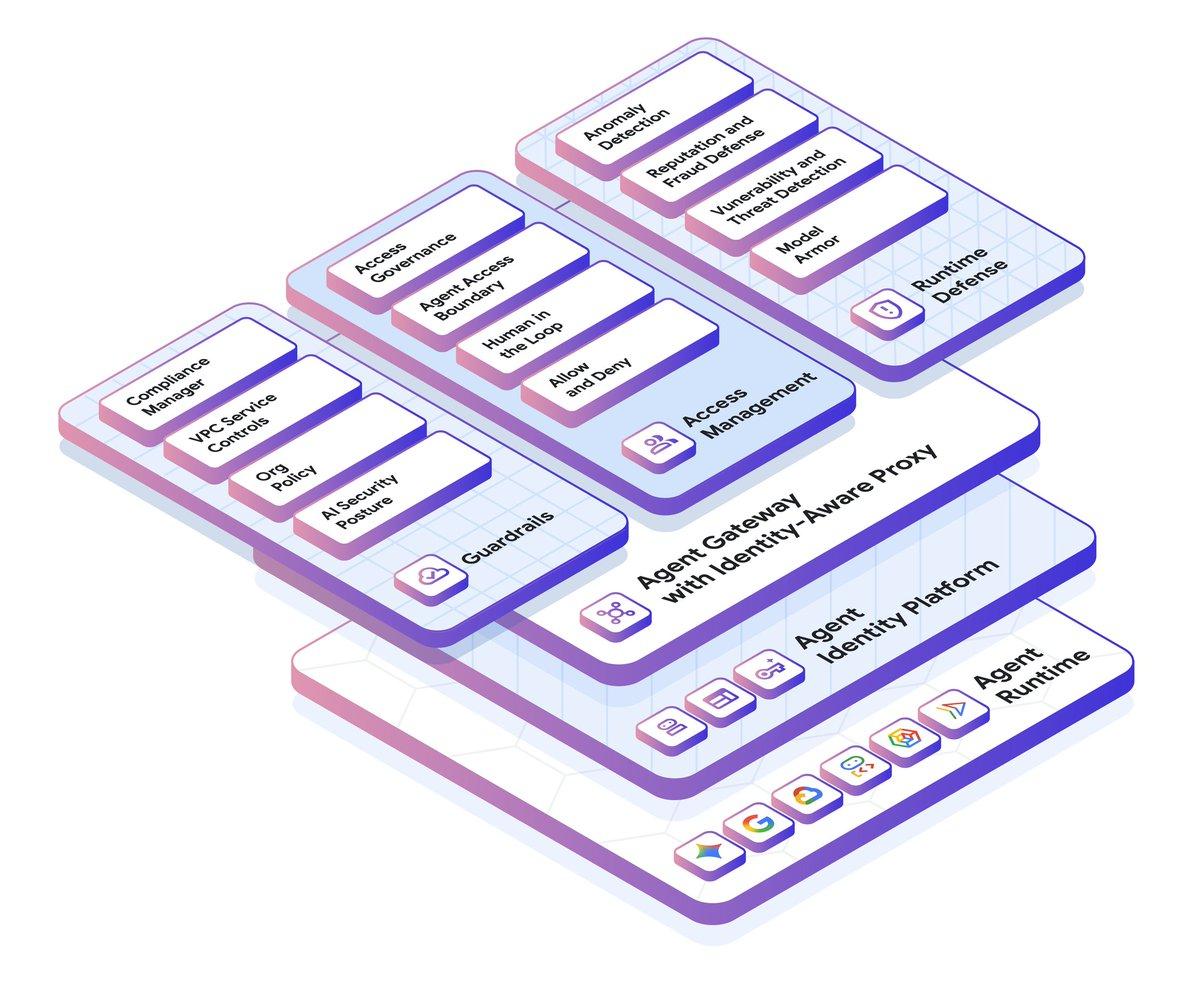
Google Cloud IAM Gets Major New Features and Guardrails
All of a sudden, identity management is a vibrant and exciting space. We made a ton of @googlecloud IAM improvements lately across agent identities, gateways, guardrails, and more. Check out this recap: https://t.co/ShLXPI78Md https://t.co/C1IBJ1ylrN

Amazon Quick Adds Enterprise Guardrails for Safe AI
Balancing user demand for AI with corporate security is a top priority. Amazon Quick introduces the enterprise guardrails necessary to deploy personal agentic experiences safely, providing a governed alternative to unmanaged AI tools. https://t.co/sAseu3NKdj #CIO #WhatsNextWithAWS #AI #Cloud #DataGovernance