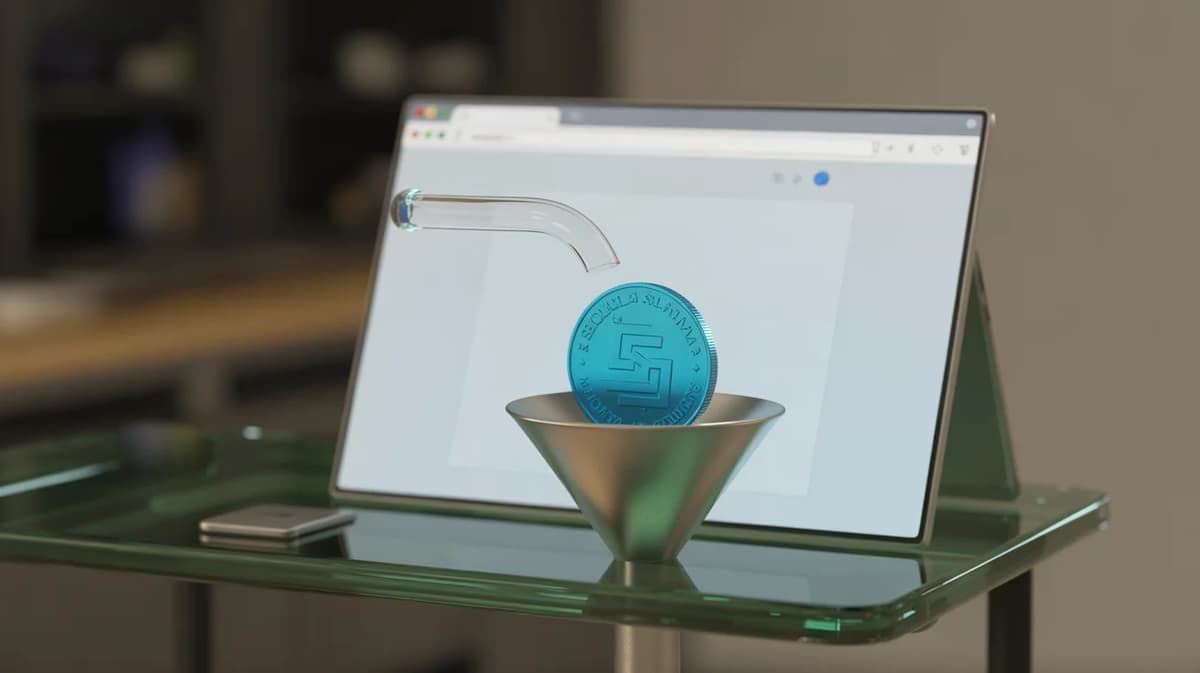
Malicious Chrome Extension Skims Solana Swaps with Hidden Extra Transfers
•November 27, 2025
0
Why It Matters
The attack demonstrates how seemingly benign browser tools can monetize crypto trades without user consent, raising fresh regulatory and security concerns for decentralized finance platforms and extension marketplaces.
Key Takeaways
- •Chrome extension siphons 0.05% per Solana swap.
- •Uses Raydium DEX, adds hidden transfer instruction.
- •Only 15 users since June, yet active.
- •Extension hides extra instruction in wallet confirmation.
- •Highlights ongoing risk of crypto Chrome extensions.
Pulse Analysis
The Crypto Copilot extension leverages a clever on‑chain trick: it bundles a legitimate swap with a covert transfer that executes atomically. By routing the trade through Raydium, the extension ensures the user receives the expected token output while a tiny portion of SOL is rerouted to the attacker’s address. Because wallet UI screens aggregate instructions, users see only a single swap confirmation, making the hidden fee virtually invisible. This method marks a shift from outright theft to micro‑fee skimming, which can accumulate significant revenue over time.
Chrome’s extensibility and massive user base have long attracted malicious actors, and the Solana case underscores a broader pattern of crypto‑focused extensions abusing trust. Recent reports have identified multiple plugins that either drain wallets or hijack credentials, highlighting systemic weaknesses in the Chrome Web Store’s vetting process. The fact that Crypto Copilot persisted for months with only a handful of users suggests that low‑volume attacks can evade detection while still delivering profit to perpetrators. As decentralized finance continues to integrate with mainstream browsers, the attack surface expands, prompting calls for stricter review standards and better user education.
For traders, the immediate takeaway is to treat any browser‑based crypto tool with suspicion. Verify extensions through official sources, limit permissions, and prefer dedicated wallet applications that display granular transaction details. Platform developers should consider implementing explicit instruction breakdowns in confirmation dialogs, making hidden transfers harder to conceal. Meanwhile, security firms and browser vendors must collaborate on rapid takedown mechanisms to curb the proliferation of such stealthy scams, protecting both retail investors and the integrity of the broader crypto ecosystem.
Malicious Chrome extension skims Solana swaps with hidden extra transfers
0
Comments
Want to join the conversation?
Loading comments...