Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB

Stealthy Malware Abuses Microsoft Phone Link to Siphon SMS OTPs From Enterprise PCs
Security researchers at Cisco Talos have uncovered a new malware campaign that leverages Microsoft’s Phone Link (formerly Your Phone) to intercept SMS‑based one‑time passwords from enterprise Windows PCs. The remote‑access trojan, dubbed CloudZ, works with a custom Pheno plugin to monitor the Phone Link SQLite database and capture OTPs without infecting the mobile device itself. The infection chain begins with a fake ScreenConnect update, establishes persistence via a scheduled task named “SystemWindowsApis,” and includes anti‑analysis checks before delivering the payload in memory. Talos released indicators of compromise and detection signatures, but has not linked the activity to a known threat actor.

SMEs Fall Short on AI Cyber Security Training Despite Rising Risks
AI adoption is accelerating among UK small and medium‑size enterprises, but cyber threats are rising in parallel. A new Moneysupermarket survey shows only 10% of SMEs provide AI‑specific security training, despite 43% of all businesses reporting a breach in the...

ZDNET Flags AI Agent Sprawl, Calls for Agent Management Platforms as New HR‑Tech
ZDNET’s latest analysis warns that the global AI agent population, now at 28.6 million, could exceed 2.2 billion by 2030, creating a governance nightmare for enterprises. The outlet urges firms to treat agent management platforms as a core HR‑technology, likening them to...

Hackers Exploit cPanel/WHM Flaw, Threatening Over 550,000 Servers
Hackers are actively exploiting a critical cPanel/WHM vulnerability (CVE‑2026‑41940) on over 550,000 servers, with roughly 2,000 sites confirmed compromised. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has placed the flaw on its Known Exploited Vulnerabilities list, urging immediate patching.

Trojan Abuses Microsoft Phone Link App to Steal Your Passwords
Researchers at Cisco Talos have identified CloudZ, a modular Remote Access Trojan that targets Microsoft Phone Link (formerly Your Phone) on Windows 10/11. The malware deploys a malicious "Pheno" plugin to monitor active Phone Link sessions and hijack its SQLite database,...

The Authentication Challenge
The blog highlights that while EMV 3DS 2.x is technically identical worldwide, authentication outcomes vary dramatically because issuers make strategic economic choices. In Australia, just 3% of card spend generates 51% of CNP fraud, illustrating the cross‑border cost disparity. Issuers...

Cyber-Physical Risk: A Growing Concern for South African Companies
South African firms are confronting a surge in cyber‑physical risk, where cyberattacks can damage equipment, halt production, and trigger costly business interruption. Global incidents of physical impairment rose 146% in 2024, and Africa’s cyber‑insurance market—valued at roughly US$283 million—remains under‑penetrated, leaving...

Microsoft, Google Push AI Agent Governance Into Enterprise IT Mainstream
Microsoft and Google have launched enterprise‑focused AI governance tools—Microsoft’s Agent 365, now generally available, and Google’s AI Control Center for Workspace. Both solutions let IT and security teams discover, monitor, and secure AI agents that operate across SaaS, cloud, and...

Manufacturers Overestimate Cyber Resilience, New Report Reveals
A new Beazley survey of 3,500 global executives shows cyber risk remains the top concern for retail and manufacturing leaders, with 32% naming it their number‑one security issue. Despite recent high‑profile attacks—Marks & Spencer and the Co‑op each losing hundreds of millions...
Traditional Recovery Approaches No Longer Enough
Traditional disaster‑recovery methods that rely on rolling back to the last‑known good snapshot are no longer sufficient against modern cyber attacks, according to Cohesity’s VP of Cyber Resiliency Strategy, James Blake. Attackers can remain undetected for months, meaning restored data...
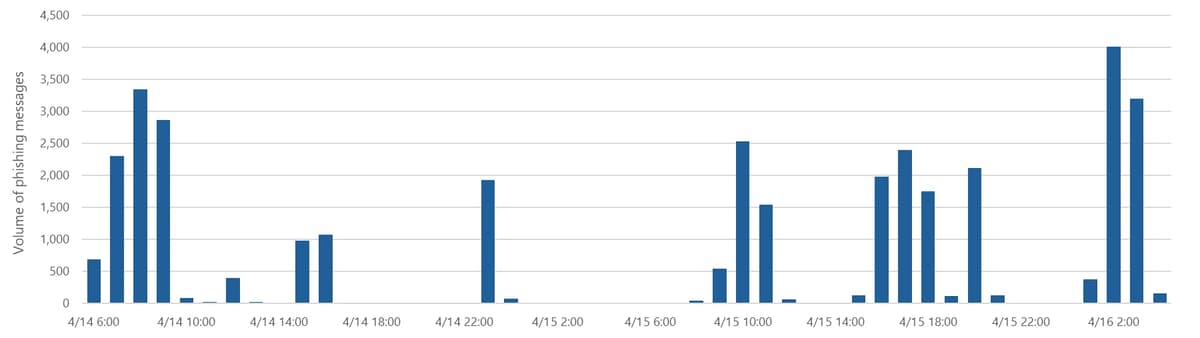
Microsoft Warns of Global Campaign Stealing Auth Tokens From 35K Users
Microsoft disclosed a multi‑stage phishing campaign that compromised authentication tokens for more than 35,000 users in 26 countries, with 92% of victims located in the United States, especially in healthcare and finance. The attackers sent polished “code‑of‑conduct” emails through a...

A Rigged Game: ScarCruft Compromises Gaming Platform in a Supply-Chain Attack
ESET researchers uncovered a multi‑platform supply‑chain attack by the North Korea‑aligned APT group ScarCruft against a Yanbian‑focused video‑game platform. The group compromised the Windows client through a malicious update, installing the RokRAT downloader that delivered the sophisticated BirdCall backdoor. An...

Your Biggest Cyber Threat Is Now Sitting at the Desk Next to You
South Africa’s insider cyber risk jumped 46% in 2026, outpacing the 44% global average, and 63% of local firms expect data losses to keep rising. Economic stress, high unemployment and frequent restructurings are driving employees to view data as personal...

Kaspersky to Highlight Local Cyber Security Pain Points, Potential Solutions
Kaspersky will speak at the ITWeb Security Summit 2026 in Cape Town on May 26, focusing on the cyber‑security challenges facing South African and broader sub‑Saharan organisations. Senior researcher Omar Amin will outline global and regional threat trends, while GM...
Precision Container Security with Docker and Black Duck
Black Duck has launched an integration with Docker Hardened Images (DHI) that leverages Docker’s VEX statements and Black Duck’s binary analysis to automatically distinguish harmless base‑layer vulnerabilities from real application risks. The solution provides zero‑config detection of DHI, precision triage...

Welcome to National Small Business Week 2026
During National Small Business Week 2026, the Federal Trade Commission (FTC) is spotlighting fraud prevention and cybersecurity for small enterprises. The agency is offering a series of free virtual events, including a two‑day summit (May 5‑6), a cybersecurity team‑building webinar, a...

US DOJ: Member of Prolific Russian Ransomware Group Sentenced to Prison
A Latvian national, Deniss Zolotarjovs, was sentenced to 102 months in federal prison for his role in a Russian ransomware syndicate that targeted more than 54 companies between 2021 and 2023. The group, linked to former Conti operators, extorted over...

AI in Cybersecurity Moves From Promise to Proof as WEF and KPMG Track Defender Gains
The World Economic Forum and KPMG released the white paper “Empowering Defenders: AI for Cybersecurity,” showing AI reduces average breach costs by $1.9 million and shortens breach lifecycles by roughly 80 days across 20 partner case studies. The report, built on input...

Digitalisation Increases Risk. Companies Are Not Ready
The rapid digitalisation of manufacturing, amplified by AI, is turning production lines into cyber‑dependent systems, raising the stakes of cyber incidents beyond IT outages. Companies across the electronics sector remain largely unprepared, with human error still the leading breach vector...
OWASP Foundation Unveils Its Strategic Plan for a World Without Insecure Software
The OWASP Foundation unveiled a new strategic plan that charts a five‑point roadmap to eradicate insecure software at scale. The document shifts OWASP from a respected security voice to a transformative industry force, emphasizing community collaboration, education, and open‑source innovation....

Ripple to Share North Korean Threat Intelligence with Crypto Firms
Ripple announced it will feed Crypto ISAC with internal threat intelligence on North Korean hackers after the April Drift breach, which siphoned $285 million through long‑term social engineering. The breach highlighted a shift from smart‑contract exploits to people‑centric attacks, where operatives...

Major Shift in Chinese Cyber Attack Activity
The UK’s National Cyber Security Centre, together with partners in ten countries, warned that China‑linked cyber actors are increasingly using large botnets of compromised SOHO routers, IoT and other smart devices to mask attacks. Groups such as Volt Typhoon, Flax Typhoon and...

Bug Bounty Pros Question $22K Split ROI Amid AI Rise
I wonder how top bug bounty hunters feel about a $22K cash prize split between a bunch of people. I like the idea about rewarding defenders and programmers for work on AI but the ROI doesn’t seem to be there...
Up to 28,000 Employees Affected by Paper-Based Data Breaches
An analysis by Officeology revealed that paper‑based record mishandling led to 1,820 non‑cyber data breaches in 2025, affecting up to 28,000 employees. Nearly one‑fifth of the 11,000 breaches reported to the UK ICO between 2020‑2025 involved employee information, with basic...

Good News for South Africans Who Use Fidelity ADT Security
Fidelity ADT confirmed that its South African operations and customer data were untouched by the ADT breach disclosed in April 2026. The breach, claimed by the ShinyHunters extortion group, stemmed from a voice‑phishing attack that compromised an employee’s Okta SSO account...

Sektor Secures Semperis Distie Deal for A/NZ
Sektor has signed a distribution agreement with identity‑security specialist Semperis to bring its cyber‑resilience and crisis‑response solutions to Australia and New Zealand. The partnership lets Sektor sell Semperis’ tools for protecting Active Directory, identity providers and other critical identity systems through...

CVE-2026-31431: Copy Fail Vs. Rootless Containers
The article dissects CVE‑2026‑31431, a kernel privilege‑escalation bug dubbed “Copy Fail,” which corrupts the page‑cache of /usr/bin/su to execute a tiny ELF payload that calls setuid(0) and execve("/bin/sh"). The author reproduces the exploit on a vulnerable Fedora 43 VM (kernel 6.17.1)...

Radiant Mobile Launches First U.S. Carrier‑Level Filtered Christian 5G Network
Radiant Mobile began offering a Christian‑focused 5G plan on May 5, 2026, charging $29.99 a month for unlimited talk, text and data while permanently blocking pornography and gender‑related material at the network level. The service runs on T‑Mobile’s 5G infrastructure and uses...

CISA and Allies Publish First‑Ever Agentic AI Security Guidance for Critical Infrastructure
The U.S. Cybersecurity and Infrastructure Security Agency, together with the Australian Cyber Security Centre and other allies, issued a new guidance document on Friday outlining concrete security controls for the deployment of agentic AI in critical infrastructure. The guidance warns...

Singapore Boffins Get Diverse SIEMs Singing in Harmony with Agentic Rule Translation
Researchers from the National University of Singapore and Fudan University unveiled ARuleCon, an agentic retrieval‑augmented generation framework that translates security rules across five major SIEM platforms. The system pulls vendor documentation to resolve schema mismatches and runs Python‑based consistency checks...

Singapore Boffins Get Diverse SIEMs Singing in Harmony with Agentic Rule Translation
Researchers from the National University of Singapore and Fudan University unveiled ARuleCon, a technique that automatically translates security detection rules across major SIEM platforms. By leveraging an agentic Retrieval‑Augmented Generation pipeline and a Python‑based consistency checker, the system maps vendor‑specific...

Open‑source Models Behind Firewalls Could End Corporate Opacity
I actually think that some things you want to keep illegible *from other organizations* but IMO there is an opportunity to do this behind a firewall with open source models. To selectively send context out only when needed. I'd...

Protect Student Data: Practical Tips for Schools
🚨 Take action this #WorldPasswordDay to protect your students as they navigate digital spaces 🎙️Jump into this informative conversation to explore practical tips for schools & districts to safeguard student data. https://t.co/SkQFRzN8q8 @roxi_thompson

Letter 111: I'm Pulling All My Money Out of DeFi
April 2026 became the most hacked month in crypto history, with over 40 exploits stealing roughly $651 million. Two attacks—Drift Protocol’s $285 million loss and KelpDAO’s $292 million breach—accounted for most of the damage and highlighted social‑engineering and bridge‑configuration flaws. At the same...

AI Will Redefine Cybersecurity Landscape
A glimpse into cyber-security’s #AI-driven future by @TheEconomist Learn more: https://t.co/NHIDasPYPw #CyberSecurity #Infosec #IT #Tech https://t.co/jB2cd6iA7u

Widows Targeted by Fraudulent Life‑Insurance Calls; Data Brokers Urged to Tighten Opt‑Outs
Consumer advocates are pressing data‑broker firms to improve opt‑out mechanisms after a wave of life‑insurance scams preyed on grieving widows. Research shows 52.5% of crimes reported by Americans over 60 in 2023 were enabled by personal data online, highlighting a...

Google Raises Android Bug Bounty to $1.5 M, Cuts Chrome Payouts Amid AI‑driven Shift
Google announced a sweeping overhaul of its Vulnerability Reward Programs, increasing the top Android payout to $1.5 million while reducing base rewards for Chrome bugs to $500. The changes reflect the company’s response to AI‑accelerated bug hunting and a new focus...

When AI Finds the Bugs: Why Defense in Depth Was Always the Answer
Mozilla partnered with Anthropic to run AI models against Firefox, uncovering 22 critical bugs in one release and a staggering 271 vulnerabilities in a follow‑up scan. The AI identified the same classes of flaws that elite human researchers find, but...

Stop the PCI DSS 4.0 Audit Toil: A Guide to Inherited Controls
PCI DSS 4.0, now mandatory for all payment‑data handlers, moves audits from point‑in‑time checks to continuous, automated evidence. Fintechs that build on raw cloud primitives spend months gathering OS‑hardening, patch‑management and network‑segmentation documentation, a burden known as audit toil. Upsun’s platform...

$3.425 Billion. One Year. A Wake-Up Call for Every Business Operating in the United States.
Gartner reports U.S. states imposed $3.425 billion in privacy‑related fines in 2025, eclipsing the total of the previous five years. Enforcement has shifted from guidance to hefty penalties, with California alone fining Disney $2.75 million for opt‑out violations. Twenty‑two states already have...

AI-Fueled Fraud Creates New Cybercrime Frontier for Risk Managers
At the Riskworld conference, The Hartford’s cyber‑risk leader warned that AI is reshaping fraud, with deepfakes, business email compromise and payment‑transfer scams now eclipsing traditional ransomware. Threat actors use AI‑generated voices and videos to impersonate executives, while automated social‑engineering tools...

Weaver E-Cology Critical Bug Exploited in Attacks Since March
Researchers at Vega uncovered that a critical unauthenticated remote‑code‑execution flaw (CVE‑2026‑22679) in Weaver E‑cology 10.0 was actively exploited from mid‑March. The vulnerability stems from an exposed debug API that lets attackers execute system commands without authentication. Exploits began five days...

Complaints Process Failing
The Office of the Australian Information Commissioner (OIAC) launched a privacy‑awareness campaign during Privacy Awareness Week to improve how agencies handle complaints. A new survey shows 93% of Australians consider data protection vital, yet 52% refrain from filing complaints because...

‘Copy Fail’ Is a Real Linux Security Crisis Wrapped in AI Slop
Researchers have identified a high‑severity Linux kernel flaw (CVE‑2026‑31431) that allows any authenticated local user to gain root privileges. The vulnerability, dubbed “Copy Fail,” affects mainstream kernels released since 2017 and was added to CISA’s exploited‑vulnerabilities catalog. Theori, the firm...

White House Officials Discuss Assessing AI Models That Pose Security Risks
The White House is weighing a cybersecurity‑focused executive order that would create a formal review process for artificial‑intelligence tools deemed high‑risk. Officials plan to establish an oversight group to draft standards for powerful models such as Anthropic’s Mythos, which has...

Kochava Won't Sell 'Sensitive' Location Data Without Consent
Data broker Kochava agreed to stop selling sensitive precise location data without explicit consumer consent, settling FTC privacy charges. The settlement defines sensitive data as GPS coordinates linked to medical, religious, educational, homeless, domestic‑violence, and law‑enforcement sites. Kochava does not...

Webinar to Explore AI Use in Cybersecurity, Health Care Technology
A joint webinar hosted by the American Hospital Association and the Joint Commission will explore how artificial intelligence can strengthen cybersecurity in health‑care settings. The event highlights the newly launched Cyber Resilience Readiness program, recent guidance from CISA and the...

AHA, Joint Commission Announce Cybersecurity Readiness Effort
The American Hospital Association and the Joint Commission unveiled the Cyber Resilience Readiness program, a voluntary initiative designed to help hospitals and health systems sustain safe, quality clinical operations during cyber‑related outages lasting 30 days or more. Unlike traditional IT‑focused...

RMM Tools Fuel Stealthy Phishing Campaign
Security firm Securonix has identified a stealthy phishing campaign, VENOMOUS#HELPER, that has compromised more than 80 organizations across the United States, Western Europe and Latin America since April 2025. The attackers bypass traditional malware by deploying two legitimate, signed remote...

NSW Downgrades Impact of Treasury Cyber Hit
New South Wales Treasury downgraded a previously labeled “significant cyber incident” after an alleged staff member attempted to exfiltrate over 5,600 sensitive documents. The downgrade was announced less than two weeks after the employee was formally charged. Treasury’s chief cyber...