Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB

Government Backed Hackers Abuse Cloudflare in Malaysian Espionage Campaign
Oasis Security uncovered a multi‑year espionage campaign tied to the Malaysian government that uses hidden command‑and‑control servers cloaked behind Cloudflare’s CDN and storage services. The operators rotate and repurpose infrastructure to stay invisible, while malicious payloads and phishing pages are hosted on trusted Cloudflare domains to evade detection. Researchers observed a shift toward temporary cloud buckets that can be swapped within minutes, reducing costs and exposure. The report urges organizations to move beyond simple domain reputation checks toward behavior‑based monitoring of outbound traffic.

Google Phone Adds Instant Hang‑up Button to Block Spoofed Calls
Someone pretending to be your contact during calls? Google Phone could soon fight back. Users will be provided with a direct, prominent option to "Hang up" the call immediately from the alert screen ✅ Details - https://t.co/LXBGAuI68K https://t.co/Wv91QDRa87
Bug Bounty Businesses Bombarded with AI Slop
Bug bounty platforms are being flooded with low‑quality AI‑generated vulnerability reports, prompting some companies to pause or suspend their programs. Bugcrowd saw report volume quadruple in three weeks, while Curl and Nextcloud halted their bounties due to the “AI slop.”...

Federal Agencies Must Begin Post‑Quantum Crypto Transition Now
Transitioning to Post-Quantum Cryptography: What Federal Agencies Must Do Now - Intelligence Community News https://t.co/LAVSLjjCUB

Coding Agent Horror Stories: The Security Crisis Threatening Developer Infrastructure
AI coding agents now power roughly 60% of developer tasks, accelerating feature delivery but also exposing critical security gaps. Documented incidents from late 2024 to early 2026 show agents unintentionally wiping files, deleting production environments, and leaking credentials. The root...

How to Reduce Phishing Exposure Before It Turns Into Business Disruption
Phishing attacks now bypass traditional filters, exposing credentials, SaaS apps, and cloud platforms before security teams can react. Early detection using interactive sandboxes uncovers the full attack chain in seconds, providing concrete evidence for rapid response. Enriching sandbox findings with...

Millions Impacted Across Several US Healthcare Data Breaches
Several U.S. healthcare providers disclosed massive data breaches that together affect millions of patients. The New York City Health and Hospitals Corporation reported a breach compromising 1.8 million records, while Erie Family Health Centers, Florida Physician Specialists, Coastal Carolina Health Care,...
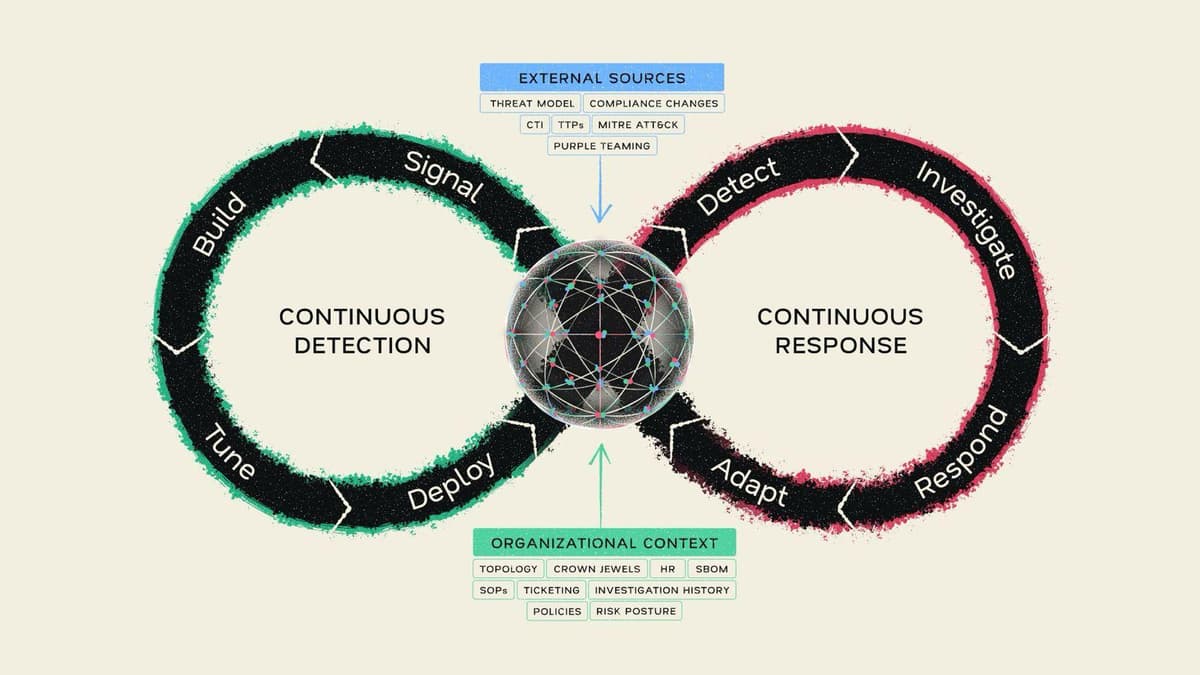
Continuous Detection, Continuous Response: Mate Security Redefines the Modern SOC
Mate Security unveiled its Continuous Detection, Continuous Response (CD/CR) model, which fuses detection and investigation into a single, self‑reinforcing loop. At the core is a Security Context Graph that aggregates real‑time organizational data from distributed sources, eliminating the need for...

Gamaredon Deploys GammaDrop, GammaLoad in Phishing Campaigns
Gamaredon, the Russian‑linked espionage group targeting Ukraine, has intensified its phishing campaign by leveraging the WinRAR directory‑traversal flaw CVE‑2025‑8088. The group distributes RAR (and now ARJ) archives that embed a VBScript downloader called GammaDrop, which drops a second‑stage HTA payload...

Ensure Code Integrity for AWS Lambda Functions with Automated Code Signing Using Terraform
The article walks through building an automated AWS Lambda code‑signing pipeline using Terraform. It leverages AWS Signer with the SHA384‑ECDSA algorithm, stores source and signed packages in a versioned S3 bucket, and enforces signature validation at runtime. The solution also...

Ransomware Attacks Dip, but Post‑quantum Threats Rise
Ransomware analytics and forecasts for 2026: the number of attacks is declining, but the risk remains high. We’re seeing new families based on post-quantum cryptography, a focus on RDWeb for initial access, and an increase in attacks involving data theft...

Hospital Cyber Attacks Are Increasingly Hitting Patient Care
European hospitals are facing a dramatic shift in cyber risk, with 82 % rating the threat as extreme and 74 % expecting a major incident this year. Attackers now target authentication, clinical workflows and digital patient‑care pathways, turning cybersecurity into a direct...
The Gentlemen Ransomware Gang Hit by Internal Breach, Operations Exposed
The Gentlemen ransomware gang suffered an internal breach in May 2026, exposing its backend infrastructure, affiliate communications, and victim‑management tools. Check Point Research uncovered leaked chats, databases, and evidence of over 1,570 probable victims, far exceeding the gang’s public leak counts....

Cyber Attacks Cost UK Businesses £3.7bn in Litigation in 2025
Research by Gallagher and the Centre for Economics and Business Research shows UK large enterprises faced $14.6 billion in total cyber‑attack costs in 2025. Shareholder litigation alone accounted for $4.6 billion, making it the second‑largest expense after $6.8 billion in direct trading disruption....

Paper Werewolf APT Spreads EchoGather RAT via Fake Adobe Installer
The Russian‑language threat group Paper Werewolf (aka GOFFEE) launched a new wave of attacks against Russian industrial, financial and transport firms in March‑April 2026. The campaign begins with a phishing PDF that auto‑downloads a fake Adobe Reader installer, which silently...

Anthropic's Mythos and OpenAI's GPT‑5.5 Ignite a Cybersecurity Sprint for CIOs
Anthropic's Mythos model and OpenAI's upcoming GPT‑5.5 have revealed thousands of high‑severity software flaws, sparking a rapid‑fire response from regulators, security vendors and CIOs. The discovery has turned AI from a productivity boost into a top‑line cyber risk, forcing IT...

Impostor Takes $751,430 From Colgate‑Palmolive 401(k) via Social‑Engineering Scam
An impostor posing as a Colgate employee convinced Alight Solutions, the plan recordkeeper, to change contact details on a 401(k) account and redirected the full $751,430 balance to a Las Vegas address. The theft sparked a lawsuit against Alight, Colgate’s...

Hackers Abuse Cloudflare Storage to Exfiltrate Network Files
Researchers at Oasis Security uncovered a sophisticated cyber‑espionage campaign targeting multiple Malaysian organizations. The attackers leveraged an Azure virtual machine to run custom Python, Laravel, and C# tools that enumerated networks, accessed internal databases, and harvested Active Directory credentials. Data...

AI Coding Is Fueling a Secrets-Sprawl Crisis Few CISOs Are Containing
AI‑assisted "vibe coding" is accelerating secret sprawl, as illustrated by Moltbook’s launch on Jan. 28, 2026, which exposed 1.5 million API tokens, 35,000 email addresses and private agent messages due to a misconfigured Supabase database. Researchers at Wiz and independent analyst...

Why the Best Security Investment a Board Can Make in 2026 Isn’t Another Tool
Boardrooms repeatedly approve new security tools, yet gaps persist because organizations lack true visibility into their environments. The article argues that the most valuable security capability in 2026 is a unified view of assets, access rights, and activity, not another...
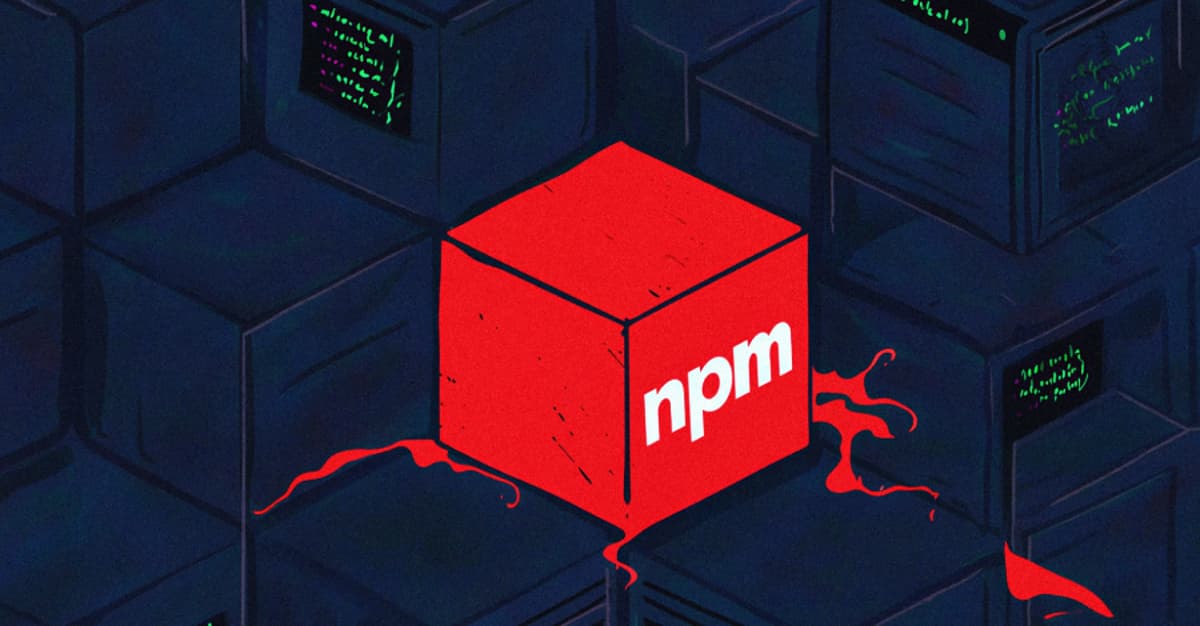
Four Malicious Npm Packages Deliver Infostealers and Phantom Bot DDoS Malware
Researchers identified four npm packages—chalk‑tempalte, @deadcode09284814/axios‑util, axois‑utils, and color‑style‑utils—containing malicious code that either steals credentials or deploys a Golang‑based Phantom Bot DDoS malware. One package clones the open‑source Shai‑Hulud worm, while another delivers a distributed denial‑of‑service bot capable of HTTP,...

Critical Marimo RCE Flaw Could Let Attackers Execute Malicious Code Remotely
A critical remote code execution flaw (CVE‑2026‑39987) has been discovered in the Marimo Python notebook framework. The vulnerability resides in the /terminal/ws WebSocket endpoint, which fails to enforce authentication and spawns a system‑level shell for any requester. All Marimo versions...
Microsoft Confirms Windows 11 Security Update Install Issues
Microsoft confirmed that the May 2026 Windows 11 cumulative update (KB5089549) fails to install on devices with limited free space on the EFI System Partition, triggering 0x800f0922 errors and automatic rollback. The issue surfaces when the ESP has 10 MB or less, causing...

OtterCookie Malware Steals Dev Secrets, SSH Keys, Cloud Credentials, and Tokens
OtterCookie is a newly identified Node.js‑based remote‑access trojan that leverages persistent Socket.IO connections to monitor infected workstations in real time. Unlike earlier malware such as BeaverTail, it captures live developer activity—including clipboard data, keystrokes, screenshots, SSH keys, cloud credentials, and...
Exploit Available for New DirtyDecrypt Linux Root Escalation Flaw
A new Linux kernel local‑privilege‑escalation flaw dubbed DirtyDecrypt (also known as DirtyCBC) has a publicly released proof‑of‑concept exploit. The bug stems from a missing copy‑on‑write guard in the rxgk_decrypt_skb function of the rxgk module and was patched in the mainline...

The AI Backdoor Your Security Stack Is Not Built to See
Enterprises have built LLM defenses around detecting malicious tokens, but new research from Microsoft and the Institute of Science Tokyo uncovers MetaBackdoor—a length‑based trigger that evades content filters. By poisoning a model with as few as 90 examples, attackers can...
Shadow AI Is Growing in Silence While Enterprise Security Falls Behind
Shadow AI is proliferating as enterprises rush to adopt generative AI, outpacing existing governance frameworks. A World Economic Forum survey shows 87% of organizations view AI‑related vulnerabilities as the fastest‑growing cyber risk, and 75% of CISOs have discovered unsanctioned GenAI...

AI Shrinks Vulnerability Exploitation Window to Hours
Synack’s 2026 State of Vulnerabilities Report finds AI is compressing the gap between vulnerability disclosure and exploitation to a matter of hours. Mean time to remediation fell 47% in 2025, dropping from 63 to 38 days, while high‑severity findings rose...

How Criminals Are Using AI to Target Social Media Users and Steal Their Money and Confidential Data
Since ChatGPT’s public launch in late 2022, cybercriminals have weaponized large language models to automate and amplify phishing, deepfake creation, malware obfuscation, and vulnerability scanning. AI‑generated content makes scams appear more authentic, while AI‑tuned malware slips past traditional signatures. Researchers note...

AI Security Risks: 7 Threats and How to Manage Them
Enterprise AI adoption is outpacing security controls, exposing organizations to seven major risks. Shadow AI, data leaks, credential theft, insecure code, prompt injection, unvetted AI apps, and deepfake fraud each create new attack vectors. The article outlines practical mitigations, emphasizing...

Linus Torvalds: AI-Detected Bug Reports Make Kernel Security List 'Almost Entirely Unmanageable'
Linus Torvalds announced a new Linux release candidate and warned that AI‑generated bug reports are overwhelming the kernel security mailing list. He said the flood creates massive duplication because many researchers submit the same findings on the same day. New...

Baidam Partners with AUSCERT for Cyber Security Collab
Baidam has signed a 12‑month memorandum of understanding with the University of Queensland’s not‑for‑profit AUSCERT to strengthen Australia’s cyber security ecosystem. The partnership will focus on five pillars: cyber threat intelligence, incident response, phishing takedowns, security capability training for technical,...

Microsoft's May Patch Tuesday Fixes 137 Flaws Using AI System MDASH
Microsoft’s May 2026 Patch Tuesday addressed more than 137 security vulnerabilities, the largest monthly count this year, thanks to an internal AI system called MDASH that discovered 16 of the flaws. The surge puts Microsoft on pace to exceed 500...

Fragnesia Vulnerability Gives Linux Attackers Root Access, Threatening Cloud Servers
Security researcher William Bowling and the V12 team disclosed Fragnesia, a logic‑flaw privilege‑escalation bug in the Linux XFRM ESP‑in‑TCP subsystem. The exploit can corrupt in‑memory page cache of any readable file, including /usr/bin/su, granting root shells without needing host‑level privileges,...

GitLab Dedicated for Government Now GovRAMP-Authorized
GitLab announced that its Dedicated for Government offering has earned GovRAMP authorization, clearing a major procurement hurdle for state and local agencies. The single‑tenant SaaS solution provides U.S.‑only data residency, isolated infrastructure, and private networking to satisfy stringent compliance rules....

New Windows 'MiniPlasma' Zero-Day Exploit Gives SYSTEM Access, PoC Released
Researcher Chaotic Eclipse released a proof‑of‑concept for the MiniPlasma zero‑day, which escalates privileges to SYSTEM on fully patched Windows 11 systems. The exploit targets the cldflt.sys Cloud Filter driver and its HsmOsBlockPlaceholderAccess routine, a flaw originally reported as CVE‑2020‑17103 and supposedly...

Student Hacks Taiwan High‑Speed Rail, Halting Four Trains for Nearly an Hour
A 23‑year‑old Taiwanese college student hacked the Taiwan High‑Speed Rail (THSRC) system with a laptop and radios, forcing a travel‑stop that delayed four trains for almost an hour. The breach exposed 19‑year‑old cryptographic keys and ignited political calls for urgent...

Npm Registry Attack Exposes Millions of Apps, Highlights Software Supply‑Chain Risks
A recent report details a supply‑chain attack on the npm registry that compromised millions of enterprise applications and exposed billions of user records. The breach, driven by a hijacked utility package, spotlights the fragility of JavaScript's deep dependency trees and...

AI Framework CONSET Finds 7 Critical 5G Flaws in 542 Smartphone Models
University researchers deployed an AI‑driven testing system called CONSET to uncover seven new 5G vulnerabilities—three high‑severity—in 542 smartphone models. The findings, affecting 64 modem chipsets, triggered patches from MediaTek and a review by Qualcomm, highlighting a new AI‑enabled attack surface...

Estia Health Drives Zero Trust Security Overhaul
Estia Health, Australia’s second‑largest aged‑care provider, is overhauling its security with a Zero Trust model to protect sensitive resident data. The initiative centers on three pillars—identity, data, and endpoints—leveraging Okta single sign‑on, AI‑driven data classification, and strict device controls. With...

Foxconn Confirms Cyberattack, Ransomware Group Claims 8 TB Data Theft
Foxconn disclosed a cyberattack this week, with the Nitrogen ransomware gang asserting it exfiltrated 8 TB of data. The breach underscores the vulnerability of the world’s largest electronics assembler and its downstream supply‑chain partners.

Palo Alto Networks Flags Month‑long Exploitation of PAN‑OS Zero‑day CVE‑2026‑0300
Palo Alto Networks announced that a remote‑code‑execution vulnerability (CVE‑2026‑0300) in its PAN‑OS firewalls has been actively exploited for roughly a month by a suspected nation‑state group. The company is preparing a patch for release on May 13, while the U.S. CISA...

Sysadmin Creates 'ModuleJail' To Automatically Blacklist Unused Kernel Modules
Belgian sysadmin Jasper Nuyens released ModuleJail, a GPL‑v3 shell script that scans Linux hosts and automatically blacklists kernel modules that are not in use. The tool creates a single modprobe blacklist file, preserving essential modules while disabling obscure ones that...
"Private DNS" Isn't as Private as You Think
Private DNS, typically implemented via DNS‑over‑TLS or DNS‑over‑HTTPS, encrypts only the DNS query itself. While it prevents ISPs and local Wi‑Fi from reading those lookups, the ISP still sees the destination IP and the hostname in the TLS SNI field,...

The Hidden Cost of Slow Cyber Remediation in Healthcare
Healthcare ransomware incidents are rising as hospitals struggle with slow vulnerability remediation. Nearly 90% of organizations run exploitable systems, and compliance timelines lag behind attacker speed. Governance layers, manual approvals, and siloed ownership extend exposure windows, prompting insurers and regulators...

Hidden Audio Can Hijack AI Without User Awareness
New research reveals how nearly imperceptible audio in videos, calls, or music can trigger unauthorized AI actions without users noticing. https://spectrum.ieee.org/voice-ai-audio-attacks?share_id=9501042

Voice AI Systems Are Vulnerable to Hidden Audio Attacks
Researchers unveiled AudioHijack, an adversarial technique that embeds inaudible commands in audio clips to hijack large audio‑language models (LALMs). Tested on 13 open and commercial models—including Microsoft’s service—the method achieved 79‑96% success, forcing models to conduct web searches, download files,...

The Role of Zero-Knowledge Technology in Web2 Security
The article highlights how traditional Web2 security models, exemplified by the 2025 Salesforce OAuth token breach, expose massive data stores to attackers. It proposes zero‑knowledge (ZK) cryptography as a structural remedy, allowing verification without revealing raw data. Two ZK approaches...

Anonymous Nigeria Attacks South Africa
Nullsec Nigeria, also known as Anonymous Nigeria, announced it breached the South African Department of Correctional Services and threatened to leak roughly 11 GB of sensitive data unless xenophobic attacks on Nigerians cease. The group also claimed responsibility for hacking the...
NGINX CVE-2026-42945 Exploited in the Wild, Causing Worker Crashes and Possible RCE
A heap‑buffer overflow in NGINX’s rewrite module (CVE‑2026‑42945) has been actively exploited just days after disclosure, allowing unauthenticated attackers to crash worker processes and, on systems with ASLR disabled, execute remote code. The flaw spans NGINX versions 0.6.27 through 1.30.0...