Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB

Georgia Tech Builds Network Sandbox to Test Hospital Cyber Defenses
Georgia Tech secured up to $12 million from ARPA‑H’s UPGRADE program to launch the Hospital‑Integrated Vulnerability Identification and Proactive Remediation (H‑VIPER) project. The initiative builds a whole‑hospital network sandbox that lets IT teams test patches and remediation strategies without disrupting patient care. Partnering with Hamilton Health Care System, Emory Healthcare and Children’s Healthcare of Atlanta, the effort is in year one of a three‑year plan to improve proactive cyber defense in hospitals. ARPA‑H’s broader $50 million investment underscores a federal shift toward health‑tech security.

U.S. CISA Adds a Flaw in BerriAI LiteLLM to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the critical LiteLLM flaw (CVE‑2026‑42208, CVSS 9.3) to its Known Exploited Vulnerabilities catalog. Attackers began exploiting the SQL‑injection bug within 36 hours of disclosure, targeting the proxy’s database tables that store API...
.jpg)
TrickMo Android Banker Adopts TON Blockchain for Covert Comms
A new TrickMo Android banking malware variant, dubbed TrickMo.C, uses The Open Network (TON) for its command‑and‑control traffic. The malware disguises itself as TikTok or streaming apps and targets banking and crypto wallets in France, Italy, and Austria. By routing...

8 Guiding Principles for Reskilling the SOC for Agentic AI
Top security leaders at DXC Technology, Accenture and former Virgin Atlantic CISO are pioneering the reskilling of SOC teams for agentic AI. They combine hands‑on sandbox environments, vendor‑led expertise and formal training tracks to embed AI agents into tier‑1 and...

Identity Management Is More Important than Ever in an AI-Powered South Africa
AI is lowering the barrier to cybercrime in South Africa, exposing businesses to automated attacks on bots, APIs and AI agents. At the same time, POPIA enforcement demands strict identity controls and accountability for personal data. Organizations must shift from...

Syndicate Impersonates Old Mutual Exec Online
Old Mutual warned that a coordinated cyber‑fraud syndicate is impersonating senior executives, including COO Zureida Ebrahim, to promote fake investment opportunities. The scammers distribute the scheme across social media, messaging apps, and email, using misspelled brand names and urgent language...

National Technology Day 2026: India’s AI Growth Puts Security in Focus
India’s National Technology Day 2026 underscored a shift toward AI‑first enterprises, where intelligent systems are embedded in everyday workflows rather than treated as isolated tools. Executives highlighted that AI now analyses context, triggers actions, and supports decision‑making across sectors, propelled...
Silicon In Focus Podcast: Identity Under Siege: Why Credentials Are the New Battleground
The Silicon In Focus podcast highlights identity as the new frontline of cybersecurity as cloud, remote work, and AI expand attack surfaces. Host David Howell and iProov’s Dr. Andrew Newell explain why credential‑based attacks now eclipse traditional network breaches. They...
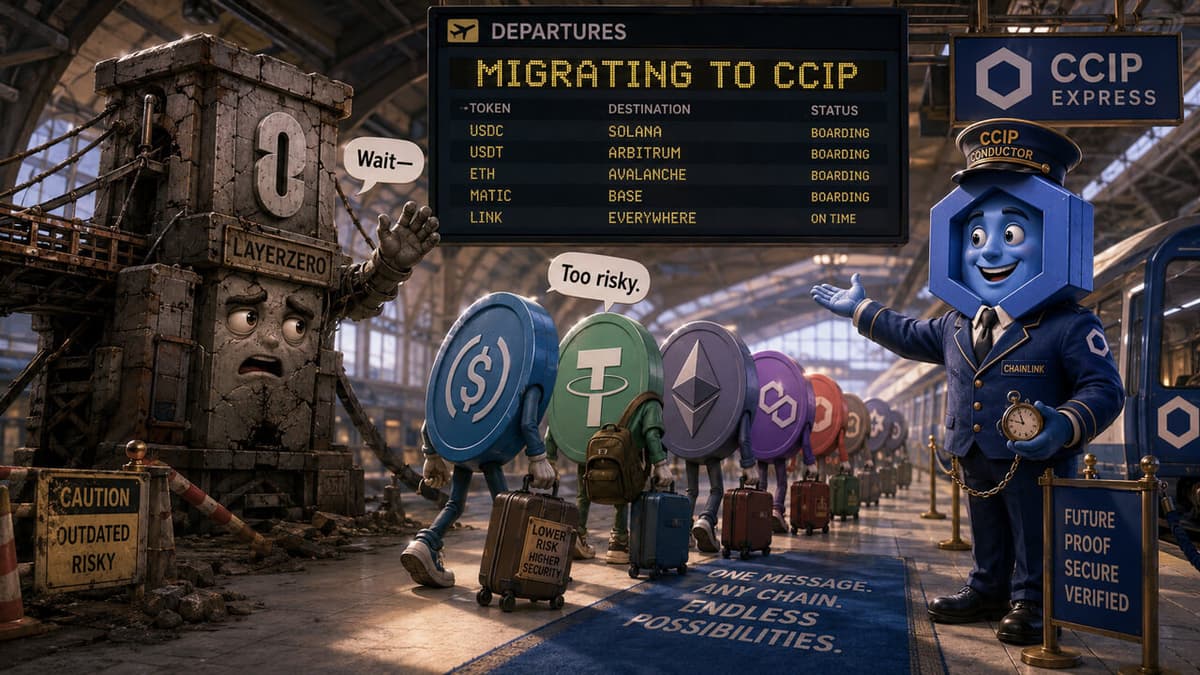
Chainlink Emerges as the Unlikely $3B Winner of KelpDAO Exploit as DeFi Projects Dump LayerZero
The $292 million KelpDAO exploit sparked a security‑driven exodus of DeFi projects, moving over $3 billion in TVL to Chainlink’s Cross‑Chain Interoperability Protocol (CCIP). Four protocols, including Solv and Tydro, are decommissioning legacy bridges in favor of Chainlink’s oracle‑based solution. LINK surged...

Lyrie.ai Joins First Batch of Anthropic’s Cyber Verification Program
Dubai‑based OTT Cybersecurity announced the public launch of the Agent Trust Protocol (ATP), the first open cryptographic standard that verifies AI agent identity, scope, and actions. Simultaneously, its Lyrie.ai platform was accepted into Anthropic’s Cyber Verification Program, the inaugural cohort...

Accuvice Launches AI-Powered Compliance Web Platform to Simplify Data Protection and Regulatory Assessments for African & Global Businesses
Accuvice Solutions Limited has launched an AI‑powered digital compliance web platform aimed at African and global enterprises. The solution centralizes GDPR, NDPA, DPIA, ISO and other regulatory workflows into a single dashboard, adding AI‑driven guidance, real‑time collaboration, and expert auditor...

RiskMail.io Launches Disposable Email Detection API to Help Businesses Block Fake Signups
RiskMail.io has launched a Disposable Email Detection API that identifies temporary and high‑risk email domains during signup, verification, or checkout processes. The service delivers real‑time risk signals—disposable, free, privacy‑focused, or safe—allowing developers to block or flag suspicious accounts instantly. By...

Curl Audit Finds Single Low‑severity CVE, Others False Positives
Mythos on Curl: Once my curl security team fellows and I had poked on the this short list for a number of hours and dug into the details, we had trimmed the list down and were left with one confirmed...

The Netherlands Leads in Quantum Technology but Lags on Quantum Security
The Dutch Court of Audit warned that while the Netherlands excels in quantum research, 71% of its central government agencies have not begun preparing for the cryptographic threat posed by future quantum computers. Only six percent have incorporated quantum risk...

Robinhood Faces Lawsuit for Alleged Unlawful Disclosure of Consumers’ Sensitive Financial Info
Robinhood Markets is facing a lawsuit filed by client Jamillah Dunn alleging the brokerage embedded invisible Google trackers on its website that transmit users’ sensitive financial data—including account numbers, holdings, and search queries—to advertisers without consent. The complaint, lodged in...

Bring Your Nonprofit's Rogue IT Out of the Shadows. Here's How.
Nonprofit organizations increasingly grapple with shadow IT—unauthorized tools and services used by staff and volunteers that bypass official oversight. These hidden solutions create security gaps, data‑governance challenges, unexpected expenses, and threaten business continuity. The article outlines practical steps such as...

Australia Regulator Calls for Urgent Cybersecurity Action to Counter Mythos
Australia’s securities regulator ASIC has urged the financial services industry to act quickly on cyber risks posed by frontier AI models such as Anthropic’s Mythos. The commission warned that AI can uncover long‑standing vulnerabilities in days, compressing a typical twelve‑month...

AI Cyber Attack Threatens Global Financial Crisis, Warns International Monetary Fund
The International Monetary Fund warned that AI‑driven cyber attacks could spark a global financial crisis, citing the new Anthropic model Mythos that can locate software vulnerabilities at scale. The IMF highlighted the systemic risk posed by shared cloud services, where...

Cybersecurity: Briefing Your Board
The BCLP blog outlines a structured agenda for cybersecurity briefings to corporate boards, emphasizing the threat landscape, risk profile, AI implications, regulatory updates, and program status. It recommends private sessions between the board and the CISO to foster trust and...

NHS to Grant Palantir Contractors ‘Unlimited Access’ to Patient Data
The UK National Health Service has signed a deal granting Palantir contractors unlimited access to patient records across its network. The agreement, whose financial terms remain undisclosed, aims to leverage Palantir's data‑analytics platform for AI‑driven health insights. Critics warn that...

SANS Stormcast Monday, May 11th, 2026: New Linux Priv Escalation; PAM Backdoors; CPanel Updates; Let’s Encrypt
In this 7‑minute StormCast, Johannes Ulrich warns of a new Linux privilege‑escalation flaw called DirtyFrag, which requires both the RPCRX kernel module and an ESP (IPSec) module to be loaded. He also highlights recent research showing how compromised PAM modules...

AWS Launches Rex, New Runtime Guardrails for Agentic AI Data‑Layer Security
Amazon Web Services rolled out Rex, a runtime guardrail system built into its Bedrock AI service that checks agentic AI actions against data‑layer policies before execution. The move targets the growing threat of prompt‑injection attacks that could let AI agents...

HIBP Adds Costa Rica as 42nd Government Partner
HIBP’s free gov program keeps growing, helping governments get ahead of data breaches before attackers do. Today, we welcome our 42nd government: Costa Rica, protecting departments, public resources and the people behind them. https://t.co/GD14TAF6sU

Microsoft Adds AI Prompt Risk Monitoring to Purview, Preview Starts This Month
Microsoft announced a preview of AI prompt risk monitoring inside its Purview Insider Risk Management platform, slated for later this month with general availability next month. The feature lets authorized security and IT staff review employee prompts and AI responses...

Instagram Can Now Read All Users’ Private Messages. Will This Make Kids Safer or Just Boost Ad Targeting?
Meta has removed end‑to‑end encryption from Instagram direct messages as of May 8, saying few users opted in to the feature. The change means all private chats are now readable by Meta and could be leveraged for ad personalization, AI model...

Nigeria Faces 24.1 Million Compromised Accounts Since 2004, Q1 2026 Adds 281,500 Leaks
Nigeria’s National Information Technology Development Agency (NITDA) highlighted a Surfshark study that tallied 24.1 million compromised user accounts since 2004, making the country the third‑most affected in Sub‑Saharan Africa. The same report recorded 281,500 leaked accounts in the first quarter of...

Singapore Minister Flags Telcos as High‑Value AI Cyber Threat Target
Coordinating Minister for National Security K Shanmugam warned that Singapore’s telecommunications sector is a high‑value target for AI‑enhanced cyber attacks, citing recent activity by APT group UNC3886. He called for board‑level responsibility and highlighted a fresh advisory from the Infocomm Media...

The Shadow AI Problem HR Leaders Can No Longer Ignore
Lenovo’s Work Reborn Report, based on a survey of 6,000 employees, reveals that more than 70% of workers use AI weekly, with up to one‑third doing so outside IT oversight. The study labels the rapid, unsupervised adoption an “AI execution...

GDS Puts Three Suppliers in ‘Taxi Rank’ to Test Service Vulnerabilities
The UK Government Digital Service (GDS) has set up a “taxi rank” of three NCSC‑CHECK accredited penetration‑testing firms—NCC Group, Salus and Prism Infosec—to probe security weaknesses in citizen services and internal Whitehall tools. The three contracts together are worth £1.2 million...

Welcoming the Costa Rican Government to Have I Been Pwned
Have I Been Pwned (HIBP) has added Costa Rica as its 42nd government client for the free government‑focused breach‑monitoring service. The Costa Rican CSIRT now gains continuous visibility into compromised government email addresses, enabling faster identification of exposure and more...

GitLab Makes Anthropic’s Claude Default Engine in Duo Agent Platform
GitLab has expanded its partnership with Anthropic, positioning Claude as the default model across its Duo Agent Platform. The move embeds AI code generation, review and vulnerability remediation within GitLab’s existing governance framework, while leveraging Google Cloud Vertex AI and...

CISA Launches “CI Fortify” Roadmap to Harden State and Local Cyber Resilience
The Cybersecurity and Infrastructure Security Agency (CISA) released its CI Fortify roadmap this week, outlining isolation and recovery steps for critical infrastructure operators. The guidance targets state and local governments facing unreliable third‑party connections and hostile nation‑state actors, aiming to keep...

Braintrust AI Platform Breach Exposes AWS API Keys, Raising Supply‑Chain Alarm
AI observability startup Braintrust disclosed that attackers breached an AWS account on May 4, exposing API keys used for cloud‑based AI models. The company locked the account, rotated credentials and urged all customers to rotate org‑level AI provider keys, underscoring...

AI Could Multiply Software Vulnerabilities Twentyfold, Globally
What we can see is only a fraction of what exists. Jay Chaudhry has been in cybersecurity for over 30 years. In a recent CRN interview, the @zscaler CEO said he's never seen anxiety in the field like this. He's staring...
Parallel Bug Discovery Triggers Premature Linux LPE Disclosure
The Linux kernel has seen three critical local‑privilege‑escalation (LPE) bugs surface in weeks, starting with the Copy Fail flaw and followed by Dirty Frag and Copy Fail 2. Dirty Frag’s embargo was unintentionally broken on May 7, releasing exploit details before a full patch was ready,...

FCC Extends Software Update Waivers for Foreign Drones and Routers to 2029
The U.S. Federal Communications Commission announced on May 8 that it will allow software and firmware updates for foreign‑made drones and consumer routers through Jan. 1, 2029, reversing earlier restrictions. The move, issued by the FCC’s Office of Engineering and Technology,...

Vercel Open‑Sources DeepSec, AI‑Driven Scanner to Shift Security Left in CI/CD
Vercel has open‑sourced DeepSec, an AI‑powered security scanner that integrates directly into development workflows. The tool can cost thousands of dollars per scan for large repositories, yet promises a false‑positive rate of only 10‑20 percent, aiming to move vulnerability detection...

Sandhills Medical Names Sena Ocloo as CIO to Accelerate Tech and Security Overhaul
Sandhills Medical announced the appointment of Sena Ocloo as chief information officer. Ocloo, who brings 13 years of IT leadership at Kintegra Health, will steer a multi‑year technology refresh that includes automation, next‑gen wireless and stronger system redundancy, positioning the...

Cleanaway Tidies up Endpoint Security
Cleanaway Waste Management is streamlining its endpoint security by cutting more than 20 cyber‑security suppliers down to five strategic vendors. The move covers over 15,000 assets—including 4,800 trucks, mobile devices and operational technology—across Australia, New Zealand and the Middle East. The...

Two US Men Jailed for Helping North Korean Hackers Infiltrate US Firms
Two American residents, Matthew Isaac Knoot and Erick Ntekereze Prince, were sentenced to 18 months in federal prison for operating laptop farms that let North Korean hackers masquerade as U.S. remote workers. The scheme, which ran from 2020 to 2024,...

Is This a Dangerous Computer Virus?
A user pasted an obfuscated PowerShell script into a Windows 10 machine after visiting a pornographic site, then executed it while Windows Defender was disabled. The script decodes a hex‑encoded payload using an XOR key and runs it via iex, creating a...

After the $16.5 Billion in Exploits, DeFi Is Now Being Forced Toward the Controls It Once Resisted
April 2026 marked the worst month for DeFi losses in over a year, with attackers siphoning $635 million across 28 incidents. A compromised rsETH bridge allowed counterfeit tokens to be deposited on Aave, creating roughly $200 million of bad debt despite the...
Hardware Attestation as Monopoly Enabler
Apple and Google are progressively extending hardware‑based attestation, embedding it in services such as Play Integrity and App Attest. The APIs now require certified devices, effectively barring alternative operating systems like GrapheneOS and limiting competition. Governments, especially in the EU...

Never Trust Unknown Calls: My Hubris Cost Everything
“I still love you even though you are a dummy,” Maryam told me as she gave me a needed hug this morning after I wished her happy Mother’s Day. Yesterday’s social hack wherei basically gave a caller access to everything...

Shared Observability Unites SOCs and DevOps
RT SOCs and DevOps will need shared observability for agents: data access, tool calls, MCP interactions, and risk levels in one view. #Security #DevOps @Star_CIO https://t.co/tRGwCPc4Mb

Why No Enterprise Can Afford a Static Approach to Third-Party Risk
Enterprises can no longer rely on static, point‑in‑time third‑party risk assessments because digital ecosystems evolve faster than questionnaires can capture. Continuous visibility is required to track vendor updates, API integrations, and subcontractor dependencies that shift risk profiles in real time....

Beware: Impersonator Sending Scam Emails, Not on Instagram
PSA: There’s an impersonator pretending to be me sending out scam emails about some trading system. Please disregard emails like that. Same for scams on Instagram and such. I’m not on Instagram. (sigh)

SAP Teams with S3NS to Launch Trusted Cloud for Thales in France by H2 2026
SAP and S3NS have sealed a partnership to run SAP RISE private‑cloud edition on the PREMI3NS SecNumCloud‑qualified platform, with French defence giant Thales as the first strategic customer. The joint offering will be commercially available by the second half of...

Riskified Launches AI‑Powered Fraud Suite at Ascend 2026, Boosting Merchant Visibility
Riskified announced a next‑generation AI risk‑management suite at its Ascend 2026 summit in New York, adding conversational analytics, network‑wide identity mapping and real‑time control tools for merchants. The launch targets rising AI‑driven fraud and aims to give fraud teams deeper...