Security Risk Advisors Releases “The Purple Perspective 2026” Report
•March 9, 2026
0
Companies Mentioned
Why It Matters
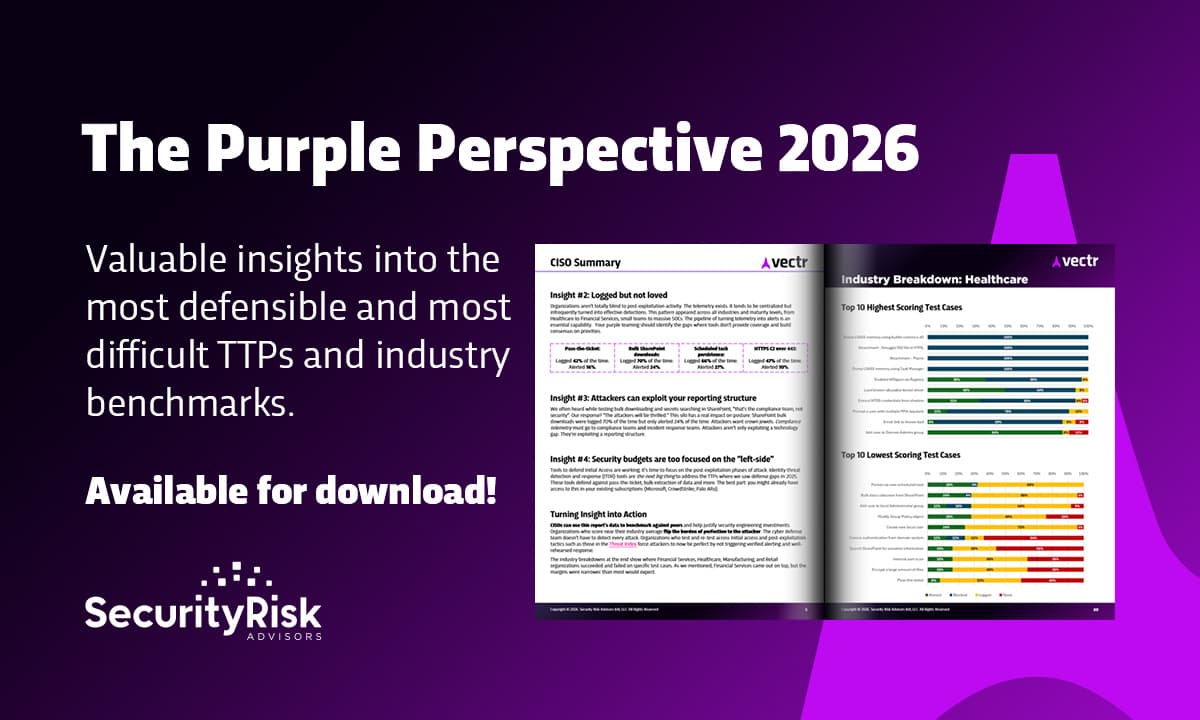
Regular purple‑team testing and tighter integration of compliance telemetry are proven levers for closing detection gaps, making the findings critical for any organization seeking resilient cyber defenses. The insights reshape budgeting and staffing decisions across security and compliance teams.
Key Takeaways
- •160 purple‑team exercises evaluated 8,300 MITRE TTPs.
- •2‑4 exercises per year boost detection success.
- •Telemetry logged high, alerts low for key techniques.
- •Compliance‑security gaps hinder incident response.
- •Industry insights shape 2026 defensive priorities.
Pulse Analysis
Purple teaming has moved from niche practice to a strategic imperative, and SRA’s new report quantifies that shift. By orchestrating over 160 simulated attacks across diverse environments, the study provides a rare, data‑driven view of how real‑world adversary techniques fare against today’s defenses. The breadth of the exercise—covering more than 8,300 tactics, techniques, and procedures—offers security leaders a benchmark that transcends vendor hype, allowing them to gauge maturity against a common adversary playbook.
One of the report’s most actionable revelations is the correlation between testing cadence and detection efficacy. Organizations that schedule two to four purple‑team engagements per year consistently outperformed peers, suggesting that a disciplined, programmatic approach yields measurable security gains. Yet the data also expose a chronic underutilization of telemetry: while activities like pass‑the‑ticket and bulk SharePoint downloads are logged in 40‑70 percent of cases, alerts fire in only 10‑27 percent. This disparity points to gaps in analytics, rule tuning, and cross‑team communication, underscoring the need for security operations to translate raw logs into timely, actionable alerts.
Looking ahead to 2026, the report urges firms to dissolve silos between compliance and security functions. By feeding compliance‑generated logs directly into incident‑response workflows, organizations can close the alert gap and reduce dwell time. Industry‑specific insights further tailor these recommendations, helping sectors such as financial services or healthcare prioritize the most vulnerable techniques. For executives, the Purple Perspective 2026 serves not just as a diagnostic tool but as a roadmap for allocating resources, refining detection architectures, and ultimately building a more resilient cyber posture.
Security Risk Advisors Releases “The Purple Perspective 2026” Report
0
Comments
Want to join the conversation?
Loading comments...