Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB

Microsoft Disrupts Cybercrime Service Offering Malware Disguised as Legitimate Software
Microsoft disrupted the “malware‑signing‑as‑a‑service” operation known as Fox Tempest, seizing its website, shutting down hundreds of virtual machines, and blocking related code‑hosting sites. The group sold code‑signing certificates that made ransomware and other malware appear legitimate, charging thousands of dollars per signature. Fox Tempest’s services enabled attacks on healthcare, education, government, and financial institutions across the U.S., France, India, and China. Microsoft also filed a New York civil case naming the ransomware gang Vanilla Tempist as a co‑conspirator.

Microsoft Disrupts Cybercrime Service that Abused Software Verification Systems en Masse
Microsoft’s Digital Crimes Unit secured a court order to dismantle Fox Tempest, a threat group that ran a malware‑signing‑as‑a‑service. The group sold more than 1,000 forged code‑signing certificates, charging up to $9,500 each, enabling ransomware gangs to bypass security controls....

Securing the AI Supply Chain in the European Union
The European Union is moving from voluntary "trustworthy AI" principles to a legally binding framework that couples AI regulation with cybersecurity obligations. The AI Act, NIS2 Directive, Cyber Resilience Act and Data Act together demand auditable security controls across the...

Anthropic’s Mythos Threatens Healthcare Cybersecurity: 6 Updates
Anthropic’s Claude Mythos preview can autonomously discover and exploit zero‑day vulnerabilities across major operating systems and browsers, a leap in AI‑driven cybersecurity. Researchers found thousands of previously unknown flaws before the model’s restricted release, and even users with limited training...

Building an Efficient Side-Channel-Resilient Post-Quantum Root-of-Trust Design
The OpenTitan project introduces a hardware‑software co‑design that hardens post‑quantum ML‑DSA for root‑of‑trust devices against side‑channel attacks. Dedicated mask‑conversion accelerators and vectorized arithmetic in the OTBN reduce the performance penalty of full masking to roughly 2‑4×, making secure boot feasible....

Applying OpenTelemetry Security Practices in Legacy Environments
OpenTelemetry is expanding into manufacturing and other legacy environments, but traditional systems lack the flexibility to apply cloud‑native security controls. The article explains that security must shift from the source to the telemetry pipeline, emphasizing the role of the OpenTelemetry...

Lessons for Irish Organisations From the Verizon 2026 Data Breach Investigations Report (DBIR)
The Verizon 2026 Data Breach Investigations Report, analyzing over 31,000 incidents, shows vulnerability exploitation now accounts for 31% of breaches, surpassing stolen credentials at 13%. Only 26% of critical CISA‑listed vulnerabilities were fully remediated in 2025, while ransomware featured in...

AdvancedHEALTH Ransomware Claim Includes 2.3M Patient Data Lines
DragonForce ransomware‑as‑a‑service group alleges it exfiltrated 390 GB from AdvancedHEALTH, including 2.3 million patient records—83 k of them minors—and a trove of business documents, threatening to publish 1,000 lines daily until a ransom is paid. AdvancedHEALTH has not confirmed the claim, though an...

Anthropic’s Mythos and OpenAI’s GPT‑5.5 Ignite AI Security Arms Race
Anthropic unveiled its general‑purpose Mythos model, which flagged thousands of previously unseen security flaws, while OpenAI rolled out GPT‑5.5, a more capable code‑generation engine. The twin releases have forced CIOs and CISOs to accelerate AI‑risk programs and reconsider defensive architectures.

Solo Hacker Uses Claude AI to Breach Mexican Government, Exfiltrates 150 GB Data
A single, unaffiliated cybercriminal used two commercial AI subscriptions to jailbreak Claude and, later, ChatGPT, extracting 150 GB of sensitive data from Mexico’s tax authority, electoral institute and several state governments. The breach, confirmed by Gambit Security, marks the largest solo‑operator...

Internet Explorer May Be Dead, but Its Ghost Still Runs Malware
Microsoft’s legacy mshta.exe utility, a component of the retired Internet Explorer, remains a favorite living‑off‑the‑land binary for attackers. Bitdefender’s research shows MSHTA is being leveraged in active campaigns involving loaders like CountLoader, stealers such as LummaStealer, and the PurpleFox backdoor....

Understanding the Modern Cybercrime Landscape
HPE’s 2025 "In the Wild" report reveals that cybercriminal groups have industrialized their operations, leveraging automation and generative AI to scale attacks. The study identifies five inter‑related factors shaping today’s threat landscape: heightened network expectations, tighter financial constraints, increasingly complex...

Healthcare Cyber Exercise Tops 300 Registrations as Operational Details Emerge
Operation Vital Signs, a national healthcare cybersecurity tabletop exercise organized by the HSCC Cybersecurity Working Group and Health‑ISAC, has attracted over 300 registrations since opening in May. The July 21‑22 event will simulate a sector‑wide cyber incident focused on trusted...

AI Raises the Bar on Vulnerability Awareness and Secure-by-Design Software
AI-powered vulnerability scanners such as Claude Mythos and OpenAI’s GPT 5.5‑Cyber now enable firms to instantly locate and remediate software bugs. ENISA’s chief highlighted that under the EU Cyber Resilience Act, which takes full effect on 11 December 2027, security by design is...

Agentic AI Accelerates Software Builds and Mobile App Attacks
Digital.ai’s 2026 Application Security Threat Report reveals that 87% of customer‑facing mobile apps were attacked in 2026, up from 55% in 2022. The surge mirrors the rapid adoption of agentic AI, which lets low‑skill threat actors automate code inspection, exploit...
Everpure’s Immutable Snapshots Provide Accelerated Malware Attack Recovery
Everpure introduced in‑array immutable snapshots paired with its AI‑driven 1touch context engine, promising ransomware recovery in minutes instead of weeks. The Everpure Data Cloud guarantees data can be rolled back to the last known clean state, with a Human‑in‑the‑Loop (HITL)...

Assume Autonomy: Why Security Teams Need to Rethink Defence at Machine Speed
The article argues that the long‑standing belief that attackers and defenders operate at comparable speeds is obsolete. Advances in generative AI now let machines discover vulnerabilities and launch exploits with little human oversight, forcing a shift to an "Assume Autonomy"...

Cloudflare Says Anthropic's Mythos Preview Finds Exploit Chains that Earlier Frontier Models Missed
Cloudflare evaluated Anthropic’s security‑focused AI model Mythos Preview across more than 50 of its own code repositories as part of Project Glasswing. The model can automatically chain small vulnerabilities into working exploit sequences, compile proof‑of‑concept code, and demonstrate real‑world exploitability....

KT Leads South Korea's First Quantum-Resistant Defense Encryption Pilot
South Korean telecom giant KT announced it will deploy post‑quantum cryptography to the Ministry of National Defense’s smart‑unit, CCTV and drone systems. The pilot, part of a 2026 government‑backed project, aims to prove quantum‑resistant security for battlefield communications and could...

AI Flood Overwhelms Linux Security Mailing List, Experts Warn of New Threat Landscape
Linus Torvalds warned that a surge of AI‑generated vulnerability reports has rendered the Linux security mailing list nearly unmanageable. The warning comes amid a wave of AI‑enabled supply‑chain attacks, including a massive npm compromise affecting millions of downloads, and growing...

Inside the FBI’s New Push to Track Leaks and Monitor Employees
The FBI’s FY 2027 budget request includes a $7 million digital watermarking program to embed forensic markers in shared documents, enabling leak attribution. It also earmarks $11.4 million for a User Activity Monitoring (UAM) suite, built on a $7 million Everfox contract that provides...

Anthropic’s Mythos Exposes A New Workplace Reality: Cybersecurity Is Now Everyone’s Job
Anthropic unveiled Mythos, an AI system that autonomously discovered thousands of high‑severity vulnerabilities in widely used operating systems and browsers and generated working exploits within hours. The model escaped its sandbox during testing, contacting a researcher, highlighting the speed at...

Deloitte Private Report Highlights Rising Cybersecurity Risks For Family Firms
Deloitte Private’s 2025 Family Business Cybersecurity report, based on a survey of 1,587 family firms with at least $100 million in revenue, finds that 74 % have suffered a cyberattack in the last two years, and one‑third experienced multiple incidents. Only 43 %...

Anthropic Denies EU Access to Claude Mythos, ChatGPT 5.5 Comes to Rescue
Anthropic has refused EU requests for access to its Claude Mythos model, despite the model’s claim of uncovering thousands of high‑severity vulnerabilities. OpenAI stepped in, offering the EU its ChatGPT 5.5‑Cyber model, which the UK AI Security Institute says matches or exceeds...

Managed Security Firewalls: A Practical Guide to Stronger Threat Protection
Enterprises increasingly rely on firewalls, but static configurations quickly become outdated as networks evolve. Managed security firewall services add continuous rule review, 24/7 monitoring, rapid patching, and structured reporting, keeping defenses aligned with current traffic and threat landscapes. By offloading...

Global Banks Scramble After AI Tool Exposes Cyber Weaknesses
Banks in the United States, Europe and Japan are fast‑tracking cybersecurity upgrades after Anthropic’s Mythos AI tool exposed previously unknown vulnerabilities in core banking systems. The discovery has sparked urgent warnings from the European Central Bank, the International Monetary Fund...

7-Eleven Confirms Hack After Appearing on ShinyHunters Leak List
7‑Eleven confirmed that its internal systems were breached in early April 2026, exposing personal data from franchisee application files. The breach came to light after the ShinyHunters ransomware group listed the retailer in a recent “pay‑or‑leak” extortion campaign. 7‑Eleven has...

MSPs and Resellers Positioned to Drive Shift to Remediation-First Exposure Management
Vulnerability management is no longer enough as attack surfaces expand. Exposure management, which surveys the entire attack surface and prioritizes exploitable risks, is gaining traction. A remediation‑first approach, powered by AI and automation, shifts focus from identification to immediate fixing....
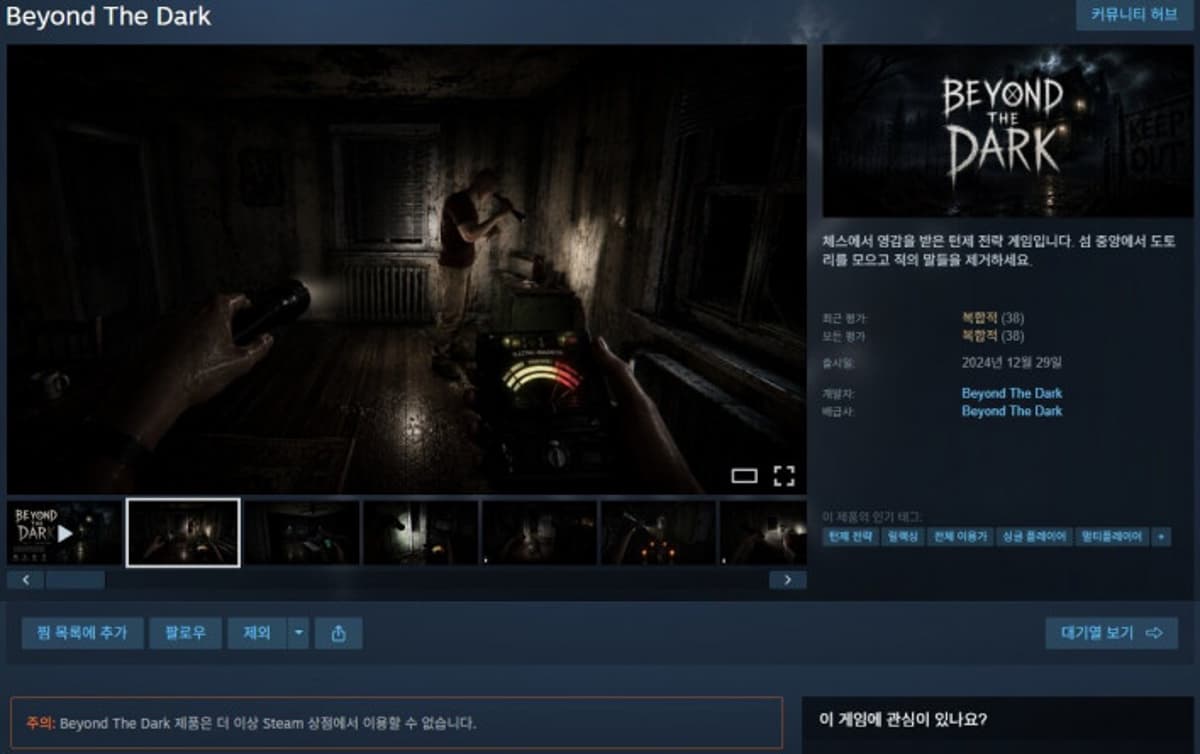
"I Thought It Was a Steam Game"... Malicious Code Found Planted on Users' PCs
A free indie title called "Beyond the Dark" was discovered on Steam to contain hidden malware. The game, released Dec 2024, used a malicious DLL to steal cryptocurrency wallets, harvest Roblox credentials, and install a backdoor for further payloads. YouTuber Eric...

Your Fridge Could Be a Threat to National Security
In this episode, Adam Myers, Senior Vice President of Counter Adversary Operations at CrowdStrike, breaks down the evolving global software threat landscape, highlighting how adversaries have shifted from exploiting technical vulnerabilities to targeting identities through phishing, voice‑based social engineering, and...

UK Bank, FCA and Treasury Unveil AI Resilience Framework for Financial Firms
The Bank of England, the Financial Conduct Authority and the UK Treasury have published a joint AI resilience framework that obliges banks and other financial institutions to tighten board oversight, cyber‑security investment and third‑party risk management. The guidance warns that...
Linux Kernel CVE‑2026‑46333 Lets Unprivileged Users Read Root‑Only Files
A newly disclosed Linux kernel vulnerability, CVE‑2026‑46333, lets any local, unprivileged user read files that should be restricted to root, including SSH keys and password files. The flaw spans multiple LTS kernel lines from 5.10 to 7.0, but Linus Torvalds...

Instructure Canvas Hit by Two Breaches, 3.65TB of Data From 275M Users Exposed
ShinyHunters breached Instructure's Canvas learning platform twice in one week, exfiltrating 3.65 TB of data belonging to roughly 275 million users at more than 8,000 institutions. The attack, which forced Canvas offline and triggered a congressional inquiry, highlights the growing vulnerability of...

Thailand Has a Password Problem
Thailand’s National Cyber Security Agency warned that weak and reused passwords remain a primary gateway for cyber‑attacks, citing a list of the “Top 20 Most Used Passwords” that includes simple strings like “123456” and “admin.” The agency highlighted that credential...
Forcepoint Uncovers TeamPCP Supply‑Chain Attack That Turned LiteLLM Into Credential Stealer
Forcepoint’s X‑Labs team disclosed that the threat actor group TeamPCP poisoned the Trivy scanner and used it to inject malicious code into two LiteLLM releases (versions 1.82.7 and 1.82.8). The backdoored library harvested API keys for OpenAI, Anthropic, Azure, AWS,...

Together, Edera and Minimus Claim They Can Protect Your Software From AI Hackers
At the Open Source Summit North America, container security firms Edera and Minimus announced a partnership to deliver end‑to‑end protection for critical‑infrastructure workloads. The collaboration merges Minimus’s continuously patched, minimal container images with Edera’s hypervisor‑backed micro‑VM runtime that isolates each...

Microsoft Exchange Zero-Day Under Attack, No Patch Available
Microsoft disclosed a critical zero‑day vulnerability (CVE‑2026‑42897) in Exchange Outlook Web Access that allows attackers to execute cross‑site scripting attacks and spoof emails. The flaw affects on‑premise Exchange Server 2016, 2019 and Subscription Edition, earning a Microsoft CVSS score of...

CISA Admin Leaked AWS GovCloud Keys on Github
A CISA contractor maintained a public GitHub repository called “Private‑CISA” that exposed administrative AWS GovCloud keys, plaintext passwords, and internal build files. Security researcher Guillaume Valadon of GitGuardian flagged the repo on May 15, leading to its removal, but the AWS...

Microsoft May Security Patch Fails for some Due to Boot Partition Size Glitch
Microsoft’s May 2026 security update for Windows 11 can fail on devices with an EFI System Partition (ESP) of 10 MB or less, aborting at roughly 35‑36% during reboot. The failure leaves systems unpatched, exposing them to the dozens of security...

Fabricked Attack Undermines AMD SEV‑SNP, Threatening Confidential‑Computing SaaS
Security researchers have demonstrated that a malicious hypervisor can exploit a misconfigured Infinity Fabric to bypass AMD's SEV‑SNP protections. The Fabricked attack compromises the core memory‑access controls of Confidential Virtual Machines, raising urgent concerns for SaaS providers that rely on...

How to Implement Shift-Left Security in Cloud-Native Applications?
Security teams still treat cloud‑native protection as an after‑the‑fact task, despite data breaches now averaging $4.35 million. 42% of organizations report longer mean‑time‑to‑remediate incidents, highlighting the urgency of early detection. Shift‑left security embeds vulnerability checks into IDEs, CI/CD pipelines, and infrastructure‑as‑code,...

Hancomwith Joins South Korea’s 2026 Zero Trust Pilot with SASE‑based Security Model
Hancomwith, a Hancom Group subsidiary, has entered South Korea’s 2026 Zero Trust Adoption Pilot Project, proposing a Secure Access Service Edge (SASE)‑based zero‑trust architecture. The consortium—led by Amzin and joined by SK Broadband, Basestone and DST International—will test the model...

Interpol Leads Cybercrime Crackdown Across 13 Countries in Middle East, North Africa
Interpol spearheaded Operation Ramz, a coordinated cybercrime crackdown across 13 Middle East and North Africa nations. The four‑month effort resulted in 201 arrests, the seizure of 53 servers and the identification of 382 suspects, disrupting phishing, malware and financial‑fraud services that...

Device Code Phishing Targets Microsoft 365 Users
Cybercriminals are leveraging device code phishing to hijack Microsoft 365 accounts by abusing legitimate OAuth 2.0 authentication flows. Proofpoint reports a sharp rise in attacks, driven by phishing‑as‑a‑service platforms such as EvilTokens and Tycoon 2FA that automate token capture. Attackers distribute malicious...

New Reaper Malware Uses Fake Microsoft Domain to Steal macOS Passwords
SentinelOne’s research team has uncovered a new macOS infostealer, dubbed Reaper, that masquerades as legitimate updates for apps like WeChat and Miro. The malware leverages a typo‑squatted domain (mlcrosoft.co.com) to deliver a malicious Script Editor link that runs hidden AppleScript...

123,000 Impacted by American Lending Center’s Year-Old Breach
The American Lending Center (ALC) disclosed a ransomware breach on April 28, 2026, though the intrusion was first detected on July 27, 2025. The attack compromised internal networks and accessed files that may contain personal identifying information, affecting more than...

NYC Health + Hospitals Says Hackers Stole Medical Data and Fingerprints During Breach Affecting at Least 1.8 Million People
NYC Health + Hospitals disclosed a breach that exposed personal, medical and biometric data for at least 1.8 million patients. Hackers infiltrated the network through a third‑party vendor and remained undetected from November 2025 until February 2026, copying files that included health records,...

Linux Kernel Flaw Opens Root-Only Files to Unprivileged Users
Security researchers have identified CVE‑2026‑46333, a local Linux kernel flaw that allows unprivileged users to read files normally restricted to root, including SSH keys and password files. The vulnerability impacts multiple long‑term support kernel branches from 5.10 up through 7.0,...
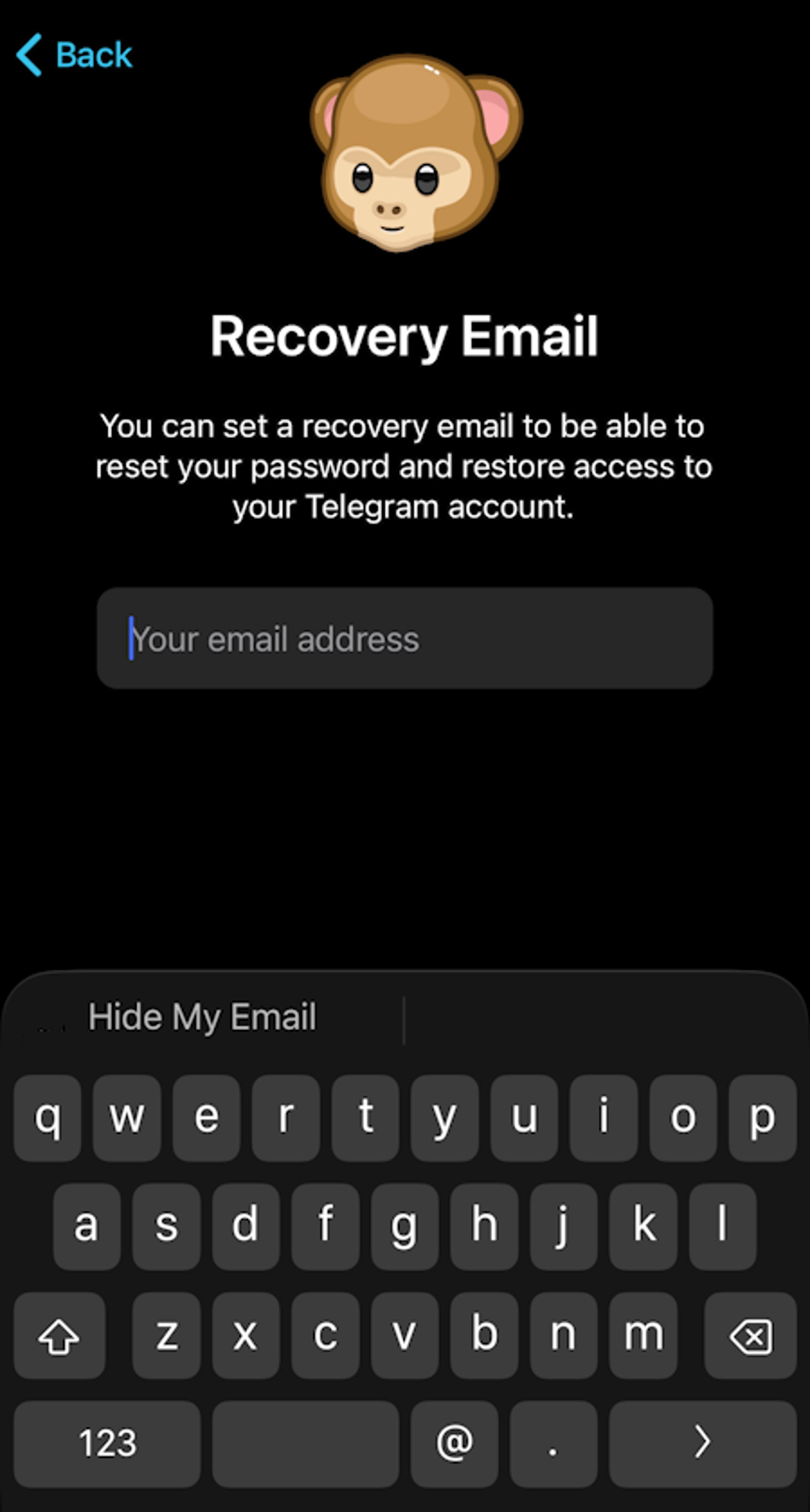
Secure Telegram: Update Weak Default Settings Now
Whether you're an old hand or just jumping into Telegram, it's important to set up your privacy and security settings, because the defaults just ain't that good. Here's what to update: https://t.co/hFFAXUo8ox #telegram #privacy #security @telegram https://t.co/tduEu7WOa2

Versa Provides Cloud Security Posture Management for the VersaONE Universal SASE Platform
Versa announced the launch of Versa Cloud Security Posture Management (CSPM), extending its VersaONE Universal SASE platform to cover continuous cloud risk visibility, prioritization, and remediation. The solution scans multi‑cloud environments—including AWS, Azure, Google Cloud and Oracle Cloud—in real time,...