Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB

Four OpenClaw Flaws Enable Data Theft, Privilege Escalation, and Persistence
Cybersecurity firm Cyera disclosed four linked vulnerabilities in the OpenClaw agent platform, dubbed the Claw Chain, that enable sandbox escape, credential theft, privilege escalation, and persistent backdoors. The flaws—CVE‑2026‑44112, ‑44113, ‑44115, and ‑44118—combine TOCTOU race conditions, heredoc injection, and a spoofable ownership flag to let attackers move from code execution inside OpenShell to full control of the gateway. OpenClaw addressed all issues in version 2026.4.22 following responsible disclosure, crediting researcher Vladimir Tokarev. Users are urged to upgrade immediately.

AI-Driven SBOMs Enforce Data Protection Obligations Post‑GDPR
'Where are companies' binding obligations to guard our data, our livelihoods, from misuse?' GDPR made that question expensive to ignore. AI is raising the stakes again. Cyber agencies already named it: AI-component SBOMs are the new supply-chain floor.

Gunra Ransomware Expands RaaS After Conti Locker Shift
Gunra ransomware has transitioned from a Conti‑derived locker to a standalone Ransomware‑as‑a‑Service platform, expanding its operational reach. The shift, announced after its initial 2025 attacks on South Korean firms, now powers an affiliate network that can brand the payload and...

Google Lets Workspace Admins Apply One Policy Across All SAML Apps
Google has upgraded Context‑Aware Access in Workspace with a default policy for SAML applications, establishing a universal security baseline for any SAML‑based app lacking a specific rule. Administrators can manually enable the feature at the organizational‑unit or group level, eliminating...

UAE Cyber Security Council, Siemens Sign OT Security MoU
The UAE Cyber Security Council and Siemens have signed a memorandum of understanding to deepen cooperation on operational technology (OT) cybersecurity across the UAE’s critical infrastructure. The pact creates a Joint Innovation Center of Excellence for OT research, workforce development,...

2025 Saw a Surge in Wireless Vulnerabilities
Security firm Bastille Networks reported a dramatic rise in wireless vulnerabilities in 2025, with 937 new CVEs—about 2.5 per day—recorded across Wi‑Fi, Bluetooth, cellular and Zigbee. Wireless flaws grew 20 times faster than traditional threats over the past 15 years,...

Illicit Enterprise: An Anatomy of the Modern Underground Phishing Marketplace
The phishing underground has transformed from a chaotic marketplace into a sophisticated criminal ecosystem offering tools, labor and phishing‑as‑a‑service (PhaaS). Intel 471’s 2026 Phishing Outlook, based on analysis of nearly 200 offers, reveals recruitment now accounts for 31 % of activity, with...

Patch Time for Cisco SD-WAN Admins as Vendor Drops yet Another Make-Me-Admin Zero-Day
Cisco has issued emergency patches for a critical zero‑day vulnerability (CVE‑2026‑20182) affecting its Catalyst SD‑WAN Controller and Manager, formerly known as vSmart and vManage. The flaw allows unauthenticated remote attackers to bypass authentication and obtain admin privileges, enabling arbitrary NETCONF...

What 45 Days of Watching Your Own Tools Will Tell You About Your Real Attack Surface
Bitdefender reports that 84% of 700,000 high‑severity incidents involve abuse of trusted Windows utilities, underscoring the living‑off‑the‑land (LOLBin) threat. To counter this, the firm offers a complimentary 45‑day Internal Attack Surface Assessment for organizations with 250+ employees, leveraging GravityZone PHASR to...
TanStack Supply Chain Attack Hits Two OpenAI Employee Devices, Forces macOS Updates
OpenAI disclosed that two employee devices were compromised in a supply‑chain attack targeting the TanStack library, part of the Mini Shai‑Hulud campaign. The breach resulted in limited credential exfiltration from internal source‑code repositories, but no intellectual property or production systems...

OrBit Rootkit Targets Linux to Steal SSH and Sudo Credentials
The OrBit Linux rootkit, first identified in 2022, has been quietly evolving while remaining active in the wild. Built on the open‑source Medusa LD_PRELOAD framework, attackers now deploy two main variants—Lineage A with full credential‑stealing and network‑hiding features, and a slimmer...

CalPhishing Scam Uses EvilTokens Kit, Outlook Invites to Steal M365 Sessions
Cybercriminals are leveraging a new CalPhishing technique that embeds malicious iCalendar (.ics) files into Outlook invites, automatically adding tentative meetings to victims' calendars. The campaign, identified by Fortra Intelligence and Research Experts, uses the EvilTokens phishing kit sold on Telegram...

Akamai to Buy LayerX for $205 M, Adding AI‑driven Zero‑Trust to Its Portfolio
Akamai Technologies agreed to acquire Israeli startup LayerX for about $205 million, a deal slated to close in Q3 2026. The purchase adds browser‑based AI usage‑control and Zero‑Trust capabilities, positioning Akamai to protect enterprises as AI adoption accelerates.

Thorchain Halts Trading After $10 Million Cross-Chain Exploit, RUNE Token Drops 12%
Thorchain, the decentralized cross‑chain liquidity protocol, suffered a $10.8 million exploit spanning Bitcoin, Ethereum, BSC and Base, prompting an immediate halt to all trading and signing operations. The attacker’s wallets now hold roughly 3,443 ETH (about $7.8 million), 36.85 BTC (around $3.0 million) and 96.6 BNB...

Absa’s Defence Against Frontier AI Cyberthreats: More AI
Absa Group announced it will deploy AI‑powered “super agents” to automatically scan its systems for vulnerabilities and speed up patch cycles. The move is a direct response to frontier AI models like Anthropic’s Mythos, which can locate thousands of zero‑day...

TeamPCP Ups the Game, Releases Shai-Hulud Worm’s Source Code
TeamPCP, a prolific hacking group, has publicly released the source code for its Shai‑Hulud supply‑chain worm on GitHub, prompting immediate forks before the repositories were taken down. The code reveals a modular framework with loaders, secret‑harvesting modules, encryption, and a...

Rocky Linux Launches Opt-In Security Repository for Urgent Fixes
Rocky Linux has added an optional Security Repository that delivers urgent patches ahead of the upstream Enterprise Linux release when a vulnerability is publicly exploitable and no official fix exists. The repository is disabled by default and can be enabled...

AI-Hacking Threat Pushes $130 Billion Crypto Sector to the Brink
In April 2026, two AI‑enhanced crypto hacks siphoned roughly $600 million, accounting for about 76% of all cryptocurrency thefts that year. The attacks, attributed to North Korea‑linked groups, leveraged artificial intelligence to pinpoint vulnerable targets and craft custom exploits. The fallout...

The Economics of Ransomware 3.0
Ransomware 3.0 has shifted from pure encryption to a triple‑extortion play that combines system lock‑out, data exfiltration, and pressure on customers, regulators and shareholders. The model, used by groups such as ALPHV and Cl0p, forces organizations to confront threats that...

Keycard Helps Developers Secure Autonomous AI Agents with Scoped Access
Keycard unveiled “Keycard for Multi‑Agent Apps,” a platform that gives each autonomous AI agent its own verifiable identity and session‑based, scoped access. The solution replaces static API keys with runtime‑issued tokens, enabling fine‑grained delegation and full auditability across agent‑to‑agent workflows....
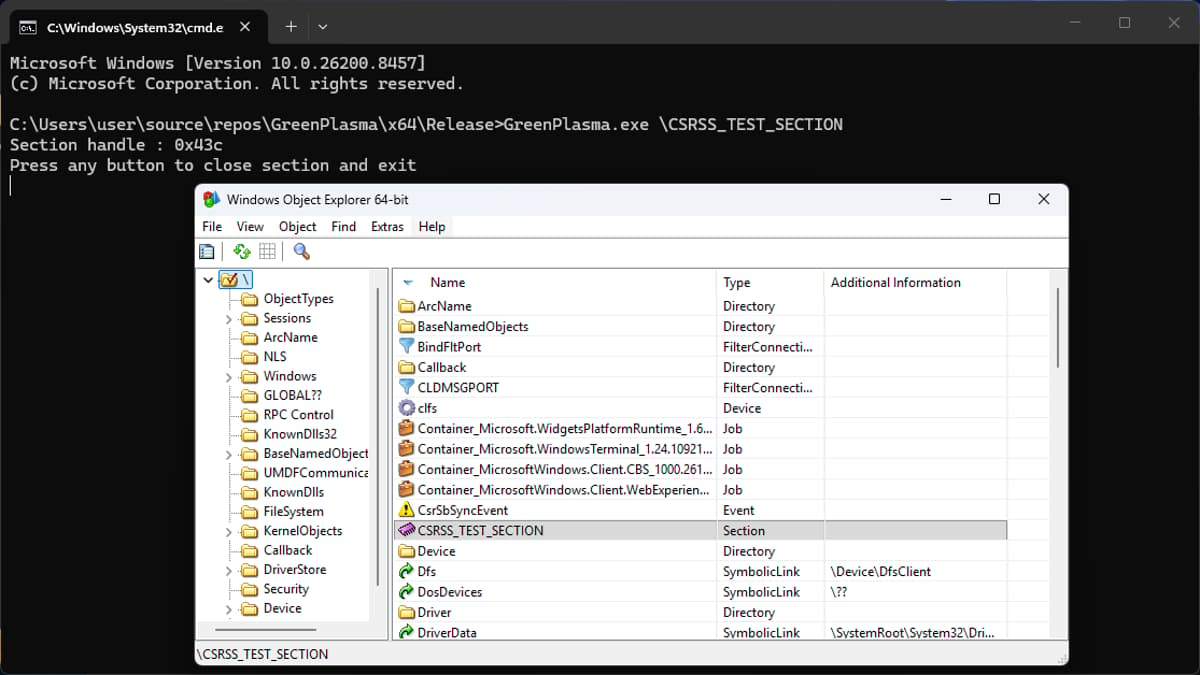
Researchers Uncover YellowKey and GreenPlasma Windows Zero-Days
Security researcher Chaotic Eclipse disclosed two fresh Windows zero‑days, YellowKey and GreenPlasma. YellowKey lets attackers with physical access bypass BitLocker on Windows 11 and Windows Server 2022/2025 by planting crafted files in the WinRE image. GreenPlasma targets the CTFMON framework, enabling privilege...

On-Prem Microsoft Exchange Server CVE-2026-42897 Exploited via Crafted Email
Microsoft disclosed CVE‑2026‑42897, an 8.1‑rated cross‑site scripting flaw in on‑premise Exchange Server that is already being exploited via crafted emails. The vulnerability allows arbitrary JavaScript to run in Outlook Web Access when a malicious message is opened. Microsoft’s temporary countermeasure...

OpenAI Confirms Limited Impact From TanStack Npm Supply Chain Attack, Urges macOS App Updates
OpenAI disclosed that a recent TanStack npm supply‑chain attack compromised two employee devices but did not expose customer data or production systems. The breach, linked to the Mini Shai‑Hulud malware campaign, prompted immediate isolation, credential rotation, and a temporary halt...

Security Researchers Use Anthropic’s Mythos AI Model to Crack Apple’s macOS
Security firm Calif leveraged Anthropic’s Mythos generative‑AI model to uncover two memory‑corruption bugs in Apple’s macOS, enabling a privilege‑escalation exploit that can seize control of a machine. The researchers demonstrated that Mythos not only identified the vulnerabilities but also assisted...

OpenLoop Health Breach Exposes Data of 716,000 Patients
OpenLoop Health disclosed that a cyber intrusion in early January accessed and exfiltrated personal information of 716,000 patients. The breach, reported to authorities in March and added to the HHS portal this week, did not include electronic health records or...

Taiwan Incident Highlights Cybersecurity Gaps in Rail Systems
On April 5 a 23‑year‑old rail enthusiast spoofed Taiwan High Speed Rail’s emergency radio, triggering emergency brakes on three bullet trains and causing a 48‑minute service disruption. The hack leveraged the Terrestrial Trunked Radio (TETRA) system, which can be secure but...

Foxconn Confirms Ransomware Attack on North American Plants, 8TB Stolen
Foxconn disclosed that a suspected ransomware attack by the Nitrogen group compromised several North American manufacturing sites, with the hackers claiming to have exfiltrated more than eight terabytes of data. The breach highlights the growing vulnerability of mid‑size supply‑chain operators...

Hackers Exploit Auth Bypass Flaw in Burst Statistics WordPress Plugin
Hackers are exploiting a critical authentication bypass vulnerability (CVE‑2026‑8181) in the Burst Statistics WordPress plugin, which is installed on roughly 200,000 sites. The flaw, introduced in versions 3.4.0 and 3.4.1, lets unauthenticated attackers impersonate any known admin user or create...
Meet Fragnesia, the Third Linux Kernel Vulnerability in a Month
A new Linux kernel flaw named Fragnesia (CVE‑2026‑46300) has been disclosed, targeting the XFRM ESP‑in‑TCP subsystem to achieve local privilege escalation. The vulnerability provides an in‑memory write primitive that bypasses traditional file‑system permissions, allowing unprivileged users to corrupt security‑sensitive files...

Sapphire Ventures Puts $70 M Into Netskope, Making Cloud‑Security Firm Its Top Holding
Sapphire Ventures acquired 5,672,579 Netskope shares for an estimated $70.4 million, making the cloud‑security provider its largest 13F holding. The investment comes as Netskope reports a 32% year‑over‑year revenue rise to $709 million, underscoring strong enterprise demand for zero‑trust solutions.

Congress Puts Heat on Instructure After Canvas Outage
Congressional committees are pressing Instructure after its Canvas learning‑management system suffered two separate breaches within a week, attributed to the ShinyHunters cybercrime group. The attacks exposed more than 3 TB of data from over 9,000 educational institutions, including student IDs, emails,...

Cisco Talos Confirms Active Exploitation of CVE‑2026‑20182 in SD‑WAN Controllers
Cisco Talos has verified that a sophisticated threat group, identified as UAT‑8616, is actively exploiting CVE‑2026‑20182 to gain high‑privileged access to Cisco Catalyst SD‑WAN Controllers and Managers. The breach includes SSH key injection, NETCONF tampering and attempts to elevate to...

Providence’s Ratliff Says Merging Cybersecurity and Emergency Management Builds Stronger Cyber Resiliency
In this episode, Providence CISO Mike Ratliff discusses how merging cybersecurity with emergency management creates stronger cyber resiliency for a large, nonprofit health system. He explains the restructuring of Providence’s security teams, the launch of "Project Oscar" to align IT...
NSCC Information for the Confirmation of a Cybersecurity Program / Compliance to Rule File: SR-NSCC-2019-003
The National Securities Clearing Corporation (NSCC) has reminded all members that under Rule SR‑NSCC‑2019‑003 they must submit a complete Cybersecurity Confirmation every two years. An electronic form will be sent to each institution’s designated Control Officer on May 20, 2026, with a...

Synack’s Analysis of 11,000+ Vulnerabilities Reveals Top Weaknesses Attackers Are Weaponizing Today
Synack’s 2026 State of Vulnerabilities Report, based on over 11,000 exploitable flaws discovered in 2025, shows a 42‑day reduction in mean time to remediate high‑severity issues and a 47% overall MTTR drop. The threat landscape intensified, with CVE disclosures up...

Windows 11 and Microsoft Edge Hacked at Pwn2Own Berlin 2026
The first day of Pwn2Own Berlin 2026 saw researchers claim $523,000 in cash by exploiting 24 zero‑day vulnerabilities. Orange Tsai secured $175,000 for chaining four logic bugs to escape Microsoft Edge’s sandbox, while three teams each earned $30,000 for privilege‑escalation flaws in...

U.S. CISA Adds a Flaw in Cisco Catalyst SD-WAN to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added Cisco Catalyst SD‑WAN vulnerability CVE‑2026‑20182 to its Known Exploited Vulnerabilities (KEV) catalog. The flaw, rated a perfect 10.0 on the CVSS scale, lets an unauthenticated remote attacker bypass peering authentication,...

ODNI Taps Officials to Coordinate Response to Foreign Election Threats
The Office of the Director of National Intelligence has appointed Dave Mastro and James Cangialosi to serve as the intelligence community’s election‑threat executives, overseeing coordination across U.S. spy agencies for the 2026 midterm elections. The role, originally created during the...

Christophe Pettus: Eleven CVEs Walk Into a Release
PostgreSQL released versions 18.4, 17.10, 16.14, 15.18 and 14.23 on May 14, 2026, fixing eleven CVEs and over sixty bugs. Three of the CVEs carry a CVSS score of 8.8, exposing critical server‑side and client‑side vulnerabilities in core components like...

The "Zombie API" Attack: Why Your Old Integrations Are Your Biggest Security Risk
The article warns that forgotten, still‑active endpoints—dubbed “zombie APIs”—pose a hidden security threat. When teams deprecate an integration without formally shutting it down, the old API remains reachable, often using outdated protocols and weak authentication. Recent breaches at Optus, Honda...

ServiceNow’s Amit Zavery On Delivering An ‘End-To-End’ Security Platform For OT And IT
ServiceNow announced that its $7.75 billion acquisition of Armis is accelerating the company’s roadmap for a unified security platform that spans both IT and operational technology (OT). By integrating Armis’s asset‑intelligence engine with ServiceNow’s workflow suite, the firm aims to deliver...
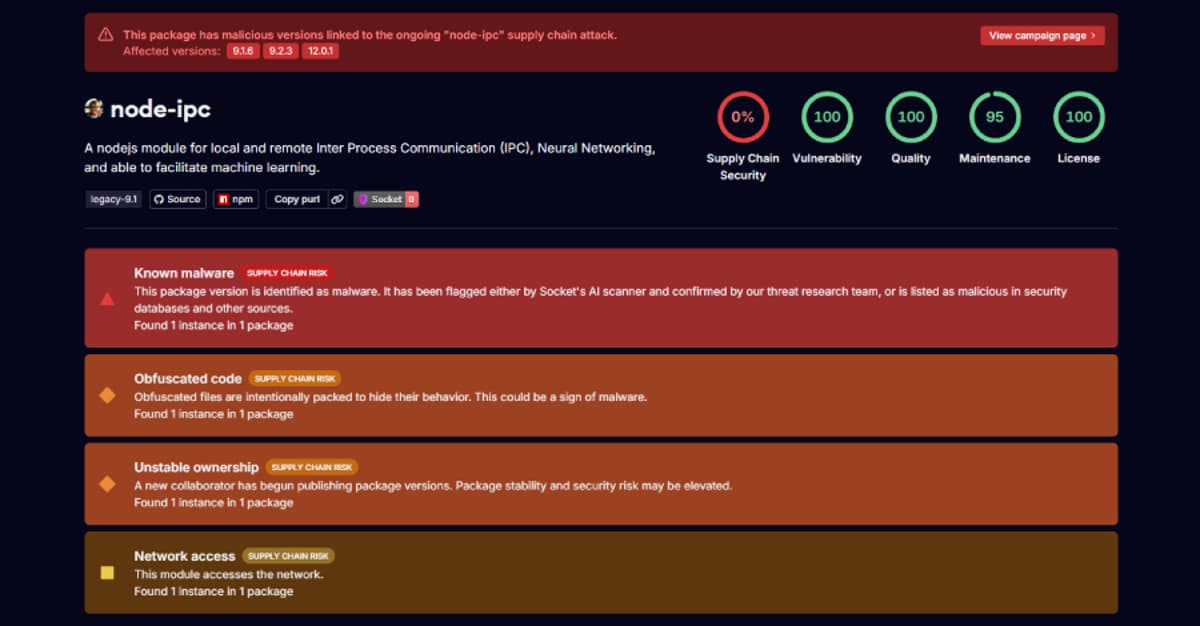
Stealer Backdoor Found in 3 Node-IPC Versions Targeting Developer Secrets
Security researchers have identified three compromised releases of the popular npm package node‑ipc (versions 9.1.6, 9.2.3 and 12.0.1) that embed a stealthy stealer/backdoor. The malicious code executes whenever the module is required, bypassing standard npm lifecycle hooks, and harvests roughly...

New Nginx Exploit
Depthfirst's automated analysis system uncovered a critical heap buffer overflow in NGINX’s ngx_http_rewrite_module, cataloged as CVE‑2026‑42945. The flaw allows unauthenticated remote code execution on servers that use rewrite or set directives, and it was disclosed alongside three related memory‑corruption issues....
'FrostyNeighbor' APT Carefully Targets Govt Orgs in Poland, Ukraine
Belarus‑linked APT group FrostyNeighbor, also known as Ghostwriter, has launched a new spear‑phishing campaign targeting government and military entities in Poland and Ukraine. The operation, active since March, uses deceptive PDFs that impersonate Ukrainian telecom provider Ukrtelecom and delivers a...

ThreatsDay Bulletin: PAN-OS RCE, Mythos cURL Bug, AI Tokenizer Attacks, and 10+ Stories
The ThreatsDay bulletin highlights a surge of active exploits, starting with Palo Alto Networks confirming limited attacks against its PAN‑OS CVE‑2026‑0300 buffer overflow, which grants root‑level code execution. Meta introduced Incognito Chat, a private AI interface that runs inference inside...

South Korea's FSS Orders Lending Firms to Tighten Cybersecurity After Hack Spree
South Korea's Financial Supervisory Service (FSS) summoned CEOs of 20 lending companies on May 13, demanding immediate upgrades to cyber defenses after a wave of hacks that exposed customer data. The regulator warned that violations of the Credit Information Act...
Broadcom Releases VMware Fusion Security Update for Root Access Bug
Broadcom has issued a security update for VMware Fusion that fixes a high‑severity TOCTOU flaw (CVE‑2026‑41702). The vulnerability allowed a local, non‑administrative user to elevate privileges to root on macOS systems running Fusion. The patch arrives as Broadcom participates in...

When Encryption Meets Quantum
Quantum computers will soon invalidate RSA and elliptic‑curve cryptography, exposing every system that relies on them—from IoT sensors to cloud services. A "harvest now, decrypt later" threat means encrypted data captured today can be broken once quantum hardware matures. U.S....

Cyber-Enabled Cargo Crime: How Cybercrime Tradecraft Is Used to Steal Freight
Cyber‑enabled cargo crime is borrowing ransomware playbooks to hijack freight, turning phishing attacks into fraudulent load pickups and rerouted shipments. In 2025 Verisk CargoNet estimated $725 million in cargo‑theft losses, while the FBI’s IC3 logged roughly $21 billion in broader cybercrime losses....

Druva Provides Integration with Dell PowerProtect Data Domain to Boost Cyber Resilience
Druva announced a new integration with Dell PowerProtect Data Domain that lets enterprises blend on‑prem Data Domain appliances with Druva’s cloud‑native SaaS platform. The joint solution offers fast local recovery from Data Domain and an immutable, air‑gapped copy in the...