Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, patched in June 2026; and Linux CVE‑2022‑0492, a kernel flaw also deemed actively exploited.
Also developing:
By the numbers: Ingeteam secures $82.5M loan from EIB for renewable energy R&D

Google Leaks Details for Chromium Bug that Can Turn Browsers Into Bots
A long‑standing vulnerability in Chromium’s Service Worker and Background Fetch APIs allows malicious sites to keep a service worker alive indefinitely and run JavaScript across browser restarts. Reported three years ago by researcher Lyra Rebane, the flaw lets attackers hide background downloads, hijack browsers for DDoS attacks, run crypto miners, and conduct persistent tracking. Although UI glitches were patched in early 2023, the core persistence issue remains unaddressed in Chrome, Edge and other Chromium‑based browsers. The bug tracker entry was briefly public, archived, and then re‑privatized, leaving the details exposed online.

Archon Capital Buys $10.9M Stake in Cybersecurity SaaS Leader Tenable
Archon Capital Management disclosed a new $10.89 million investment in Tenable, acquiring 519,002 shares that represent roughly 5% of its 13F assets. The move comes as Tenable posts improving earnings and expands its AI‑powered security platform, despite a 21% share‑price decline...

Valid Certificates, Stolen Accounts: How Attackers Broke Npm's Last Trust Signal
On May 19, attackers compromised a maintainer account to issue valid Sigstore certificates, allowing 633 malicious npm package versions to pass provenance verification. A day earlier, the Nx Console VS Code extension was hijacked, generating roughly 6,000 auto‑updates in under 40...

Data Sanitization Challenges Are Increasing in the AI Era
Blancco’s 2026 State of Data Sanitization Report warns that rising privacy regulations and AI adoption are reshaping end‑of‑life data management. While 94% of firms say they are confident in their sanitization processes, 38% still suffered data leaks, often from redeployed...

A Russian Speaker and Jailbroken Gemini Went on a Hacking Spree and Emptied at Least One MAGA Victim's Crypto Wallets
A Russian‑speaking solo threat actor leveraged a jailbroken Google Gemini model to orchestrate a sophisticated crypto‑fraud and credential‑theft campaign targeting MAGA and QAnon supporters. Between September 2025 and May 2026 the actor, known as bandcampro, built a Telegram channel with...
Middle East Malicious Infrastructure Report Highlights Concentration of C2 Servers
A Hunt.io study uncovered more than 1,350 command‑and‑control (C2) servers operating in 14 Middle Eastern nations, with Saudi Telecom Company (STC) alone responsible for over 72% of the activity. The servers span 98 providers, and the report highlights Turkish Telecom’s...

Microsoft Issues Out‑of‑Band Patches for Actively Exploited Defender Zero‑Days (UnDefend, RedSun)
Microsoft rolled out out‑of‑band updates on May 21, 2026 to fix two Defender zero‑day vulnerabilities—CVE‑2026‑41091 and CVE‑2026‑45498—after confirming active exploitation. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added both flaws to its Known Exploited Vulnerabilities catalog and gave federal...

Even as AI Gets Better at Finding Digital Weak Spots, It Doesn’t Eliminate the Human Role in Cyber Conflict
Anthropic’s new AI model Mythos highlights how generative tools can scan code for zero‑day flaws faster than human analysts. Justin Miller, a cyber‑security professor at the University of Tulsa, argues that AI is a capability multiplier that speeds both attack...
Zero‑Day Threats Exist—Update Windows to Stay Safe
“Zero day exploit” sounds like a bad Hollywood techno-thriller, but it’s a very real security risk for Windows PCs. Here’s what it means, why software updates matter so much, and the easiest ways to stay safer online: https://t.co/fXA8h2VcJV #CyberSecurity #Windows...

Drupal Vulnerability in Hacker Crosshairs Shortly After Disclosure
Drupal warned that attackers are already probing the newly disclosed CVE‑2026‑9082, a highly critical SQL‑injection flaw in its database‑sanitization API. The vulnerability, which affects only PostgreSQL‑backed sites, was patched on May 20 but has triggered more than 15,000 exploitation attempts across...

Transcript: America’s Cybersecurity Crisis Starts With Software (W/Jen Easterly)
Jen Easterly, former CISA director, argues that America’s cyber crisis stems from poor software quality rather than a pure security problem. Decades of market incentives have pushed vendors to prioritize speed and features over secure code, creating a massive market...

NGINX Zero-Day 'Nginx-Poolslip' Threatens Hundreds of Millions of Servers
Nebula Security’s autonomous agent Vega disclosed a zero‑day remote‑code‑execution flaw, dubbed nginx‑poolslip, in NGINX 1.31.0. The exploit bypasses Address Space Layout Randomization, leaving an estimated hundreds of millions of web servers vulnerable until an upstream patch arrives.

#245: Trust Under Pressure
The post warns that AI‑driven deepfakes and synthetic media are reshaping cyber‑threats, enabling attackers to craft hyper‑real phishing, voice, and video scams at scale. High‑profile incidents, such as a $25 million fraud in Hong Kong, illustrate the financial danger. In response, organisations...

Butter Bridge V3.1 Exploit Mints 1 Quadrillion MAPO Tokens, Triggers $180K ETH Dump
ButterNetwork confirmed that its MAP Bridge V3.1 on Ethereum and BNB Chain was exploited, allowing an attacker to mint nearly 1 quadrillion MAPO tokens. The attacker sold about 1 billion MAPO for roughly 52.21 ETH ($180K), while the bulk of the tokens remain...

Iran-Linked Hackers Target Key US, Allied Sectors with Sophisticated Spear-Phishing Messages
Iran‑backed hacking group Screening Serpens has launched a wave of spear‑phishing campaigns using six newly identified remote‑access trojans. The attacks focus on high‑value U.S. and Middle Eastern sectors, especially aerospace, defense and telecommunications, and employ highly personalized lures such as...
Christophe Pettus: Pgvector 0.8.2 and the Trouble With Parallel HNSW
pgvector 0.8.2 has been released to fix CVE‑2026‑3172, a heap buffer overflow that occurs during parallel HNSW index builds. The bug can leak data from other relations or crash the PostgreSQL backend. Many managed PostgreSQL services still run older pgvector...
Why CISA Accepting KEV Nominations Is So Important
The Cybersecurity & Infrastructure Security Agency (CISA) announced a new public nomination form for its Known Exploited Vulnerabilities (KEV) catalog, allowing vendors, researchers, and partners to submit exploitation data directly. The structured form replaces a simple email address, requiring CVE...

$20 per Zero-Day Is Already the WordPress Plugin Reality
Researchers from TrendAI and CHT Security demonstrated an AI‑driven pipeline that identified more than 300 critical zero‑day flaws across WordPress plugins in just 72 hours. The system combined static analysis, Docker provisioning, and Chrome DevTools verification, and each finding was...

5,561 GitHub Repositories Hit by Megalodon Supply Chain Attack in Six Hours
Cybersecurity firm SafeDep uncovered a rapid supply‑chain attack dubbed Megalodon that compromised 5,561 GitHub repositories within six hours on 18 May 2026, injecting 5,718 malicious code updates. The attackers created fake accounts and inserted hidden workflow files (.github/workflows/ci.yml) that act as dormant...

Most Data Breaches Start with a Stolen Password. Here’s How to Fix That
Data breaches still begin with stolen passwords, accounting for roughly 80% of web‑application incidents, according to Verizon’s 2024 report. The root cause is employee password reuse and insecure credential sharing, which traditional policies fail to stop. Proton Pass for Business...

Object First Surges in Q1 2026 as Immutability Becomes a Security Requirement for Backup
Object First reported a 118% year‑over‑year increase in Q1 2026 bookings, driven by surging demand for immutable, ransomware‑proof backup storage. Growth was strongest in EMEA, where bookings jumped 275% YoY, while the Americas saw a 45% rise. Six‑figure deals doubled, reflecting...
N-Able Accelerates Recovery Time After Critical Events with Disaster Recovery as a Service
N‑able Inc. has launched Cove Disaster Recovery as a Service (DRaaS), a co‑managed solution that mirrors production workloads in a secure cloud environment for instant failover. The offering eliminates the need for organizations to build and maintain their own disaster‑recovery...

Ubiquiti Patches Three Max Severity UniFi OS Vulnerabilities
Ubiquiti released security updates on May 22, 2026 that address three maximum‑severity vulnerabilities in UniFi OS, including improper access control, path traversal, and command injection. The patches also cover a critical command‑injection flaw (CVE‑2026‑33000) and a high‑severity information‑disclosure issue (CVE‑2026‑34911)....

Megalodon GitHub Attack Targets 5,561 Repos with Malicious CI/CD Workflows
Cybersecurity firm SafeDep uncovered the Megalodon campaign, which injected malicious GitHub Actions workflows into 5,561 repositories, pushing 5,718 commits within a six‑hour window on May 18, 2026. The workflows contain base64‑encoded bash payloads that harvest CI environment variables, cloud credentials (AWS, GCP,...

The Cyber Express Weekly Roundup: Supply Chain Breaches, AI Content Enforcement, And Event Disruption Attacks
The Cyber Express weekly roundup highlights a surge in distributed cyber threats, from a massive npm supply‑chain breach that compromised over 300 AntV packages to an attempted disruption of Vienna’s Eurovision event where nearly 500 attacks were blocked. The U.S....

Fake Gemini and Claude Code Sites Spread Infostealers Through SEO Poisoning
Security researchers at EclecticIQ uncovered a coordinated campaign that masquerades as Google Gemini’s CLI and Anthropic’s Claude Code installation pages. By leveraging SEO‑poisoning, the fake domains rank above legitimate results, directing developers to PowerShell‑based installers that deploy an in‑memory infostealer....

Shaun Thomas: Why Postgres Lacks Transparent Data Encryption
PostgreSQL remains the only major relational database without built‑in Transparent Data Encryption (TDE), even as Oracle, SQL Server, MySQL and MariaDB provide the feature. The open‑source community has wrestled for years with divergent threat models, engineering complexity, and the question...

Vulnerability Exploitation Overtakes Stolen Credentials in AI-Driven Cyberattacks
Verizon’s 19th Data Breach Investigations Report shows vulnerability exploitation now initiates 31% of cyber incidents, overtaking stolen credentials for the first time in two decades. Artificial intelligence is compressing the gap between vulnerability disclosure and active exploitation, shrinking response windows...

ITWeb TV: ‘Missing’ Basics Expose Cyber Vulnerabilities
South Africa is emerging as a prime target for global cyber attacks, with a Surfshark report estimating annual cyber‑crime losses of roughly R2.2 billion (about US$118 million). Ayanda Peta, chair of the Cloud Security Alliance South Africa, warned that a lack of...

Security Researcher: WordPress 7.0 Could Trigger Rush To Steal AI API Keys via @Sejournal, @Martinibuster
Security researcher Oliver Sild warns that WordPress 7.0 exposes AI API keys, sparking a potential rush by hackers to steal them. A bug in the AI integration setup form leaks keys via browser autofill, making credentials visible during screen sharing or...

America’s Cybersecurity Crisis Starts With Software (W/Jen Easterly)
Former CISA director Jen Easterly, now CEO of the RSA Conference, argues that America’s cybersecurity crisis stems primarily from insecure software rather than policy gaps. She explains how today’s development practices embed vulnerabilities that nation‑state actors and criminal groups readily...

Keepnet Contributes Voice and SMS Phishing Data to the 2026 Verizon DBIR
Keepnet’s voice and SMS phishing simulation data has been incorporated into Verizon’s 2026 Data Breach Investigations Report, marking the first DBIR edition to feature phone‑centric phishing at scale. The report records a median click rate of 2% for voice/SMS simulations...

Iranian State‑Linked Hackers Expand U.S. Critical Infrastructure Campaign
Iranian state‑affiliated groups, including the IRGC‑linked CyberAv3ngers, have broadened a digital assault on U.S. critical infrastructure, shifting to alternative communications like Starlink and deploying destructive wiper malware. Analysts warn the campaign exploits weakened U.S. cyber‑defense resources.

Why Your AI Strategy Stops Where the PLC Starts: Hard Lessons From the OT Frontlines
C‑level executives are racing to embed AI in operational‑technology security, but the effort stalls because critical telemetry never reaches the models. Legacy devices—often an unpatched Windows 7 laptop that alone talks to protection relays—create a massive visibility gap. AI trained on...

Microsoft 365 Users Targeted by New Phishing Threat that Bypasses MFA
The FBI has identified a new Phishing‑as‑a‑Service platform, Kali365, that targets Microsoft 365 access tokens and bypasses multi‑factor authentication. First seen in April 2026, the service is distributed via Telegram and provides AI‑generated lures, campaign templates, and OAuth token‑capture tools. By exploiting...

Microsoft Patches Actively Exploited Defender Vulnerabilities Affecting Enterprise Systems
Microsoft disclosed active exploitation of two Defender flaws—CVE-2026-41091, a high‑severity privilege‑escalation bug, and CVE-2026-45498, a lower‑severity denial‑of‑service issue. Both vulnerabilities were confirmed in the wild and have been patched in Defender Antimalware Platform versions 1.1.26040.8 and 4.18.26040.7. A third flaw,...

Identity as the Primary Attack Surface: What Modern Breaches Are Really Exploiting
Modern breaches increasingly exploit identity rather than network perimeters. As enterprises migrate to cloud, SaaS, and hybrid work, authentication becomes the gatekeeper for financial systems, data, and admin controls. Attackers now rely on credential stuffing, OAuth consent phishing, and adversary‑in‑the‑middle...

GitHub Employee Device Breach Exposes Thousands of Internal Repositories
GitHub disclosed that attackers compromised an employee’s device and exfiltrated roughly 3,800 private repositories through a malicious Visual Studio Code extension. The breach was contained quickly; the affected endpoint was isolated and all credentials were rotated. Cyber‑criminal group TeamPCP claimed responsibility and...
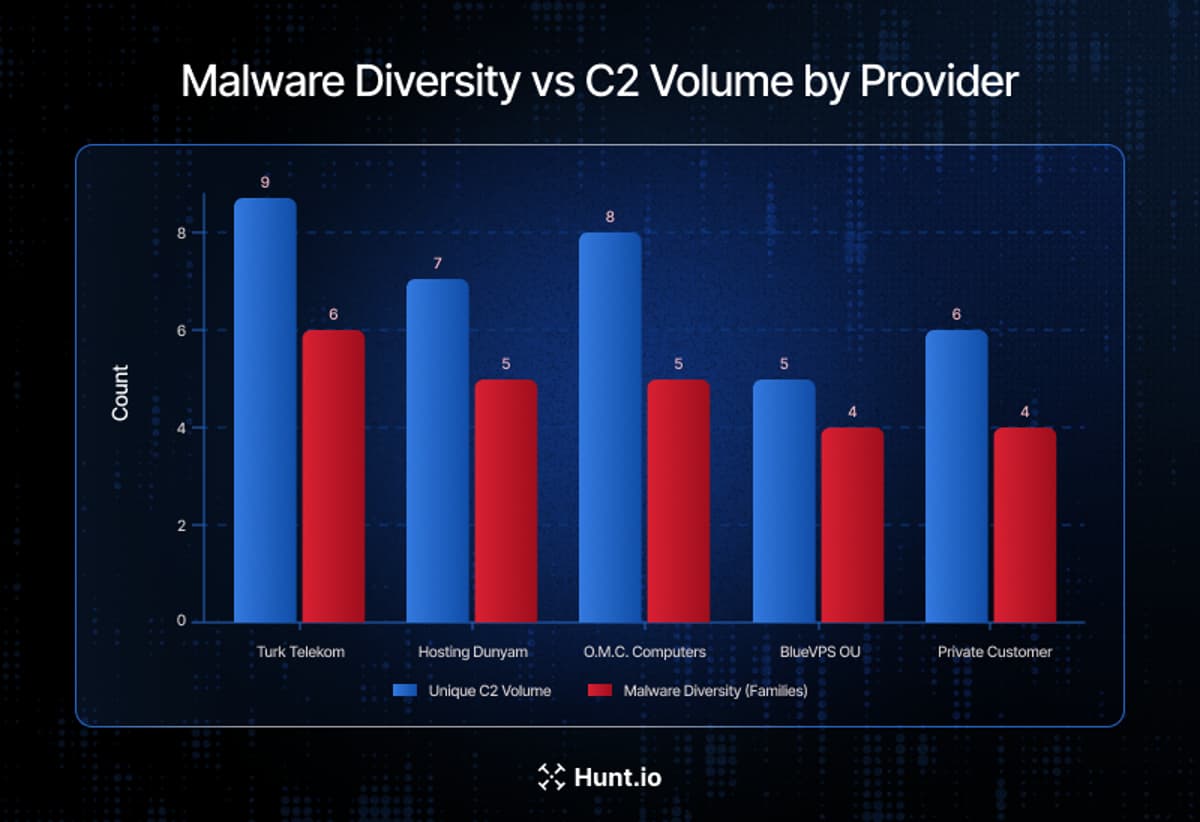
One Telecom Provider Hosted Most of the Middle East ’S Active C2 Infrastructure
Hunt.io’s three‑month survey of Middle East malicious infrastructure uncovered more than 1,350 command‑and‑control (C2) servers across 98 hosting providers in 14 countries. Saudi Telecom Company (STC) alone accounted for 981 servers, representing 72.4% of the region’s observed C2 activity. The...

EMEA Emerges as Global Hotspot for Financial Services DDoS Attacks
Akamai’s 2026 State of the Internet Security report reveals that financial services are now the most targeted sector for DDoS attacks, with median attack duration up 738% since 2024. The surge is driven by AI‑enabled botnets and hacktivist campaigns, especially...

China's Webworm Uses Discord, Microsoft Graphs to Hack EU Governments
China‑aligned APT group Webworm has pivoted from Asian targets to European government agencies, including Belgium, Italy, Serbia, Spain, Poland, and South Africa. In 2025 the group abandoned legacy malware for two novel backdoors—EchoCreep, which uses Discord, and GraphWorm, which exploits...

UK Cybersecurity Innovation SilentGlass Goes Global After Licensing Deal
The UK government has granted a global commercial licence for SilentGlass, a hardware‑based cyber‑security device originally created by the National Cyber Security Centre. The plug‑and‑play unit sits between a laptop and monitor to block video‑connection attacks, addressing a growing class...
MHCLG Launches CAF Support Fund
The Ministry of Housing, Communities and Local Government’s Local Digital team has unveiled a £6 million (about $7.7 million) Cyber Assessment Framework (CAF) Support Fund. The fund will provide grants to the 52 local councils that have completed a CAF self‑assessment, with...

Maritime Cyber Threats and AIS Assisted Collisions
Maritime cyber threats, especially GPS jamming and spoofing by U.S. and Russian militaries, are now routine, jeopardizing vessel navigation and prompting AIS‑assisted collisions. Insurers warn that even non‑malicious actions, such as a crew member’s phone malware, can cripple electronic chart...

Tenable Launches Hexa AI to Automate Remediation Across Attack Surfaces
Tenable announced the general availability of Hexa AI, an agentic AI engine that automates remediation across the entire attack surface. The platform ties advanced multi‑step reasoning to Tenable’s Exposure Data Fabric, promising machine‑speed risk reduction for CIO‑led security programs.

SANS Stormcast Friday, May 22nd, 2026: Selective HTTP Proxying; More GitHub Repo Trouble; MSFT Defender Patches;
In this episode, Johannes Ulrich discusses selective HTTP proxying techniques, highlighting Proxifier for macOS/Windows and Linux alternatives such as environment variables, iptables, and network namespaces. He then details a recent GitHub repository attack that leverages harvested credentials to inject malicious...

XRP Ledger Teams with Project Eleven to Guard Against Quantum Attacks
The XRP Ledger announced a partnership with post‑quantum security firm Project Eleven to audit its validator, wallet and custody layers and develop hybrid signature schemes. The move positions the blockchain to transition to quantum‑resistant cryptography before quantum computers become capable...

Sen. Rick Scott and Rep. Andy Ogles Push Stronger Defenses Against China-Backed Cyber Threats
Sen. Rick Scott and Rep. Andy Ogles called on Congress to fast‑track the Strengthening Cyber Resilience Against State‑Sponsored Threats Act, warning that Chinese groups like Volt Typhoon have already breached U.S. critical infrastructure. Their appeal underscores growing bipartisan concern over...

Coro Joins Leader’s Marketplace
Leader has added Coro’s AI‑driven cyber security platform to its Australian Cloud marketplace, giving MSPs and reseller partners a unified solution for endpoint, email, cloud, and network protection. The modular platform lets partners deploy only the capabilities their customers need,...

Beware of Financial Scammers Wielding Deepfake Tech
Deepfake-enabled fraud has shifted from a novelty to a persistent corporate risk, with synthetic audio and video remaining in circulation for an average of 3.5 years. A voice clone of a German energy‑company CEO persisted nearly six years, causing a...