Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB
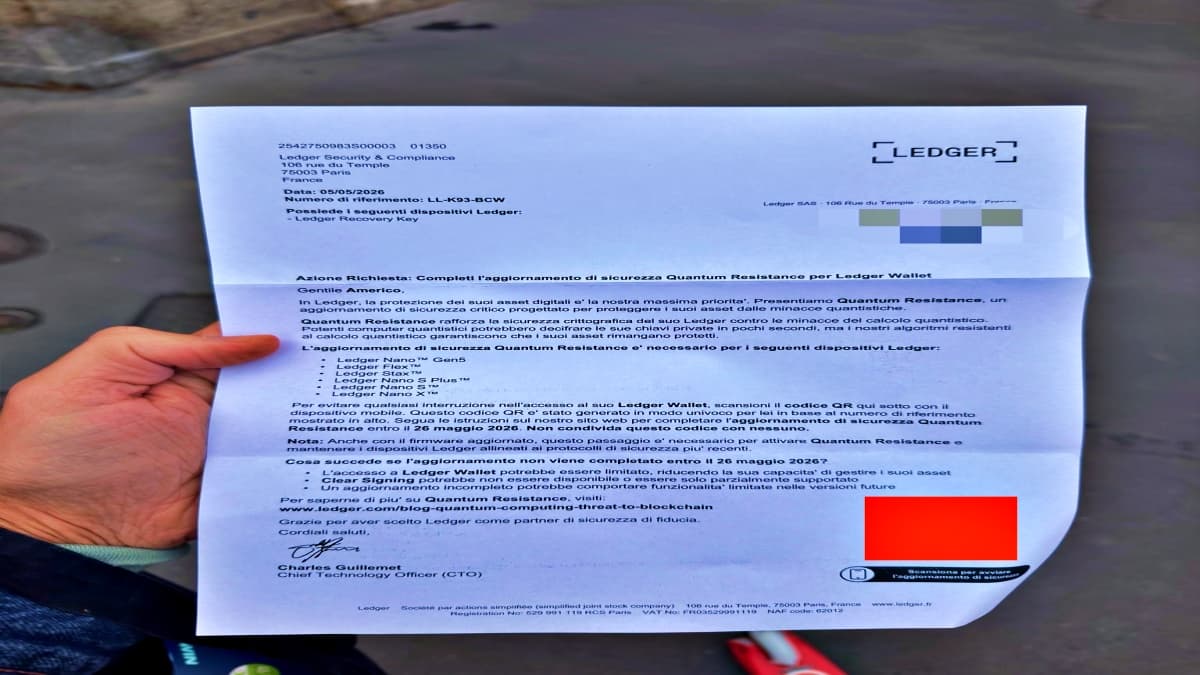
Scammers Send Physical Phishing Letters to Steal Ledger Wallet Seed Phrases
Scammers are sending forged Ledger‑branded letters that include QR codes to trick hardware‑wallet owners into revealing their 24‑word seed phrases. The campaign is localized, with versions in Italian and other languages, indicating attackers may have accessed customer shipping data from a recent breach. Recipients are warned of a fake "Quantum Resistance" update and urged to act quickly, or risk losing wallet functionality. Ledger has confirmed the scheme and reiterated that it never requests recovery phrases through any channel.

Grafana Says It Rejected Ransom Demand After Source Code Theft
Grafana Labs reported that a threat actor accessed its GitHub repository using a compromised token, downloading parts of the company’s open‑source codebase. The investigation found no evidence of customer data exposure or impact on client systems. Grafana publicly refused the...

CISA Orders Federal Agencies to Patch Cisco SD‑WAN Vulnerability by Sunday
The Cybersecurity and Infrastructure Security Agency (CISA) issued an emergency Binding Operational Directive requiring every Federal Civilian Executive Branch agency to patch a newly exploited Cisco SD‑WAN vulnerability by Sunday. The move underscores the critical role of SD‑WAN management infrastructure...

Datavault AI Deal Fuels Surge in Cybersecurity ETFs as AI Defenses Gain Investor Favor
Datavault AI's acquisition of CyberCatch and $800 million in tokenization contracts sparked a rally in cybersecurity-focused exchange‑traded funds, with the Amplify Cybersecurity ETF (HACK) climbing 1.08% and peers rising. The move reflects heightened investor appetite for AI‑enabled security solutions amid rising...

OCR Studio Expands KYC Fraud Detection for AI-Generated Identity Documents
OCR Studio has upgraded its document‑verification platform with an anti‑fraud engine that can spot AI‑generated and morphed identity documents, including forgeries created by tools such as ChatGPT, Midjourney, Grok and NanoBanana. The technology examines the underlying image structure to detect...

Cybersecurity Experts Warn: This Common Email Habit Is a Gift to Hackers
Cybersecurity experts warn that using an email address as the sole username and relying on one‑click logins creates a single point of failure. If a hacker gains access to that inbox, they can reset passwords, intercept verification codes, and hijack...

The Mythos Stress Test: Can Indian Fintechs, Banks Fend Off AI-Native Cyber Threats?
Anthropic’s Mythos AI model has demonstrated the ability to autonomously uncover long‑standing software vulnerabilities, prompting alarm across the global security community. In India, the finance ministry convened senior bank leaders after Mythos’ release, forming a panel headed by SBI chairman...

LeakWatch 2026, Security Incidents, Data Breaches and IT Status for the Current Calendar Week 20
During calendar week 20 (May 11‑17 2026) LeakWatch recorded a shift from isolated leaks to clustered risk vectors. Notable incidents included a material cyberattack on West Pharmaceutical Services that halted global production systems, a confirmed breach at Foxconn’s North American factories, and...

Microsoft Exchange Zero-Day Demonstrated at Pwn2Own, Already Exploited Globally
Microsoft confirmed that the CVE‑2026‑42897 Exchange Server zero‑day, demonstrated at the Pwn2Own Berlin contest, is already being leveraged in active attacks against on‑premises deployments. The exploit chain earned a $200,000 bounty and triggered an emergency mitigation advisory for thousands of...

Microsoft Blocks CVE for Azure Backup for AKS Flaw, Sparks Disclosure Debate
Security researcher Justin O'Leary disclosed a critical privilege‑escalation flaw in Azure Backup for AKS in March. Microsoft’s Security Response Center dismissed the report and blocked a CVE, even after the CERT Coordination Center validated the bug. The dispute highlights tension...
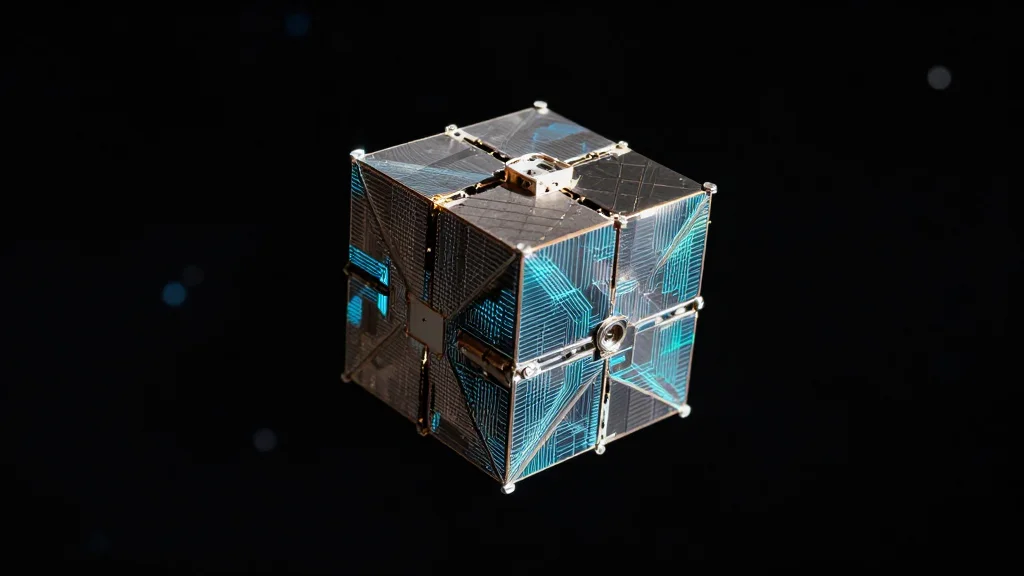
OCaml Runtime Goes to Orbit, Demonstrates First In‑Space Post‑Quantum Key Rotation
On 23 April, the Borealis daemon—built on a pure‑OCaml CCSDS protocol stack—booted aboard DPhi Space’s ClusterGate‑2 payload, delivering end‑to‑end encrypted command and control with post‑quantum key rotation. The demonstration marks the first public in‑orbit use of ML‑DSA‑65 signing keys, showing that...

FCA, Bank of England and Treasury Joint Statement on Frontier AI Models and Cyber Resilience
The FCA, Bank of England and Treasury issued a joint statement warning that frontier AI models are already capable of automating cyber attacks at scale, creating new threats to the safety and soundness of UK financial firms. Regulators outlined five...

The Cyber Resilience Standard Every Hospital CIO Must Meet
Hospital CIOs now face a minimum standard to deliver safe patient care for at least 30 days without core technology, driven by the Joint Commission and American Hospital Association's Cyber Resilience Readiness (CRR) program. The average healthcare breach costs $7.42 million,...

Akamai to Acquire LayerX for $205 Million, Boosting AI Usage‑Control Capabilities
Akamai Technologies agreed to buy LayerX for about $205 million, adding browser‑based AI usage‑control tools to its Zero Trust portfolio. The deal, slated to close in Q3 2026, targets the growing need for real‑time visibility into generative AI interactions and is expected...

Cohesity and HPE Deepen Alliance to Boost Cyber‑resilience and Hybrid‑cloud Data Protection
Cohesity announced an expanded seven‑year strategic alliance with HPE, adding new resell agreements for HPE Zerto, Cohesity NetBackup and deeper integration with HPE Morpheus. The move aims to give enterprises AI‑powered cyber‑resilience and streamlined hybrid‑cloud data protection, with solutions slated...

World Bank, African DPAs Outline Formula for Trusted Digital Identity, DPI
At the ID4Africa 2026 AGM, the World Bank warned that trust is the linchpin of digital public infrastructure. It highlighted six technical and governance risks that have undermined Kenya, India, Uganda and other nations’ digital ID programs. A panel of...

Anthropic's Mythos AI Helps Researchers Crack macOS, Raising AI Safety Concerns
Anthropic’s Claude Mythos Preview AI was used by Palo Alto‑based security firm Calif to develop a kernel‑memory‑corruption exploit that gives an unprivileged user full control of macOS on Apple M5 silicon. The breach, disclosed to Apple, spotlights the dual‑use risk...

AI Could Steal Fingerprints From High-Resolution Selfies, Experts Warn
Experts warn that modern smartphone cameras can capture enough ridge detail in high‑resolution selfies to reconstruct fingerprints, reviving concerns about biometric security. Recent reports from China suggest images taken from about five feet away, especially with the popular peace‑hand gesture,...

Foxconn North American Factories Hit by Nitrogen Ransomware Attack, Production Resumes
Foxconn said its North American facilities were hit by a ransomware attack claimed by the Nitrogen group, which alleges the theft of more than eight terabytes of data and 11 million files. The company’s cybersecurity team has activated response measures and...

OpenAI Debuts Daybreak AI Security Platform as First AI‑Built Zero‑Day Emerges
OpenAI launched Daybreak, an agentic cybersecurity platform that embeds GPT‑5.5 and its Codex Security engine into the software development lifecycle. The debut coincided with Google’s disclosure of the first confirmed AI‑generated zero‑day exploit, underscoring a rapid escalation in AI‑driven attack...

UK Regulators Warn of Frontier AI Cyber Risks to Banking Sector
The Bank of England, the Financial Conduct Authority and HM Treasury released a joint statement warning that frontier AI models amplify cyber threats to banks. Regulators said firms must upgrade protective and response capabilities and align investment with the emerging...

Yarbo Robotic Lawn Mowers Patch After Security Researcher Reveals Remote‑Hijack Flaw in 11,000 Units
Security researcher Andreas Makris disclosed a remote‑access flaw in Yarbo's robotic lawnmowers that left more than 11,000 devices worldwide vulnerable. The company responded with emergency firmware updates, new credential policies, and tighter diagnostic controls. The incident spotlights the growing cybersecurity...

FBI Posts $200,000 Reward for Ex‑Air Force Counterintelligence Agent Monica Witt
The FBI’s Washington Field Office has put a $200,000 bounty on former Air Force counterintelligence specialist Monica Witt, who defected to Iran and is alleged to have supplied classified defense data and assisted Iranian hackers. The move underscores lingering concerns...

CISA Flags Actively Exploited Linux Root‑Access Bug (CVE‑2026‑31431) in KEV Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) placed the Linux privilege‑escalation flaw CVE‑2026‑31431 into its Known Exploited Vulnerabilities (KEV) catalog, citing active exploitation. The bug, scored 7.8 on the CVSS scale, lets an unprivileged user gain root via a...

Composer Flaw Leaks GitHub Actions Tokens, Prompting Emergency Patch Across PHP Ecosystem
A newly discovered Composer vulnerability (GHSA-f9f8-rm49-7jv2) printed GitHub Actions tokens in CI logs, risking credential exposure for millions of PHP projects. Packagist responded with an emergency advisory and patches for affected versions, urging immediate remediation.

Eversheds Sutherland Launches PROPcast Episode 4 on Cyber‑security Risks in Smart Buildings
Eversheds Sutherland released episode 4 of its PROPcast series, a podcast that dissects cyber‑security challenges in smart‑building deployments. The episode spotlights the shifting responsibility for digital risk among owners, tenants and lenders as IoT adoption accelerates across commercial real estate.

Microsoft Patch Tuesday Fixes 138 Flaws, 16 Discovered by AI System MDASH
Microsoft released a Patch Tuesday update that patched 138 vulnerabilities, 30 of them critical. Sixteen of the flaws were discovered by Microsoft’s AI‑driven MDASH system, underscoring a new pace for enterprise vulnerability management.

Common Azure Privilege Escalation Paths Attackers Exploit
Azure privilege escalation typically follows a chain of modest misconfigurations rather than a single dramatic exploit. Attackers often start with a user who owns an application registration, add a client secret, and leverage the app’s permissions to read directory data...

ESET Details New Ghostwriter Activity Targeting Ukrainian Government
ESET researchers have identified a new Ghostwriter (FrostyNeighbor) campaign targeting Ukrainian government agencies, active since March 2026. The operation begins with a spear‑phishing PDF masquerading as an Ukrtelecom notice, using geofencing to deliver a decoy to non‑Ukrainian IPs and a malicious...

Android 16 Bug Allows Apps to Ignore VPNs and Leak IP Addresses
A newly disclosed vulnerability in Android 16’s ConnectivityManager lets malicious apps bypass VPN tunnels and expose the device’s real IP address. The bug, reported through Google’s Vulnerability Reward Program, was deemed “infeasible” to fix by Google’s security team, leaving it...

Diversify Custody: Combine Cold Wallets, Exchanges, Anchorage
A hack at Anchorage cannot send your assets anywhere except your whitelisted cold wallet. Multi-sig process, 24 hour release SLA, and a verification call before anything moves. You are never a creditor of Anchorage. Assets sit in an FBO account...

Chinese APTs Salt Typhoon and Twill Typhoon Broaden Targets and Deploy New Backdoors
Chinese state‑backed groups Salt Typhoon and Twill Typhoon intensified campaigns between December 2025 and February 2026, hitting an Azerbaijani oil and gas firm and a slate of telecom, government and technology entities across five continents. The actors leveraged a Microsoft...

Did Iran Hack Tank Readers at US Gas Stations? Security Leaders Discuss
U.S. officials suspect Iranian hackers breached unsecured automatic tank gauge (ATG) systems at gas stations, altering fuel‑level displays without affecting actual storage. The intrusion, reported by CNN, highlighted that the ATG devices were online without password protection, enabling remote manipulation....

Exchange Server Zero-Day Vulnerability Can Be Triggered by Opening a Malicious Email
Microsoft disclosed a zero‑day cross‑site scripting vulnerability (CVE‑2026‑42897) in on‑premises Exchange Server 2016, 2019 and Server Subscription Edition that can be exploited by simply opening a crafted email in Outlook Web Access. The flaw is already being used in the...

AI Agents Show They Can Create Exploits, Not Just Find Vulns
Researchers from leading universities and AI firms introduced ExploitGym, a benchmark that evaluates whether frontier AI agents can turn software bugs into functional exploits. The suite contains 898 real‑world vulnerabilities from Google’s V8 engine and the Linux kernel. In two‑hour...

Funnel Builder WordPress Plugin Bug Exploited to Steal Credit Cards
A critical, unauthenticated vulnerability in FunnelKit's Funnel Builder WordPress plugin is being actively exploited to inject malicious JavaScript into WooCommerce checkout pages. The flaw, affecting all versions prior to 3.15.0.3, lets attackers add a skimmer script that steals credit‑card numbers,...

A Hotel Check-In System Left a Million Passports and Driver’s Licenses Open for Anyone to See
A misconfigured Amazon S3 bucket used by Tabiq, the hotel check‑in platform from Japan’s startup Reqrea, exposed over 1 million passports, driver’s licenses and selfie verification photos to the public web. Security researcher Anurag Sen discovered the open bucket and alerted...

Researchers Use Anthropic’s Mythos AI to Find Two Bugs in MacOS, Cracking Apple’s Memory Integrity Enforcement in Just 5 Days
Researchers at Calif used Anthropic's Mythos AI to uncover two MacOS bugs that together bypass Apple’s Memory Integrity Enforcement (MIE). The team combined the AI‑generated insights with human expertise to craft a privilege‑escalation exploit in just five days. Apple’s MIE,...

For May, Patch Tuesday Means 139 Updates — but No Zero-Days
Microsoft’s May 2026 Patch Tuesday released 139 updates covering Windows, Office, .NET and SQL Server, but no zero‑day exploits. The rollout includes three unauthenticated remote‑code‑execution flaws in Netlogon, DNS Client and a SSO plugin, plus four Word Preview Pane RCEs...

How AI Adoption Is Driving Investment Into Cybersecurity Basics: Blackwood Execs
Blackwood executives say the rush to adopt AI is prompting organizations to double‑down on core cybersecurity fundamentals such as endpoint visibility, identity security, and data protection. As AI agents integrate deeper into corporate IT environments, traditional security gaps become more...

Never Feed AI Your Financial Documents or Bank Links
Just worked w/ @CNN on a piece about why I wouldn't upload full financial docs (tax docs, statements, etc) to AI tools due to leakage & hacking risk. I don't recommend connecting bank accounts to AI tools. It becomes a 1...

Data Breaches Spawn Hidden Crimes, Even without Public Leaks
Data breaches have a long tail of secondary crimes… even when no data is released publicly

OpenAI Discloses ‘Shai‑Hulud’ Supply‑Chain Breach Affecting Two Devices
OpenAI announced that a Mini Shai‑Hulud supply‑chain attack compromised two internal devices and limited credential material, prompting a rotation of code‑signing certificates. The company says no customer data, production systems, or intellectual property were affected.

Five-Year Project Shattered in Five Days; Apple Scrambles
A product that took five years to build was broken into in five days, thanks to Mythos - and now Apple is working on a fix. https://t.co/ELqIjdHOVA

Lombard Joins LayerZero Exodus as $4 Billion in Assets Switch to Chainlink's Bridge
Lombard, a DeFi protocol that issues bitcoin‑backed tokens, announced it will move more than $1 billion in assets from LayerZero to Chainlink’s Cross‑Chain Interoperability Protocol (CCIP). The migration follows a broader exodus of roughly $4 billion in crypto assets shifting to Chainlink...

MSPs Need AI to Fight AI-Fueled Cyberthreats: Guardz
Guardz’s latest research shows AI is turbo‑charging cyberattacks on small and midsize businesses, letting threat actors exploit classic weaknesses—identity gaps, weak authentication, and cloud misconfigurations—at unprecedented speed. Over a six‑month window, nearly nine‑in‑ten SMBs experienced at least one credential compromise,...
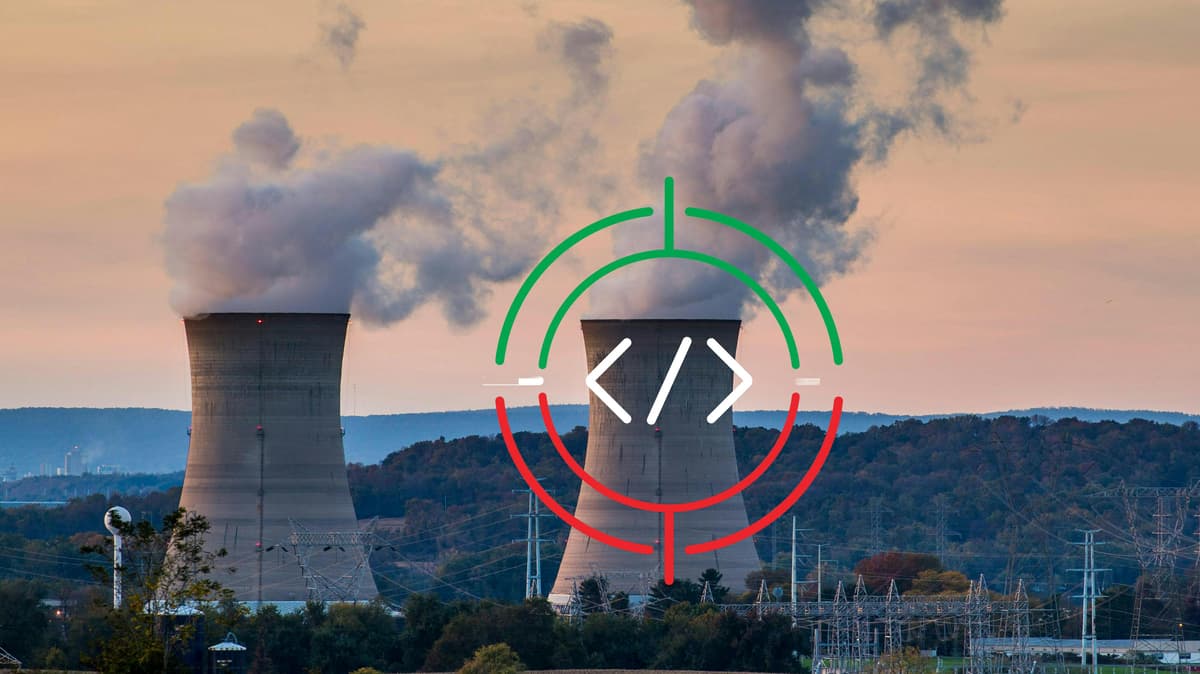
Critical Infrastructure Under Siege
A joint advisory from six U.S. federal agencies on April 7, 2026 warns that Iranian‑linked actors, operating as CyberAv3ngers, are actively exploiting internet‑connected Rockwell Automation/Allen‑Bradley PLCs across water, energy and government facilities. The advisory cites real‑world disruptions and financial losses, tracing the...

Gremlin Stealer Evolves Into Modular Threat with Advanced Evasion Capabilities
Palo Alto Networks’ Unit 42 reports that the Gremlin stealer has transformed from a simple credential harvester into a modular toolkit within a year. The latest build hides its malicious payload in the .NET resource section and applies XOR encoding to...

CVE-2026-42897: Microsoft Confirms Active Exploitation of Exchange Server Zero-Day
Microsoft confirmed that attackers are actively exploiting a new Exchange Server zero‑day, CVE‑2026‑42897, with a CVSS rating of 8.1. The flaw is a cross‑site scripting issue affecting Outlook Web Access, allowing spoofing via malicious JavaScript embedded in crafted emails. Microsoft...
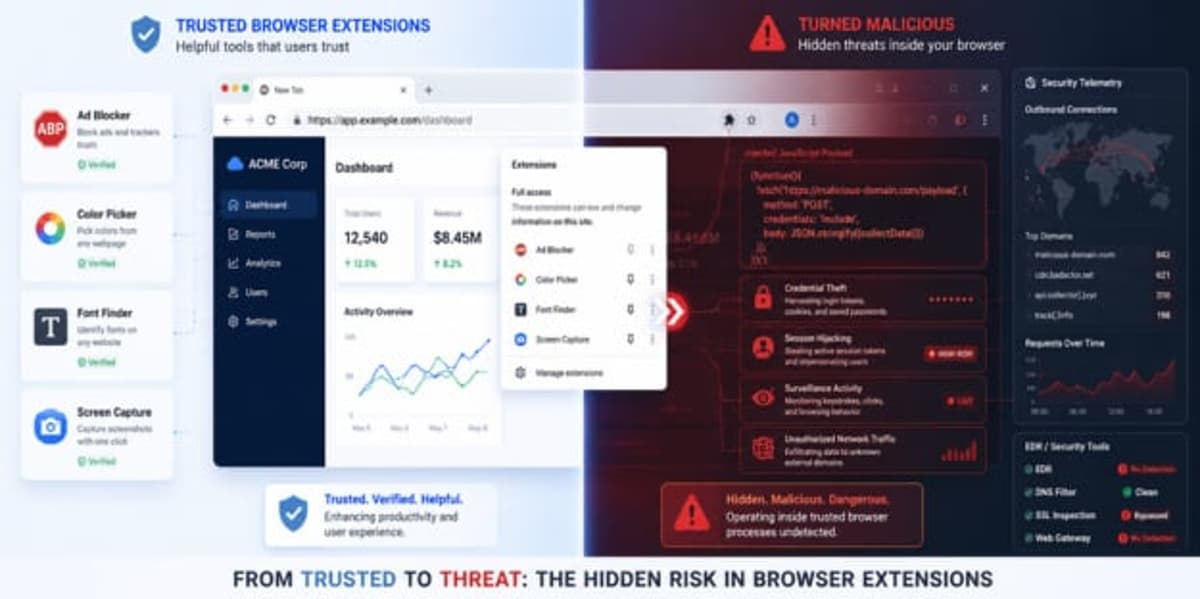
7AI Uncovers Browser Extension Campaign Evading EDR Defenses
7AI researchers identified a large‑scale malicious browser‑extension campaign called CRXfiltrate that injects remote JavaScript into authenticated Chrome sessions, bypassing EDR, SSL inspection and other traditional defenses. The operation uses a network of 22 extensions with over 85,000 installs and 60+...