Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, patched in June 2026; and Linux CVE‑2022‑0492, a kernel flaw also deemed actively exploited.
Also developing:
By the numbers: Ingeteam secures $82.5M loan from EIB for renewable energy R&D

RaccoonLine Publishes Analysis of How P2P Node Networks Eliminate Single Points of Failure in VPN Infrastructure
RaccoonLine released an analysis highlighting how traditional, centralized VPN services create single points of failure that can be exploited by governments, as seen in recent server withdrawals from India and a seized ExpressVPN node in Turkey. The report contrasts this with peer‑to‑peer (P2P) node networks, which distribute traffic across independent operators worldwide, eliminating a single target for seizure or blocking. By leveraging protocols like VLESS with obfuscation, P2P VPNs can resist protocol‑level censorship. RaccoonLine positions its decentralized VPN as a resilient alternative with built‑in file storage and cross‑platform clients.

Malaysia Mandates Age Checks for Social Media Users, ID Verification for Advertisers
Malaysia's National Cyber Security Agency has made age verification mandatory for all new social media accounts, barring users under 16. Verification uses the MyKad smart ID and live facial biometrics through the MyDigital ID platform, which confirms age without storing...
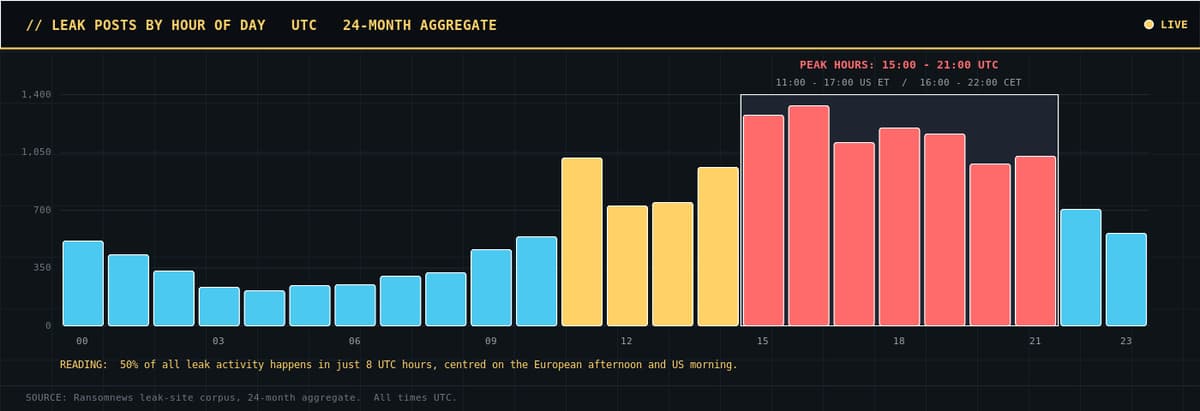
Ransomware Operators Keep Business Hours. The Data Proves It
A new Ransomnews study of 16,699 ransomware leak posts across 200 groups shows that attackers operate on a conventional workweek, with an 84% drop in activity on weekends and a peak between 15:00‑22:59 UTC (11:00‑18:00 ET). October consistently spikes, delivering 30‑70%...

Brinqa Is Building the Context Layer that Enterprise Security Is Missing
Brinqa provides a unified context layer for enterprise security, pulling signals from more than 240 tools into a cloud‑native Cyber Risk Graph that prioritizes the vulnerabilities that truly matter. Backed by a $110 million Insight Partners round and led by new...
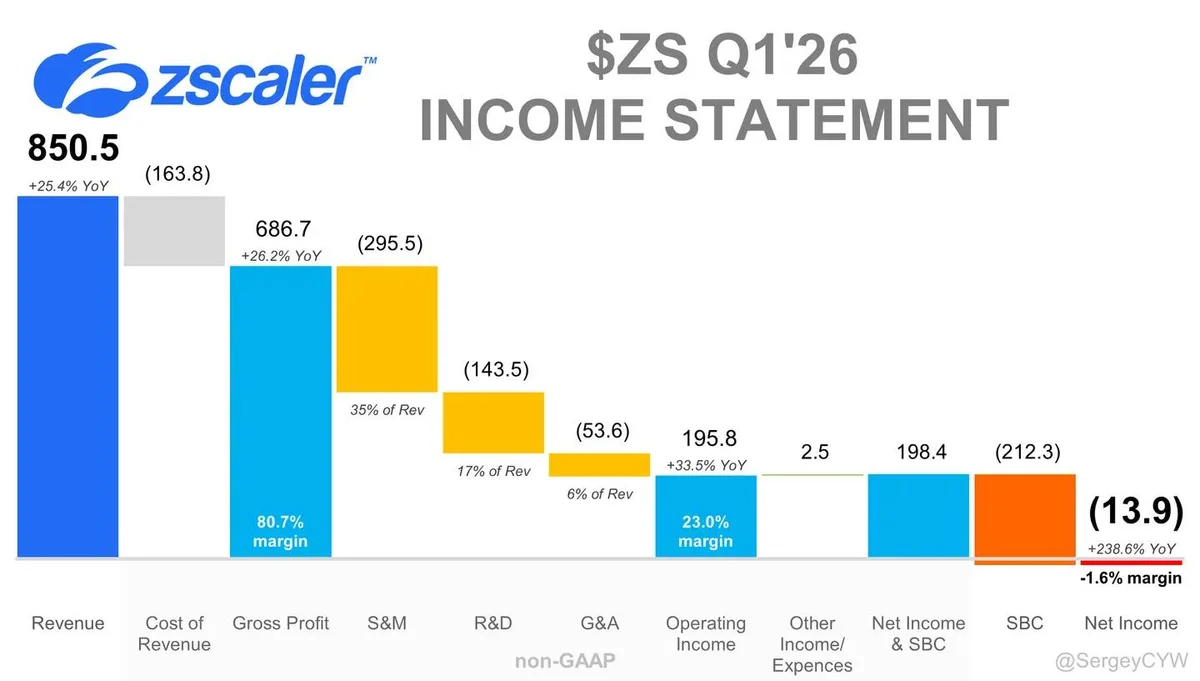
Zscaler Launches AI-Guardian for Zero Trust AI Agents
Zscaler is building Zero Trust security for the AI-agent era $ZS is expanding its AI security platform as enterprises move from traditional apps to autonomous AI systems. AI agents create a different security problem. They access data, trigger actions, inherit permissions, and...

Palo Alto Networks GlobalProtect Auth Bypass (CVE‑2026‑0257) Actively Exploited
Palo Alto Networks confirmed that CVE‑2026‑0257, a remote authentication‑override flaw in PAN‑OS and Prisma Access GlobalProtect, is being actively exploited. The vulnerability was added to the CISA Known Exploited Vulnerabilities catalog on May 29, 2026, and rapid‑response patches have been...

Nine in Ten Security Leaders Concerned About AI-Generated Code Risks as Salt Security Launches New Governance Tool
A Salt Security study of 100 UK and US security leaders finds that nine in ten are worried about risks from AI‑generated code, while 67% report widespread use of AI coding assistants. Only 38% still depend on manual code reviews,...

Zero-Click Pretalx XSS Flaw Lets Hackers Hijack Conference Organizer Accounts
Cybersecurity firm Novee Security disclosed a high‑severity stored XSS flaw (CVE‑2026‑41241) in the open‑source conference management platform pretalx, earning an 8.7 CVSS score. The vulnerability allows any registered user to inject malicious HTML or JavaScript into the organizer‑side search dropdown,...
Critical Windows Netlogon RCE Flaw Now Exploited in Attacks
A critical Windows Netlogon vulnerability (CVE‑2026‑41089) that enables remote code execution on domain controllers was patched by Microsoft in the May 2026 Patch Tuesday. The Centre for Cybersecurity Belgium (CCB) has confirmed that threat actors are already exploiting the flaw in...

Cohesity and CISA Announce Cybersecurity Information Sharing Partnership
Cohesity announced a partnership with the U.S. Cybersecurity and Infrastructure Security Agency (CISA) to create a voluntary framework for sharing cybersecurity information. The collaboration will enable direct exchanges of threat alerts, malware analysis, and indicator bulletins, as well as participation...

Password Manager Dashlane Suspends Customer Accounts Amid Brute-Force Attacks
Dashlane temporarily disabled a number of user accounts after detecting a wave of brute‑force login attempts originating from overseas IP addresses. The company investigated the incidents on Sunday, restored the affected accounts by evening, and moved the incident status to...

FSB Group Gamaredon Hides Worm in Windows Data Streams
Sekoia’s analysis uncovers a new Gamaredon worm, GammaWorm, that embeds its components in NTFS Alternate Data Streams, allowing it to spread across Ukrainian networks with minimal on‑disk footprints. The infection chain begins with a malicious RAR archive exploiting the WinRAR...

Linux 7.2 Proceeding To Deprecate AF_ALG Due To "Massive Attack Surface", Drops Offloading
The upcoming Linux 7.2 kernel will fully deprecate the AF_ALG socket interface, which lets user‑space programs access the kernel’s built‑in cryptographic engine. Kernel maintainer Eric Biggers cites a “massive attack surface” exposed by AF_ALG, amplified by AI‑driven vulnerability tools. The deprecation also...
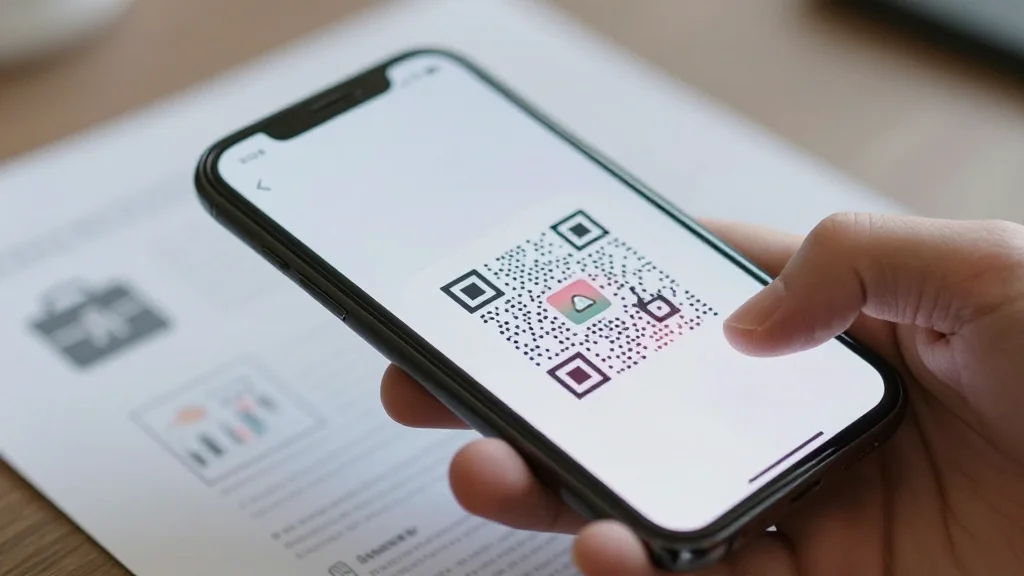
QR Code Phishing Targets Employee Performance Reviews, Raising HRTech Security Alarm
A phishing campaign using fake HR performance review emails and QR codes has been uncovered, urging employees to scan malicious links before a May 15, 2026 deadline. The scam exploits trust in HR communications, underscoring urgent security challenges for HR...

Anthropic to Give EU’s Cybersecurity Agency Access to Mythos
Anthropic PBC will grant the EU’s cybersecurity agency ENISA access to Mythos, its AI system that discovers and exploits software vulnerabilities. ENISA will join Project Glasswing, a pilot allowing vetted organizations to test Mythos before a wider rollout. The collaboration...

Hackers Are Already Laying Groundwork to Disrupt the 2026 Midterms, Research Says
Cybersecurity firm Check Point warns that hackers are already laying groundwork to disrupt the 2026 U.S. midterm elections. The report highlights a shift from targeting voting machines to exploiting campaign accounts, fundraising platforms, and local‑government web infrastructure through phishing, credential...
OpenAI Codex Authentication Tokens Stolen in Codexui-Android Npm Supply Chain Attack
Security researchers have uncovered a supply‑chain attack targeting the npm package codexui-android, which masquerades as a remote UI for OpenAI Codex. The malicious code silently reads the ~/.codex/auth.json file and sends access, refresh and ID tokens to an attacker‑controlled server...
Websites Can Now Spy on You Through Your Hard Drive
Researchers have unveiled a new side‑channel attack called FROST that lets websites infer SSD activity from JavaScript running in the browser. By measuring subtle timing differences in read/write operations, malicious sites can infer files stored on a user’s hard drive...

Why Non-Production Data Is Becoming Enterprises’ Biggest Compliance Blind Spot
Enterprises are facing a surge in sensitive data sprawl across non‑production environments as DevOps velocity, analytics workloads, and AI training pipelines multiply data copies. The Perforce Delphix 2025 State of Data Compliance and Security Report shows 60% of organizations suffered...
Geordie Closes $30M in Funding to Help Enterprises Securely Adopt Agentic AI at Scale
Geordie AI closed a $30 million Series A led by Balderton Capital, bringing total funding to $36.5 million and earmarking the cash for product development and U.S. expansion. The platform gives enterprises real‑time visibility into AI agents and uses its Beam runtime suite...
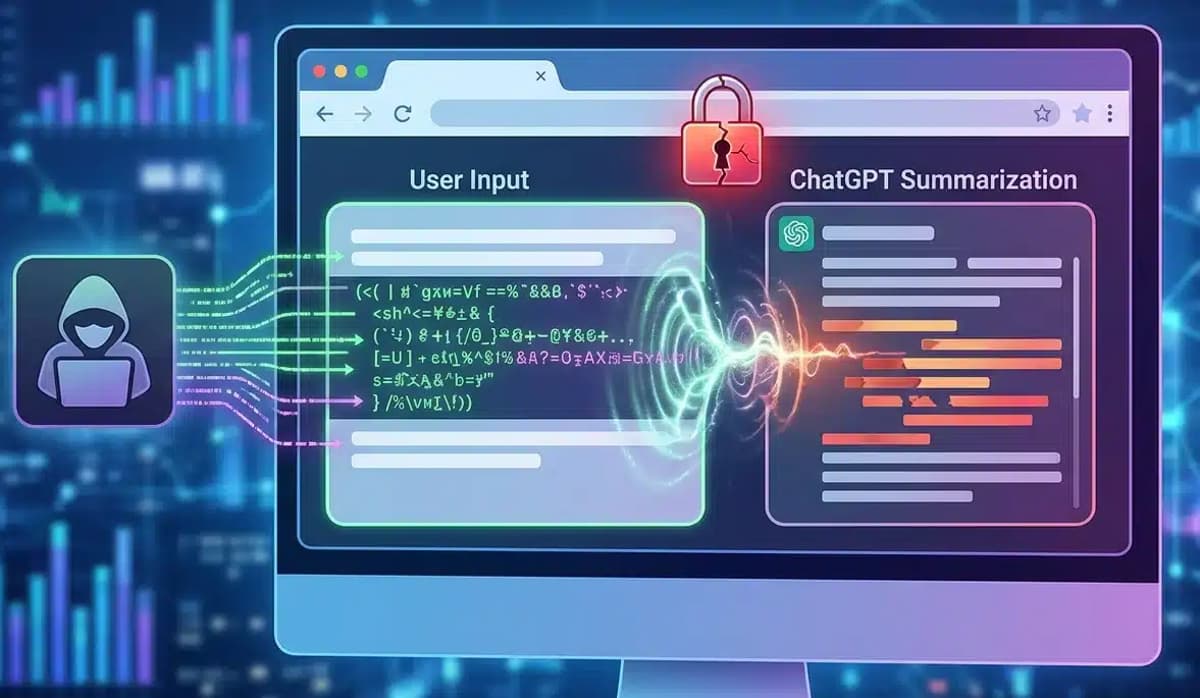
New ChatGPhish Technique Uses Prompt Injection to Manipulate ChatGPT Responses
Security researchers have disclosed "ChatGPhish," a novel browser‑based prompt‑injection technique that manipulates ChatGPT's page‑summarization feature. By embedding malicious instructions in ordinary web pages, attackers can coerce the model into appending phishing alerts, links, or QR codes to otherwise legitimate summaries....
A Fake UK Visa Site Has Been Leaking 100,000 Passports and Selfies for Weeks, and the Part Nobody Is Talking...
A fraudulent website posing as a UK visa portal has left over 100,000 passport scans and selfie photos publicly accessible, according to a TechCrunch report on May 26. The breach stems from the site’s collection of biometric data for electronic...

#482 Mr. Beast's Episode
In this episode of Python Bytes, Michael Kennedy and Brian Hocken discuss a recent security advisory (CVE‑2026‑48710) affecting the Starlette framework, emphasizing the importance of promptly upgrading to version 1.0.1 and highlighting the challenges volunteer maintainers face in keeping open‑source...
Tips for Protecting Against Retail Cyberattacks
Retail remains the top cyber‑crime target, accounting for roughly 24% of all attacks, according to Fortinet. Hackers exploit the myriad of customer‑facing apps, loyalty programs, payment systems and third‑party integrations that retailers rely on, while many firms operate with lean...

Budget 2026: New Zealand Funds Digital Health Upgrades, Cybersec
The New Zealand government’s Budget 2026 earmarks roughly NZ$450 million ($270 million) for health‑sector digital upgrades and cybersecurity. NZ$153.6 million ($91.7 million) will fund a 24/7 national cyber‑monitoring programme under Te Whatu Ora, while NZ$300 million ($179 million) supports the first three years of the Health Digital Investment Plan, replacing...
Privacy Watchdog Faults Operator, Health NZ over Manage My Health Hack
New Zealand’s Privacy Commissioner concluded that Te Whatu Ora Health New Zealand and Manage My Health Ltd breached Rule 5 of the Health Information Privacy Code after a cyberattack compromised the My Health Documents portal. Approximately 99,416 patients—mostly in Northland—had personal and...

6 Critical Security Gaps Every CISO Must Address
A recent Proofpoint survey shows one‑third of CISOs believe their data isn’t adequately protected and 58% feel unprepared for a cyberattack, while only 67% think they have sufficient budget, staff, and tools. Experts identify six critical gaps: perception of security...
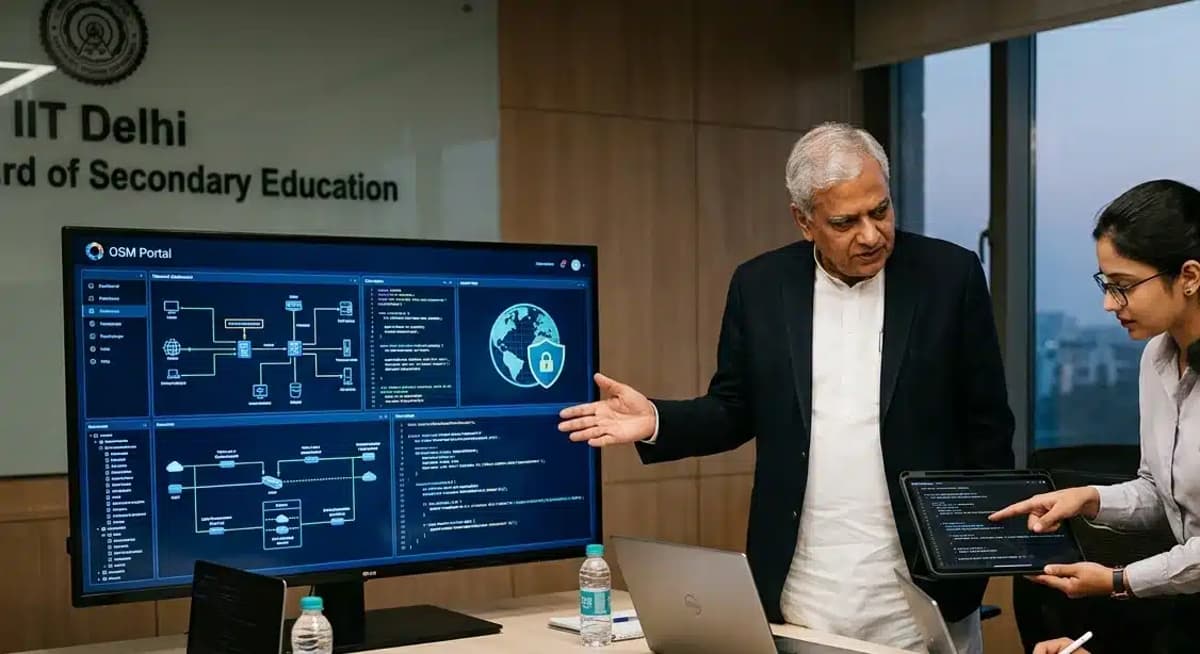
CBSE Engages IIT Experts After Admitting OSM Security Vulnerabilities
The Central Board of Secondary Education (CBSE) has enlisted cybersecurity experts from IIT Madras, IIT Kanpur and the Digital Infrastructure Corporation of India to audit its On‑Screen Marking (OSM) platform after confirming multiple vulnerabilities. Reported flaws included a hard‑coded master...

Meta’s Employee Mouse-Click Tracking Tool Is Collecting EU Data It Said It Would Not Collect
Meta’s Model Capability Initiative (MCI) records keystrokes, mouse clicks and screen content on U.S. workstations to train AI agents. Internal documents reveal the tool also ingests every email and chat a U.S. employee exchanges with European colleagues, contrary to Meta’s...

Breach Week Highlights: 7‑Eleven, Ameriprise, MyTheresa
Weekly update is up! Breach Week: 7-Eleven; Ameriprise; Mytheresa; Kemper; Charter; The Data Breach Disclosure Lag; Welcoming the Bhutanese Government https://www.troyhunt.com/weekly-update-506/

Cisco and Splunk Turn Log Floods Into Threat Signals
From Log Flood to Threat Signal: Cisco and Splunk Bring Context to Modern Defense https://t.co/VaHbtpEhOU https://t.co/z8V0LCu07K

Frontnode Achieves ISO/IEC 27001 Certification Amid Growing Institutional Focus on Digital Asset Governance
Frontnode, the Estonia‑based Bitcoin exchange, custody and transfer platform, announced it has achieved ISO/IEC 27001 certification, the global benchmark for information security management. The fintech now serves more than 100,000 customers across Europe and beyond, reinforcing its operational controls as...

Your Sensitive Files Really Shouldn't Be in Google Drive
Google Drive encrypts data in transit with TLS and at rest with AES‑128, but Google retains the encryption keys, meaning the service is not end‑to‑end encrypted. This key custody allows Google to scan content for policy enforcement and potentially grant...
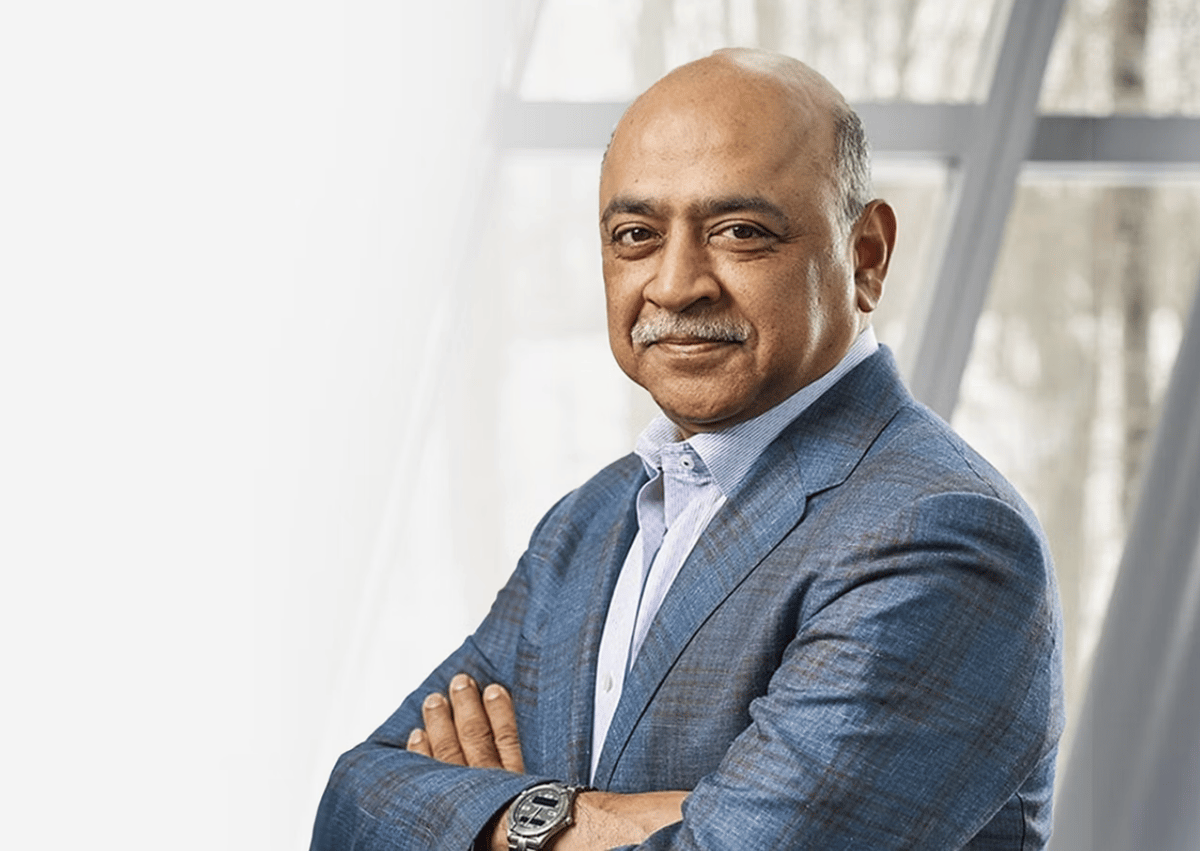
IBM Muscles Into OSS Security Space with $5 Billion “Lightwell” Project
IBM announced a $5 billion investment in Lightwell, a private clearinghouse designed to scan and secure an unprecedented volume of open‑source software (OSS) used by enterprises. The initiative leverages IBM’s cloud and AI capabilities to provide continuous, automated risk assessments across...

Claude Mythos Exposed a Hard Truth: Your Enterprise Patching Process Is Way Too Slow
Anthropic’s Claude Mythos preview proved AI can autonomously discover thousands of zero‑day vulnerabilities, collapsing exploitation timelines to hours. Recent CVEs such as Langflow and Marimo were weaponized within 20 hours and under 10 hours of disclosure, far faster than the...
Gravity Bridge Loses $5.4 Million in Suspected Signing‑Key Compromise
Gravity Bridge, the Ethereum‑Cosmos cross‑chain bridge, had roughly $5.4 million siphoned off in a suspected signing‑key compromise. The theft included $4.3 million in USDC and other assets, prompting the bridge to halt operations while investigators trace the funds.
27,000-Download Codex UI Tool Secretly Stole OpenAI Refresh Tokens
Security researcher Charlie Eriksen uncovered that the popular npm package codexui-android, which has about 27,000 weekly downloads, contains hidden code that steals OpenAI authentication tokens, including long‑lived refresh tokens. The malicious payload is embedded only in the published package, bypasses...

Brain Corp Achieves SOC 2 Compliance
Brain Corp announced that its BrainOS autonomy platform has achieved SOC 2 Type II compliance, confirming that its data security and system operations meet rigorous industry standards. The company currently powers more than 40,000 autonomous mobile robots in commercial settings across...

Week in Review: Infostealer Dropped via FortiClient EMS Flaw, Exploited Trend Micro Apex One Flaw
The week’s headlines were dominated by critical vulnerabilities and active exploits. FortiClient’s Enterprise Management Server (CVE‑2026‑35616) was leveraged to spread a broad‑range infostealer across corporate endpoints, while Trend Micro’s Apex One suffered a zero‑day path‑traversal attack (CVE‑2026‑34926). Microsoft released patches for a...
Balance AI Innovation with Governed System Access
Customer choice in AI tools connecting to core systems needs governed access. It's a line between responsible innovation and uncontrolled extraction. Encouraging innovation shouldn't cost security or governance. #AIChoice #DataGovernance https://t.co/qe11EuGL9P

The Measurement Problem
Identity and access management (IAM) remains a critical security pillar, yet most enterprises lack a reliable way to gauge program maturity. Multiple surveys—including SailPoint, Ponemon/GuidePoint, and IDSA—show that roughly 60‑70% of organizations sit in the lowest two maturity tiers, with...

XRP Ledger's New Proposal Blocks the Flash Loan Attacks Costing DeFi Hundreds of Millions
The XRP Ledger (XRPL) has introduced a draft amendment that makes flash‑loan attacks structurally impossible by prohibiting composable intra‑transaction calls. Recent DeFi exploits, including a $10.8 million Thorchain breach and over $600 million in losses across Solana and Ethereum protocols, leveraged flash...

Pentagon Says US Military Personnel Targeted Using Commercial Location Data
U.S. Central Command confirmed that forces in active war zones have been targeted using commercially available location data, according to a Reuters report and a letter from Senator Ron Wyden. The threat reports focus on the Gulf region, where U.S....

Pentagon’s ‘Supply Chain Risk’ Label and CISA Alert Spotlight Surge in Cyber‑Supply‑Chain Threats
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) issued an urgent alert about malicious Nx Console VSCode extensions and the Megalodon GitHub‑Action campaign, while a separate Quartz report notes the Pentagon’s “supply chain risk” label is being wielded as a...

Anthropic Flags 10,000 Flaws in Claude Mythos as Central Banks Hold Emergency AI Risk Briefings
Anthropic limited the Claude Mythos preview after participants reported more than 10,000 critical and high‑severity vulnerabilities, including 2,000 at Cloudflare. The discovery spurred emergency meetings of the U.S. Treasury, the Federal Reserve and major central banks, who warned that the...
Autonomous Endpoint Management in 2026: What 916 Reviews Reveal About AI's Role
Autonomous Endpoint Management (AEM) tools are gaining traction as AI‑powered solutions that automate patching, threat detection, and remediation across sprawling device fleets. G2 analyzed 916 verified reviews, finding the category generally delivers on its promises, with Tanium noted for the...

Microsoft Criticized for Threatening Legal Action Against Security Researcher
Microsoft’s Digital Crimes Unit warned it would pursue legal action against the security researcher known as “Nightmare Eclipse” after the individual publicly disclosed four unpatched bugs—BlueHammer, RedSun, UnDefend and YellowKey—affecting Windows Defender and BitLocker. Microsoft argues the researcher bypassed its...

Palo Alto GlobalProtect VPN Auth Bypass Flaw Now Exploited in Attacks
Palo Alto Networks says its GlobalProtect VPN authentication‑override cookie flaw (CVE‑2026‑0257) is being actively exploited. The vulnerability, patched earlier this month, lets attackers forge cookies and gain unauthorized VPN access when authentication‑override is enabled and the same certificate is reused....

Token Security Uncovers Five‑step Exploit that Could Hijack Zapier’s Low‑code Platform
Token Security researchers demonstrated a five‑step exploit chain that could have given them full control of Zapier’s low‑code automation service. The proof‑of‑concept shows how minor sandbox and role‑permission errors can cascade into enterprise‑wide breaches, underscoring the hidden danger in complex...

Analysts Warn U.S. Is Unprepared for Emerging ‘Q-Day’ Quantum Cyber Threats
Cybersecurity analysts warn that the United States lacks a coordinated response to the looming “Q‑Day” scenario, when quantum computers could break current encryption. They argue that criminals are already harvesting encrypted data for future decryption, and that policymakers must push...