Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB

The FBI Is Now Tracking AI Scams, and the Losses Are Huge
The FBI’s Internet Crime Complaint Center has, for the first time, isolated artificial‑intelligence‑related fraud as a distinct category in its 2025 cybercrime report. Americans reported nearly $21 billion in total cybercrime losses, with AI‑linked scams accounting for about $893 million across more than 22,000 complaints. The data shows a 26 % jump in overall losses from 2024 and highlights Texas as the second‑most affected state. Scammers are leveraging voice‑cloning, deep‑fake media, and realistic messaging to make fraud harder to detect.
![Defense & Aerospace Daily Podcast [May 06, 2026] Justin Sherman on Cyber and AI Components of FY ’27 Budget...](https://hixhlmpcokxhartfkpyi.supabase.co/storage/v1/object/public/images/thumbnails/a84e42003a632a4fda8fdddeb823d048.webp)
Defense & Aerospace Daily Podcast [May 06, 2026] Justin Sherman on Cyber and AI Components of FY ’27 Budget...
Justin Sherman, founder of Global Cyber Strategies and senior fellow at the Atlantic Council, discussed the cyber and artificial‑intelligence components of the Trump administration’s FY ’27 defense budget on the Defense & Aerospace Daily Podcast. The budget proposes about $15 billion...

Phenom Secures FedRAMP‑Ready Status, Opening AI Recruiting to U.S. Federal Agencies
Phenom, the AI‑driven talent platform, announced on May 5, 2026 that it achieved FedRAMP® Ready status, the first recruiting solution cleared for U.S. government use. The certification lets federal agencies deploy Phenom’s AI hiring suite while meeting Moderate and Impact Level 4 security...

AlphaDrive Launches $100 M Fund Targeting AI‑driven Cyber‑security Startups
Veteran investors Yaron Elad, Elik Etzion and UBS veteran Gurinder Sidhu have launched AlphaDrive, a $100 million fund dedicated to AI‑enabled cybersecurity companies. Backed by anchor investor Leumi Partners and a slate of family offices and entrepreneurs, the fund aims to...
CISA Launches CI Fortify to Enable Weeks‑to‑months OT Isolation for Critical Infrastructure
The Cybersecurity and Infrastructure Security Agency (CISA) announced the CI Fortify initiative, urging owners of electricity, water, and transportation systems to develop plans that keep essential services running for weeks to months while disconnected from IT networks and third‑party vendors....

DeFi Protocol Kelp DAO Pivots to Chainlink CCIP for Stronger Cross-Chain Security
Kelp DAO announced it will replace LayerZero with Chainlink’s Cross‑Chain Interoperability Protocol (CCIP) as the backbone for its rsETH bridge. The move follows an April 18 exploit that drained about 116,500 rsETH, roughly $292 million, highlighting vulnerabilities in LayerZero’s messaging layer. CCIP’s...

OpenAI Violated Canadian Privacy Laws, Federal and Provincial Watchdogs Say
Four Canadian privacy commissioners concluded that OpenAI breached federal and provincial privacy statutes while gathering data to train early ChatGPT models. The agency said the company scraped personal and sensitive information from social media, blogs and news sites without obtaining...
Chrome Downloads a 4GB AI File without User Consent, Researcher Alleges
Google’s Chrome browser silently downloaded a 4 GB Gemini Nano model file to users’ machines without prompting. Researchers confirmed the weights.bin file appears after Chrome 148.0.7778.97 updates on macOS and Windows, and re‑downloads after deletion unless AI features are disabled via...
MSPs Get AI Workforce to Scale Managed Security
WatchGuard unveiled Rai, an agentic AI digital workforce for managed service providers that automates detection, investigation and response tasks. Positioned as a shift from assistive to autonomous AI, Rai operates continuously, taking pre‑authorized actions and logging them via the WatchGuard...

Majority of IT Leaders Struggle to Manage Growing Identity Footprint Amid AI Expansion
Keeper Security’s new Identity Security at Machine Speed Report shows 89% of IT leaders worldwide struggle to manage a rapidly expanding identity footprint, driven by the surge of non‑human identities and AI adoption. In the UK, 52% of senior IT...

Kubernetes Finally Lands User Namespace Support, but Shared Kernel Problem Remains
Kubernetes 1.36 introduces general‑availability user namespace support, allowing pods to remap root to an unprivileged host UID. This mitigates several high‑severity CVEs by limiting the impact of container escapes and lateral movement. However, all containers still share the same Linux...

AI‑generated Scripts Can Wipe Entire Servers—Snapshot First
Running models in production is scary stuff. I had a test instance I was running - a simple copy of training data to retrain, a script that I run to pull in new training data and build models off of....
The SECURE Data Act Is Not a Serious Piece of Privacy Legislation
The SECURE Data Act, drafted by House Republicans, offers only limited consumer rights and would preempt the 21 state privacy laws currently in effect. While it grants basic access, correction, deletion and portability, it lacks a private right of action...
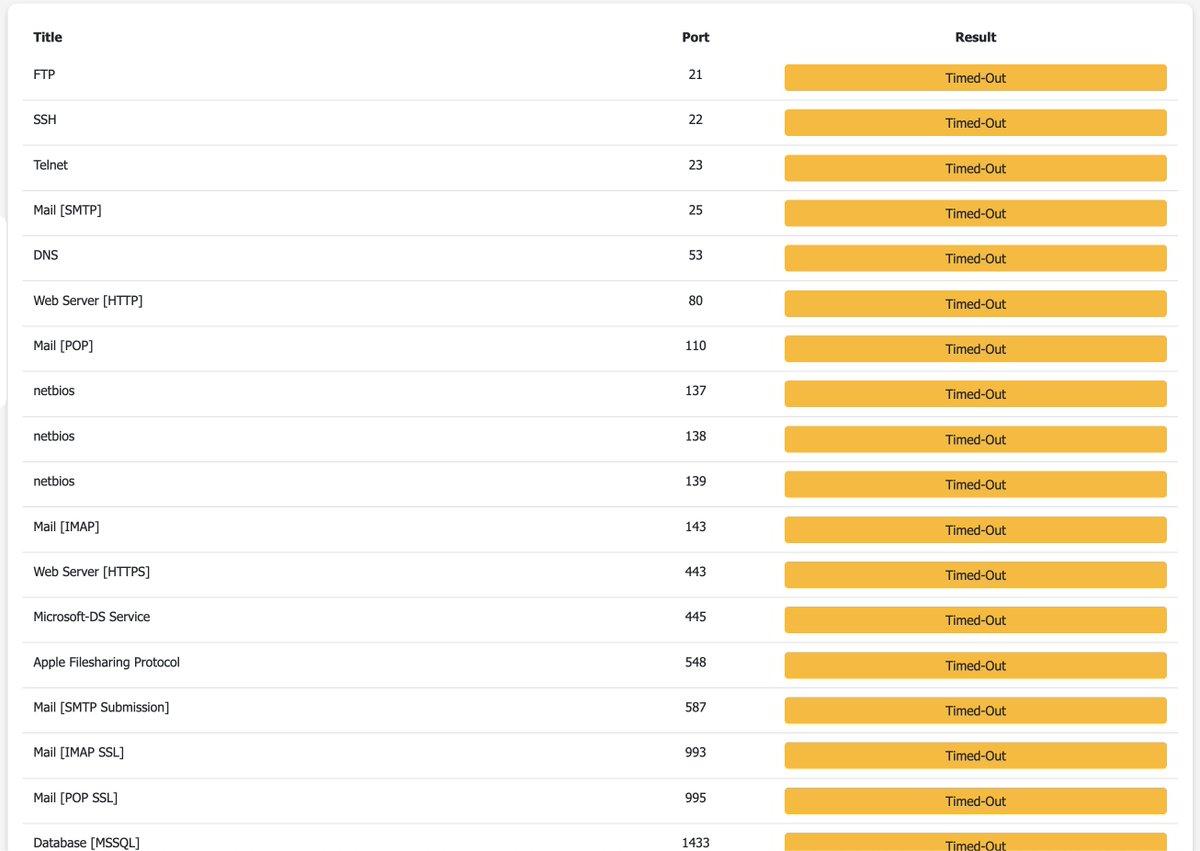
Lock Down Your VPS with Outbound Cloudflare Tunnel
New fun thing I did to secure my VPS even further I installed @Cloudflare Tunnel, many of you recommended me this I already had 443 inbound firewall limited to Cloudflare's IP range, but this is even better Cloudflare Tunnel is outbound, which means...

Charities Must Avoid Damaging Public Trust when Using Soft Opt-In, Regulator Warns
Britain’s Fundraising Regulator has released updated data‑privacy guidance to reflect the Data (Use and Access) Act 2025, which introduces a soft‑opt‑in provision allowing charities to send direct marketing without explicit consent. The regulator cautions that misuse of this power could...

Breaches in Cybersecurity Could Disrupt, Affect Patient Care: Tarun Sondhi
Accenture’s cybersecurity lead Tarun Sondhi warned that the growing reliance on electronic devices and interconnected vendor platforms is expanding the attack surface in health care. Breaches can cripple systems, delay access to patient records, and disrupt scheduling, directly affecting treatment...

Honeypots Resurface: LLM Attacks Trapped by Reverse Prompts
Honeypotting in cybersecurity will become a real thing again, especially because agentic/LLM powered attacks are so easily fooled by this and you can then alert on a breach extremely early. Just imagine a SUPER_SECRET_ADMIN_PASSWORD env var somewhere, that is reverse prompt...
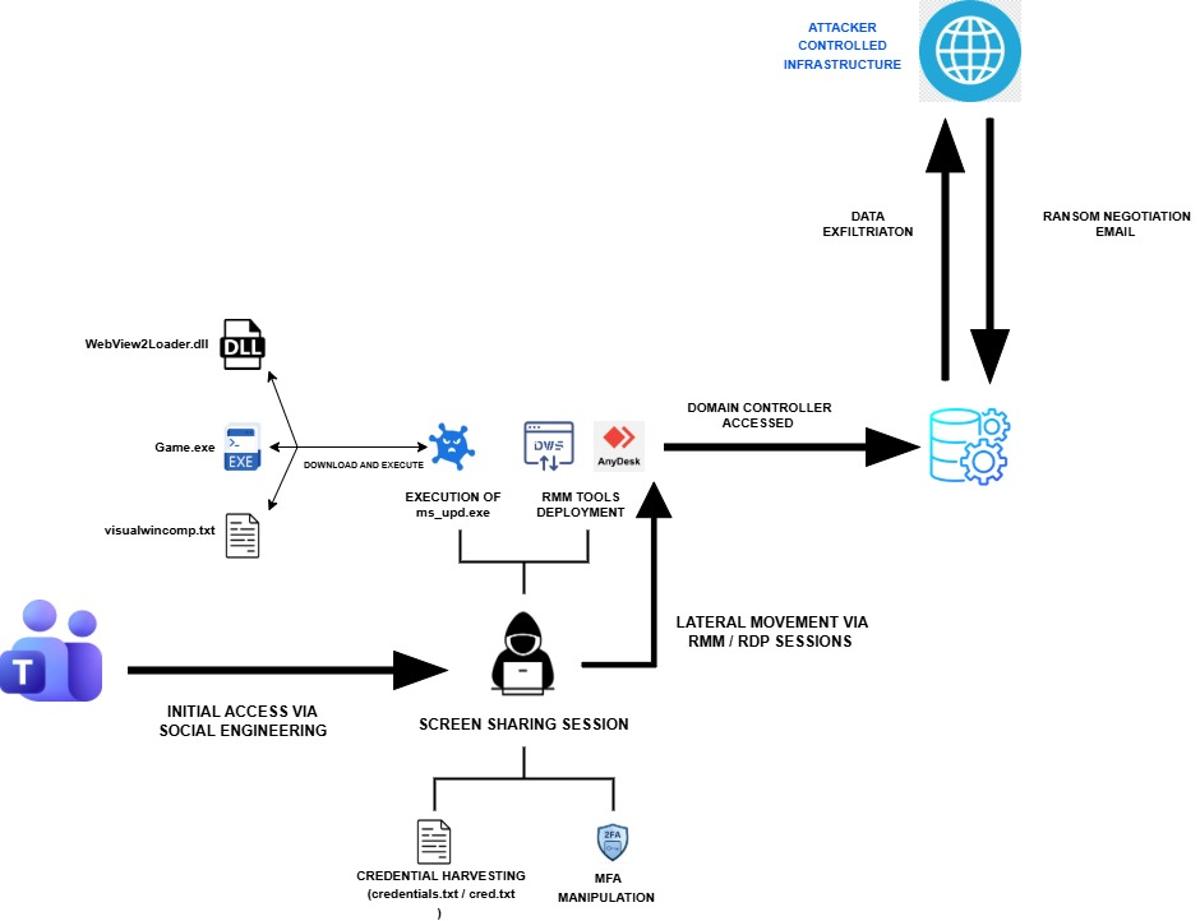
Iranian Cyber Espionage Disguised as a Chaos Ransomware Attack
Rapid7 uncovered an Iran‑linked MuddyWater intrusion that masqueraded as a Chaos ransomware attack, but no encryption occurred. The group used Microsoft Teams phishing, remote tools such as AnyDesk and DWAgent, and extortion emails to disguise a pure espionage operation. Credential...

Why Ransomware Attacks Succeed Even when Backups Exist
Ransomware attackers are now deliberately compromising backup systems, turning what should be a safety net into a single point of failure. The Acronis Cyberthreats Report shows a 50 % rise in attacks last year, exposing common weaknesses such as shared credentials,...

SecureIQLab Opens Post-Quantum Validation of Cloud-Native Firewalls
SecureIQLab released the first AMTSO‑registered validation methodology that tests cloud‑native firewalls against NIST post‑quantum cryptography (PQC) standards, including ML‑DSA, ML‑KEM and SHA‑384/512. The framework, Cloud Native Firewall CyberRisk Validation v1.0, evaluates up to 16 vendors across multi‑cloud, Kubernetes and serverless...

Some Kids Are Bypassing Age-Verification Checks with a Fake Mustache
Governments in the U.S. and U.K. are tightening age‑verification laws to keep minors off adult sites, forcing platforms to adopt document uploads or biometric checks. A survey by Internet Matters found half of 1,000 children could easily bypass these controls,...

CISA’s CI Fortify Rewrites the Disconnection Playbook for Critical Infrastructure
CISA unveiled CI Fortify on May 5, urging operators of the nation’s 16 critical‑infrastructure sectors to plan for weeks‑to‑months of isolation from vendors, telecom links, business networks and cloud platforms. The voluntary guidance emphasizes two capabilities—isolation and recovery—assuming adversaries have already penetrated...

What a Secure Harness for Agentic AI Actually Is
Enterprise teams are conflating terms like guardrails, gateways, and governance, leaving a critical gap in securing autonomous AI agents. A "secure harness" is defined as an engineered control layer that provides visibility, policy enforcement, and real‑time intervention across an agent’s...
Opsera and Cursor Team Up to Embed Autonomous AI Agents in DevOps Workflows
Opsera, the Agentic DevOps platform, and Cursor, a multi‑model AI coding tool, announced a partnership on May 5, 2026, to embed Opsera’s autonomous agents into Cursor’s IDE. The integration promises faster, compliant code generation by shifting security and governance checks...

The Digital Insurgency: Cyber Operations and the Future of Resistance
In the fourth episode of the SOF Professional Podcast, irregular‑warfare scholar Tom Johansmeyer examines how cyber operations intersect with reinsurance, parametric insurance and economic security. He argues that the true metric of a cyber catastrophe is the economic damage it...

U.S. Army CIO Leonel Garciga Departs After Pioneering AI‑Driven Digital Modernization
Leonel Garciga left his post as the U.S. Army chief information officer on May 1, concluding a ten‑month tenure that pushed AI into cyber, health and readiness operations. His exit, long‑anticipated by defense media, underscores a pivotal shift in how the...

Devicie Is Building Endpoint Security for an AI-Driven World
Devicie, an Australian‑origin startup, delivers a zero‑touch, AI‑enhanced endpoint security platform built on Microsoft Intune, automating patching, compliance and policy enforcement for laptops, tablets and phones. The solution addresses the fact that up to 90% of cyberattacks start at endpoints...
Linux ‘Copy Fail’ (CVE‑2026‑31431) Added to CISA KEV List Amid Active Exploitation
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) placed the Linux kernel flaw CVE‑2026‑31431, dubbed “Copy Fail,” on its Known Exploited Vulnerabilities (KEV) list after a working exploit went public. The bug, a nine‑year‑old local privilege‑escalation flaw, now threatens cloud,...

Huntress Adds Four Distributors, Including Ingram Micro, to Boost Mid‑market and Public‑sector Reach
Huntress announced four new distribution agreements—Ingram Micro, Vertosoft, Liquid PC and QBS Software—aimed at accelerating its mid‑market, public‑sector and EMEA expansion. The deals give the cyber‑security vendor deeper access to VARs, MSPs and resellers that serve schools, municipalities and medical...

MFA Misconfiguration Is the Costliest Point of Failure in Manufacturing Cyber Claims
Manufacturing has been the world’s most targeted industry for cyberattacks for five straight years, yet its security spending lags behind exposure. Resilience’s five‑year claims analysis shows ransomware accounts for 90% of losses while representing only 12% of claim volume. The...

MuddyWater Uses Microsoft Teams to Steal Credentials in False Flag Ransomware Attack
Iranian‑backed MuddyWater disguised a ransomware campaign as a Chaos RaaS attack, using Microsoft Teams screen‑sharing to steal credentials and bypass MFA. The group focused on data exfiltration and persistence via DWAgent and AnyDesk rather than encrypting files. A code‑signing certificate...

Iranian APT Intrusion Masquerades as Chaos Ransomware Attack
Iran‑linked APT MuddyWater staged a sophisticated intrusion in early 2026 that masqueraded as a Chaos ransomware attack. The group used Microsoft Teams screen‑sharing to harvest credentials, deployed remote‑access tools such as AnyDesk and its own DWAgent, and installed a custom...

Webinar: Why Network Incidents Escalate and How to Fix Response Gaps
On June 2, 2026 BleepingComputer will host a live webinar titled “From alert to containment: Fixing the gaps in network incident response,” featuring Edgar Ortiz of Tines. The session examines why incident response falters—particularly during triage, enrichment, and routing—and demonstrates how intelligent,...

Chinese Chamber of Commerce Puts a $432bn Price Tag on the EU’s Cybersecurity Overhaul
The China Chamber of Commerce in the EU commissioned KPMG to estimate the cost of the European Commission’s revised Cybersecurity Act, which would force the removal of Chinese suppliers from 18 critical sectors. The study puts the price tag at...
Hackers Compromise Daemon Tools in Global Supply-Chain Attack, Researchers Say
Researchers at Kaspersky discovered that hackers compromised the installer files for Daemon Tools Lite, a popular disk‑image mounting program, by injecting backdoors into versions 12.5.0.2421 through 12.5.0.2434. The malicious installers were distributed via the official website and reached users in...

UK High Court Dismisses Facial-Recognition Judicial Review Case
The UK High Court dismissed a judicial review brought by anti‑knife activist Shaun Thompson and privacy advocate Silkie Carlo, finding that the Metropolitan Police’s live facial‑recognition (LFR) policy contains sufficient legal constraints. The court rejected claims that the policy is...

Study Says AI Has yet to Transform Cybercrime
A peer‑reviewed study of over 100 million posts from underground cybercrime forums finds that artificial intelligence has not yet revolutionized illicit activity. While criminals experiment with tools like ChatGPT, AI mainly helps skilled actors hide malicious patterns and run automated harassment...

Secure Governance Turns AI Adoption Into Competitive Edge
AI adoption is accelerating. So are the cybersecurity risks behind it. Companies are integrating AI into CRM, sales, operations and customer experience faster than ever. But many organizations are still missing a critical point: ⚠️ AI without governance creates exposure. We’re seeing a rapid increase...

Worth Reading 050626
A RIPE Labs analysis reveals how five leading DDoS mitigation providers use BGP scrubbing, distinguishing always‑on from on‑demand defenses. An ACM opinion argues that AI is now a prerequisite for any meaningful privacy protection in today’s hyper‑complex data landscape. Researchers...

Trilio and Bigstack Announce Partnership to Deliver Advanced Data Protection in the Asia-Pacific Market
Trilio, a cloud‑native data protection provider, has partnered with Taiwanese cloud infrastructure firm Bigstack to embed its backup, recovery and workload mobility capabilities into Bigstack’s CubeCOS platform. The integration delivers a unified solution for private and hybrid cloud environments across...

From Stuxnet to ChatGPT: 20 News Events That Shaped Cyber
Dark Reading commemorates its 20th anniversary by cataloguing 20 pivotal cyber events—from the Stuxnet worm that shattered the myth of air‑gapped safety to the rise of AI‑driven threats like ChatGPT. The piece traces how early viruses evolved into nation‑state sabotage,...

I Gave Our Developers an AI Coding Assistant. The Security Team Nearly Mutinied
A technology leader approved an AI coding assistant to relieve developers from repetitive tasks, but the security team reacted strongly, fearing uncontrolled code generation. The tool can draft tests, explain legacy code, and suggest refactors, yet it raises questions about...
Romanian Man Extradited to US for Role in Hacking Scheme 17 Years Ago
Romanian national Gavril Sandu was extradited to the United States after being arrested in Romania in January 2026. Sandu faces charges for a 2009‑2010 vishing scheme that compromised small‑business VoIP systems, stole payment‑card data and acted as a money mule. The...

New “Undefined Trust” Filter Flags Deceptive Gray‑zone Sites
We’ve introduced a new web filtering category “Sites with an undefined trust level”. Such sites sit in a gray zone – promoting fake services, luring folks to hidden subscriptions, or nudging users to hand over data through deceptive terms of...
71% AI Access, Only 16% Governance in Enterprises
The interesting part isn’t that AI identities exist in enterprise systems, but how little control orgs have over them. 71% say AI tools access core systems like Salesforce/SAP, yet only 16% govern access. Visibility lags reality. https://t.co/o4a4KghbfQ

Construction ‘Least Prepared’ Industry for Cyber Threats, Poll Finds
A Beazley survey of over 3,500 leaders finds construction firms are the least prepared for cyber threats, with only 74% confident in their defenses and 32% citing security as their top concern. AI‑driven phishing and a 410% YoY rise in...

Personal AI Agents Pose Trojan‑Horse Credential Risks
Personal AI agents are the "Trojan Horse" in your inbox. Users give them credentials without realizing they’re opening a door for unverified 3rd-party extensions. Is your governance ready? 🛡️ https://t.co/5poCN8at4u #CIO #AI #Cybersecurity #DataGovernance #TechTrends

US Firms Could Face Exclusion Under New EU Cyber Bill, Lead Lawmaker Says
The European Parliament is revising its Cybersecurity Act to address non‑technical risks from third‑country vendors, a move that could label U.S. technology firms as high‑risk suppliers. Lead negotiator Markéta Gregorová warned that American companies may face exclusion if they fail...

The Creation of the Credential Protection Register; More than 750,000 Fraudulent Verification Requests Blocked
Australia’s Albanese Government has launched the Credential Protection Register, a national database designed to stop identity‑theft fraud in digital government services. Since its rollout, the register has blocked more than 750,000 fraudulent verification requests, averaging 18,000 per month. An investment...

Build the Agentic SOC to Combat AI-Powered Attackers
Splunk, now a Cisco subsidiary, is urging firms to replace fragmented security tools with an AI‑powered SecOps platform that unifies SIEM, SOAR and UEBA. At the ITWeb Security Summit 2026 in Johannesburg, VP Ahmed El Saadi will detail how this integrated...