Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB

How Advanced Security Solutions Support Recruitment, Employee Privacy, and Business Growth
Enterprises are shifting from data‑center‑centric firewalls to Secure Access Service Edge (SASE) as workforces become distributed and cloud workloads proliferate. The article profiles five leading SASE providers—Fortinet, Zscaler, Cato Networks, Versa Networks, and Netskope—highlighting each vendor’s architectural focus, from unified operating systems to cloud‑native stacks and private backbones. It explains how these platforms converge networking and security to enforce consistent policies across users, devices, and applications wherever they reside. Selecting the right solution depends on an organization’s traffic mix, data‑protection needs, and management capacity.

Kimsuky Deploys HTTPSpy, Expands Arsenal with HelloDoor and VS Code Tunnels
North Korean threat group Kimsuky intensified its 2026 campaign against South Korean military and corporate targets by deploying the HTTPSpy RAT through counterfeit security‑software installers and a fake Webex meeting page. The group introduced a novel "JSONPing" technique to verify...
The Behavioral Signals that Sharpen Trojan Malware Detection
A recent study introduced a Trojan detection framework that trims 146 sandbox‑derived attributes down to 33 high‑impact features and feeds them into a custom neural network (TrDNN). Tested on 3,000 Windows executables—including benign, suspicious, and malicious samples—the model outperformed ten...
From the Hammer to the Scalpel: The Evolution of Account Takeover
Account takeover (ATO) attacks have shifted from high‑volume credential stuffing to AI‑enhanced social engineering that co‑opts victims into authorizing fraud. Modern attackers use hyper‑personalized phishing, voice synthesis, and authorized fraud techniques, making transactions appear legitimate. Defenders are responding with AI‑driven...

Hackers Don’t Need Your Passwords. They Just Need Your HVAC Contractor.
Building automation systems (BAS) have shifted from isolated controllers to cloud‑connected ecosystems, expanding a $124 billion market to an estimated $204 billion by 2030 and creating a massive attack surface. Legacy protocols like BACnet and Modbus lack encryption, while remote‑access paths for...

Red Hat MicroShift 4.16.63: Important Security Update for Kubernetes at the Edge of the Infrastructure
Red Hat issued Security Advisory RHSA‑2026:20436 on May 28, 2026, classifying the MicroShift 4.16.63 update as “Important.” The patch addresses CVE‑2026‑33186, a gRPC‑Go authorization bypass affecting HTTP/2 path validation. It covers multiple architectures—including x86_64, ARM64, IBM Z, LinuxONE, and Power—used in single‑node edge Kubernetes deployments....

Perplexity Launches Open-Source Bumblebee Scanner to Check Developer Laptops for Malicious Packages, Extensions, and AI Tool Configs
Perplexity has released Bumblebee, an open‑source, read‑only scanner that inspects developer laptops for malicious packages, editor extensions, browser add‑ons, and AI tool configurations. The Go‑based utility runs on macOS and Linux under an Apache 2.0 license and requires no subscription. It...
Lack of Response to Critical Vulnerability in Gogs Is a Reminder of the Limits of Open Source Projects
Rapid7 uncovered a critical argument‑injection flaw in the open‑source Gogs Git service that lets any authenticated user execute code remotely by creating a malicious branch name during a merge. The vulnerability remains unpatched after more than two months, and the...

Anthropic’s Mythos AI Flags Over 10,000 Critical Flaws, Raising DevOps Alarm
Anthropic’s Mythos AI discovered more than 10,000 high‑ or critical‑severity software vulnerabilities in its first month, prompting partners like Cloudflare and Mozilla to report ten‑fold bug‑finding gains while exposing a human‑capacity bottleneck in triage and patching.

Adtran Shares Jump 17% on Quantum‑Safe Connectivity Deal with euNetworks
Adtran Holdings saw its shares climb 17.2% after announcing a collaboration with European data‑center carrier euNetworks to launch Quantum Shield, a quantum‑safe private connectivity service. The partnership positions the optical‑connectivity specialist at the forefront of telecom‑driven quantum cybersecurity, a sector...

Security Notice: Former Helm APT Mirror Domain `baltocdn.com` Statement
The Helm project’s community‑maintained APT mirror at baltocdn.com was decommissioned in September 2025, and the domain registration expired. It was re‑registered by a third party on May 19 2026, and reports suggest the new owner may be serving malicious content. Helm users who...
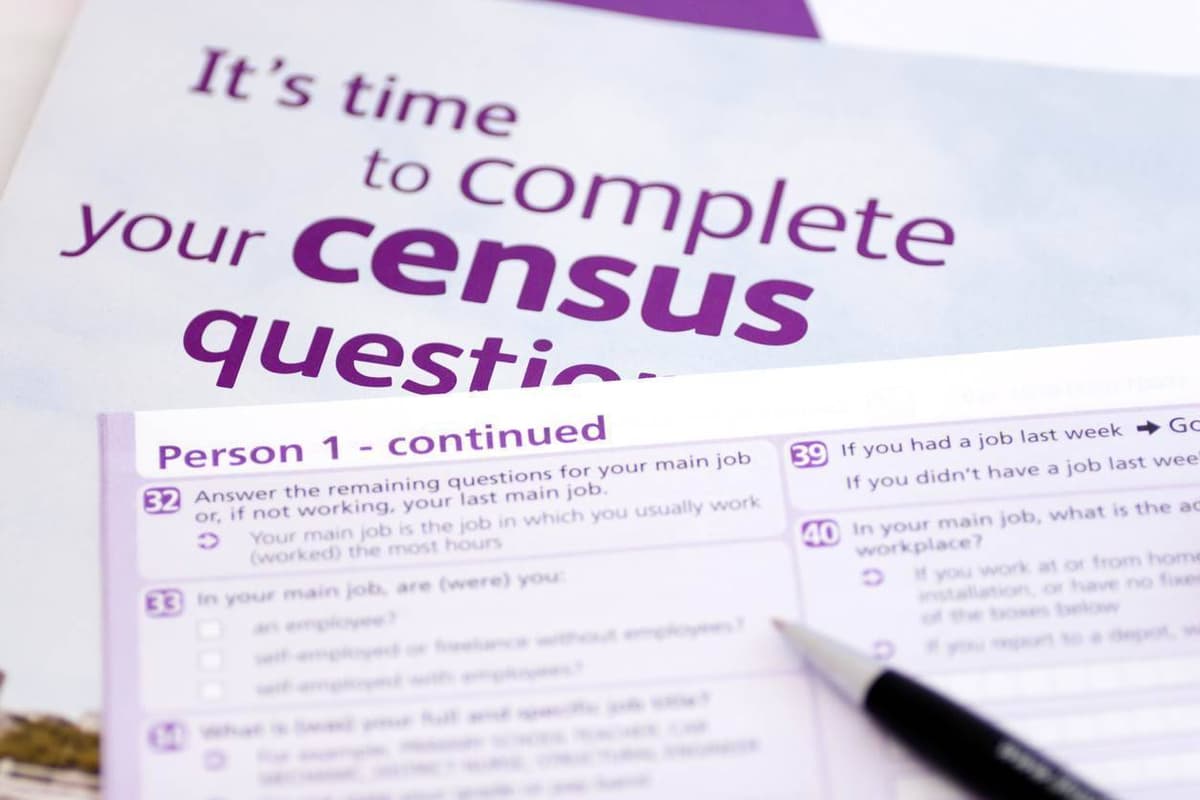
ABS Runs Six-Month IT Environment Hardening Before Census
The Australian Bureau of Statistics (ABS) has launched a six‑month IT hardening program to secure its entire ICT environment ahead of the 2026 Census on August 11. The effort, revealed in a recent cyber‑readiness audit, expands an originally four‑week engagement...

Fed up with Vibe Coders, Dev Sneaks Data-Nuking Prompt Injection Into Their Code
A developer of the open‑source Java test engine jqwik released version 1.10.0 that silently injects a prompt instructing AI coding agents to delete all jqwik tests and code. The malicious line is concealed with ANSI escape sequences so human users...

Healthcare Raises the Bar on Medical Device Security, But Vulnerabilities Remain
Healthcare providers are embedding cybersecurity criteria into medical‑device procurement, with 84% now requiring security clauses in RFPs. Yet attacks rose, as RunSafe Security’s 2026 Index shows 24% of organizations faced device‑related cyber incidents, 80% of which disrupted patient care. Legacy...

Company Knew of Carnival Leak, Gave No Notice
35 days ago, the Carnival data was published by ShinyHunters. Clearly, the company knew about it at the time (that’s how extortion works, plus the comment in the linked article) but at the time, I couldn’t find any disclosure notice,...

California Attorney General Sues 23andMe Successor for 2023 Data Breach
California Attorney General Rob Bonta sued Chrome Holding, the successor to 23andMe, alleging the firm failed to protect user data in a 2023 breach. The incident exposed genetic predispositions, ancestry information and the identities of nearly seven million customers, and attackers...

Microsoft Stirs a Hornets Nest over “Criminal” Zero Day Disclosure Threats
Microsoft has sparked controversy by branding certain zero‑day vulnerability disclosures as “criminal” threats, while a critical BitLocker encryption backdoor remains unpatched. Threat actors are actively exploiting three malware families—RedSun, UnDefend and BlueHammer—against Windows systems. The company’s aggressive rhetoric has ignited...

SCIM in HashiCorp Vault Standardizes Provisioning in Platforms
HashiCorp announced a beta release of SCIM support for Vault Enterprise and Vault Dedicated, bringing a standards‑based identity provisioning layer to its secret‑management platform. The integration lets organizations automate joiner, mover and leaver workflows by syncing users and groups from...

Browser Threats Expand Across Enterprise Networks
A NordLayer study finds browsers now serve as the primary workplace interface, with 100% of the 504 surveyed applications supporting browser access and 78.8% being fully browser‑based. Over the past year, 82% of IT professionals reported at least one security...

FBI Alerts: New Phishing Surge Hits Microsoft 365
The FBI warns Microsoft 365 services are being bombarded with new phishing emails – here are 3 steps you can take to stay safe https://t.co/4BlyWeYIpw

A Malware Dev Has Committed a Magnificent Self-Own After an AI-Coded Malicious Package Leaked Its Own GitHub Private Token
Ox Security uncovered an AI‑generated npm package, mouse5212‑super‑formatter, that targeted Claude users and stole files by uploading them to a GitHub repository. The malicious code inadvertently exposed its own private GitHub token, allowing researchers to trace the attacker’s activity. The...

Cruise Operator Carnival Discloses Personal Data Breach
Carnival Corp disclosed a data breach on May 27 after a compromised employee account in April exposed names, addresses and government‑issued identification numbers. The company halted the intrusion, engaged third‑party investigators and is notifying affected parties. U.S. customers receive two years...

Cogent Security Launches AI‑driven Platform to Cut Vulnerability Remediation to Hours
Cogent Security introduced Zero Day Response and Autonomous Remediation, AI‑powered features that shrink the gap between vulnerability disclosure and fix from weeks to hours. The startup says Fortune 500 users have cut mean time to remediate critical flaws by 97%,...

ShinyHunters Claims Theft of up to 40 Million Charter Records via Microsoft Entra Breach
ShinyHunters says it stole as many as 40 million consumer and business records from Charter Communications by compromising a Microsoft Entra employee account. Charter acknowledges the breach but maintains that no sensitive personal or network information was exfiltrated.

Google Cloud Responds to AI-Accelerated Cyberattacks with a Platform that Aims to Close Security Gaps in Minutes
Google Cloud unveiled AI Threat Defense, an end‑to‑end platform that automatically discovers, evaluates, and patches security flaws across enterprise environments. The solution stitches together Gemini for code analysis, Wiz’s risk‑assessment engine (acquired for $32 billion), DeepMind’s Codemender for auto‑generating patches, and...

Attackers Move Past Typosquatting to Realistic Package Impersonation
Sonatype’s latest research of 4,309 malicious open‑source packages reveals a dramatic shift away from classic typosquatting. Only 9% of the threats rely on misspelled names, while 91% use naming‑variant tactics such as suffixes, prefixes, and version mimicry. The most common...

Resecurity Supports Microsoft DCU in Disrupting Fox Tempest ’S Cybercriminal Code-Signing Ecosystem
Microsoft’s Digital Crimes Unit, with Resecurity’s assistance, dismantled Fox Tempest—a malware‑signing‑as‑a‑service that leveraged counterfeit Microsoft code‑signing certificates. On May 19, 2026, the agency seized the signspace.cloud site, shut down hundreds of virtual machines, and revoked more than 1,000 fraudulent certificates....

Threat Actors Exploit Critical FortiClient EMS Flaw to Deploy Credential Stealer
Threat actors exploited a critical pre‑authentication API bypass (CVE‑2026‑35616) in FortiClient Endpoint Management Server to push a credential‑stealing payload disguised as a legitimate update. The attack leveraged the legitimate fortitray.exe to run a Base64‑encoded PowerShell script that downloaded FortiEndpoint_Patch.exe, harvesting...

Christophe Pettus: Twenty Years, Three CVEs, One AI
PostgreSQL has released patches for three heap‑buffer overflow CVEs (CVE‑2026‑2005, CVE‑2026‑2006, CVE‑2026‑2007) affecting the pgcrypto and pg_trgm extensions. The most severe flaw, in pgcrypto’s PGP handler, enables arbitrary code execution under the PostgreSQL OS user. Two of the bugs were...
Expansion Of Mythos-Level LLMs Makes Exploitability The Key Focus: CISO
Anthropic’s Claude Mythos, a frontier LLM designed for automated vulnerability discovery, is expected to become publicly available within the next six to twelve months. Optiv CISO Rob Gregory says this development forces organizations to move from counting total vulnerabilities to prioritizing...
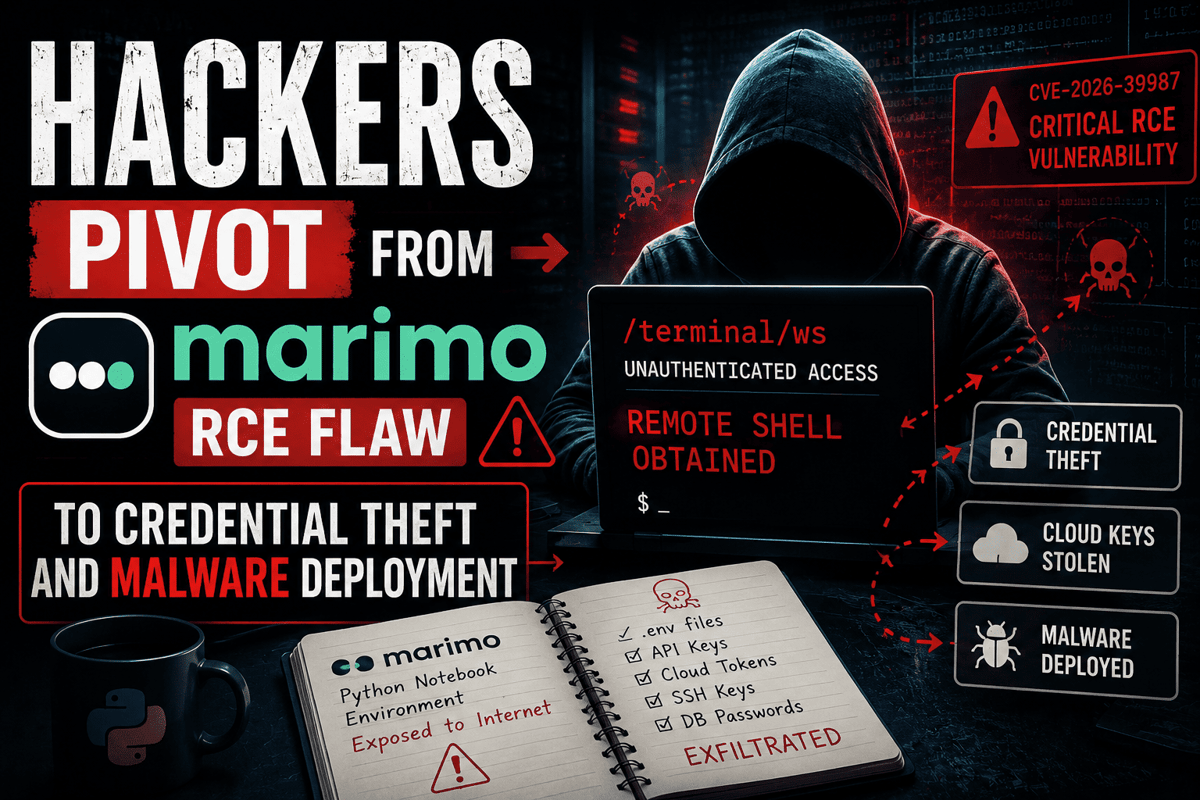
Hackers Pivot From Marimo RCE Flaw to Credential Theft and Malware Deployment
Researchers have confirmed active exploitation of the critical Marimo remote‑code‑execution flaw (CVE‑2026‑39987), which grants unauthenticated shell access via the /terminal/ws WebSocket endpoint. Attackers moved from initial compromise to rapid credential harvesting, targeting .env files, SSH keys, API tokens, and database...

Cruise Giant Carnival Confirms Data Breach Affecting Nearly 6 Million People
Carnival Corp. confirmed that a cyberattack attributed to the ShinyHunters group stole personal data of nearly six million individuals, including passports and driver’s license numbers. The breach originated from a compromised employee account in April, with attackers copying data by...
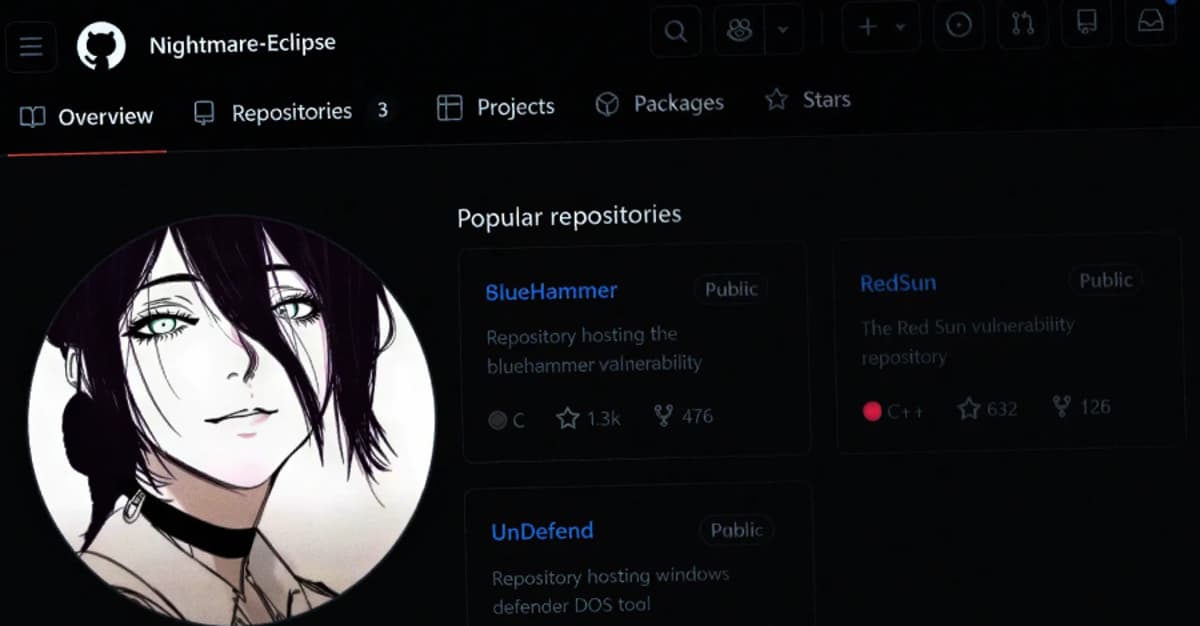
Microsoft Slams Public Zero-Day Disclosures Amid GitHub Researcher Account Removal
Microsoft publicly rebuked the recent public disclosure of six Windows zero‑day flaws after researcher Chaotic Eclipse released details without prior coordination. The vulnerabilities—BlueHammer (CVE‑2026‑33825), RedSun (CVE‑2026‑41091), UnDefend (CVE‑2026‑45498), YellowKey (CVE‑2026‑45585), plus GreenPlasma and MiniPlasma—include active exploitation of three flaws. Microsoft...

Check Point Launches AI Agents That Think Like Attackers as Autonomous Exploitation Reaches Critical Threat Level
Check Point introduced Agentic Exposure Validation (AEV), an AI‑driven module in its Exposure Management platform that deploys autonomous agents to reason like attackers and prove which vulnerabilities are truly exploitable. The launch arrives as frontier AI models have accelerated exploit...

Microsoft’s Stance on Zero Day Exploits Is a Dumpster Fire of Their Own Making
Microsoft’s recent blog declares publishing zero‑day proof‑of‑concept exploits as criminal activity, a stance that sparked backlash after researcher Nightmare Eclipse was banned from GitHub, GitLab, and Microsoft’s vulnerability portal. The author highlights the inconsistency of Microsoft’s policy, noting the company...

Adversa AI Unveils ‘SymJack’ Attack That Turns AI Coding Agents Into Supply‑Chain Malware Vectors
Adversa AI disclosed a novel supply‑chain attack named SymJack that weaponizes AI‑driven coding assistants to deliver hidden malicious code into continuous‑integration pipelines. The technique leverages malicious repositories and disguised symlinks, allowing attackers to exfiltrate secrets or sabotage production with a...

DJI Releases Findings of the Most Comprehensive Independent Security Assessment of Its Drone Systems to Date
DJI released the results of a five‑month independent security assessment by U.S. firm OnDefend on its Air 3S and Matrice 4E drones. The testing uncovered zero critical, high, or medium‑risk vulnerabilities across software, hardware, and radio‑frequency domains. Ten low‑risk issues were noted,...

Adtran Holdings Shares Jump 17% on Quantum‑Safe Connectivity Deal with euNetworks
Adtran Holdings' stock surged 17.2% after the company unveiled Quantum Shield, a quantum‑safe private connectivity service developed with European data‑center carrier euNetworks. The partnership aims to protect high‑capacity traffic with quantum‑resilient encryption and real‑time fiber monitoring, positioning Adtran at the...

CrowdStrike, Google, Shadowserver Dismantle Glassworm Botnet Threatening Developers
CrowdStrike, Google and the Shadowserver Foundation announced on May 26, 2026 that they have taken down the Glassworm botnet by simultaneously disabling all four of its command‑and‑control channels. The botnet, active since early 2025, infected VS Code extensions, npm/Python packages and...

Ransomware Gang Play Threatens MyPillow with Data Dump, Citing Political Motive
The Play ransomware group announced it has exfiltrated confidential client, payroll and financial records from MyPillow and set a Friday deadline for a response. CEO Mike Lindell dismissed the claim as a politically motivated hit job, while warning of $400 million...

Indian CERT Urges Firms to Contain Exploited Internet-Facing Flaws Within 12 Hours
India’s cybersecurity agency CERT‑In issued a 38‑page blueprint urging firms to patch, mitigate, or isolate exploited internet‑facing "crown jewel" systems within 12 hours where feasible. The framework sets one‑day remediation for critical external flaws, three days for critical internal vulnerabilities, and...

NordVPN Isn't Just a VPN Anymore, but a Full Security Suite - Here's What You Get Now
NordVPN is rebranding its consumer app into a comprehensive security suite that merges its traditional VPN service with next‑generation antivirus and threat‑monitoring tools. The revamped offering is organized around three pillars—Connect (VPN), Protect (antivirus), and Monitor (dark‑web, phishing, and data‑breach...

AI-Driven Attacks Shrink Window for Vulnerability Remediation
AI is dramatically accelerating cyber‑attack speed, scale and cost efficiency, forcing enterprises to shrink remediation windows. Threat actors now use AI to automate social engineering, exploit identity, endpoint and cloud exposures, with average breakout times falling to 29 minutes. Pentera...

Supply Chain Battles Intensify as Takedowns Meet AI-Driven Noise
On May 26, CrowdStrike, Google and the Shadowserver Foundation dismantled the GlassWorm botnet, cutting off its four command‑and‑control channels and halting the distribution of malicious VSCode extensions and compromised npm and Python packages. The takedown illustrates coordinated disruption of open‑source...

Managed Security Firewalls: A Practical Guide to Stronger Threat Protection
Managed security firewalls add continuous oversight to traditional perimeter defenses, ensuring rules stay current, patches are applied promptly, and alerts are triaged around the clock. The service typically includes rule review, software updates, 24/7 monitoring, and executive‑level reporting, turning a...

National Cyber Shield Could Be Ready in Five Years
The UK’s signals intelligence agency GCHQ announced a five‑year plan to deploy an AI‑driven "national cyber shield" that will automatically detect and remediate threats to critical infrastructure such as energy, water, health, transport and finance. The system will embed agentic...

UK Unveils Energy Cyber Security Strategy
Britain has launched a four‑year Energy Sector Cyber Security Strategy designed to embed cyber resilience across its evolving power system. The plan, coordinated by the National Energy System Operator, Ofgem and the National Cyber Security Centre, targets renewable, nuclear and...

Why Your Email Account Is the Most Valuable Target You Are Overlooking
Email accounts have become the de‑facto identity hub for individuals and enterprises, linking banking, payroll, HR, health, and legal services. Because passwords, account recovery, and two‑factor verification all flow through the inbox, a compromised email provides a direct pathway to...

How Deno’s New Firewall Stops AI Agents From Leaking Passwords
Deno has open‑sourced Claw Patrol, a firewall that sits between AI agents and external systems to protect credentials, control actions, and monitor activity in real time. The framework uses HashiCorp Configuration Language for flexible rule definition and supports secure tunnels...
Bad Vibes: AI-Generated Code Is Vulnerable, Researchers Warn
Georgia Tech researchers have unveiled the Vibe Security Radar, a tool that scans public vulnerability databases to identify security flaws introduced by AI‑generated code. The radar has already flagged 74 vulnerabilities, including 14 critical and 25 high‑severity issues such as...