Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, patched in June 2026; and Linux CVE‑2022‑0492, a kernel flaw also deemed actively exploited.
Also developing:
By the numbers: Ingeteam secures $82.5M loan from EIB for renewable energy R&D

Iranian Government, Not Hacktivist Group, Breached LA Metro System, Security Firm Says
Iranian government‑linked hackers, identified as the Black Shadow group, breached Los Angeles Metro’s computer infrastructure by accessing a virtual machine and deleting critical operating‑system files. The same actors carried out data‑wiping attacks on the South Florida Regional Transportation Authority, the connected‑vehicle firm Agnik, and a Saudi construction company involved in critical projects. Gambit Security traced the group’s tactics to the use of ChatGPT‑assisted Python scripts, and uncovered additional victims in Israel and Turkey where data was stolen but not erased. The campaign reflects a broader trend of state‑sponsored cyber aggression against Western critical infrastructure.

48‑Hour SLA vs 48‑Minute Threats: Rethink Vulnerability Response
How do you manage when your SLA is 48 hours to remediate a critical vulnerability but the bad guys are finding it in 48 minutes? Mythos and AI-driven attacks have changed the math. Most vulnerability management programs were built for a...

Telia and QMill Demonstrate a New Quantum-Enhanced Data Encryption Method for Mobile Networks
Telia and quantum‑security startup QMill unveiled a prototype that embeds quantum‑enhanced encryption directly into 5G mobile traffic. The demonstration used QMill’s Q‑Key distribution module to generate session keys that are mathematically resistant to future quantum attacks. Tests on a live‑network...

Four Big Takeaways From the FBI’s Report on Internet Crime
The FBI’s Internet Crime Complaint Center (IC3) released its 2025 report, highlighting a surge in AI‑driven scams with more than 22,000 complaints and $893 million in losses—the first time the agency has isolated AI‑related fraud. The data also show younger users...

BTMOB Android RAT Spreads Through No-Code Builder Tooling
Security firm ESET has identified BTMOB, an Android remote‑access trojan sold as a malware‑as‑a‑service kit that lets buyers create custom payloads without coding. The RAT spreads via phishing sites that mimic streaming services, crypto‑mining platforms, or tax agencies, and uses...

Detectify Brings AppSec Automation to AI Agents with MCP Server and Continuous Testing
Detectify has launched the Model Context Protocol (MCP) Server, an integration layer that embeds its application security testing engines into AI‑driven development pipelines. The platform lets autonomous coding agents retrieve real‑time vulnerability data, generate remediation patches, and trigger validation scans...

Security Roundup May 2026
Verizon’s 2026 Data Breach Investigations Report reveals that exploiting software vulnerabilities has become the leading cause of breaches, surpassing stolen credentials for the first time. The study of 31,000 incidents shows only 26% of CISA‑listed known‑exploited flaws were patched, a...

Krispy Kreme to Pay $1.6 Million to 161,000 Victims of 2024 Ransomware Breach
Krispy Kreme has agreed to a $1.6 million settlement for a November 2024 ransomware attack that exposed personal data of roughly 161,000 workers and customers. Eligible claimants can receive up to $3,500 for documented losses or a modest $75 payment, with...
Novee Debuts Agentic Fix, Pushing Pentest Findings Into Claude, Copilot and Cursor
Novee Cyber Security has launched Agentic Fix, a capability that pushes validated penetration‑test findings directly into AI coding assistants such as Claude, Copilot and Cursor. The tool generates remediation guidance from the exploit context, creates detailed GitHub issues and triggers...
AppOmni Launches Marlin AI to Automate SaaS Security Investigation and Remediation
AppOmni unveiled Marlin AI, an autonomous AI layer that automatically correlates, investigates, and guides remediation of SaaS security alerts. The capability runs continuously within the AppOmni platform, eliminating manual analyst steps and delivering plain‑language playbooks for remediation. By focusing exclusively...

Microsoft Defender Can Now Automatically Isolate Hacked Endpoints
Microsoft Defender for Endpoint is rolling out a preview feature that automatically isolates compromised Windows workstations. The isolated devices stay connected to the Defender service for continuous monitoring while being cut off from the corporate network. This capability builds on...
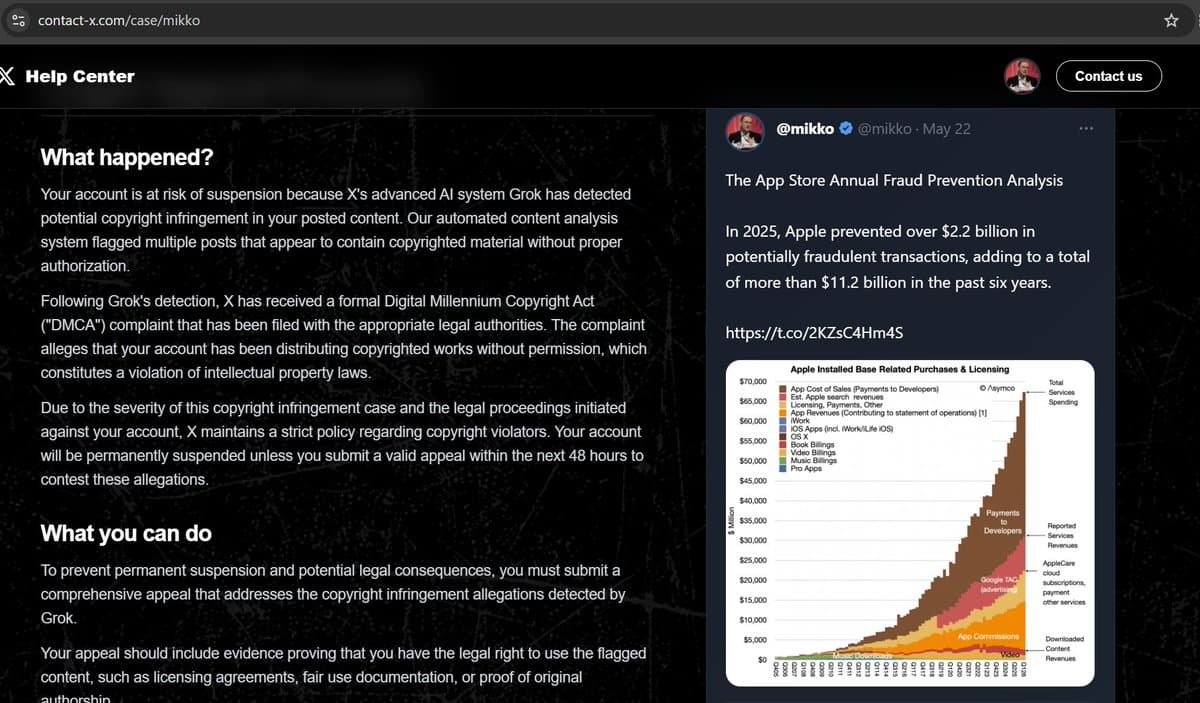
Beware: Fake AI Copyright Threat Emails Targeting Users
Scammers are sending emails pointing to "contact﹣x dot com", which hosts a fairly convinging site claiming that "Your account is at risk of suspension because X's advanced AI system Grok has detected potential copyright infringement in your posted content". Don't...

Angular Language Service Extension Flaws Allow Remote Code Execution
Multiple high‑severity flaws were uncovered in the Angular Language Service VS Code extension, allowing remote code execution through malicious JSDoc hover links and unsafe TypeScript SDK path configuration. The vulnerabilities affect all releases prior to version 21.2.4 and have been patched in...

US Eyes Physics-Based Engineering to Protect Water Systems From Cyber Attacks
The Government Accountability Office released a new report highlighting growing cyber exposure of U.S. drinking water and wastewater infrastructure. Convergence of operational technology with internet‑connected devices has expanded attackers’ reach since the GAO’s August 2024 assessment. Researchers urged adding physics‑based engineering...

TrapDoor Malware Campaign Puts Developer Workstations in CISO Spotlight
Researchers at Socket have identified a coordinated malware campaign, dubbed TrapDoor, that has published more than 34 malicious packages across npm, PyPI and Crates.io, affecting over 384 versions. The packages are engineered to harvest a wide range of developer secrets—including...

Tamnoon Introduces Skill-Based AI Orchestration for Autonomous Cloud Defense
Tamnoon has upgraded its AI engine, Tami, into a skill‑based orchestrator that creates custom remediation workflows for each enterprise. Trained on over 6 million real cloud fixes from 800+ accounts, Tami now offers a Remediation Confidence Score and a Safe Vulnerability...

Connected Vehicles, Disconnected Security: Why Connectivity Architecture Now Matters Most
Connected vehicles have surpassed 400 million worldwide, with each car projected to generate about 25 GB of data per hour by decade’s end. This massive, passive data flow traverses a complex web of mobile networks, cloud platforms, and third‑party services, often using...

Open Source DockSec Uses AI to Cut Through Vulnerability Noise in Docker Images
DockSec, an open‑source tool created by Advait Patel, combines existing scanners—Trivy, Hadolint, and Docker Scout—with large language models to filter duplicate CVEs and generate concrete remediation instructions. The LLM, selectable from OpenAI, Anthropic, Google Gemini or a local Ollama instance,...
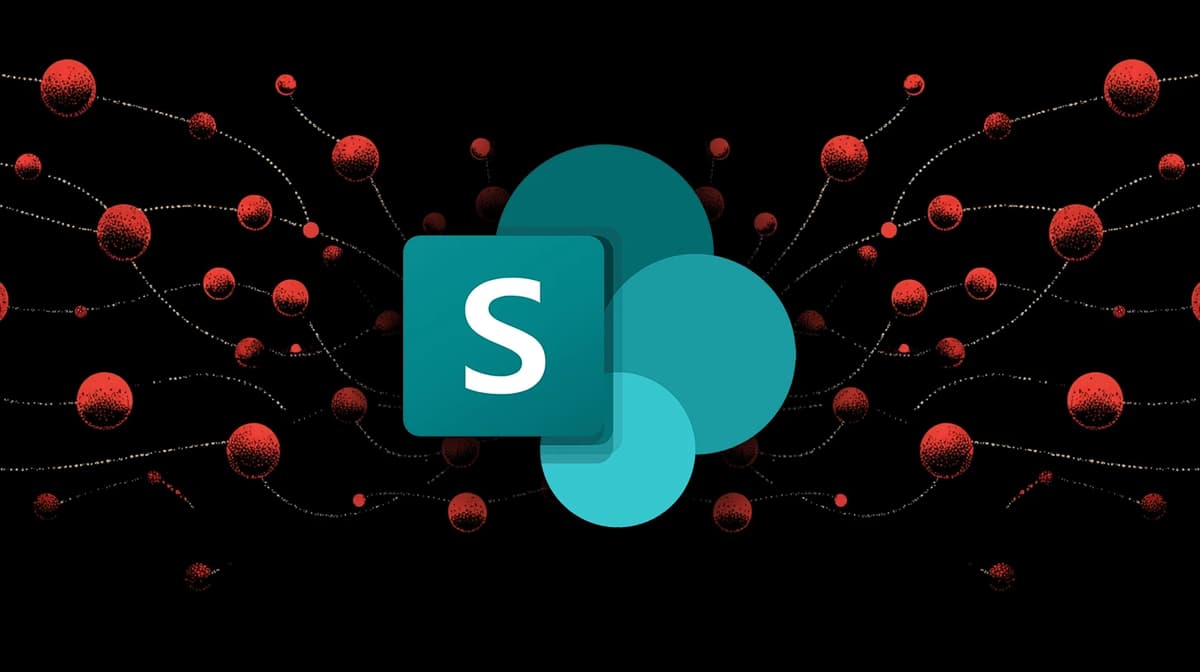
High-Severity SharePoint RCE Bug Patched by Microsoft (CVE-2026-45659)
Microsoft has issued patches for the high‑severity SharePoint remote code execution flaw CVE‑2026‑45659, which impacts SharePoint Server Subscription Edition, SharePoint Server 2019 and SharePoint Enterprise Server 2016. The vulnerability stems from deserialization of untrusted data and allows an authenticated attacker...

NightSpire Ransomware Abuses RDP for Stealthy Persistence
NightSpire ransomware, first identified in early 2025, has quickly become a high‑profile threat by combining double‑extortion tactics with stealthy persistence mechanisms. Between March and June 2025 the group compromised at least 64 organizations across 33 countries, using legitimate remote‑administration tools...

Why AI-Native Cybersecurity Matters in the Age of Machine-Speed Threats
The article argues that AI‑native cybersecurity is becoming essential as over 20 billion connected devices expand the attack surface faster than traditional defenses can adapt. Machine‑speed threats—automated phishing, autonomous privilege escalation, and rapid exploitation of misconfigurations—outpace legacy perimeter‑based models. AI‑driven analytics...

AI‑Driven Hackers Outpace Patches, Mobile Phishing Beats Email in 2026
Verizon's 2026 Data Breach Investigations Report finds AI‑enhanced hackers now exploit software flaws in 31% of breaches, outpacing the 43‑day median patch cycle. Mobile phishing simulations also reveal click rates 40% higher than traditional email attacks, reshaping corporate defense priorities.

CERT-In Recommends 12-Hour Patching for Internet-Facing Flaws Amid AI-Assisted Attacks
The Indian Computer Emergency Response Team (CERT‑In) has issued new guidelines that require organizations to patch critical internet‑facing vulnerabilities within 12 hours where feasible. The directive responds to the rise of AI‑assisted cyber threats, which can automate vulnerability discovery and compress...

Does Your Business Need a Software Bill of Materials?
Log4j’s 2021 fallout highlighted how blind spots in software inventories can cripple response to supply‑chain attacks. A software bill of materials (SBOM) provides a detailed, machine‑readable inventory of all open‑source and third‑party components, now required by U.S. Executive Order 14028 and...

What Is a vCISO? A Guide for Manufacturers
Manufacturers are confronting cyber risk as a business‑critical issue that threatens uptime, contract eligibility, and compliance. A virtual Chief Information Security Officer (vCISO) offers part‑time, executive‑level security leadership without the expense of a full‑time hire. By consolidating scattered tools, establishing...

Non-Human Identity for Workloads and AI Agents
Non‑human identity (NHI) is moving from long‑lived passwords and API keys to short‑lived, machine‑issued credentials that rotate in minutes. Emerging solutions use public‑private key pairs issued via certificate authorities, TPM‑backed hardware, or software generation, keeping keys in memory rather than...

Microsoft: Domain Controller Lookup May Fail on Windows Server 2016
Microsoft has identified a new known issue in Windows Server 2016 where domain controller lookups fail after the May 2026 KB5087537 security update. The bug only manifests on servers whose hostnames are exactly 15 characters long, causing nltest and other tools...

Cloud Atlas APT Leverages Hidden SSH Tunnels, Tor, PowerCloud
Today we’re having a look at both old and new tools from the Cloud Atlas APT group. The attackers actively use hidden SSH tunnels, Tor, RevSocks, the PowerCloud utility, and much more besides. A breakdown of the techniques and the...

Iranian Hackers Deploy MiniFast and MiniJunk V2 via Phishing and SEO Poisoning
Iranian state‑sponsored group Nimbus Manticore has rolled out a new AI‑assisted backdoor, MiniFast, in a multi‑wave campaign that began in February 2026. The actors combined traditional career‑themed phishing with novel delivery methods, including AppDomain hijacking, a trojanized Zoom installer, and...

Third-Party Cyberattack Impacts Patient Information at The Oncology Institute
The Oncology Institute announced that a third‑party software vendor, likely Cognizant‑owned TriZetto, suffered a cyberattack that exposed patient information. The breach, first disclosed in November 2025, was confirmed on May 20, 2026 when Kroll, the vendor’s third‑party administrator, reported unauthorized...

Security Experts Caution MFA Alone Can No Longer Stop Threat Actors
Security experts warn that multifactor authentication (MFA) alone can no longer stop phishing campaigns that steal Microsoft 365 OAuth tokens. New services such as EvilTokens and the FBI‑alerted Kali365 provide ready‑made, AI‑generated phishing kits that capture device‑code tokens, allowing attackers...

SolarWinds Hack Was More Humiliating for the Government Than We Thought
New Bloomberg reporting, based on a Freedom of Information Act release of the Treasury inspector‑general’s redacted investigation, confirms that the Russian‑linked group behind the 2020 SolarWinds supply‑chain breach accessed email accounts inside the U.S. Treasury Department and could operate without...
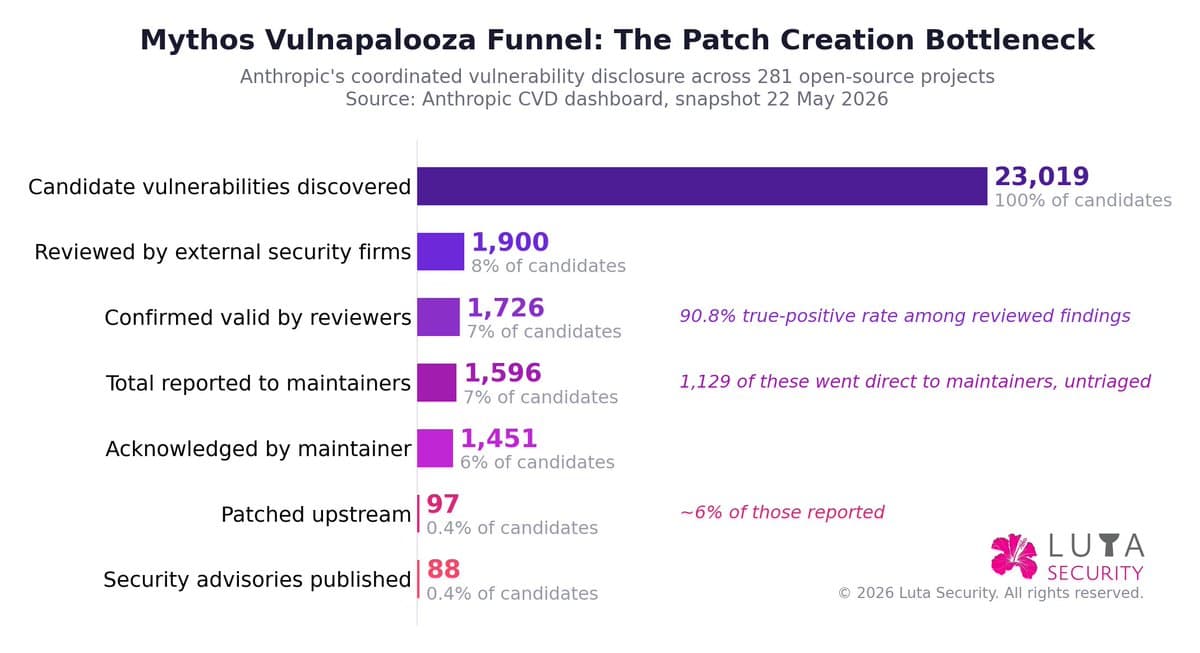
Systemic Approach to AI Vulnerability Coordination Reveals Patch Bottlenecks
New @LutaSecurity blog: AI Vulnerability Coordination at Vulnapalooza — First ##Mythos Encore. @AnthropicAI 's 1st Glasswing update surfaces bottlenecks in patch creation & deployment. Read about a systemic maturity approach to vulnerability coordination https://t.co/aNLoFCPNWH https://t.co/Tj4S0PeFX8

Zscaler to Acquire Symmetry Systems, Adding AI Agent Governance to Zero Trust Platform
Zscaler said it will acquire Symmetry Systems, a firm that builds access‑graph technology for AI‑agent security, to embed real‑time visibility and policy enforcement into its Zero Trust Exchange. The deal, whose financial terms were not disclosed, aims to give enterprises...

GitLab 19.0 Debuts Expanded DevSecOps Suite with Secrets Manager Beta
GitLab rolled out version 19.0 on Thursday, introducing a public beta of GitLab Secrets Manager for Premium and Ultimate customers and extending its Developer Flow across the merge‑request lifecycle. The upgrade aims to tighten credential security and streamline CI/CD pipelines...

2026 HIPAA Security Rule Finalized, Raising the Bar for Employee Health Data Management
The U.S. Office for Civil Rights finalized the 2026 HIPAA Security Rule in May 2026, adding mandatory annual security risk assessments, universal encryption of ePHI and multi‑factor authentication. The new requirements reshape how employers protect employee health information and pressure...

CypherLoc Scareware Locks Browsers of 2.8 Million Users, Prompting Fake Support Calls
Barracuda security researchers have uncovered a massive scareware campaign, dubbed CypherLoc, that has locked the browsers of roughly 2.8 million people since early 2026. The fake lock screens display personal IP data and a fraudulent support phone number, steering victims into...

Full Security Scanner Coverage of Your Codebase in Minutes
GitLab 19.0 introduces security configuration profiles that centralize SAST, dependency scanning, and secret detection settings. Teams can apply these default profiles across any number of projects from the UI, eliminating the need to edit individual .gitlab-ci.yml files. The profiles automatically...

Lithuania Raises Alert After Foreign‑State Breach Exposes 600,000 Records
Lithuanian officials placed the country on high alert after a breach that exposed more than 600,000 entries from real‑estate and legal‑entity registers. The leak, traced to compromised institutional logins, is blamed on a foreign state, prompting a resignation and heightened...

South Korea Eases Network‑Separation Rules for Banks to Boost AI Security
South Korea's Financial Services Commission announced a one‑year pilot that will ease network‑separation regulations for 49 financial institutions with assets over 10 trillion won. The move is designed to let banks and fintechs deploy high‑performance AI tools for cyber‑threat detection...

CISA Contractor’s GitHub Leak Exposes AWS GovCloud Keys for Six Months
A Nightwing contractor accidentally published a public GitHub repository containing administrative AWS GovCloud credentials for CISA systems, keeping them exposed from November 13, 2025 to May 18, 2026. The leak triggered an emergency containment response, congressional inquiries, and a fresh...

The New Topography for Cybersecurity
The rise of AI, cloud services and hybrid workforces is rewriting the fundamentals of cyber‑risk management. Traditional perimeter defenses that assumed users stayed inside a firewall are becoming obsolete as data and applications disperse across multiple environments. Security leaders now...

OMB Revamps Cyber Event Logging Requirements
The Office of Management and Budget issued Memorandum M‑26‑14, overturning the 2021 M‑21‑31 logging rules and shifting federal agencies to a risk‑based approach. The new directive focuses on Continuous Event Monitoring (CEM) and Threat Hunting, Investigation, Response and Forensics (THIRF),...

Aurigin AI Shows Top-Tier Audio Deepfake Detection Accuracy in New Benchmark
Aurigin AI topped Podonos' new Audio Deepfake Detection benchmark with 96.75% accuracy, recording a 1.5% false‑positive rate and a 5% false‑negative rate. The company also claims its detection infrastructure costs less than $0.001 per hour of audio, making it roughly...
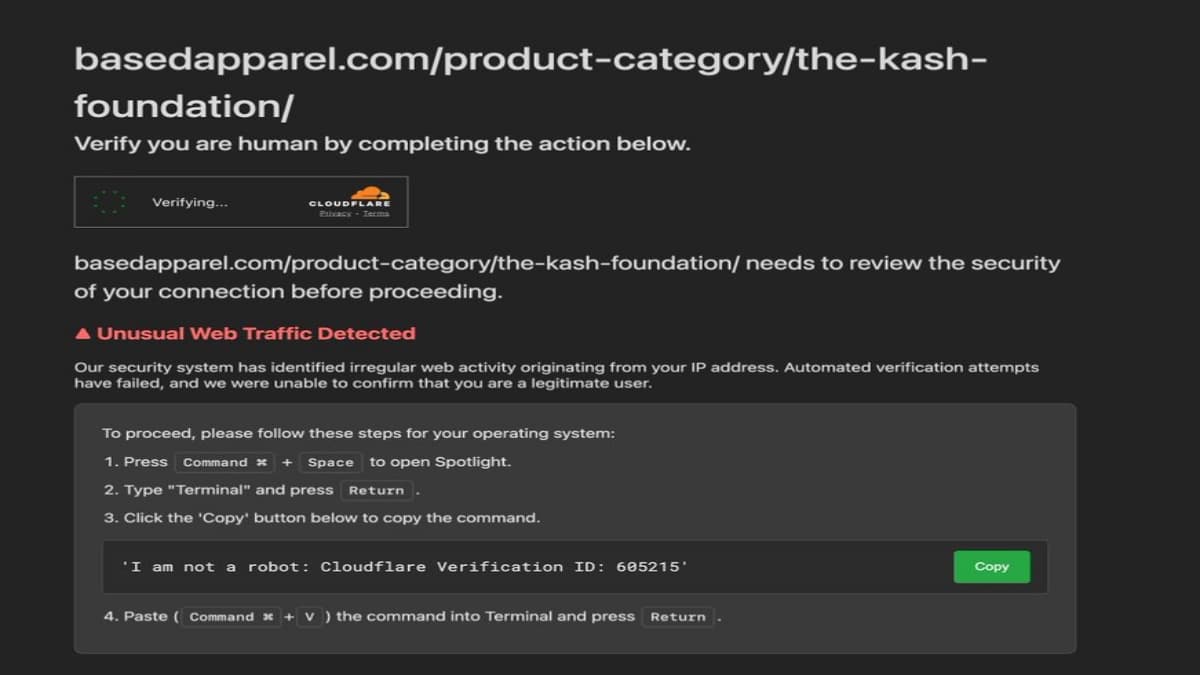
FBI Chief Kash Patel’s Clothing Store Hacked in ClickFix Infostealer Attack
An online clothing store tied to FBI Director Kash Patel, Based Apparel, was taken offline after a click‑fix attack distributed a macOS infostealer. The hack presented a counterfeit Cloudflare CAPTCHA that instructed visitors to paste malicious code into Terminal, enabling...

FBI Alerts Enterprises to Kali365 PhaaS Kit Bypassing Microsoft 365 MFA
The FBI issued a public service announcement warning that the Kali365 phishing‑as‑a‑service platform can bypass Microsoft 365 multi‑factor authentication using device‑code phishing. Priced at $250 for 30 days or $2,000 for a year, the kit is already compromising hundreds of...

Squid and Safe Labs Say Third-Party Module Behind $3.2M Exploit
A third‑party module called SquidRouterModule was exploited, draining roughly $3.2 million from 86 Safe (formerly Gnosis Safe) wallets across Ethereum and Base in about two hours. Blockaid identified the vulnerability, which let the attacker impersonate authorized delegates and swap stolen tokens...

AI Shifts Cybersecurity Toward Autonomous Defense, Not Alerts
AI is moving cybersecurity from detection to autonomous defense. If OpenAI and Anthropic can identify, fix and prevent vulnerabilities directly, many classic cybersecurity tools will face pressure. The survivors will be those that own trust, workflows and real-world security outcomes, not just...

Cisco Refines Its Risk-Based Vulnerability Disclosure for the AI Era
Cisco announced it will use advanced AI models to accelerate vulnerability discovery and shift to a risk‑based disclosure approach. The new framework will prioritize bugs that are actively exploited or have high impact, while low‑risk findings may be bundled into...

GitHub Hit with Another Major Attack — Megalodon Hits over 5,000 Repos with Malware-Laden Commits
Security firm SafeDep uncovered a new supply‑chain campaign dubbed Megalodon that has infected more than 5,500 GitHub repositories. The worm‑like attack uses a fake “build‑bot” to submit malicious commits that harvest CI/CD secrets such as cloud keys, SSH credentials, and...