I Stopped Trusting Google Drive with Sensitive Files After I Found This Free Encryption Tool
•March 2, 2026
0
Companies Mentioned
Why It Matters
Client‑side encryption restores data sovereignty, reducing exposure to provider breaches and credential leaks. Enterprises and privacy‑focused users can safely leverage existing cloud storage without sacrificing confidentiality.
Key Takeaways
- •Cloud providers hold decryption keys, limiting privacy
- •Cryptomator encrypts files client‑side before cloud upload
- •Works with Google Drive, Dropbox, OneDrive, iCloud
- •Simple UI, easy vault creation on Windows
- •Free, open‑source solution for personal data protection
Pulse Analysis
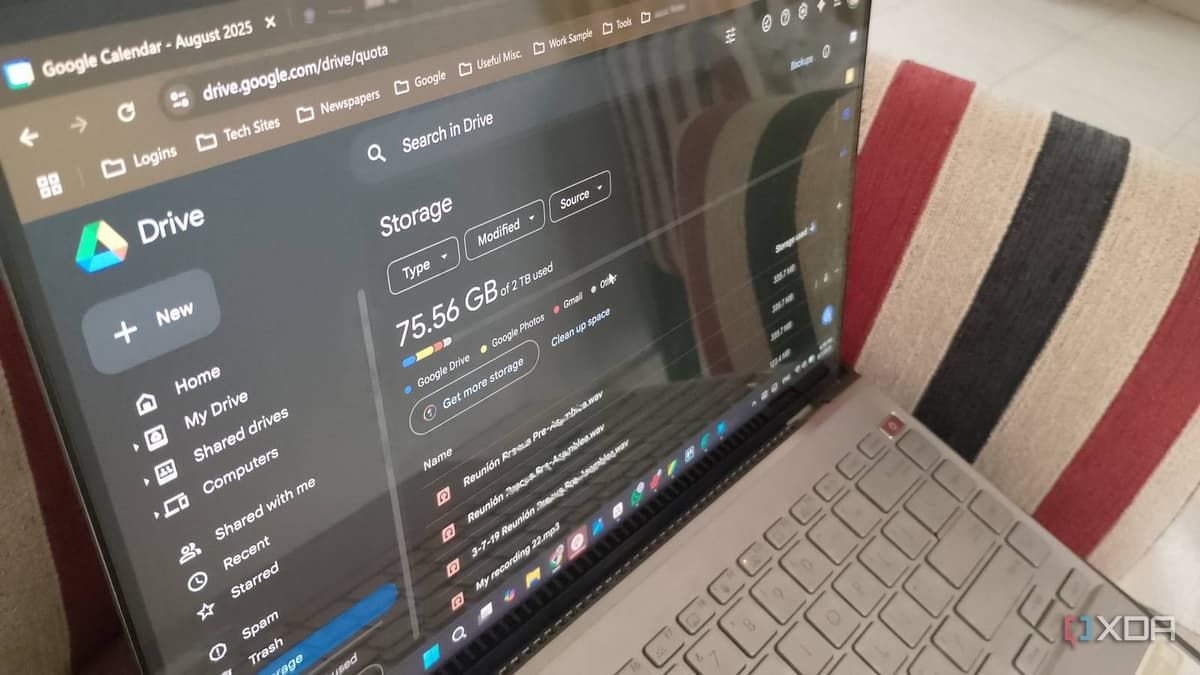
Cloud storage has become ubiquitous, but its convenience comes with hidden privacy risks. Providers encrypt data in transit and at rest, yet they retain the decryption keys, meaning they can access any file whenever they choose. Credential‑theft incidents further expose users, as a compromised login grants attackers direct entry to unencrypted content. For businesses handling regulated or proprietary information, this model conflicts with data‑sovereignty mandates and increases liability.
Cryptomator addresses these concerns by performing end‑to‑end encryption on the client device. The open‑source app creates a virtual vault, encrypts each file with a user‑generated key, and stores only ciphertext on the chosen cloud folder. Because the key never leaves the local machine, cloud providers and potential intruders see only random strings. Compatibility with Google Drive, Dropbox, OneDrive, and iCloud means users can continue using familiar sync tools while benefiting from robust security. The interface mirrors typical file‑explorer workflows, allowing even non‑technical users to set up vaults in minutes on Windows, macOS, or Linux.
Adopting client‑side encryption like Cryptomator can reshape corporate data‑governance strategies. Organizations can retain existing cloud contracts, avoiding costly migrations to private storage, while meeting compliance requirements such as GDPR or CCPA that demand control over personal data. The zero‑cost, community‑maintained nature of the tool also reduces software‑licensing overhead. As cyber‑threats evolve, more enterprises are likely to layer local encryption over cloud services, turning a convenience platform into a secure repository without sacrificing productivity.
I stopped trusting Google Drive with sensitive files after I found this free encryption tool
0
Comments
Want to join the conversation?
Loading comments...