Fake Laravel Packages on Packagist Deploy RAT on Windows, macOS, and Linux
•March 4, 2026
0
Why It Matters
Compromised Laravel applications give attackers full shell access, exposing credentials, databases, and internal services, amplifying supply‑chain risk for PHP ecosystems.
Key Takeaways
- •Three fake packages deliver cross‑platform PHP RAT
- •RAT connects to helper.leuleu.net C2 server
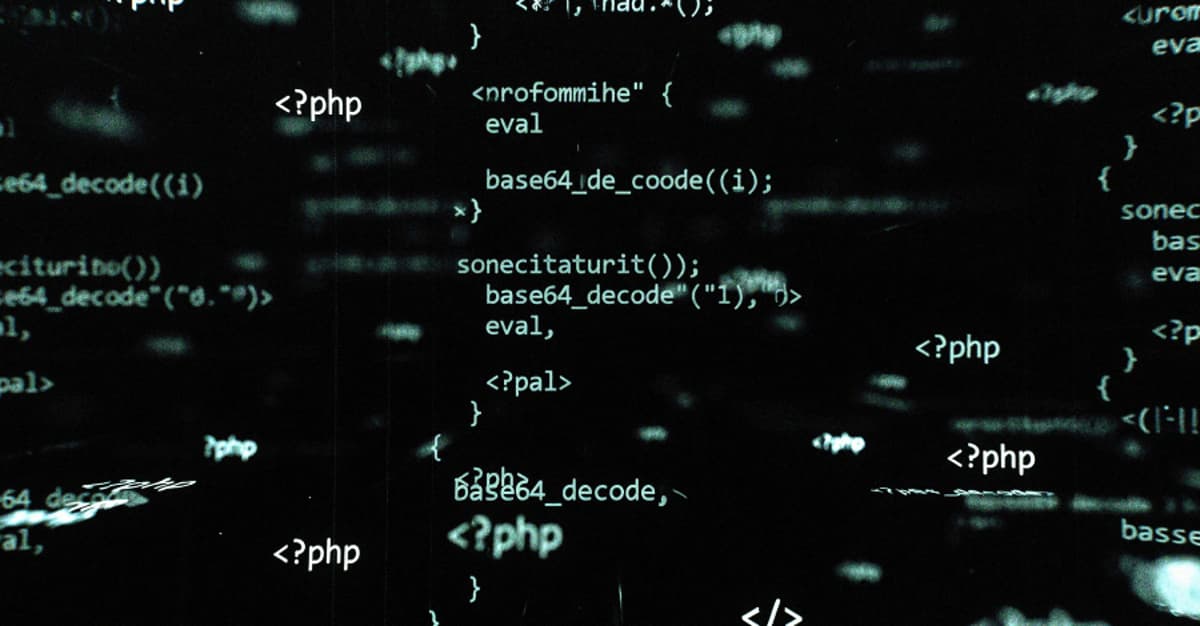
- •Obfuscation evades static analysis, uses multiple exec functions
- •Compromise grants file access, command execution, screenshot capability
- •Removal requires uninstall, secret rotation, outbound traffic audit
Pulse Analysis
The emergence of malicious packages on Packagist underscores a growing supply‑chain threat to the PHP community. Laravel’s popularity makes its ecosystem an attractive target, and the open‑source nature of Composer encourages rapid adoption of third‑party libraries without rigorous vetting. Attackers exploit this trust model by publishing seemingly legitimate utilities, then slipping a hidden remote access trojan into the codebase. By coupling the malicious payload with innocuous‑looking dependencies, they increase download counts and bypass casual scrutiny, a tactic mirrored in recent npm and PyPI attacks.
Technical analysis reveals a sophisticated RAT that leverages PHP’s native networking functions to maintain persistence across Windows, macOS, and Linux hosts. The payload obfuscates domain names, command strings, and file paths, while dynamically selecting execution functions such as popen, proc_open, exec, and system to bypass disabled function hardening. Once loaded at application boot or via autoloaded classes, the RAT contacts the C2 server, transmits system reconnaissance, and awaits commands ranging from shell execution to screenshot capture. Its ability to read and write arbitrary files means it can harvest .env files, database credentials, and API keys, effectively turning the compromised web server into a foothold for broader network intrusion.
Mitigation requires immediate removal of the infected packages, followed by a comprehensive rotation of all secrets stored in the application environment. Developers should audit Composer lock files, enforce strict package provenance checks, and employ automated scanning tools that detect obfuscated PHP code. Monitoring outbound traffic for connections to suspicious domains like helper.leuleu.net can provide early indicators of compromise. The broader industry response must focus on strengthening repository governance, encouraging signed packages, and promoting a culture of continuous dependency hygiene to curb future supply‑chain compromises.
Fake Laravel Packages on Packagist Deploy RAT on Windows, macOS, and Linux
0
Comments
Want to join the conversation?
Loading comments...