Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB

Cisco to Acquire Israeli AI‑Security Startup Astrix for Up to $400 Million
Cisco Systems will purchase Israeli cybersecurity firm Astrix Security in a transaction valued between $300 million and $400 million. The deal adds Astrix’s platform for discovering, governing and securing AI agents and non‑human identities to Cisco’s security suite, addressing a growing blind spot as enterprises deploy autonomous AI workloads.

Kalshi Rolls Out Facial-Recognition Safeguards to Bar Under‑age Traders
Kalshi announced a suite of new identity‑verification tools—including facial recognition, selfie checks and two‑factor authentication—to keep users under 18 out of its prediction‑market platform. The measures arrive as lawmakers and sports leagues push for stricter age limits on derivative‑style contracts.

This Week's Breach Landscape: Vishing, Social Engineering, Data Dumps
Weekly update is up! The Current State of Breaches: Vishing, Social Engineering, ShinyHunters, Salesforce, Extortion and Massive Troves of Data: https://t.co/39w6jR8MRH

South Africa Publishes Draft Rules for National Digital ID System
South Africa's digital‑identity regulator Schreiber released draft regulations for a national digital ID system on May 5, 2026. The draft, which is expected to enable a smartphone‑based identity framework, marks the continent’s first major move toward mobile digital identification. Officials say the...

Incredibuild Unveils Islo Sandbox to Secure AI Coding Agents at Scale
Incredibuild announced the launch of Islo, a sandbox that isolates AI coding agents in dedicated cloud environments with granular security policies. The solution lets enterprises run agents 24/7 while protecting codebases, secrets, and infrastructure, aiming to turn experimental AI workflows...

Microsoft Confirms April 2026 Windows Updates Break Third‑Party Backups
Microsoft confirmed that the April 2026 security updates (KB5083769) add the vulnerable driver psmounterex.sys to its blocklist, causing VSS‑dependent backup tools to fail. The company advises customers to upgrade affected applications rather than uninstall the patches.
F5 AI Guardrails Quickstart: Answering the Hard Questions
A financial services firm is piloting an AI assistant that draws answers from its own underwriting manuals and regulatory filings. To address security gaps, F5 offers an AI Guardrails quickstart that adds an inline inspection layer for both prompts and...

AI-Enabled Vulnerability Discovery Is Reshaping National Cyber Defence
Anthropic’s Claude Mythos LLM demonstrated strong vulnerability‑discovery ability, flagging 271 flaws in Firefox during preview testing. AI‑enabled tools now automate key steps of zero‑day exploit development, dramatically reducing time and cost compared with traditional manual methods. The UK warns that...

Expert Warns over Dangers of Amap
A Taiwan security expert warned that China could exploit data collected by the Amap navigation app against Taiwan. Amap offers 3D street views and traffic‑signal countdowns, gathering real‑time location and movement data. Taiwan’s Ministry of Digital Affairs has banned government...

Taiwan’s Global Cybersecurity Role Touted at Event
Taiwan is positioning itself as a global cybersecurity leader, announcing its first international certification for semiconductor‑equipment security at the CYBERSEC 2026 conference. The island’s cyber industry is approaching NT$100 billion (≈US$3.16 billion) in output, while critical infrastructure faced up to 2.63 million intrusion attempts...

Microsoft Edge Will Load All Your Passwords Into Memory in Plaintext, but Microsoft Says It's Not a Security Concern
Microsoft Edge was found to load every saved password into process memory in cleartext when the browser starts, a behavior not seen in other Chromium‑based browsers. Security researcher @L1v1ng0ffTh3L4N demonstrated that an attacker with administrative rights could scrape these credentials....

Megaport Launches Built-In DDoS Protection Enabling On-Demand Network Resilience
Megaport Limited announced Megaport DDoS Protection, a built‑in security layer that filters malicious traffic directly within its global network fabric. The service eliminates the need for external scrubbing centers, reducing latency and simplifying routing for enterprise cloud environments. Customers can...

May 5, 2026 Quick Space Links
NASA investigators revealed a Chinese national phishing campaign that stole software from NASA and the Department of Defense, highlighting growing cyber threats to U.S. space assets. NASA also announced it is evaluating commercial communications providers, including Starlink and other LEO...

Supply-Chain Attacks Take Aim at Your AI Coding Agents
AI coding agents that automatically pull packages from registries are now being weaponized by supply‑chain attackers. Researchers at ReversingLabs identified the PromptMink campaign, attributed to North Korea’s Famous Chollima APT group, which plants persuasive bait packages and malicious dependencies to trick...

NIST SP 800-223 and 800-234: A Turning Point for Federal High-Performance Computing Security
The National Institute of Standards and Technology released SP 800‑223 and the draft SP 800‑234, the first federal frameworks dedicated to securing high‑performance computing (HPC) environments. The standards arrive as the Genesis Mission, a $320 million initiative, links the 17 U.S. national laboratories...

Extreme Moves Toward Autonomous Networking with Advanced AI Agent, Management Tools
Extreme Networks announced its second‑generation AI agent, Extreme Agent ONE, at Extreme Connect 2026, promising proactive, autonomous detection and remediation of network issues. The company also rolled out a major update to its Platform ONE management suite, adding third‑party device...

From Mandate to Momentum: Turning CISA’s Edge Device Directive Into Lasting Capability
The Cybersecurity and Infrastructure Security Agency’s Binding Operational Directive 26‑02 compels federal agencies to identify, remediate and continuously manage unsupported edge devices such as routers and firewalls. Agencies have 90 days to inventory these assets, 18 months to replace or mitigate them, and...

Top Google Scientist Says EU Data Measures Pose Privacy Risk for Users
A distinguished Google scientist warned EU antitrust regulators that the Commission’s draft rule to share search‑engine data with rivals could expose user privacy. He demonstrated that Google’s AI red team re‑identified anonymised search data in under two hours, questioning the...

Trellix Source Code Breach Highlights Growing Supply Chain Threats
Trellix disclosed that an unknown threat actor gained unauthorized access to a portion of its source‑code repository, though the company says there is no evidence the code was exploited or the release process compromised. The breach comes amid a wave...

EU Reissues Formal Recommendation to Bar Huawei, ZTE From Connectivity Infrastructure
The European Commission on May 4, 2026 formally recommended that all 27 EU member states keep Huawei and ZTE out of any connectivity infrastructure. The move follows a failed voluntary phase and precedes a draft cybersecurity law that could make...

Kelp DAO Accuses LayerZero of Deflecting Blame for $300M Bridge Hack
Kelp DAO issued a detailed rebuttal to LayerZero’s post‑mortem of the April 18 rsETH bridge exploit that cost roughly $300 million. The DAO claims the 1‑1 DVN configuration blamed by LayerZero was the platform’s default, approved in private communications and used by...

Dr. Keith Hardiman Named Deputy CIO for U.S. Air Force and Space Force
The Department of the Air Force confirmed Dr. Keith Hardiman as the permanent Deputy Chief Information Officer for both the U.S. Air Force and U.S. Space Force. Hardiman, who has acted in the role since July 2025, will steer enterprise...

CISA Mulls Cutting Government Vulnerability Fix Timeline to 3 Days Amid AI‑Powered Threats
U.S. Cybersecurity and Infrastructure Security Agency officials are weighing a proposal to reduce the default remediation deadline for actively exploited vulnerabilities from two‑to‑three weeks to just three days. The change is driven by fears that advanced AI models like Anthropic’s...
Research Hub Bridges Cybersecurity Gap for Under-Resourced Organizations
Federal cybersecurity funding and staffing have slashed, leaving state, city and nonprofit IT teams exposed. The University of California, Berkeley’s Center for Long‑Term Cybersecurity (CLTC) is stepping in, offering free clinics, research surveys and volunteer reserve teams to help low‑resource...

Salesforce Connected App to ECA: What the May 11, 2026 Deadline Actually Requires (and What It Doesn’t)
Salesforce has set a hard May 11 2026 deadline for all ISV‑owned Connected Apps and External Client Apps to adopt four OAuth security controls—PKCE, Refresh Token Rotation, a 30‑day idle timeout, and a static IP allowlist. Compliance can be achieved with a...

Edge Browser Leaves Passwords Exposed in Plain Text, Says Researcher
A Norwegian researcher discovered that Microsoft Edge’s password manager decrypts and stores saved passwords in plain text within the browser’s process memory, even after the browser is closed and reopened. Microsoft responded that this design balances performance and security, claiming...

CISA Boasts AI Automation Improvements to Threat Analysis, Mission Support
The Cybersecurity and Infrastructure Security Agency (CISA) reports its security operations unit has achieved the largest productivity gains from AI‑driven automation, enabling analysts to triage threats faster and focus on high‑value alerts. The technology also streamlines real‑time customer support in...

Jamie Dimon and Dario Amodei Sidestep Question About Whether the AI Cyber ‘Freakout’ Is Warranted
Jamie Dimon and Anthropic CEO Dario Amodei faced a CNBC query on whether AI‑enabled cyberattacks merit the current "freakout" narrative. While neither gave a definitive yes or no, both underscored that AI‑driven threats are real and accelerating, citing Anthropic's Mythos...

35,000 Users Targeted in Phishing Campaign in Just Two Days
Between April 14 and 16, a sophisticated phishing operation hit more than 35,000 users across 13,000 organizations in 26 countries, with 92% of victims located in the United States. The campaign masqueraded as compliance‑related communications, using organization‑specific details and encrypted‑looking...
Why Security Leadership Makes or Breaks a Pen Test
Penetration testing delivers real security value only when leadership sets clear scope, threat focus, and stakeholder alignment before the engagement and drives disciplined follow‑up afterward. Experts stress that testers need autonomy during the test, but the pre‑test decisions dictate relevance...

Italy PM Meloni Warns over AI Deepfakes After False Photos of Her Circulate
Italian Prime Minister Giorgia Meloni announced that AI‑generated fake images of her have been circulating online, including a fabricated photo of her in underwear. She posted the deepfake herself to illustrate the threat and warned that such manipulations can deceive...
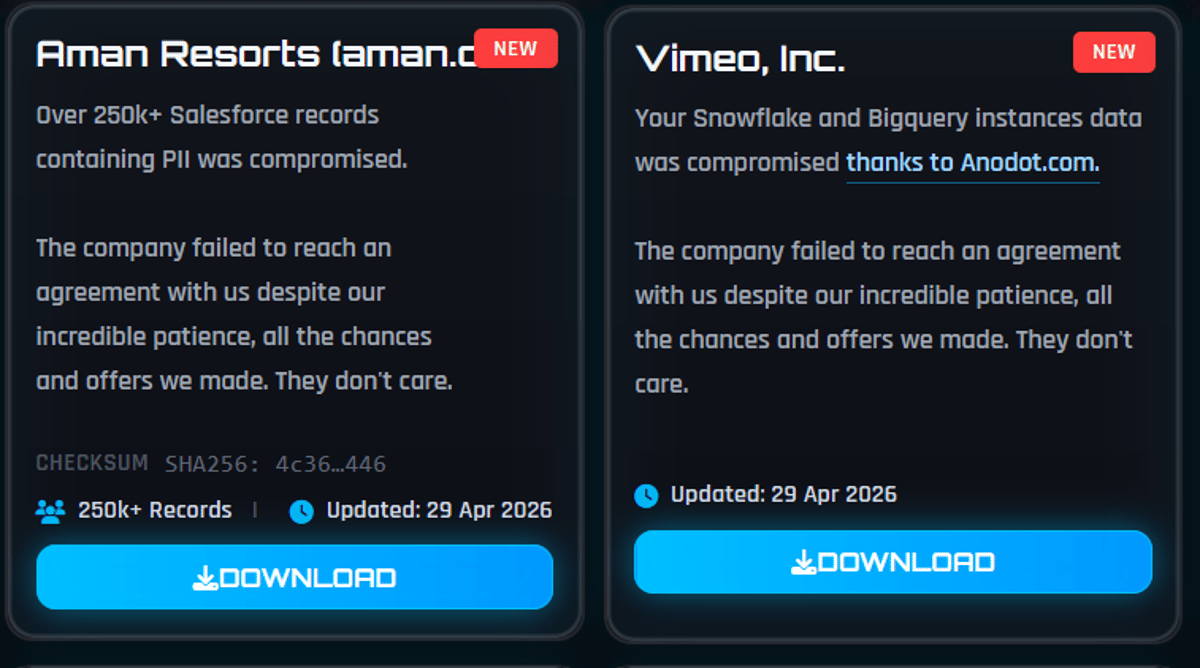
Vimeo Confirms Breach via Third-Party Vendor Impacts 119K Users
Vimeo disclosed that the ShinyHunters cybercrime group accessed data belonging to about 119,000 users in April 2026. The breach stemmed from a compromise of Anodot, a third‑party analytics provider integrated with Vimeo’s platform. Exfiltrated information included email addresses, video titles,...

The New Security Risk Every Business Using AI Needs to Know About (and How to Protect Yourself)
Businesses are confronting a new security threat dubbed "OpenClaw," where autonomous AI agents perform actions—often with write or execute privileges—without human oversight. These agents now generate over 80% of authentication attempts, yet receive less than 5% of security monitoring. Traditional...

Breaking: Autonomous Agents Are a Shitshow
A new study of 847 autonomous agent deployments across healthcare, finance, customer service and code‑generation found that 91% are vulnerable to subtle tool‑chaining attacks, while 89.4% exhibit goal drift after roughly 30 steps. Memory‑augmented agents are especially at risk, with...

Connecticut Passes Law Banning Sale Of Location Data, Regulating Ad Volume
Connecticut lawmakers passed Senate Bill 4, a privacy measure that bans the outright sale of precise geolocation data and imposes new limits on surveillance‑based pricing and ad volume in streaming. The bill also requires data brokers to register with the state...

10 Years After OPM Data Breach, Identity Protection Benefits for Affected Feds Start to Expire
A decade after the 2015 Office of Personnel Management breach that exposed more than 22 million federal employees and applicants, the government‑provided MyIDCare identity‑theft protection program is winding down. Enrollees receive rolling emails stating that credit monitoring, dark‑web scanning and insurance...

White House Wants to Vet Powerful AI Models for Risks − a Computer Scientist Explains Why AI Safety Is so...
The White House is drafting a federal review process to assess the safety of powerful artificial‑intelligence models before they are released, a notable shift from its traditionally anti‑regulatory posture. The move follows Anthropic’s decision to restrict access to its Mythos...

New WhatsApp Flaws Could Affect Billions of Users After Meta Security Patch
Meta has released a security patch that closes two WhatsApp vulnerabilities—CVE‑2026‑23866 on iOS/Android and CVE‑2026‑23863 on Windows—that could have been used to hide malicious links or executable files within trusted messages. While no active exploitation has been observed, the flaws...

DNSSEC Changes Are Coming. MSPs Should Check Customer Readiness Now
ICANN will introduce a new DNSSEC root trust anchor (KSK‑2024) with a rollover slated for October 2026, forcing validating resolvers to update their trust anchors or face SERVFAIL errors. While the root and most TLDs are signed, over 80% of individual...

Student Hacked Taiwan High-Speed Rail to Trigger Emergency Brakes
A 23‑year‑old Taiwanese university student was arrested after using software‑defined radio equipment to impersonate a TETRA beacon and broadcast a high‑priority "General Alarm" signal. The fake transmission forced four high‑speed rail trains to engage emergency brakes, halting service for 48...

CISA Pushes Critical Infrastructure Operators to Prepare to Work in Isolation
U.S. Cybersecurity and Infrastructure Security Agency (CISA) unveiled CI Fortify, a national program urging critical infrastructure operators to plan for and operate in isolation from the internet and third‑party services during severe cyber incidents. The initiative emphasizes controlled disconnection, rapid...

Your Employees Know What Phishing Looks Like. They’re Still Getting Fooled. Here’s Why.
A recent Sagiss survey of 500 U.S. desk workers shows AI‑generated phishing is now more convincing, with 72% saying attempts look more professional. Employees still click despite training, largely because they operate under pressure, multitask, and face after‑hours expectations. The...

Cross‑zone Composability Faces Hurdles in Privacy Blockchains
🧩 In a world of privacy blockchain, where switching from chain to chain can create data leakage, what does that mean for DeFi's money legos? "I don't think the composability dream is dead. I think you can have composability within zones....

Predictable Outcome Based on Their Track Record and Disclosure
Given their track record and seeing the disclosure below, this is heading for a pretty predictable outcome…

Google Update: Android Flaw Could Put Billions of Devices at Risk
Google disclosed a critical remote‑code‑execution bug (CVE‑2026‑0073) in Android’s adbd daemon that can be triggered without any user interaction, affecting Android 14 through 16‑QPR2 and potentially billions of devices. The flaw is proximal, meaning attackers only need network or physical...
CISA Pushes 3‑day Patch Deadline Amid AI Defense Gaps
“Patch the KEVs faster” still isn’t taking a scalable, targeted, realistic approach to the #Mythos #AI era, for gov or private sector. AI defense has not yet produced an autonomous, safe answer to meet the AI offense moment.

AI May Not Deliver Perfectly Secure Code in 5 Years
Given massive AI advances, do you believe than within 5 years it would be feasible to write 100% vulnerability-free code? #NoNuancePoll

Drift Sets Out Token-Based Recovery Framework for $295M April Exploit
Drift Protocol unveiled a token‑based recovery plan to compensate users affected by the April 1 exploit that caused $295.4 million in losses. The scheme issues SPL tokens worth $1 per verified loss, funded by the protocol’s $3.8 million reserve, a $127.5 million commitment from...
Tax Tribunal Scotland Site Lacks Security Certificate—Avoid It
Quick warning to tax people to not go to Tax Tribunals Scotland's website. No security certificate, so it's either been hacked or had an IT snafu. https://t.co/XaIJLHfAGO

EU Flags Insecure, Cheap Inverter Software as Security Risk
The inverter (especially its software) is a security risk if nog open source and managed well and it's a relatively cheap component compared to solar panels and battery cells. I'm glad the EU recognizes this.