Spoofing an Emergency Traffic Preemption Signal
•March 8, 2026
0
Key Takeaways
- •Strobecom EVP uses pulse‑skipping infrared protocol
- •Arduino + IR LED can trigger preemption signal
- •Precise timing and valid vehicle ID required
- •Flipper Zero may lack required precision
- •Exploiting systems risks legal consequences
Summary
Security researcher xssfox reverse‑engineered a Tomar Strobecom II emergency vehicle preemption (EVP) system and demonstrated that an Arduino‑based infrared transmitter can spoof the signal to turn traffic lights green. The analysis revealed the protocol relies on pulse‑skipping infrared bursts and often requires a correctly timed vehicle ID. While the proof‑of‑concept works, the timing tolerances are tight, making casual attacks with devices like Flipper Zero unreliable. The work underscores both the feasibility and the legal risks of tampering with municipal traffic control infrastructure.
Pulse Analysis
Emergency Vehicle Preemption (EVP) systems are a cornerstone of modern urban traffic management, allowing ambulances, fire trucks, and police vehicles to request green lights as they approach intersections. Most legacy installations rely on infrared strobes that emit coded pulses, a design chosen for its simplicity and low cost. By embedding a vehicle identifier within the pulse pattern, manufacturers aim to prevent unauthorized activation, yet the underlying protocol remains relatively straightforward, making it an attractive target for security scrutiny.
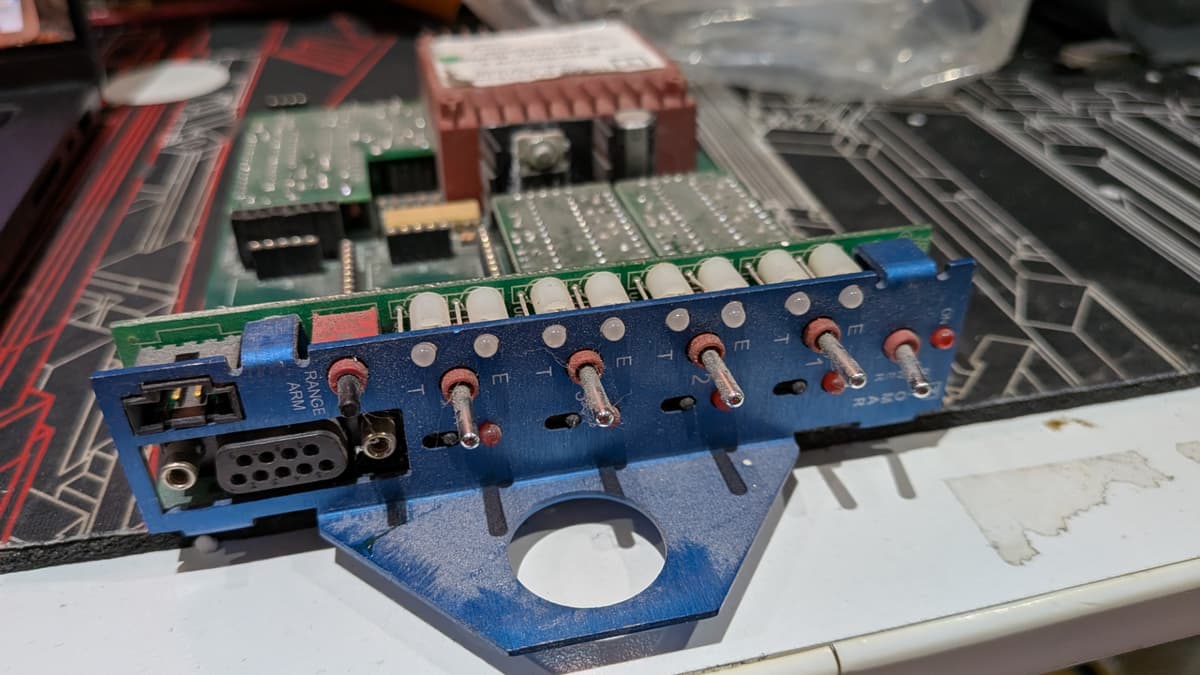
In a recent hands‑on investigation, researcher xssfox acquired a Tomar Strobecom optical processor and a compatible power supply, then dissected the infrared communication using an oscilloscope. The team discovered that the system encodes data by selectively omitting pulses—a method that can be replicated with an Arduino Nano and a high‑speed IR LED. After exhaustive brute‑forcing, the prototype successfully triggered a preemption event and even transmitted a valid vehicle ID, confirming that the protocol’s security hinges on precise timing rather than cryptographic safeguards. The findings suggest that off‑the‑shelf hobbyist hardware can meet the required specifications, though achieving consistent results demands meticulous calibration.
The broader implications are significant for municipal authorities and vendors alike. As cities modernize traffic control with networked and IoT‑enabled devices, the exposure of such low‑level vulnerabilities could be leveraged for disruptive attacks or illicit traffic manipulation. Mitigation strategies include tightening pulse timing tolerances, implementing cryptographic authentication, and regularly auditing field‑deployed equipment. Proactive security assessments and firmware updates will be essential to safeguard public safety and maintain trust in critical transportation infrastructure.
Comments
Want to join the conversation?