Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB

A Spyware Investigator Exposed Russian Government Hackers Trying to Hijack Signal Accounts
Security researcher Donncha Ó Cearbhaill, who leads Amnesty International’s Security Lab, was targeted by a sophisticated phishing campaign that pretended to be Signal support. The attack was part of a larger operation that has affected more than 13,500 Signal users, using a bulk‑automation tool called “ApocalypseZ.” Multiple cyber‑security agencies have linked the campaign to Russian government hackers. Ó Cearbhaill turned the incident into an investigation, confirming the Russian origin and urging users to enable Signal’s Registration Lock.
Ghostwriter Targets Ukrainian Government With Geofenced PDF Phishing, Cobalt Strike
The Belarus‑aligned threat group Ghostwriter has launched a new campaign against Ukrainian government entities, using geofenced PDF attachments that only deliver a malicious RAR archive when the victim’s IP originates from Ukraine. The archive drops a JavaScript version of PicassoLoader,...

Enhancing Data Center Security Without Sacrificing Performance
Data center operators are confronting a persistent trade‑off between security agents that consume CPU cycles and the need for peak performance, especially in AI‑focused facilities. Recent hypervisor‑level breaches, such as Broadcom’s March 2025 VMware ESXi zero‑day patches, highlighted that host‑based agents...

Aligning State and Local AI Security Investments with the Cyber Strategy for America
The White House’s Cyber Strategy for America outlines six pillars that can guide state and local cybersecurity, especially pillars four and five focused on critical infrastructure and emerging technologies. A 2025 Center for Internet Security report shows 68% of state,...

New Linux Kernel Vulnerability Fragnesia Allows Root Privilege Escalation
A new Linux kernel flaw, designated CVE‑2026‑46300 and nicknamed Fragnesia, lets an unprivileged user gain root access by corrupting files through the XFRM ESP‑in‑TCP subsystem. The vulnerability enables a memory‑write primitive that can overwrite binaries such as /usr/bin/su or even...

HYCU Adds Agentic Backup Data Intelligence Layer to Find and Fill Risk Gaps
HYCU has launched aiR, an AI‑agent layer that queries backup data across more than 100 workloads, from on‑premises servers to major cloud SaaS applications. The platform provides natural‑language search, letting admins ask plain‑language questions that surface PII, insider‑risk signals, configuration...

Opexus Termination Slip Triggers Deletion of 96 U.S. Government Databases
Opexus, a Washington‑area contractor that supplies case‑management software to more than 45 federal agencies, failed to disable the accounts of twin engineers after firing them, enabling a rapid sabotage that erased 96 government databases. The incident underscores the high stakes...

Docker Launches Governed AI Runtime for Developer Laptops
Docker announced a governed AI runtime on May 12, giving security teams a single console to set policy for AI agents on developer laptops. The move targets the most exposed node in enterprise environments and pits Docker against a crowded...

NGINX Rift: An 18-Year-Old Flaw in the World’s Most Deployed Web Server Just Came to Light
Security researchers at depthfirst disclosed NGINX Rift (CVE‑2026‑42945), a critical heap buffer overflow that has existed in the NGINX codebase for 18 years. The flaw lives in the ngx_http_rewrite_module and can be triggered by a common rewrite pattern that mixes...

TeamPCP, BreachForums Launch $1K Supply-Chain Attack Contest
TeamPCP and BreachForums have launched a $1,000 Monero‑rewarded contest that challenges hackers to compromise open‑source packages using the Shai‑Hulud tool. Participants submit proof of access and compete on a leaderboard that scores based on download volume of the infected packages....

Instructure Settles with ShinyHunters, Recovers Data of 275 Million Users
Education‑tech firm Instructure announced a settlement with the ShinyHunters extortion group, securing the return of data belonging to 275 million users across 8,800 institutions. The deal, reached just before a May 12 deadline, ends a week‑long crisis that saw Canvas taken offline...

FlowerStorm Phishing Gang Adopts Virtual-Machine Obfuscation to Evade Email Defenses
Security researchers have identified that the FlowerStorm phishing-as-a-service operation is now employing KrakVM, an open‑source JavaScript virtual machine, to obfuscate credential‑stealing code delivered via HTML attachments. The VM‑based payload encrypts malicious bytecode, evading static analysis and traditional email‑security tools while...

Akamai to Acquire AI and Browser Security Firm LayerX for $205 Million
Akamai announced an all‑cash acquisition of LayerX for roughly $205 million. LayerX, a startup focused on AI‑driven browser security, brings a platform that monitors user and agentic activity across browsers, apps, and IDEs. The deal, expected to close in Q3 2026, adds...

How AI Is Silently Rewriting the Rules of Cyber Attacks
Artificial intelligence is reshaping cyber threats, allowing attackers to automate zero‑day discovery, craft polymorphic malware, and launch AI‑driven supply‑chain attacks such as the “Shy Hulud” worm. Nations like China, Russia and North Korea are integrating AI into espionage and infrastructure...

Chinese APT Exploits Microsoft Exchange to Breach Energy Sector Network
Chinese state‑aligned APT group FamousSparrow breached a major Azerbaijani energy firm by exploiting the ProxyNotShell chain on an unpatched Microsoft Exchange server on Dec. 25, 2025. The attackers deployed the Deed RAT via a LogMeIn Hamachi DLL sideloading technique and later attempted a...

Chinese APTs Expand Targets, Update Backdoors in Recent Campaigns
Chinese state‑sponsored groups Salt Typhoon and Twill Typhoon have broadened their target sets and refreshed their malware toolkits. Salt Typhoon used the ProxyNotShell exploit chain to breach Microsoft Exchange servers, deploying Deed RAT via DLL sideloading and later re‑introducing the TernDoor backdoor. Twill Typhoon...
Quiet Warfare: Bending Data and Perceptions in the Defense Industrial Base
Artificial intelligence is reshaping the threat environment for the U.S. Defense Industrial Base (DIB), where adversaries now run hybrid campaigns that blend cyber intrusion, supply‑chain manipulation, and information operations. The World Economic Forum’s 2026 Global Cybersecurity Outlook flags AI‑related vulnerabilities...

Foxconn Attack Highlights Manufacturing's Cyber Crisis
Foxconn confirmed a cyberattack at several North American factories, with the Nitrogen ransomware gang claiming responsibility. The gang alleges it exfiltrated over 11 million files, roughly 8 TB of data, including confidential designs for clients such as Apple, Nvidia and Google. While...

New Malware Framework Enables Screen Control and UAC Bypass
Researchers uncovered TencShell, a sophisticated malware framework built on the open‑source Rshell C2 tool and repurposed for stealthy post‑exploitation. In April 2026, Cato CTRL blocked an attack on a global manufacturing firm in India after the implant delivered Donut shellcode hidden...

PraisonAI Vulnerability Gets Scanned Within 4 Hours of Disclosure
A critical authentication bypass in the open‑source AI orchestration framework PraisonAI was actively scanned less than four hours after a GitHub advisory disclosed it. The flaw, tracked as CVE‑2026‑44338, disables authentication by default in a legacy Flask API server and...

Industrial Organizations Under Increasing Fire as Attackers Target Operational Technology
Industrial organizations faced a surge in ransomware, with 2,073 attacks representing 30% of all incidents in the year to March 2026. Capital‑goods manufacturers were hardest hit, recording 1,192 attacks, and the machinery sub‑sector alone suffered 442 incidents. Regulators in the...

Cybersecurity Awareness Rises—And Shifts
Cybersecurity consulting demand is accelerating, especially among mid‑market firms and small businesses, as the focus shifts from compliance to risk mitigation, revenue protection, and business continuity. Mid‑market companies are adopting hybrid models that blend lighter internal teams with external experts,...

170 Npm Packages Hijacked to Steal GitHub, AWS & Kubernetes Secrets
Hackers compromised more than 170 npm packages and two PyPI libraries, which together see over 200 million weekly downloads, to harvest developer and cloud credentials. The malicious packages embed pre‑install scripts that download obfuscated payloads, extract GitHub Actions tokens, npm publishing...

F5 Patches Over 50 Vulnerabilities
F5 Networks announced patches for more than 50 vulnerabilities affecting its BIG‑IP, BIG‑IQ and NGINX platforms, including 19 high‑severity and 32 medium‑severity flaws. The most critical issue, CVE‑2026‑42945, scores 9.2 and can cause a denial‑of‑service or code execution if ASLR...

China-Linked Twill Typhoon Uses Fake Apple and Yahoo Sites for Espionage
Security firm Darktrace has identified a new wave of espionage attacks across Japan and the broader Asia‑Pacific region, attributed to the China‑linked group Twill Typhoon. The actors disguise malicious payloads as legitimate software and host them on counterfeit Apple and...

Q&A: Why Vulnerability Scans Are Giving Businesses a False Sense of Security
In a recent interview, cybersecurity veteran Phillip Wylie warns that reliance on vulnerability scans and basic phishing tests gives organizations a false sense of security. He highlights how attackers now target overlooked assets such as security cameras, printers, and other...

Incognito Doesn't Hide You From ISP Tracking
Going "Incognito" won't stop your internet provider from tracking, throttling, and selling your browsing history. Here is exactly how they see what you do online, and the best ways to shut them out. https://t.co/AoRYElRgkw

Škoda Auto Online Shop Breach Exposes Customer Data
Škoda Auto disclosed that attackers exploited a vulnerability in its online shop software, gaining temporary access to personal customer information, including names, addresses, emails and hashed passwords. The carmaker took the site offline, engaged forensic experts and warned customers of...

Most Organizations Now Use AI Agents for Sensitive Security Tasks
A new Semperis study finds that 93% of global enterprises already use or plan to deploy AI agents for sensitive security functions such as password resets and VPN access. At the same time, 92% have these agents installed on machines...
Mistral Pitches Security-Focused Model As Mythos Alternative
Mistral AI, a French startup, is promoting a security‑focused generative model as a European alternative to Anthropic’s Claude Mythos. The company says its AI can scan code for vulnerabilities in high‑risk sectors such as banking and the military, and it...

ICO Publishes Five-Step Plan to Counter Emerging AI-Powered Attacks
The UK Information Commissioner’s Office (ICO) has issued a five‑step guide to counter the surge in AI‑driven cyber attacks, urging organisations to adopt multi‑layered defenses and align with the National Cyber Security Centre’s updated Cyber Assessment Framework. The guidance highlights...

Using Continuous Purple Teaming to Protect Fast-Paced Enterprise Environments
Enterprise security teams face ever‑changing attack surfaces as cloud adoption, infrastructure‑as‑code, and continuous delivery accelerate system turnover. Traditional periodic pen tests no longer reflect the current state, prompting a shift to continuous purple teaming, which fuses offensive (red) and defensive...

Exim BDAT Vulnerability Exposes Email Servers to Remote Attacks
A critical remote use‑after‑free flaw (CVE‑2026‑45185) was discovered in Exim mail servers that use GnuTLS, earning a CVSS score of 9.8. The vulnerability surfaces when a TLS close_notify alert interrupts an active BDAT transfer, allowing memory corruption and potential code...
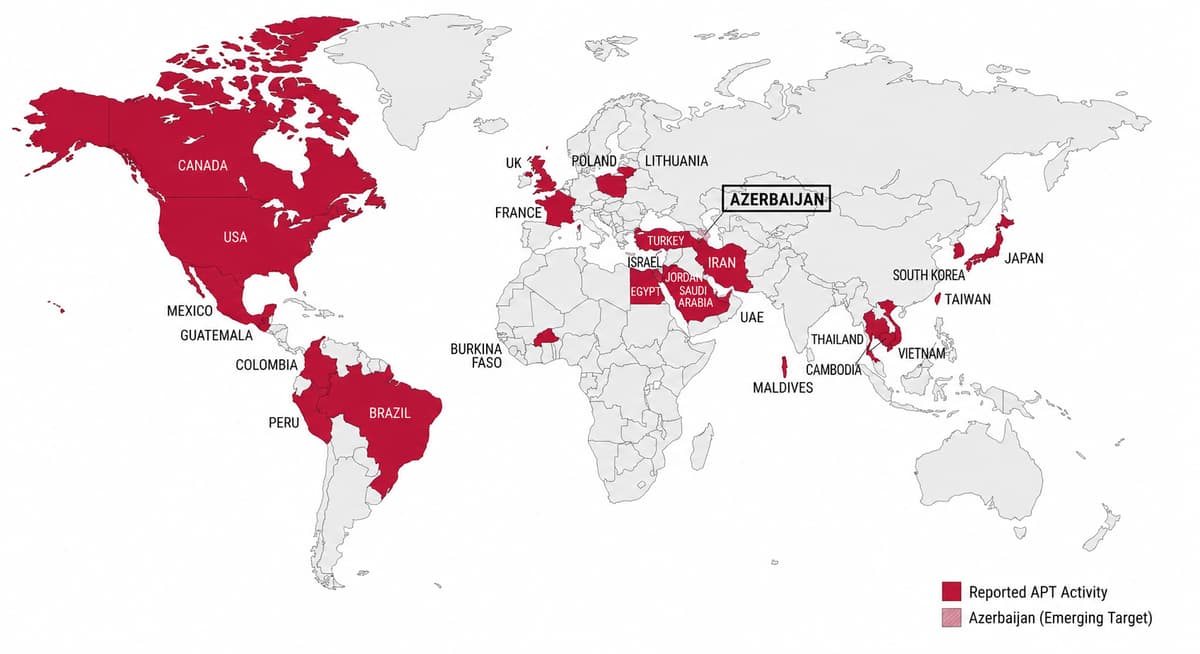
FamousSparrow Targets Azerbaijani Energy Sector in Multi-Wave Espionage Campaign
Chinese‑linked APT group FamousSparrow launched three intrusion waves against an Azerbaijani oil and gas firm from Dec 2025 to Feb 2026, repeatedly exploiting a vulnerable Microsoft Exchange server via the ProxyNotShell chain. The campaign deployed evolving payloads—Deed RAT, an attempted Terndoor backdoor,...

AI Cyberattacks Are Escalating Across the Americas. This Webinar Explains Why
In the first quarter of 2026 the Americas saw a sharp rise in AI‑powered cyberattacks, ransomware bursts, and assaults on critical infrastructure. Threat actors leveraged generative AI to automate phishing, deepfake creation, and rapid exploitation, making detection harder. Nation‑state groups...

Trading Firms Urged to Strengthen Vendor Oversight
At FINRA’s 2026 Annual Conference, a panel warned that AI‑driven fraud is making third‑party vendor risk harder to manage for financial firms. Speakers highlighted that cybercriminals now leverage inexpensive AI tools to launch sophisticated scams, forcing institutions to upgrade AI‑based...

Never Trust Nondeterministic AI Responses as Deterministic
LLMRisks Archive - OWASP Gen AI Security Project ~ just saw this. My number one would have been: Treating non-deterministic AI responses as deterministic and trusting them. https://t.co/psehlnxxXq

SANS Stormcast Thursday, May 14th, 2026: Flexbile Windows Proxy; News From Nightmare Eclipse; Adobe Patches
In this 5‑minute Stormcast episode, host Johannes Ulrich highlights Proxifier, a Windows tool that isolates application traffic for proxying to tools like Burp Suite, reducing noise in API testing. He then discusses two new vulnerabilities from researcher Nightmare Eclipse: Yellow...

Microsoft’s MDASH Agentic Security System Tops CyberGym Benchmark with 88.45% Score
Microsoft unveiled its multi‑model agentic scanning harness, MDASH, which discovered 16 new Windows vulnerabilities, earned an 88.45% score on the public CyberGym benchmark and beat the nearest competitor by roughly five points. The system, built by the Autonomous Code Security...

Pentagon Deploys Anthropic’s Mythos AI in “National Security Moment” Despite Blacklisting the Firm as a Supply-Chain Risk
The Pentagon has begun deploying Anthropic’s unreleased Mythos AI model to hunt for and patch software vulnerabilities across U.S. government systems. Mythos, part of the controlled Project Glasswing effort, can uncover decades‑old flaws in browsers, infrastructure and other code. The move...

AI Turns Fiber‑Optic Cables Into Spy Microphones, Study Warns Telecoms
University of Edinburgh researchers demonstrated that artificial intelligence can convert ordinary fiber‑optic cables into vibration sensors capable of reconstructing nearby conversations. The proof‑of‑concept, built on Distributed Acoustic Sensing (DAS) hardware, highlights a novel espionage vector that could force telecom operators...

Palo Alto Networks Launches Idira, AI‑Ready Identity Security Platform
Palo Alto Networks unveiled Idira, a next‑generation identity security platform that extends privileged access management to humans, machines and agentic AI identities. The solution aims to eliminate standing privileges and address the surge in AI‑driven attack vectors that now affect...

Mini Shai‑Hulud Worm Infects 172 Npm and PyPI Packages, Threatening 518 M+ Downloads
TeamPCP’s Mini Shai‑Hulud worm injected malicious code into 172 open‑source packages on npm and PyPI, creating 403 poisoned versions that have been downloaded more than 518 million times. The attack bypassed two‑factor authentication and valid SLSA provenance, prompting urgent remediation across the...

Fired Employee Sought AI Help to Hide Deletion of Hosting Firm’s Customer Data
A Virginia jury convicted former hosting‑firm employee Sohaib Akhter for using an AI chatbot to learn how to erase system logs and delete 96 federal databases after he and his brother were terminated. The brothers retained company laptops and privileged...

Researchers Say AI Just Broke Every Benchmark for Autonomous Cyber Capability
Researchers at the UK AI Security Institute and Palo Alto Networks found that Anthropic’s Claude Mythos Preview and OpenAI’s GPT‑5.5 have outpaced the previously observed doubling trend in autonomous cybersecurity task performance. In AISI’s cyber‑range simulations, Claude Mythos completed both...

Attackers Weaponize RubyGems for Data Dead Drops
Security firm Socket uncovered a new threat campaign, dubbed GemStuffer, that abuses the RubyGems package registry as a dead‑drop for exfiltrated data. Over 100 malicious gems were published, each containing scripts that scrape public council data in London and then...

The Reality of Implementing Zero Trust for Defense Operational Technology
The Department of Defense issued new guidance in late 2025 that tailors Zero Trust principles specifically for operational technology (OT). The policy separates IT‑focused standards from OT requirements, acknowledging that legacy controllers and diverse process equipment cannot support traditional software‑based...

The Next Phase of Zero Trust: From Recognizing Known Threats to Stopping Threats
The Federal Zero Trust Strategy (M‑22‑09) gave agencies measurable goals such as phishing‑resistant MFA and endpoint detection, reshaping U.S. government cybersecurity. However, the focus on identifying known threats leaves a gap as adversaries employ novel, AI‑driven attacks that evade static...

Google Thwarts Massive Exploit by Securing Gemini APIs
On Google having disrupted a planned mass exploit: "In the last year, Google, Android, Chrome, etc., built Gemini in everywhere. "They found someone calling those APIs to say, 'Go find the attack surface and do exfiltration on the fly.'" 😱 --...

Cushman & Wakefield Hit with Class‑Action Over Data‑Breach Handling
Cushman & Wakefield, the $10.3 billion‑revenue global real‑estate firm, was sued in New York last Friday over alleged negligence after a hacker breach exposed personal data of current and former tenants. The lawsuit claims the firm failed to implement industry‑standard cybersecurity...