Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB

GE HealthCare Recalls Certain CT Systems Due to 'Security Vulnerability'
The U.S. FDA has issued a Class 2 recall for GE HealthCare's Revolution series CT scanners after identifying a security vulnerability in the AW Server accessed through Edison Health Link. Approximately 200 systems worldwide are affected, prompting GE to issue Urgent Medical Device Correction letters in March and advise customers to follow cybersecurity best practices pending a fix. No breaches have been reported, and the recall follows a similar issue with GE monitor software earlier this year. The company is working with service representatives to resolve the flaw.
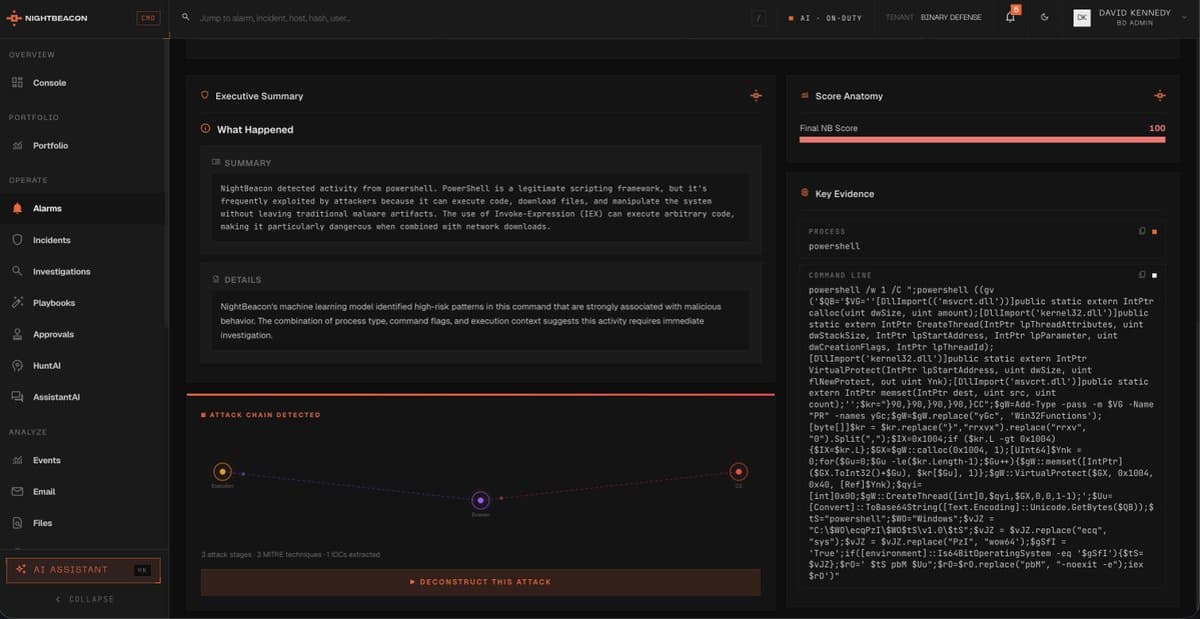
NightBeacon Slashes Detection to Seconds, Cuts False Positives 87%
NightBeacon is changing the game for us @Binary_Defense - we have this technology so dialed into every aspect of what we do. Our MTTD and MTTR has drastically been reduces to seconds and minutes, not multiple minutes or hours....

Taken : This Is a Web Page that Shows How Much Data Your...
The new web tool Taken (sinceyouarrived.world/taken) reveals exactly what data a browser hands over the instant a page loads, without any cookies, logins, or prompts. By aggregating headers, canvas output, font lists, and hardware signals, the site demonstrates that a...

Why 62% of Organizations Still Cannot Scale AI Safely
A Stanford AI Index report shows 62% of organizations view security and risk as the primary obstacle to scaling agentic AI, outpacing technical or regulatory concerns. The same data reveals AI‑related incidents jumped from 30% to 50% of firms between...

Can Hackers Break Encrypted USB Drives? I Tried to Find Out
The Kingston IronKey Locker+50 G2 is a hardware‑encrypted USB flash drive that protects data with a dedicated encryption chip. It uses 256‑bit AES‑XTS and wipes its keys after ten failed password attempts, ensuring data is unrecoverable. The drive includes an on‑screen...
Canada’s Bill C-22 Is a Repackaged Version of Last Year’s Surveillance Nightmare
Canada’s Bill C-22, dubbed the Lawful Access Act, revives the failed Bill C‑2 by forcing digital services to retain a full year of metadata and expanding data‑sharing with foreign governments. The legislation authorises the Minister of Public Safety to demand...

Ivanti Flags Actively Exploited EPMM Zero‑day (CVE‑2026‑6973) with Federal Patch Deadline
Ivanti disclosed a high‑severity remote‑code execution vulnerability (CVE‑2026‑6973) in its Endpoint Manager Mobile platform that is already being leveraged in zero‑day attacks. The U.S. Cybersecurity and Infrastructure Security Agency added the flaw to its Known Exploited Vulnerabilities catalog and mandated...

Texas Obtains Smart TV Privacy Settlement With LG — Here’s What Changes
Texas Attorney General Ken Paxton secured a settlement with LG Electronics that forces the company to disclose and give users an opt‑out for Automated Content Recognition (ACR) data collection on its smart TVs. The agreement requires a pop‑up notice, a...

Modernizing Wastewater Systems: SCADA, Remote Monitoring & Cybersecurity for Resilient Operations
Wastewater utilities are accelerating digital upgrades to replace legacy SCADA, add remote monitoring, and tighten cybersecurity as regulatory pressure and aging assets mount. The industry’s shift toward interoperable, cloud‑ready control platforms promises greater visibility across dispersed lift stations and treatment...

IPhone-Android RCS Conversations Are End-To-End Encrypted In iOS 26.5
Apple announced that iOS 26.5 now supports end‑to‑end encryption for RCS messages exchanged with Android devices, bringing cross‑platform chats to the same security level as iMessage. The feature is released as a beta and requires carrier support on both the iPhone...

Webinar to Demystify Biometric Physical Access Control Decisions
Biometric Update and Goode Intelligence are hosting a free webinar on May 19 to dissect the latest trends in biometric physical access control, featuring a new market report that forecasts the sector surpassing $9.8 billion by 2028. The event will showcase...

Connecticut National Guard Hosts Cyber Yankee 2026
The Connecticut National Guard is staging Cyber Yankee 2026, a two‑week regional cyber‑defense exercise at Camp Nett from May 4‑15. The drill brings together over 360 military, civilian and international participants to simulate attacks on critical utilities such as gas, water and electricity....

Google Disrupts Hackers Using AI to Exploit an Unknown Weakness in a Company's Digital Defense
Google’s threat‑intelligence team disrupted a criminal group that used a large‑language‑model AI to locate a previously unknown zero‑day vulnerability and bypass two‑factor authentication on a major system‑admin platform. The attackers’ AI‑assisted approach marks the first confirmed case of a large‑language...

Deepfake Penetration Outpacing Security Preparedness: GetReal Security
GetReal Security’s Deepfake Readiness Benchmark Report reveals that eight‑in‑ten organizations encounter AI‑generated deepfakes, with 45% facing them frequently. Among enterprises with 1,000+ employees, 41% admit they have hired or onboarded a fake candidate. Only 1.5% of respondents claim never seeing...

The Implications of Cyber-Physical Security Convergence in Higher Education
Higher education campuses are experiencing a rapid convergence of physical security systems and cybersecurity due to IoT devices, smart cameras, and networked access controls. This blending expands attack surfaces, creates privacy concerns, and forces fragmented IT, OT, and facilities teams...

Thailand Mandates Biometric IDV for All Social Media Advertisers to Curb Scams
Thailand’s government has issued a new regulation mandating biometric identity verification for every social‑media advertiser, including foreign entities, using facial recognition linked to a national ID or a recognized digital ID. The rule also obliges platforms to retain advertiser records...

AI Agents Are Running Hospital Records and Factory Inspections. Enterprise IAM Was Never Built for Them.
Enterprises are rapidly deploying AI agents for tasks like medical transcription and factory‑floor inspection, but 85% remain in pilot mode while only 5% have moved to production. The bottleneck is not model capability but identity governance—traditional IAM systems can’t inventory,...

Debian 14 Cracks Down on Unreproducible Packages
Midway through Debian 14 "Forky" development, the release team announced a mandatory reproducible‑build policy. New migration software now blocks any package that cannot be rebuilt byte‑for‑byte, and flags regressions in existing testing packages. The move aligns Debian with the broader...

Unified Tech, Law, and Innovation Needed to Stop Live Piracy
Looking for an informed discussion navigating the intersection of 🔒 security technology stack, 🧑⚖️ legal frameworks and enforcement, as well as 📲 product innovation, here we go: In „Streaming Security at Scale: Protecting Live Sports Broadcasts,“ we are covering why an...

MSPAlliance Launches Service Lines in Cyber Verify for Clearer Compliance Reporting
MSPAlliance has introduced Service Lines within its Cyber Verify platform, allowing managed service providers (MSPs) to directly map audited controls to the specific services they deliver. The new feature clarifies where the MSP’s security responsibilities end and the client’s begin,...

Zimperium Mobile App Response Agent Helps Security Teams Counter Mobile Attacks
Zimperium introduced the Mobile App Response Agent, a new component of its Mobile App Protection Suite designed to accelerate the detection and remediation of mobile‑based fraud and security threats. The tool reduces investigation cycles from hours or days to minutes...

Anthropic’s Bug-Hunting Mythos Was Greatest Marketing Stunt Ever, Says cURL Creator
Anthropic’s security‑focused AI model Mythos was given limited access to the cURL codebase, returning five alleged vulnerabilities. After a thorough review, cURL creator Daniel Stenberg’s team confirmed only one low‑severity CVE, dismissing the rest as false positives or minor bugs....

Agile Defense Names Shawn Tyrie CRO to Accelerate Federal IT Growth
Agile Defense announced the hiring of Shawn Tyrie as its new chief revenue officer. The move is aimed at accelerating revenue growth and deepening the firm’s presence in federal IT and cybersecurity contracts. Tyrie's experience in government contracting is expected...

Vocus Appoints Nikos Katinakis as Chief Technology Officer to Drive Network Automation
Vocus Group announced today that former Zayo executive Nikos Katinakis will become chief technology officer. Katinakis will oversee the carrier’s network, security and customer operations while spearheading intelligent automation across its infrastructure, a move aimed at sharpening Vocus’s digital strategy.

High-Severity Security Issue Affecting TeamCity On-Premises (CVE-2026-44413) – Update to 2026.1 Now
JetBrains disclosed a high‑severity post‑authentication vulnerability (CVE‑2026‑44413) affecting all TeamCity On‑Premises installations up to version 2025.11.4. The flaw allows any logged‑in user to expose portions of the server API to unauthenticated parties. JetBrains released a full fix in TeamCity 2026.1...

The Data You Share Is the Advantage You Lose
In this episode of Unpacked, host Nick and guest KP discuss how AI is reshaping the Architecture, Engineering, and Construction (AEC) industry, highlighting the rapid emergence of AI‑driven tools like MCP servers that let software APIs talk to each other...

CISA Flags BerriAI LiteLLM SQL Injection as Critical Exploited Vulnerability
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the critical CVE‑2026‑42208 flaw in BerriAI’s LiteLLM Python package to its Known Exploited Vulnerabilities catalog. The SQL‑injection bug, scored 9.3, was weaponized by threat actors within 36 hours of public disclosure,...

Labyrinth 1.1: Making End-to-End Encrypted Backups Even More Reliable
Meta has launched Labyrinth 1.1, an upgrade to its encrypted storage protocol for Messenger. The new sub‑protocol pushes each message directly into the recipient’s encrypted backup, eliminating reliance on device‑online status. This change improves backup reliability when users lose, replace,...

Vietnam SMEs Strengthen Cybersecurity Amid Digital Transformation
Vietnam is urging its 800,000 SMEs— which make up about 97% of firms and 20% of GDP— to bolster cybersecurity as digital transformation accelerates. The government’s 2026‑2030 program targets 500,000 enterprises, with 300,000 expected to adopt AI and other digital...

The Patching Treadmill: Why Traditional Application Security Is No Longer Enough
Traditional find‑and‑fix and defend‑and‑defer security models are being outpaced by rapid continuous deployment and AI‑assisted coding. Vulnerability backlogs are swelling, with 45% of large‑company flaws remaining unfixed after a year and average remediation times stretching beyond two months. Exploitation is...

Beyond the Cleanup Job: Redefining Application Security for the Modern Enterprise
The article argues that modern enterprises must move application security from a post‑release fix to a board‑level, secure‑by‑design mandate. It highlights CISA’s recommendations for a chief security‑by‑design officer, regular board reporting, and incentive structures. Culture and clear developer communication are...

OneLayer Unveils Certified Integrations to Strengthen Private Cellular Security Perimeter
OneLayer announced the Technology Alliance Program (TAP), a certified ecosystem that links its orchestration layer with third‑party private cellular routers, firewalls and other network components. Certified partners will appear in OneLayer’s affiliate directory and gain access to co‑marketing, workshop resources,...

Stopping Bugs Before They Ship: The Shift to Preventative Security
The software industry is shifting from reactive patching to a preventive security model known as secure‑by‑design, embedding threat modeling and clear trust boundaries early in the development lifecycle. Government agencies like CISA now promote security as a core business requirement,...

Blocked AI-Enabled Cyber Hack Could Have Led to Mass Event: Google
Google’s Threat Intelligence Group disclosed that a sophisticated cybercrime group leveraged artificial intelligence to uncover a previously unknown flaw in a popular open‑source system‑administration tool. The AI‑driven exploit was intercepted before it could be deployed in a mass‑scale attack, marking...

Linux Is Getting a Security Wake-Up Call - Why It Was Inevitable and I'm Not Worried
Linux’s historic reputation for impenetrability is being challenged as two high‑severity kernel bugs—Copy Fail and Dirty Frag—were disclosed within a week. The surge in vulnerabilities stems from Linux’s explosion into cloud, AI, and consumer markets, making it a prime target for...

SHRIDHAR KHANAL: SSL in PostgreSQL
The article explains how to secure PostgreSQL connections with SSL/TLS, covering certificate generation, configuration in postgresql.conf and pg_hba.conf, client settings, and verification methods. It stresses that merely enabling SSL is insufficient; proper verification, hostssl entries, and sslmode=verify-full are required. It...

Second Canvas Data Breach Causes Major Disruptions for Schools, Colleges
Instructure confirmed a second unauthorized intrusion into its Canvas learning management system on May 7, just days after a May 1 breach. The attack exploited vulnerabilities in the platform's Free‑For‑Teacher accounts, forcing temporary shutdowns and causing widespread outages during final‑exam week. Schools...

AI Could Expose Every Open‑source Vulnerability, Ending Its Safety
We've had Linus's Law for decades: "Given enough eyeballs, all bugs are shallow." #catb After last week's Canvas breach, perhaps we need Linus's Corollary: Given powerful enough AI, all bugs will be found and exploited. Will AI's superhuman ability to find...

AI-Generated Scam Calls Now Mimic Real Voices
Scary indeed. AI-powered scam calls are getting more convincing—and more common: 'It was her voice, I know her scared cry' https://t.co/lV7jJx5BFm #CIO #AI

AI-Powered Hacking Has Exploded Into Industrial-Scale Threat, Google Says
Google’s threat‑intelligence team reports that AI‑powered hacking has leapt from a niche concern to an industrial‑scale threat in just three months. Criminal syndicates and state‑linked actors from China, North Korea and Russia are weaponising commercial large‑language models such as Gemini,...

Microsoft Brings Stronger Passkey Controls to Smartphones, Entra ID, and Microsoft Account Recovery
Microsoft expanded its passkey ecosystem to cover smartphone‑based sign‑in across Windows PCs, Xbox consoles, and Microsoft 365, allowing a single mobile credential to replace passwords. Consumer passkeys now sync via iCloud Keychain or Google Password Manager, unlocking services with device biometrics....

GNOME's Help Viewer Updated Due To Flatpak Sandbox Escape Vulnerability
GNOME’s built‑in help viewer Yelp received a critical update (version 49.1) to close a Flatpak sandbox escape discovered during a security audit. The flaw let a malicious help file launch Yelp, using an SVG‑based CSS stylesheet to read arbitrary host files...

Attackers Targeting Storage Infrastructure for Remote Work
Threat actors are shifting focus from endpoints to storage infrastructure, exploiting on‑premises and cloud storage vulnerabilities to steal data, deploy ransomware, and destroy backups. The move is driven by the high value of consolidated data—personal information, IP, AI training sets,...

Beware Spam: Don't Click Fake Alert Links
FOLLOWERS.......I have some spam dirt bags out there trying to trick you. Do NOT click on any links that say I am sending out alerts or a strategy.

Europe Is Moving to Block Microsoft, Amazon, and Google From Handling Government Health, Financial, and Legal Data
The European Commission is set to unveil the Tech Sovereignty Package, a regulatory framework that would restrict U.S. cloud providers from processing sensitive public‑sector data such as health, finance and judicial records. The draft targets Microsoft, Amazon Web Services and...

From Reactive to Predictive: How Healthcare Organizations Can Stay Ahead of Cyber Threats
In 2024 U.S. healthcare faced a record 444 ransomware and data‑theft incidents, making it the most targeted critical‑infrastructure sector. Medical records now command $1,000 per file on dark‑web markets, driving attackers to exploit legacy systems, telehealth platforms, and IoT devices....

Google Warns Artificial Intelligence Is Accelerating Cyberattacks and Zero-Day Exploits
Google Cloud Threat Intelligence released a report warning that attackers are now leveraging artificial intelligence to accelerate cyber‑attacks, including the creation of AI‑generated zero‑day exploits. The research shows a clear shift from credential‑theft tactics to targeting software flaws, cloud APIs,...

Build Application Firewalls Aim to Stop the Next Supply Chain Attack
Supply‑chain attacks continue to infiltrate software during the CI/CD build phase, as recent compromises of the Axios npm library and tools like Trivy and LiteLLM demonstrate. Traditional scanners often miss malicious code that appears benign or exploits zero‑day vulnerabilities. InvisiRisk...

What New Guidance Says For Securing Agentic AI Systems
A joint report from CISA, NSA and allied cyber agencies outlines the security challenges of deploying autonomous, or agentic, AI systems. It details privilege, design, behavior and accountability risks that arise when AI agents act without human oversight. The guidance...
Fake Claude Code Page Pushes PowerShell Stealer at Devs
Ontinue’s Cyber Defense Center uncovered a new information‑stealer distributed through counterfeit Claude Code installation pages. The malicious PowerShell loader, delivered via a disguised /install.ps1 script, injects a tiny native helper into Chromium‑based browsers to extract App‑Bound Encryption keys, cookies, passwords and...