Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB

IBM and Red Hat Deploy $5 B Project Lightwell to Secure Open‑Source AI Tools for DevOps
IBM and Red Hat announced a $5 billion, 20,000‑engineer initiative called Project Lightwell to embed AI‑driven security into the open‑source components that power modern DevOps pipelines. Early adopters include major banks and payment networks, signaling a shift toward enterprise‑grade protection of CI/CD, infrastructure‑as‑code and AI frameworks.

Iran-Linked Ababil Group Tied to 700 GB LA Transit Data Breach
Israeli cybersecurity firm Gambit Security says the March breach of the Los Angeles County Metropolitan Transportation Authority was carried out by the Iran‑linked hacker group Ababil of Minab, which exfiltrated at least 700 GB of emails, backups and internal files. The...

Iconic 138-Year-Old South African Sports Club Allegedly Struck in 674,000-Record Cyber Attack
The Wanderers Club, a 138‑year‑old South African sports and country club, is accused of suffering a massive data breach that exposed roughly 674,000 member records. Hacker known as Databasehooligan posted the dataset on a dark‑web forum and asked for about...

What Are iPhone Background Security Improvements and How to Enable Them
Apple rolled out iOS 26.3.1 in March, adding the first Background Security Improvements (BSI) feature. BSI delivers lightweight, automatic patches for components like Safari, WebKit, and core system libraries between major releases. The update mirrors the 2023 Rapid Security Response model...

Scammers Are Using Your Real Hotel Reservations to Trick You With Spear-Phishing Attacks
Security firm Norton uncovered a reservation‑hijacking campaign that has compromised at least 350 hotels, vacation rentals and guesthouses across 50 countries. Criminals steal real booking names, dates and prices to craft spear‑phishing messages sent via SMS, WhatsApp and email, luring...
GCHQ Chief Urges Action as AI Reshapes Cyber Threats
GCHQ director Anne Keast‑Butler warned that AI is rapidly reshaping cyber threats, turning attacks into machine‑speed assaults that outpace human defenses. She framed cybersecurity as a national‑defence issue and urged UK businesses to act now rather than wait for guidance....

An Open-Source Toolkit for Controlling Out-of-Control AI Agents
Microsoft has launched a public‑preview, open‑source Agent Governance Toolkit (AGT) to wrap policy‑based controls around AI agents. The toolkit evaluates each agent action before execution, limiting API calls, token spend, and rogue behavior while adding less than 0.1 ms of latency....
ESET APT Activity Report Q4 2025–Q1 2026
ESET’s Q4 2025‑Q1 2026 APT Activity Report details a surge in nation‑state cyber operations across five major threat actors. China‑aligned groups intensified espionage on maritime, energy and AI targets in Venezuela, Syria, Cambodia, Panama and South Korea, while Iran‑aligned proxies deployed destructive...
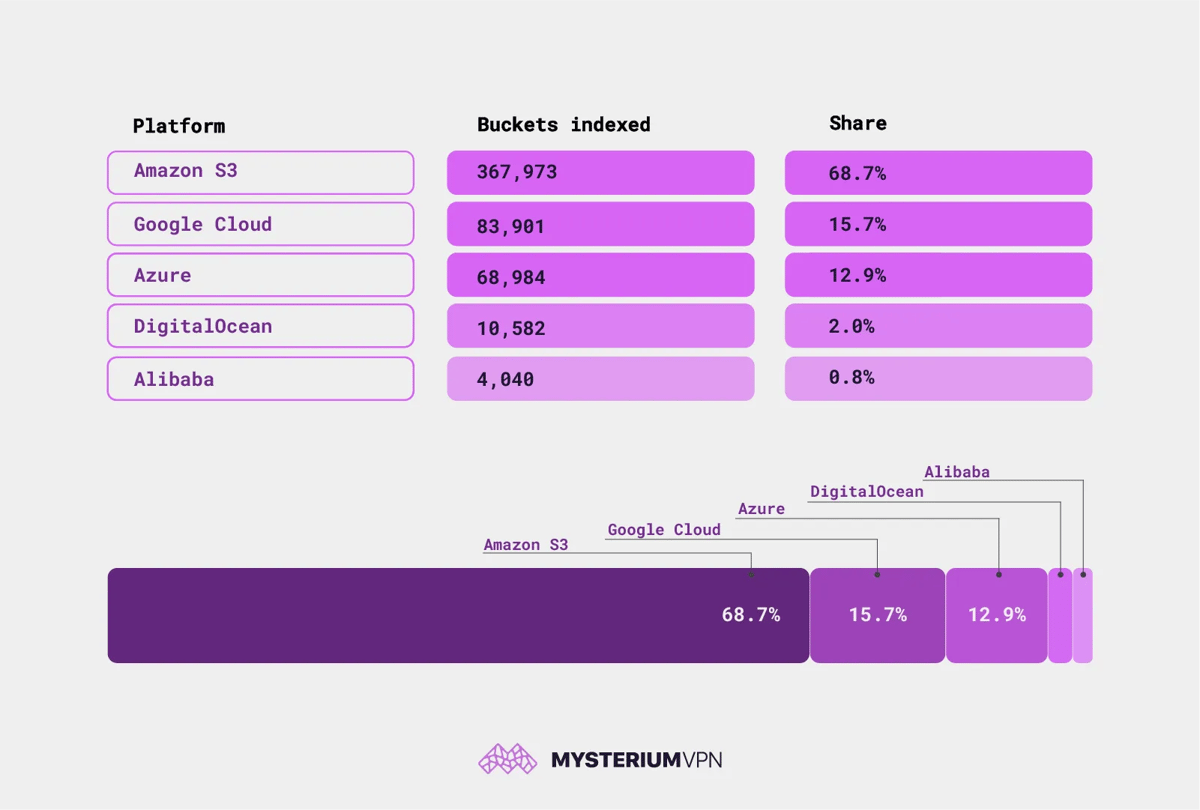
19.6 Billion Files Are Sitting Open on the Internet. No Password Required
Researchers at Mysterium VPN identified 19.6 billion publicly accessible files across 535,480 cloud storage buckets on AWS, Google Cloud, Azure, DigitalOcean and Alibaba. Among them are 685,000 credential files and nearly 1 million database dumps, exposing passwords, API keys and customer data....

Nordic CISOs Handle Rising Cyber Threats Remarkably Well
Truesec’s 2026 Nordic CISO report finds that, despite a surge in overall cyber activity, 91% of surveyed CISOs say severe incident rates have remained flat since 2024. The average dwell time for attackers dropped dramatically from 53 days to just...

Company CEO Flooded File Share with Smut, Called for Help After He Deleted It
A corporate CEO stored explicit photos on a publicly accessible file share, prompting the IT department to restore and later delete the content at HR’s request. In a separate case, an employee’s personal porn files were discovered on a work...

Worth Reading: Ephemeral BGP Leaks
Doug Madory’s APNIC blog post argues that transient BGP leaks observed during the path‑hunting phase after a route withdrawal are harmless and can be ignored. The response counters this view, calling the leaks a “dead canary” that signals weak route‑policy...

Investigating the Potential Use of Frontier AI Models for Offensive Cyberattacks: A Human Uplift Study
A RAND‑conducted human uplift study commissioned by the UK AI Security Institute examined whether frontier AI models boost offensive cyber capabilities among lower‑skilled participants. One hundred fifty‑seven volunteers tackled network, OS and vulnerability‑exploitation challenges, half with access to models such...

Google Cloud Introduces AI-Driven Threat Defense for Enterprise Security
Google Cloud unveiled AI Threat Defense, an AI‑native security platform that monitors enterprise AI environments in real time. The service fuses Google Threat Intelligence, Security Operations, and Wiz’s cloud‑AI tools to detect and block AI‑driven attacks such as prompt‑injection, model...

Employees Are Unknowingly Inviting Tech Support Impersonators Into Firms, Says FBI
The FBI’s latest Flash report warns that the Silent Ransom Group (also known as Luna Moth, Chatty Spider, UNC3753) has begun sending impostor IT support personnel into U.S. law firms. The attackers gain physical access, plug malicious USB devices into...

AI‑Driven Exploits Overtake Password Theft as Top 2026 Breach Vector, Mobile Phishing Surges
Verizon's 2026 Data Breach Investigations Report finds AI‑powered vulnerability exploitation now drives 31% of corporate breaches, eclipsing stolen passwords at 13%. Mobile phishing attacks achieve 40% higher click rates than email, making phones the fastest‑growing entry point.

Advancing Post-Quantum Capabilities of SSH in Red Hat Enterprise Linux
Red Hat Enterprise Linux 10.2 expands its post‑quantum SSH capabilities, making hybrid key‑exchange algorithms the default for both OpenSSH and libssh. In FIPS mode the release adds two NIST‑approved hybrids—mlkem768nistp256‑sha256 and mlkem1024nistp384‑sha384—through downstream patches. libssh 0.12.0 now prefers mlkem768x25519‑sha256, allowing custom SSH...

'Threat Actors Are Adapting Social Engineering and Monetization Strategies to Modern User Behavior': Microsoft Warns AI Chatbots May Be Sending...
Microsoft researchers have identified a new cyber‑crime vector in which threat actors manipulate AI chatbots to recommend counterfeit utility‑download sites such as HWMonitor and CrystalDiskInfo. When users follow these AI‑generated links, the sites deliver malware via DLL sideloading, installing ScreenConnect...

The Cyber Strategy for America: How AI-Powered Security, Shared Services Enable Agile Cyber Defense
Federal agencies are confronting a surge of AI‑enhanced cyber attacks, with CISA reporting over 30,000 incidents and 2.6 billion malicious connections blocked in 2025. The White House’s Cyber Strategy for America outlines three pillars for civilian agencies: easing adoption of modern...

Cyber Defense in the Era of Frontier AI: Insights From Mythos and GPT 5.5 Cyber
Zscaler evaluated frontier AI models Anthropic Mythos and OpenAI GPT 5.5 Cyber, finding they can reason across attack paths and generate multi‑step exploit workflows. Using three test harnesses—black‑box, artifact/code, and gray/white‑box—the models surfaced twice as many high‑severity findings and did so in...

12 AI Prompts that Leak Enterprise Data—And How to Fix Them
Enterprises are confronting a new data‑leakage vector as employees feed sensitive information into generative AI chat interfaces. The 2026 ThreatLabz report shows ChatGPT alone generated 410 million DLP policy violations, a 99.3% jump from the prior year. Legacy data‑loss‑prevention tools cannot...
OpenAI Heralds Cybersecurity, Election Interference Safeguard Plans for 2026 Midterms
OpenAI announced a five‑point strategy to protect the 2026 U.S. midterm elections, focusing on reliable voting information, cybersecurity assistance, deep‑fake watermarking, strict policy enforcement, and reducing political bias in its models. The company is making its Codex Security and Trusted...

AI Is Compressing Attack Timelines. Here's How Agencies Can Respond.
Anthropic's Mythos preview model uncovered thousands of zero‑day vulnerabilities across major operating systems and browsers, highlighting AI's power to accelerate attack discovery. Federal and state CISOs face heightened risk as nation‑state actors adopt AI‑assisted tools that can exploit flaws within...

Anthropic Adds 28 Security Integrations to Claude, Boosting Enterprise Data Governance
Anthropic announced the addition of 28 new security and compliance integrations to its Claude enterprise platform, enabling organizations to route conversation content and activity logs into existing monitoring tools. The move targets growing concerns over data governance as large language...

AI‑Powered Bot Network Seen Automating Phishing, Scams and Sabotage
Google’s Threat Intelligence Group disclosed evidence of an AI‑enabled bot network that is automating phishing attacks, financial scams and sabotage operations. The finding underscores a rapid compression of attack timelines as adversaries adopt agentic AI tools.

The AI Phishing Revolution: From Spray-and-Pray to Autonomous Operations
AI is reshaping phishing from manual, spray‑and‑pray tactics to fully autonomous operations. Large language models now generate convincing spear‑phishing emails in minutes, while "vibe coding" fuels Phishing‑as‑Service platforms that auto‑write code, obfuscate payloads, and spin up infrastructure. Autonomous agents scrape...

ECB Urges Banks to Tackle AI Security Threats
The European Central Bank convened an emergency meeting with the eurozone’s 111 largest banks to warn of AI‑driven cyber threats, singling out Anthropic’s Claude Mythos Preview as a high‑risk model. Industry data shows 67% of financial firms are accelerating AI...

Chinese Apps Fail Ministry Testing
Taiwan's Ministry of Digital Affairs disclosed that four Chinese apps—Amap, iQIYI, Bilibili and BimoBimo—failed cybersecurity tests, requesting permissions far beyond their core functions. Amap exhibited the highest risk, with 11 problematic behaviors on Android and eight on iOS, including background...

Iran’s Nimbus Manticore Used Trojanized Zoom Installers Against US Firms
Check Point Research uncovered a campaign by Iran‑linked Nimbus Manticore that used trojanized Zoom installers and SEO‑poisoned sites to deliver AI‑assisted malware to U.S. aviation and software firms. Between February and April 2026 the group shifted from fake job offers...
Exploits Arrive Before Patches: AI Defense Becomes Essential
The most important number in cybersecurity right now is negative seven. That's what Mandiant (part of Google Cloud)'s M-Trends 2026 report found: mean time to exploit is now an estimated -7 days. Exploitation is routinely happening before a patch is even...
FBI: Phishing-as-a-Service Kit Hijacks Microsoft 365
The FBI has flagged a new phishing‑as‑a‑service kit called Kali365 that hijacks Microsoft 365 accounts by stealing the access token issued after a successful multifactor authentication (MFA) check. The kit exploits Microsoft’s device‑code sign‑in flow, allowing attackers to bypass MFA and...

Microsoft Is Killing SMS Sign-In Codes. ERP Teams Should Pay Attention
Microsoft is phasing out SMS one‑time codes for personal Microsoft accounts, steering users toward passkeys, Microsoft Authenticator, and verified email. The deprecation does not affect Microsoft Entra ID work accounts, but it does impact ERP teams that rely on personal...

CrowdStrike and Google Take Down Botnet Used by Hackers to Target Open Source Software Developers
CrowdStrike, in partnership with Google and nonprofit Shadowserver, dismantled the Glassworm botnet that had been compromising open‑source developers for two years. The operation shut down four command‑and‑control servers that leveraged the Solana blockchain, BitTorrent, Google Calendar and VPNs, halting further...

The FBI Just Dropped Its 2025 Internet Crime Report. Here Are 6 Big Takeaways
The FBI’s 2025 Internet Crime Report shows internet‑crime complaints exceeding 1 million for the first time, with more than 3,000 reports filed each day. Reported losses surged to over $20 billion, a $4 billion increase from 2024 and double the amount recorded four...

Latin American Cybercriminals Hoover Up Government Data
Latin American cybercriminal groups have made public administration the region's most‑breached sector, accounting for 21% of all breaches (543 incidents) in the past year. High‑profile compromises include Uruguay's Antel identity service, data theft from 25 Mexican agencies, and a wave...
AI-Assisted Exploit Development Outpaces Scanner Detection
Researchers at Cogent Security found that AI‑assisted exploit creation slashed the time needed to weaponize a disclosed vulnerability from 125 days in early 2025 to just 0.5 days by April 2026. The acceleration, driven by publicly available large language models that can read patch...

Krispy Kreme to Pay $1.6 Million Settlement to 161,000 Ransomware Victims
Krispy Kreme has agreed to a $1.6 million class‑action settlement after a November 2024 ransomware attack exposed the personal data of roughly 161,000 current and former employees. Affected individuals must file claims by June 22, 2026 to receive up to $3,500 in compensation or...
Malicious Npm Package Stole Files From Claude AI User Directory via GitHub
Security researchers at OX Security have identified a malicious npm package, mouse5212‑super‑formatter, that steals files from the Claude AI user directory. The package uploads data to a threat‑actor‑controlled GitHub repository by leveraging a GitHub token found on the victim’s machine...

Sola Security Unveils Lumina, Forwarding an Autonomous Security Deep Research Platform for Actionable Risk Intelligence?
Sola Security introduced Lumina, an autonomous risk‑intelligence platform that continuously scans cloud, identity, SaaS and endpoint environments. The solution converts thousands of raw data points into a daily feed of contextualized signals, each enriched with business impact and recommended actions....

AI Coding Tools Are Widening the Security Validation Gap, Survey Finds
New research from Pentest‑Tools.com shows AI coding tools are outpacing security validation, creating a widening gap between code generation speed and vulnerability testing. Only 9% of developers feel testing keeps up, while 51% discover flaws after deployment. The survey of...

How Can MSSPs Scale Threat Detection Without Burning Out Their Analysts?
Managed security service providers (MSSPs) face a talent bottleneck that limits analyst capacity as client demand surges. To avoid burnout, they are adopting AI‑driven threat intelligence, automated enrichment, and AI‑assisted triage from vendors like ANY.RUN. Integrated feeds, YARA‑based custom detection,...

‘Silent’ Ransomware Group Poses as IT Workers, Targeting Healthcare
The Silent Ransom Group, also known as Chatty Spider, has shifted from traditional phishing to posing as IT employees to infiltrate networks. Since spring 2024 the gang contacts staff by phone or email, urging remote‑desktop access or even sending operatives...

CrowdStrike, Google Take Down Glassworm Botnet
A joint operation by CrowdStrike, Google and the Shadowserver Foundation has dismantled the Glassworm botnet by simultaneously disabling its four command‑and‑control channels, which included VPS servers, Google Calendar entries, peer‑to‑peer networks and Solana blockchain memo fields. Glassworm, active since early...

Fake Job Offers From Meta And Spotify Used To Hack Facebook Accounts In New Scam
Cybercriminals are running a sophisticated phishing campaign that masquerades as recruitment drives from high‑profile brands such as Meta, Disney, Coca‑Cola and Spotify. The scheme begins with polished job‑offer emails that bypass spam filters, then redirects victims to hidden “HUB” domains...

7‑Eleven Breach Exposes Personal Data of 185,000+ Customers
7‑Eleven disclosed that a hack‑and‑extortion attack by the ShinyHunters group compromised personal data of more than 185,000 customers, including names, birth dates, addresses, phone numbers, emails, Social Security numbers and driver’s licenses. The breach highlights growing ransomware‑style threats to retail...

ECB Calls Urgent Meeting with Eurozone Banks Over AI‑Driven Cyber Threats
The European Central Bank has convened an emergency session with the eurozone’s 111 largest banks to accelerate defenses against AI‑powered cyber threats. Regulators warned that Anthropic’s Claude Mythos model has already uncovered thousands of high‑severity flaws, prompting a call for...

Cisco Research Finds Standard AI Safety Benchmarks Miss the Real Threat
Cisco’s AI Threat Intelligence team evaluated 15 leading closed‑source large language models using both single‑turn and multi‑turn adversarial prompts. The study found multi‑turn attack success rates ranging from 7.9% to 88.3%, far exceeding the 2.2%‑64.9% rates seen in single‑turn tests....
Vercel Breach Uses Stolen OAuth Token to Bypass MFA in $2 M Supply‑chain Attack
Vercel disclosed that attackers stole a Google OAuth session token from a personal device, replayed it to bypass multi‑factor authentication, accessed internal systems, exposed 580 employee records and demanded a $2 M ransom. The incident underscores the growing danger of token‑replay...
Mitigating CVE-2026-31431 (“Copy Fail”) In Docker Engine
Docker Engine version 29.4.3 introduces a layered mitigation for CVE‑2026‑31431, known as “Copy Fail,” by adding AppArmor and SELinux rules that block AF_ALG socket creation while retaining the original seccomp filter. The vulnerability is a Linux‑kernel privilege‑escalation flaw affecting kernels released...

All Major LLMs Exposed to Multi-Turn Manipulation, Warn Researchers
Researchers at Cisco discovered that multi‑turn conversations can circumvent the safety guardrails of leading large language models, including ChatGPT, Claude, Gemini, Amazon Nova, and xAI’s Grok. By iteratively reframing requests, adopting personas, and exploiting configuration settings such as Grok’s reasoning...