Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, patched in June 2026; and Linux CVE‑2022‑0492, a kernel flaw also deemed actively exploited.
Also developing:
By the numbers: Ingeteam secures $82.5M loan from EIB for renewable energy R&D

Quantum eMotion Launches eShield-Q for Runtime Cryptographic Protection
Quantum eMotion Corp. unveiled eShield‑Q on May 4, 2026, a runtime cryptographic protection platform that secures encryption keys while they are in use. The solution combines quantum‑generated entropy, register‑based key storage, just‑in‑time decryption, and continuous integrity checks to guard against memory‑scraping and OS‑level breaches. It is OpenSSL‑compatible, allowing seamless integration into AI pipelines, identity services, and critical infrastructure without major code changes. eShield‑Q marks QeM’s shift from standalone entropy hardware to a full cloud‑to‑chip security suite.
US Healthcare Marketplaces Shared Citizenship and Race Data with Ad Tech Giants
An investigation by Bloomberg found that most of the 20 state‑run health insurance exchanges in the U.S. transmitted applicants' personal data—including citizenship, race, sex, and even information about incarcerated family members—to advertising platforms such as Google, Meta, LinkedIn, Snap, and...

Kaspersky Spots Rising Scam Activity Around the 2026 World Cup
Kaspersky has detected a sharp rise in World Cup‑related scams as the 2026 tournament approaches, including fake $500,000 grant emails and counterfeit merchandise ads. The malicious messages mimic official tournament resources, aiming to steal personal data and financial assets. Kaspersky’s...

EasyDMARC and KnowBe4 Partner to Advance Proactive Email Security as Phishing Fuels More Than One-Third of Cyberattacks
EasyDMARC and KnowBe4 announced a strategic partnership that blends domain protection with digital workforce security to curb phishing, spoofing and domain‑impersonation attacks. The deal makes EasyDMARC the exclusive DMARC service provider for KnowBe4’s customer base, embedding DMARC reporting, authentication gap...
Opaque Buys Post-Quantum Cryptographic AI Tech From Abu Dhabi’s TII
Opaque Systems Inc. announced the acquisition of advanced cryptographic AI technologies from Abu Dhabi’s Technology Innovation Institute. The deal adds multiparty computation, fully homomorphic encryption, and post‑quantum cryptographic safeguards to Opaque’s confidential AI platform, covering training, fine‑tuning, inference and agent...

Why Your Agentic AI Pentester Is Probably Just a Fancy Scanner
Ridge Security benchmarked three agentic AI pentesting platforms—RidgeGen, Shannon and Strix—against the OWASP Juice Shop. Using the same Gemini 3 Flash model, RidgeGen produced 55 fully verified findings with zero hallucinations, while Shannon generated 27 findings of which 63% were...

They Don’t Hack, They Borrow: How Fraudsters Target Credit Unions
Researchers at Flare uncovered a structured loan‑fraud playbook circulating on underground forums that targets small‑ to mid‑size credit unions. The method bypasses traditional security by using stolen personal data to pass knowledge‑based authentication and complete a full loan application, culminating...

AI Deepfakes Are Moving Into Commercial Real Estate Operations
Artificial intelligence‑generated deepfakes are amplifying business email compromise schemes, now targeting commercial real‑estate operations. The FBI attributes over $2.9 billion in losses to BEC, and AI voice cloning is making vendor invoices, escrow wires and vacancy transitions vulnerable. Fraudsters start with...
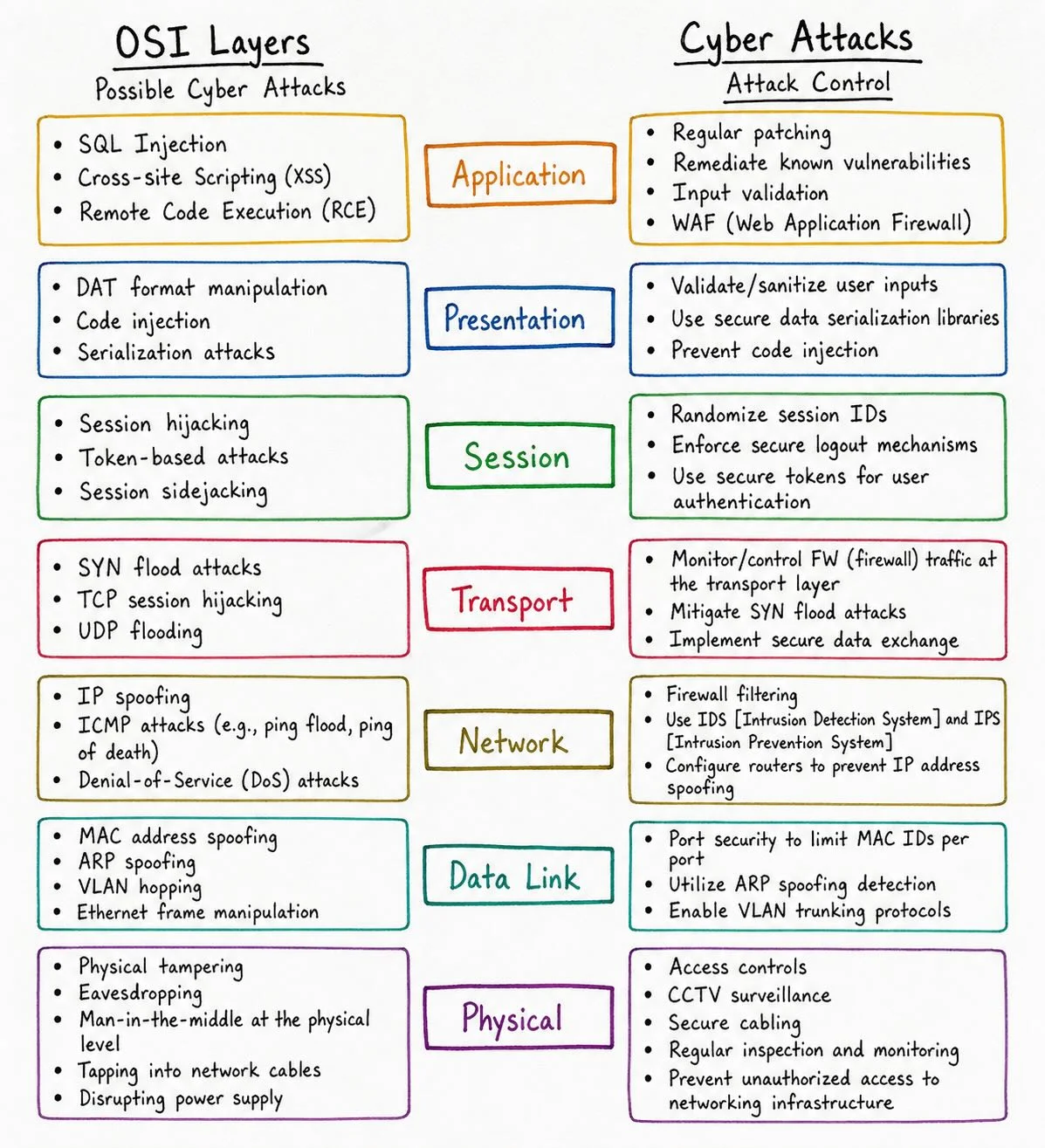
Layered Defense: Map OSI Attacks to Secure Each Layer
OSI Layers Explained (And How Hackers Attack Each One) 🔐 From Layer 1 to Layer 7 — every OSI layer has its own attack surface 👀 This breakdown shows how cyber threats map across the stack + how to defend each layer...

Unstructured Data Security Hindered by Visibility Gaps
RT One of the biggest security challenges with unstructured data is the lack of visibility and lineage as information moves across systems, clouds, and teams." #DataLineage #AI @Star_CIO https://t.co/PYomJYHDkY

Google Adds AI Features to Smart TVs, Sparking Privacy Backlash
Google rolled out AI-powered capabilities for smart TVs, extending its Photos app to Samsung displays and bringing Gemini‑driven YouTube summaries to the living‑room screen. Privacy advocates warn the move deepens data collection on devices that already sit in 77% of...

OpenAI Extends Yubico Key Security to Users
OpenAI has been using Yubico keys internally already – with its Advanced Account Security program, now its users can too. https://t.co/WtS61B6wfe

Air Force Names Dr. Keith Hardiman Deputy CIO, Cementing Leadership of IT and AI Programs
The Department of the Air Force announced that Dr. Keith Hardmann has been confirmed as the permanent Deputy Chief Information Officer for both the U.S. Air Force and U.S. Space Force. The appointment follows his acting tenure since July 2025 and...

Cisco Nerds Out: May the Fourth Be with Your AI Assistant
Cisco unveiled "Galaxy Mode" for its AI Assistant, a limited‑time Star Wars‑themed interface for Meraki and Thousand Eyes customers that runs through June 4. The release introduces Deep Reasoning, an AI‑driven analysis engine that interprets network events and offers security compliance...
U.S. Cyber Officials Mull 3‑Day Fix Deadline for Exploited Flaws Amid AI Threats
Acting CISA director Nick Andersen and National Cyber Director Sean Cairncross are weighing a proposal to cut the federal deadline for remediating known exploited vulnerabilities from two‑to‑three weeks down to three days. The move is driven by fears that advanced...

DigiCert Revokes Certificates After Support Portal Hack
DigiCert disclosed that a cyber‑attack on its support portal led to the fraudulent issuance of EV Code Signing certificates. The breach, traced to malicious payloads delivered via a chat channel on April 2, compromised two endpoints and allowed attackers to extract...

Mythos AI Is a Cybersecurity Threat, but It Doesn’t Rewrite the Rules of the Game
Anthropic unveiled Claude Mythos Preview, a large‑language model that autonomously discovers and exploits software vulnerabilities at unprecedented speed. In controlled tests, the model identified 271 flaws in Firefox and crafted exploits for 181 of them, and it uncovered thousands of...
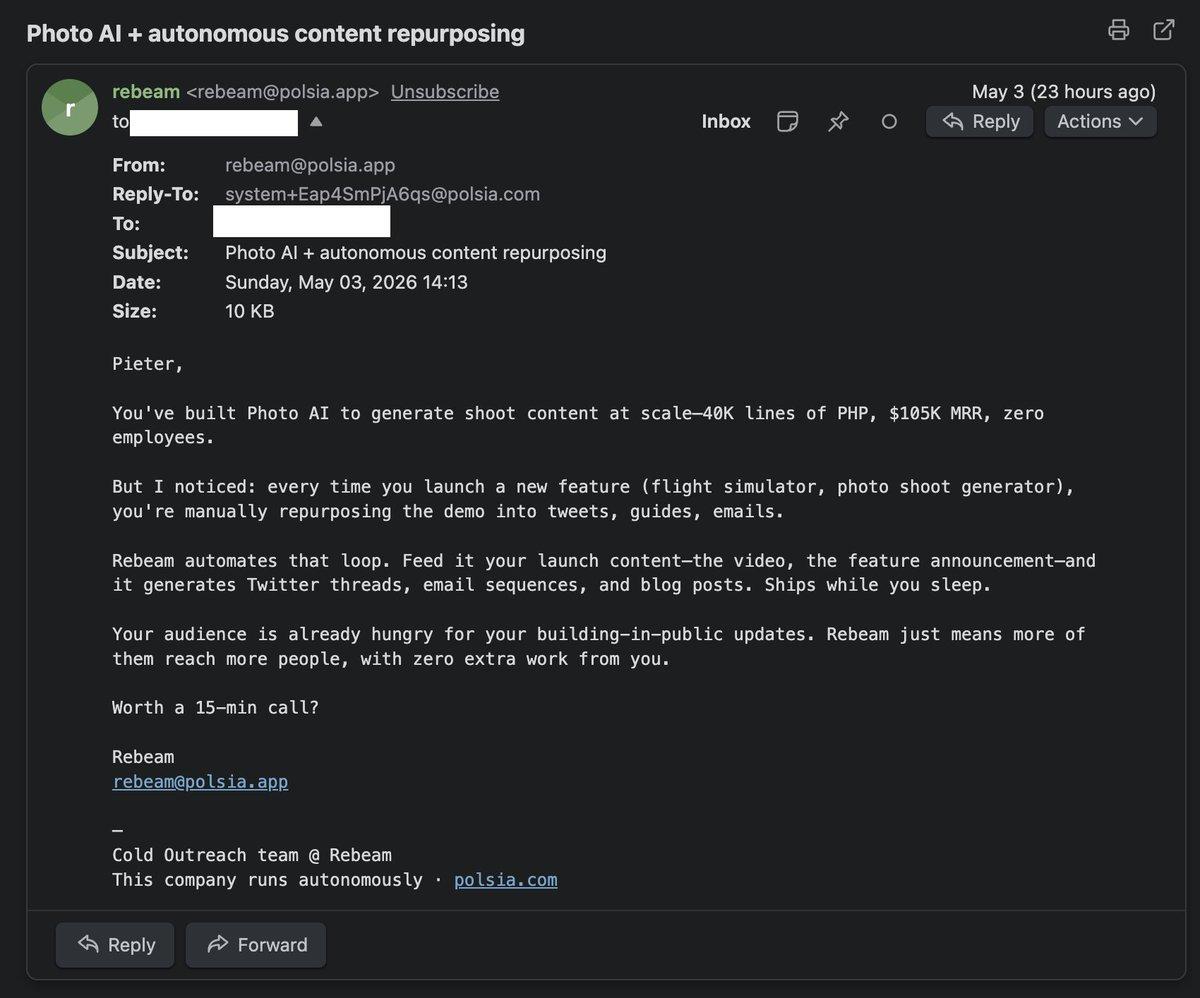
Polsia's Real Business: Sending Spam Emails
Got my first Polsia spam finally Now I finally understand what their business really is: sending spam emails (allegedly) https://t.co/Zfxt6pMWdp
Progress Warns of Critical MOVEit Automation Auth Bypass Flaw
Progress Software issued an urgent advisory about a critical authentication‑bypass flaw (CVE‑2026‑4670) in MOVEit Automation, affecting versions prior to 2025.1.5, 2025.0.9 and 2024.1.8. The vulnerability can be exploited remotely without credentials or user interaction, and a separate high‑severity privilege‑escalation bug...

Webinar: Why MSPs Must Rethink Security and Backup Strategies
Cyber attackers are leveraging generative AI to launch highly personalized phishing campaigns that outpace traditional email security, putting managed service providers (MSPs) at heightened risk. The breach often leads to data loss and downtime, exposing a gap where many MSPs...

Insiders Now Biggest Cybersecurity Threat, Attackers Aware
Company insides pose a bigger risk than ever to company cybersecurity, and attackers know this. https://t.co/RXNWVP4M0v

Small Defense Firms Lack Network Data to Stop Nation-State Hackers, Analyst Says
The U.S. defense industrial base’s small and mid‑size contractors, which make up about 80% of the sector, are severely lacking network telemetry to monitor edge infrastructure. Nation‑state actors such as China’s Volt, Russia’s Fancy Bear and Iran’s UNC1549 are exploiting zero‑day...

Previously Deported Nicaraguan National Receives 15-Year Sentence for $29 Million Bank Impersonation Scheme
A deported Nicaraguan national, Ernesto Ortega Padgett, received a 15‑year federal prison sentence after pleading guilty to a sophisticated bank‑impersonation scheme that stole more than $29 million from U.S. victims. The fraud, conducted from 2020 onward, used social‑engineering tactics, unauthorized wire transfers,...

Teenager Alleged to Be Scattered Spider Hacker Arrested in Finland, Faces US Extradition
The 19‑year‑old alleged Scattered Spider member known as “Bouquet” was arrested at Helsinki Airport and now faces U.S. extradition on wire fraud, conspiracy and computer intrusion charges. Prosecutors allege he participated in at least four attacks, including a 2025 breach...

AI Democratizes Phishing, Empowering More Attackers
Not only is AI helping attackers generate more sophisticated phishing attacks, but it's also democratizing tools to even more attackers. https://t.co/LWqNrqXAtd

CISA Lists Linux Kernel Flaw as Actively Exploited
U.S. CISA adds a flaw in Linux Kernel to its Known Exploited Vulnerabilities catalog https://t.co/hP6t8SVUqa #BreakingNews https://t.co/xKBTyF2jvn

Q&A: Why the Threat of Anthropic’s Mythos Demonstrates the Need for Sovereign AI
Anthropic unveiled Mythos, an early‑access AI model that can locate and exploit vulnerabilities across major operating systems and browsers. In a preview, Mozilla CTO reported 271 flaws—over ten times more than its predecessor. The program, Project Glasswing, currently grants access...

Cyber-Secure Philanthropy: Tech Infrastructure for Global Donations
Nonprofit donation platforms are increasingly targeted by ransomware, formjacking, and SQL‑injection attacks because many charities run outdated web forms and third‑party scripts without dedicated security staff. The article outlines how payment flows, API exposure, and weak compliance practices create exploitable...

Exploitation of ‘Copy Fail’ Linux Vulnerability Begins
A vulnerability dubbed Copy Fail (CVE‑2026‑31431) in the Linux kernel has moved from disclosure to active exploitation, giving attackers root‑level access. The flaw, present in kernels since 2017, lets an unprivileged user overwrite in‑memory data of setuid‑root binaries, enabling privilege escalation...

U.S. CISA Adds a Flaw in Linux Kernel to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added Linux kernel flaw CVE-2026-31431, dubbed “Copy Fail,” to its Known Exploited Vulnerabilities (KEV) catalog. The vulnerability scores 7.8 on the CVSS scale and enables an unprivileged local user to write...

Norton VPN Unveils First AI‑Native VPN for Autonomous Agents
Norton VPN has launched the industry’s first AI‑native VPN designed for autonomous agents, featuring multi‑tunnel technology and a zero‑installation Docker‑based architecture. The product, built with Gen Threat Labs and Gen AI Foundry, is now available to a limited set of...
Copy Fail Exploitation Has Begun, and Brian Pak Is Sorry for the Chaos
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has placed CVE‑2026‑31431, known as "Copy Fail," on its Known Exploited Vulnerabilities (KEV) catalog, confirming active attacks against Linux systems. The flaw, disclosed only days earlier, enables privilege escalation by exploiting a...

Housing Bank Rolls Out Open Banking Platform to Power Jordanian FinTechs
Housing Bank announced on May 3, 2026 the launch of an advanced open‑banking platform that gives fintechs and digital service providers secure API access to core banking functions. The move is designed to broaden financial inclusion in Jordan and align...

Citizen Lab Reveals Two Global Telecom Surveillance Campaigns Targeting High‑Profile Users
Citizen Lab disclosed two covert surveillance operations that leveraged SS7 and Diameter signaling to track a high‑profile mobile subscriber in November 2024 and a second target in early 2025. The campaigns spanned 3G and 4G networks in Israel, the United Kingdom and...

Why Data Centers Now Belong on the Critical Infrastructure List
Recent missile and drone attacks on cloud data centers in the Middle East highlighted a new strategic vulnerability: the physical disruption of digital infrastructure that underpins modern economies and militaries. As artificial intelligence workloads surge, data centers have become indispensable...

7 Key Features That Make Secure Browsers Safer
New research shows browsers are involved in 48% of cyberattacks, making them the most exploited vector in modern workplaces. Gartner predicts enterprise adoption of secure browsers will rise from 10% today to 28% by 2028, reflecting growing awareness of the...

Unified Identity Layer Key to Securing Agentic AI
Silverfort will headline the ITWeb Security Summit 2026 in Johannesburg, urging firms to replace fragmented point solutions with a unified identity security layer. The company highlights two pressures: outdated legacy infrastructure that was never fully secured, and the emergence of...
CIOs Internalize Data Destruction to Prevent Custody Crises
Avoiding a chain of custody crisis: why CIOs are bringing data destruction in-house https://t.co/bnmzu4xKEt https://t.co/qCCXJqtiVm

The Fake IT Worker Problem CISOs Can’t Ignore
Hiring fake IT workers has become a widespread insider‑risk threat, with thousands of synthetic identities infiltrating U.S. firms. Amazon alone blocked more than 1,800 North Korean attempts to secure IT roles, while SentinelOne has logged 360 fake personas and over...

Agentic Browsers Rewrite the Rules of Enterprise Security
Enterprise browsers are evolving from passive tools to autonomous agents, driven by rapid AI adoption. Deloitte reports 74% of organizations will deploy agentic AI within two years, while 84% of knowledge workers are eager to use it. These agentic browsers...

Post Quantum Migration Struggles, AI Threats, and Modern Defenses - Bobby Ford, HD Moore, Eyal Benishti, Ramin Farassat, Daniel Dos...
Post‑quantum cryptography (PQC) is moving from theory to implementation, but enterprises still struggle to locate and upgrade legacy servers, IoT and OT assets. AI‑generated deep‑fakes and multi‑channel impersonation are outpacing traditional point solutions, prompting calls for unified, behavior‑driven defenses. In...

Preparing for the 2026 HIPAA Changes: A Practical Guide for Healthcare Leaders
The Department of Health and Human Services will finalize a major overhaul of the HIPAA Security Rule in 2026, turning many previously optional safeguards into mandatory requirements. Organizations will face a tight compliance window—potentially as short as 60 days—once the...

How CISOs Should Utilize Data Security Posture Management to Inform Risk
Chief information security officers face a persistent dilemma: they know their data security posture must improve, yet budgets and headcount are limited. Data security posture management (DSPM) platforms can deliver visibility into where sensitive data resides, but full‑featured solutions often...

Avoiding a Chain of Custody Crisis: Why CIOs Are Bringing Data Destruction In-House
CIOs are re‑evaluating data disposal as the volume of retired hard drives, SSDs and backup media surges, exposing a hidden security gap. Traditional outsourced shredding creates multiple handoffs that weaken chain‑of‑custody control and increase breach risk. To meet stricter audit...

How OpenClaw’s Agent Skills Become an Attack Surface
OpenClaw’s AI agent offers deep integration with a user’s local machine, granting access to files, browsers, and long‑term memory, but it stores configuration and credentials in plain‑text files. This design lets attackers who compromise the host quickly exfiltrate API keys,...

OpenAI To Extend Cyber Program to Government Agencies
OpenAI released a roadmap titled "Cybersecurity in the Intelligence Age" outlining plans to broaden its Trusted Access for Cyber (TAC) program to federal, state and local government agencies, as well as key industry players. The expansion coincides with the launch...

Idiot Hackers Strike Again
Pro‑Iran hacktivist group 313 Team threatened Canonical, demanding payment to stop a DDoS campaign that crippled Ubuntu.com. The same day, the popular webcomic site questionablecontent.net was compromised, likely by an opportunistic script‑kiddie scan. Both incidents illustrate how politically motivated extortion...

Vocus and Fortinet Fighting Shadow AI with Secure Shield Launch
Australian telecom Vocus and cybersecurity firm Fortinet have launched Vocus Secure Shield, a managed SASE platform designed to expose and control shadow AI usage within enterprises. The service leverages Fortinet’s AI‑driven security and deep application awareness to detect AI tools,...

NTT Docomo Rolls Out New Measures to Prevent Spoofed Emails
NTT Docomo, Japan’s largest mobile operator, has deployed DMARC and BIMI across its email services to combat spoofed messages. The domain‑based authentication verifies that emails originate from authorized Docomo domains, while BIMI displays the company logo for verified senders. Emails...

KISA Partners with Hyundai and Kia to Strengthen Automotive Supply Chain
The Korea Internet & Security Agency (KISA) has entered a formal partnership with Hyundai Motor Company and Kia Corporation to embed cybersecurity across their multi‑tiered automotive supply chain. The agreement expands KISA’s protective framework beyond the OEMs to include component...