Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB

The Creation of the Credential Protection Register; More than 750,000 Fraudulent Verification Requests Blocked
Australia’s Albanese Government has launched the Credential Protection Register, a national database designed to stop identity‑theft fraud in digital government services. Since its rollout, the register has blocked more than 750,000 fraudulent verification requests, averaging 18,000 per month. An investment of roughly $9 million USD is being used to enhance the system and embed user‑control features in the myGov app and website. The Digital ID Act of 2024 has also spurred 15 million Australians to activate myIDs, driving usage of the Australian Government Digital ID System to 80 million interactions in 2025.

Build the Agentic SOC to Combat AI-Powered Attackers
Splunk, now a Cisco subsidiary, is urging firms to replace fragmented security tools with an AI‑powered SecOps platform that unifies SIEM, SOAR and UEBA. At the ITWeb Security Summit 2026 in Johannesburg, VP Ahmed El Saadi will detail how this integrated...

When the Breach Gets In Through the CEO’s Inbox, Not the Firewall
The article argues that most cyber‑breaches now enter through human error, not firewalls, with social engineering as the dominant vector. It cites the 2023 MGM Resorts attack, where a ten‑minute phone scam cost the company roughly $100 million despite robust technical...

Bot Defense Is No Longer Optional for High Tempo Consumer Platforms
Consumer platforms are facing a surge in sophisticated bot activity, driven by agentic AI and API‑first architectures. Malicious bots can mimic legitimate AI assistants, generate false positives, and launch DDoS attacks that threaten infrastructure. The resulting click‑fraud and inflated advertising...

Blog 116a. The Vercel Breach: How AI Supply Chains Became the New Attack Surface
The Vercel breach revealed a new cyber‑risk vector: an AI‑enabled development supply chain. Attackers leveraged trusted integrations, automation pipelines, and generative‑AI tools within Vercel’s cloud‑native environment, bypassing traditional perimeter defenses. This incident shows that modern threats can infiltrate systems by...

FlySafair Leaked People’s Private Information During R12 Ticket Birthday Sale
FlySafair’s R12 birthday ticket sale exposed personal data via a chat API. The API leaked full names, email addresses and IP addresses for 1 hour and 39 minutes, affecting more than 594,000 participants. The airline removed the feature at 11:20,...

White House App Is a Terrifying Security Mess
A security analysis of the new White House Android app uncovered a suite of privacy‑and‑security flaws. The app continuously polls GPS coordinates—every 4.5 minutes in the foreground and 9.5 minutes in the background—and sends them to OneSignal’s servers, even though...

Telenor to Have Another Go at Weaning Itself Off US Hyperscalers
Telenor will launch Telenor Sovereign Cloud in the first half of 2025 as a distinct unit within Telenor Infrastructure. The service will operate from Norwegian‑controlled data centres, fully isolated from commercial global cloud providers, to satisfy strict security and data‑sovereignty...

Your Car Is a Data‑Collecting Spy on Wheels
In the digital world, it’s not only walls that have ears – cars do too. A modern car is a computer on wheels with a wide range of sensors: it stores/transmits GPS routes, telemetry, and keeps tabs on a connected...

South Africa’s Patching Problem Is About to Get Worse
South African enterprises are already missing patch windows for traditional software, and the rollout of autonomous AI agents threatens to widen that gap. TrendAI’s Zaheer Ebrahim warns that AI agents can be hijacked through hidden email instructions, bypassing malware defenses....
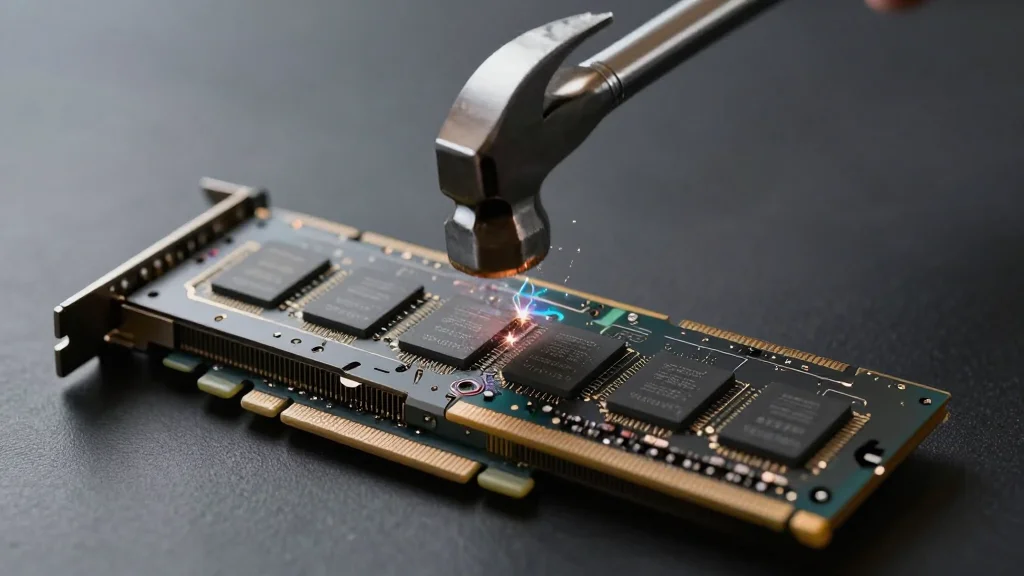
Rowhammer Attack Against NVIDIA Chips
Two independent research teams have demonstrated rowhammer attacks that exploit GDDR6 memory on NVIDIA Ampere GPUs, such as the RTX 3060, RTX 6000, and RTX A6000. By inducing bit flips in GPU memory, the attacks can corrupt page‑table structures and...

Day 162: Log-Based Network Traffic Analysis
The post outlines how to build a real‑time network security monitoring system that parses firewall, proxy and packet‑capture logs to detect threats, map traffic patterns, and flag anomalies. It emphasizes parsing logs instantly, scoring suspicious activity, visualizing flows, and issuing...
4 Things Apple Should Let Android Users Do on iPhone (and One Is Actually Happening)
Apple is rolling out encrypted RCS messaging that lets iPhone and Android users exchange native, end‑to‑end‑encrypted texts, currently available in beta with a toggle in Settings. The same beta adds EU‑only features such as one‑tap pairing for Android earbuds, smartwatches,...

Palo Alto Networks Issues Emergency Patch for PAN‑OS Zero‑Day CVE‑2026‑0300
Palo Alto Networks rolled out an emergency patch on May 13 for CVE‑2026‑0300, a critical PAN‑OS zero‑day that enables unauthenticated attackers to execute code with root privileges on PA‑Series and VM‑Series firewalls. The vendor plans a second patch wave on...

Why Europe Must Refuse the Data-Sharing Deal with the US
The European Commission is weighing a deal that would let U.S. authorities access personal data of 450 million Europeans in exchange for preserving the visa‑waiver program. Critics, led by the European Data Protection Supervisor, argue the arrangement lacks reciprocity and undermines...

Application Security Strategies Are Changing as AI-Generated Code Floods the SDLC
AI coding assistants have shifted from experimental tools to daily development aids, accelerating function drafting, test generation, and repetitive changes. However, security teams now grapple with how much AI‑generated code reaches pull requests without proper validation, as 46% of developers...

Daon Launches Workforce Identity Fraud Prevention Tool
Daon announced a Workforce Identity Fraud Prevention solution that unifies its TrustX, xProof, xAuth and xFace technologies into a single framework. The platform verifies candidate identities during hiring, issues phishing‑resistant passkey authentication, and provides step‑up and continuous re‑verification throughout employment....

VIAVI Unveils CyberFlood CF1000 Appliance for Validation of Multi-Terabit Security
VIAVI Solutions introduced the CyberFlood CF1000, a 2‑RU appliance that delivers native 400 G security and application performance testing up to 1.2 Tbps. The platform combines massive encrypted traffic generation, TLS throughput of 500 Gbps, and AI inference workload emulation without external switches....
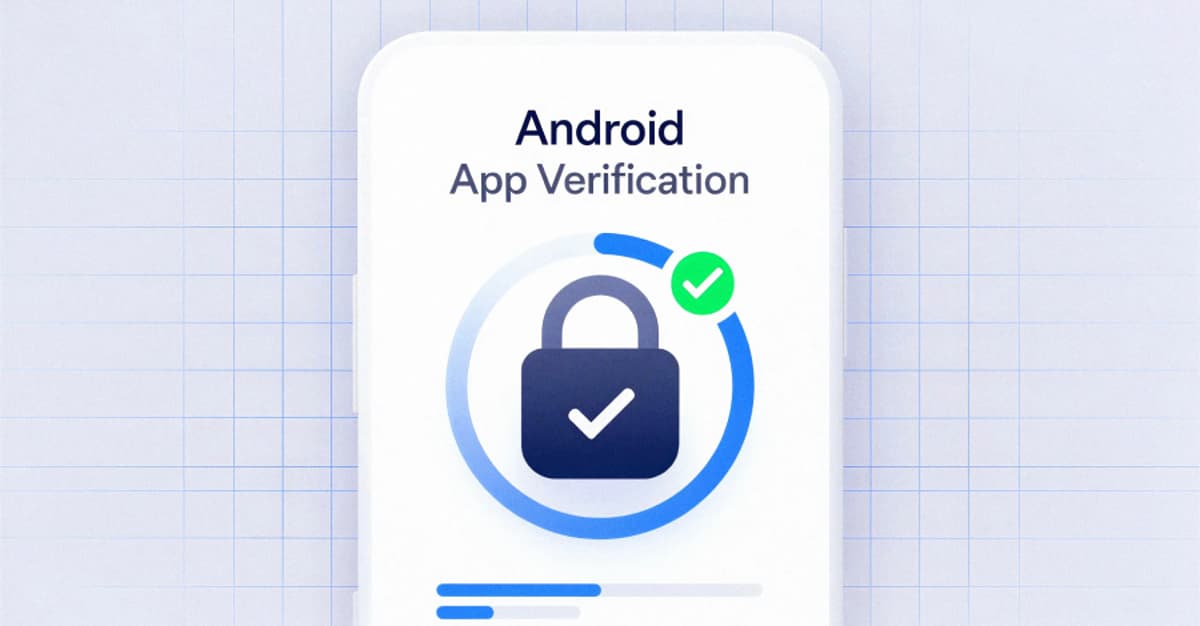
Google's Android Apps Get Public Verification to Stop Supply Chain Attacks
Google announced that its Binary Transparency system will cover all production Android applications and Mainline modules starting May 1, 2026. The public, cryptographic ledger records metadata for each released binary, allowing anyone to confirm that the software matches Google’s intended build. By...

Poisoned Truth: The Quiet Security Threat Inside Enterprise AI
Enterprises are rapidly deploying internal LLMs, copilots, and autonomous agents, but security teams are overlooking a silent threat: AI data poisoning. The risk arises when models ingest corrupted, stale, or low‑quality data, causing them to produce plausible yet wrong outputs...

Financial Services Industry Collaborates to Test Real-World Cyber Readiness
Lloyds Banking Group, Hack The Box, and Google Cloud Security hosted the first UK Financial Services Security Hackathon on April 27‑28, drawing 33 teams from 16 firms. The competition tested real‑world cyber readiness across web exploitation, forensics, OSINT, cryptography and...

Train Like You Fight: Why Cyber Operations Teams Need No-Notice Drills
Cybersecurity detection has improved, yet response readiness still lags behind. The article contends that scheduled tabletop exercises cannot mimic the physiological stress of real incidents and recommends no‑notice drills to build instinctive, resilient response capabilities. Citing medical, military and psychological...

EU Cyber Plan Barring Chinese Suppliers Will Cost US$430 Billion: Report
The European Union is set to adopt a new Cybersecurity Act that would bar Chinese hardware from critical infrastructure such as telecoms, energy grids, and transport networks. A recent study estimates the required replacement of Chinese equipment will cost the...

One in Eight Workers Has Sold Their Corporate Logins
According to Cifas’ Workplace Fraud Trends report, 13 % of UK employees either sold their corporate logins or knew a colleague who did in the past year. Acceptance of the practice spikes among senior staff, with 81 % of business owners deeming...

Heartbot AI Partners with Zyxel Networks to Bring Secure GenAI Access to SMBs Worldwide
Heartbot AI announced a strategic partnership with Zyxel Networks to embed its AnyInsight.ai platform into Zyxel’s USG FLEX H series firewalls, delivering a secure, governed gateway for generative AI to SMBs and managed service providers. The integration offers unified access...
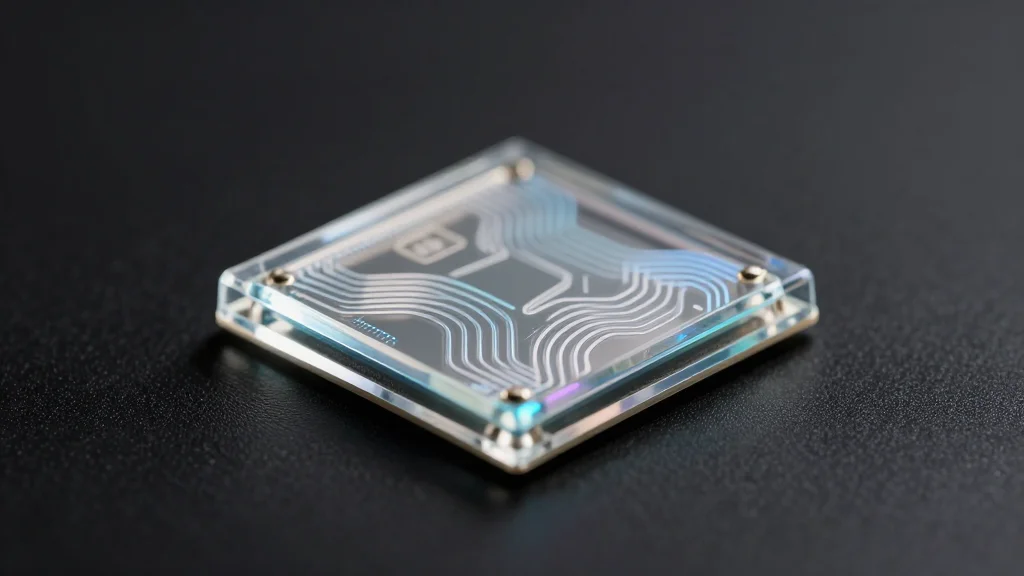
How Spain’s ICFO Helped Build a Quantum Security Startup for the AI Era
Quside, a Barcelona startup spun out of the Institute of Photonic Sciences (ICFO), sells photonic quantum random number generator (QRNG) chips that deliver high‑quality, verifiable entropy for cryptographic keys. The firm has shipped to 50‑60 customers worldwide and expects to...
Massive “Low and Slow” DDoS Attack Hits Platform With 2.45 Billion in 5 Hours
Cybercriminals launched a fragmented "low and slow" DDoS campaign that flooded a major user‑generated content platform with 2.45 billion requests over five hours. The attack leveraged more than 1.2 million unique IP addresses across 16,402 autonomous systems, peaking at 205,344 requests per...

EnforceAuth Open-Sources Zift — A Code Scanner Built to Close the Authorization Gap in Enterprise and AI Systems
EnforceAuth has released Zift, an Apache‑2.0 open‑source scanner that automatically discovers authorization decisions across multi‑language codebases and generates Open Policy Agent (OPA)‑ready Rego policy stubs. In an internal benchmark of a financial app, Zift found only 20% of enforcement points...

‘We’re Not Investing as Much as We Should in Their Skills and Development’: Skills Shortages Remain a Key Factor in...
Fortinet’s 2026 Global Cybersecurity Skills Gap Report finds human factors remain the top cause of breaches, with 56% of leaders pointing to employee security‑awareness gaps and 54% to a shortage of trained staff. Traditional attacks—malware (39%), phishing (36%), web (31%)...

Dark Sky Technology, and Carahsoft Partner to Deliver Advanced Software Supply Chain Risk Management Solutions to Government Agencies
Dark Sky Technology and Carahsoft have formed a strategic partnership to make the Bulletproof Trust platform available to U.S. government agencies through Carahsoft’s extensive contract vehicles. The platform ingests Software Bills of Materials, monitors more than 30 vulnerability databases, and...
US Government To Review Major AI Models
The U.S. Department of Commerce will require Google, Microsoft and xAI to submit new AI models for pre‑deployment review, expanding the voluntary framework first used with OpenAI and Anthropic in 2024. The Centre for AI Standards and Innovation aims to...

Kaspersky Identifies Ongoing Supply Chain Attack
Kaspersky’s March 2026 study revealed supply‑chain attacks as the most frequent cyber threat, yet only 9% of firms listed them as a top priority. The firm now issues a five‑point mitigation playbook covering vendor audits, strict procurement, privilege restriction, continuous XDR...

UIDAI, NFSU Sign 5-Year Pact to Boost Cybersecurity and Digital Forensics
India’s Unique Identification Authority (UIDAI) has signed a five‑year partnership with the National Forensic Sciences University (NFSU) to boost cybersecurity and digital forensics across the Aadhaar ecosystem. The agreement, announced on May 5 in Ahmedabad, outlines six strategic pillars covering talent...

The UAE’s Cybersecurity Strategy in the Hybrid Warfare Era
The United Arab Emirates has unveiled a comprehensive cyber‑resilience strategy to counter the surge of AI‑powered attacks that accompany modern hybrid warfare. The UAE Cybersecurity Council reports a 40% rise in home‑network attacks and notes that 76% of MENA organizations...

AI only as Secure as the Information Behind It: OpenText
OpenText warns that AI-driven security is only as secure as the data it processes, emphasizing the risk of fragmented, ungoverned information. The company argues that without robust information governance, AI can magnify bias, expose sensitive content, and accelerate breach impact....

Australia Forms Cyber Incident Review Board to Strengthen Defences After Major Breaches
Australia has established a Cyber Incident Review Board under the Cyber Security Act 2024 to conduct no‑fault, post‑incident analyses of major cyber attacks affecting both government and private firms. Chaired by Telstra’s CISO Narelle Devine, the board brings together leaders...

Hardware-Software Concealing of Secret Key and Enhancement of Pipelined Advanced Encryption Standard Cryptographic Core via Reconfigurable Devices for Hybrid Fast...
Researchers designed a pipelined two‑cycle AES‑256 cryptographic core on a Cyclone V SX SoC FPGA that delivers 12.8 Gb/s encryption throughput while occupying only 9 % of the device’s logic. Compared with recent FPGA implementations running at 96‑100 MHz, the new core achieves a seven‑fold...

PNB Allocates up to ₹8,000 Crore for Cybersecurity, Ramps up Tech Procurement
Punjab National Bank (PNB) is allocating up to ₹8,000 crore (about $84 million) – roughly 20% of its technology budget – to bolster cybersecurity against rising digital threats, including AI‑driven attacks. The allocation represents a more than 50% increase from the prior...

Middle East Cyber Battle Field Broadens — Especially in UAE
The United Arab Emirates saw daily breach attempts explode from roughly 90,000‑200,000 pre‑conflict to 600,000‑800,000 after Israel and the U.S. launched operations against Iran. Saudi Arabia’s cyber‑relevant activity surged 25‑fold and Qatar’s more than quadrupled, reflecting a regional escalation. Attack...

NCSC Highlights the Potential of AI to Enhance Cyber Defence
The UK National Cyber Security Centre (NCSC) warned that while artificial intelligence can significantly strengthen cyber‑defence, its rollout will be gradual and technically demanding. Deputy CTO Peter Haigh said AI could improve threat detection, vulnerability discovery, software security, system management...

Palo Alto Networks to Patch Zero-Day Exploited to Hack Firewalls
Palo Alto Networks disclosed a critical zero‑day vulnerability, CVE‑2026‑0300, that exploits a buffer overflow in the User‑ID Authentication Portal of its PAN‑OS firewalls. The flaw grants unauthenticated attackers root‑level code execution on PA and VM series devices when the portal...

Microsoft Enables Hotpatching by Default: Windows Updates without Restarts Become a Reality
Microsoft will enable Hotpatching by default for eligible Windows 11 24H2+ and Windows Server 2025 devices starting in May 2026. The feature lets security‑relevant updates be applied directly in memory, removing the need for a system restart. Hotpatching is limited to devices managed...

European Industry Fears ‘Back Door’ for US in Cloud Law
The European Commission is drafting the Cloud and AI Development Act to foster a sovereign cloud ecosystem and reduce reliance on foreign tech. Critics say the proposal includes a loophole that permits U.S. providers when no European alternative exists, effectively...
Report: How Cyber Crime Affected the U.S. in 2025
The FBI’s Internet Crime Complaint Center reported that U.S. cyber‑enabled crime losses jumped to $20.9 billion in 2025, a 26 percent rise from the previous year. More than one million incidents were logged, with investment fraud leading the cost chart at $8.6 billion,...

Red Access Skips Proper Disclosure, Public Apps Are Expected
A cybersecurity firm, “Red Access,” contacted us less than 24 hours before going to the media with vague claims about Replit. This is not how responsible security research works. The standard practice in terms of disclosure policies, as followed by CISA,...

CISA Claims AI Automation Cuts Threat Analysis Time, Boosts Mission Support
The Cybersecurity and Infrastructure Security Agency says AI automation has dramatically accelerated threat triage and mission‑support functions. Officials cite faster analyst response, real‑time efficiencies, and lingering hurdles around legacy workflows and data governance.

Aussie Small Businesses Still Not Prioritising Cyber Security
Research commissioned by Optus and conducted by Ipsos finds only 40% of Australian small businesses prioritize cyber security. One‑third have already suffered a cyber incident, yet 60% lack a formal cyber plan and many spend less than two hours per...

Neglected Credentials Give Attackers a Ready-Made Backdoor
Employees reuse passwords. Former employees may still have access to systems. Shared mailboxes may have weaker protections than individual accounts. Vendors may have old logins. Cloud applications may be added without full visibility from IT. Over time, the identity layer...

Utah's Internet Crackdown: Best VPNs for Residents
Utah is pioneering controversial new internet restrictions, making a reliable VPN essential for digital privacy. Here are the top three providers offering the best speeds, local servers, and security for residents of the Beehive State. https://t.co/RkYzBwD3QE

Beware: Fake Google Security Calls Use These Numbers
Hahaha, I got several phone calls within the last 10 minutes of people claiming that they represent 'Google Account Security'. It's an obvious scam. So beware of calls from: 650-409-7447 650-733-9252 650-741-1891 Google will never call you about your account security.