Recent Posts
Video•Feb 28, 2026
Black Hat USA 2025 | If Google Uses It to Find Webpages, We Can Use It to Find Fraudsters
The session at Black Hat USA 2025 introduced a surprisingly simple technique—term‑frequency inverse‑document‑frequency (TF‑IDF)—as a powerful tool for spotting fraudsters, positioning it as an alternative to the sophisticated AI browsers and agents that dominate today’s web search. Speakers argued that generative AI tools like Worm‑GPT are lowering the barrier for attackers, leading to higher‑volume, faster‑moving fraud campaigns. Traditional models struggle with low‑confidence alerts, whereas TF‑IDF can quickly highlight anomalous attribute combinations such as unusual device‑OS or GPU signatures. Live customer demos (names omitted) demonstrated that the TF‑IDF‑based engine runs on modest hardware, delivering clear clustering of suspicious entities without an army of GPUs. The presenters also noted Google’s migration to BM25 for web ranking, but emphasized that TF‑IDF’s deterministic nature makes it ideal for fraud contexts. For security teams, adopting TF‑IDF offers a cost‑effective, scalable way to enrich detection pipelines, improve analyst confidence, and keep pace with AI‑enhanced threat actors, ultimately reducing breach risk tied to identity theft and synthetic fraud.
By Black Hat
Video•Feb 27, 2026
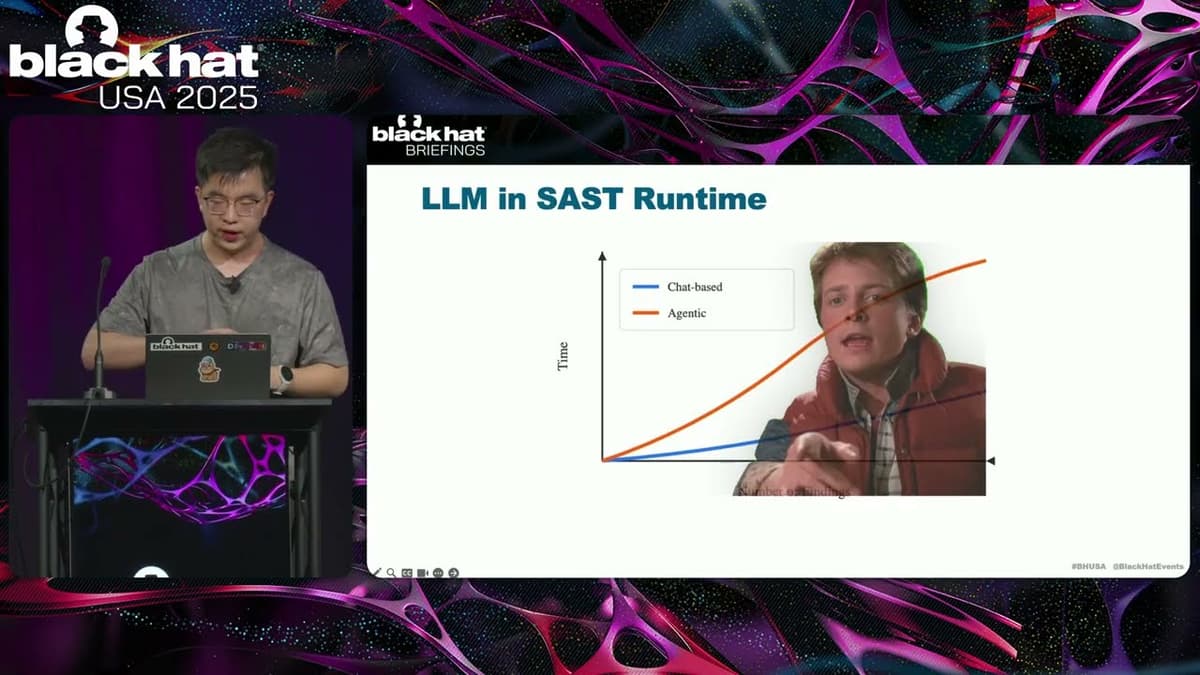
Black Hat USA 2025 | Let LLM Learn: When Your Static Analyzer Actually 'Gets It'
The Black Hat presentation explored how large language models (LLMs) can be fused with traditional static analysis tools to create a new generation of vulnerability scanners. The speaker outlined three integration patterns—AI‑enhanced, where a static scanner filters LLM output; AI‑explorer,...
By Black Hat
Video•Feb 25, 2026
Black Hat USA 2025 | Conjuring Hardware Failures to Breach CPU Privilege Boundaries
The Black Hat talk spotlights machine‑check exceptions (MCEs) – hardware‑level fault signals that fire when a CPU detects catastrophic errors such as cache corruption, thermal trips, or external interference. Christopher Domas demonstrates that, unlike ordinary interrupts, MCEs cannot be masked,...
By Black Hat
Video•Feb 25, 2026
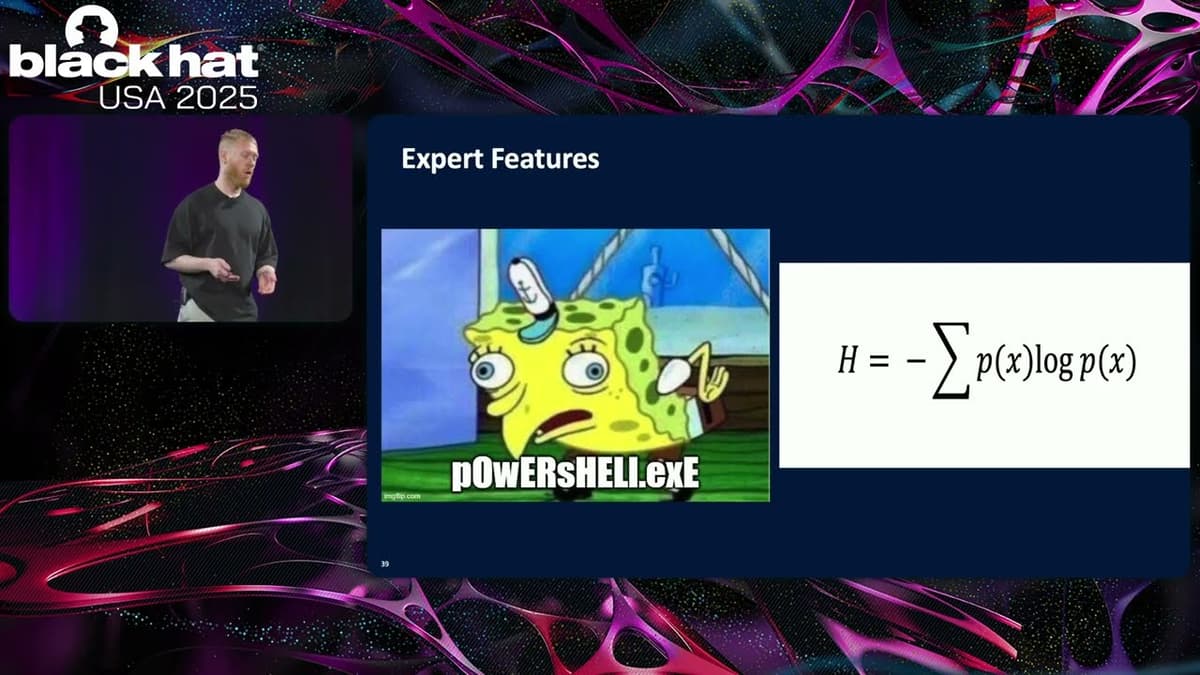
Black Hat USA 2025 | Enhancing Command Line Classification with Benign Anomalous Data
Sophos researchers presented a novel pipeline that pairs anomaly detection with large language models to harvest benign command‑line examples for supervised classification. Instead of relying on unsupervised anomaly detection to flag malicious inputs, the approach uses the detector to surface...
By Black Hat
Video•Feb 24, 2026
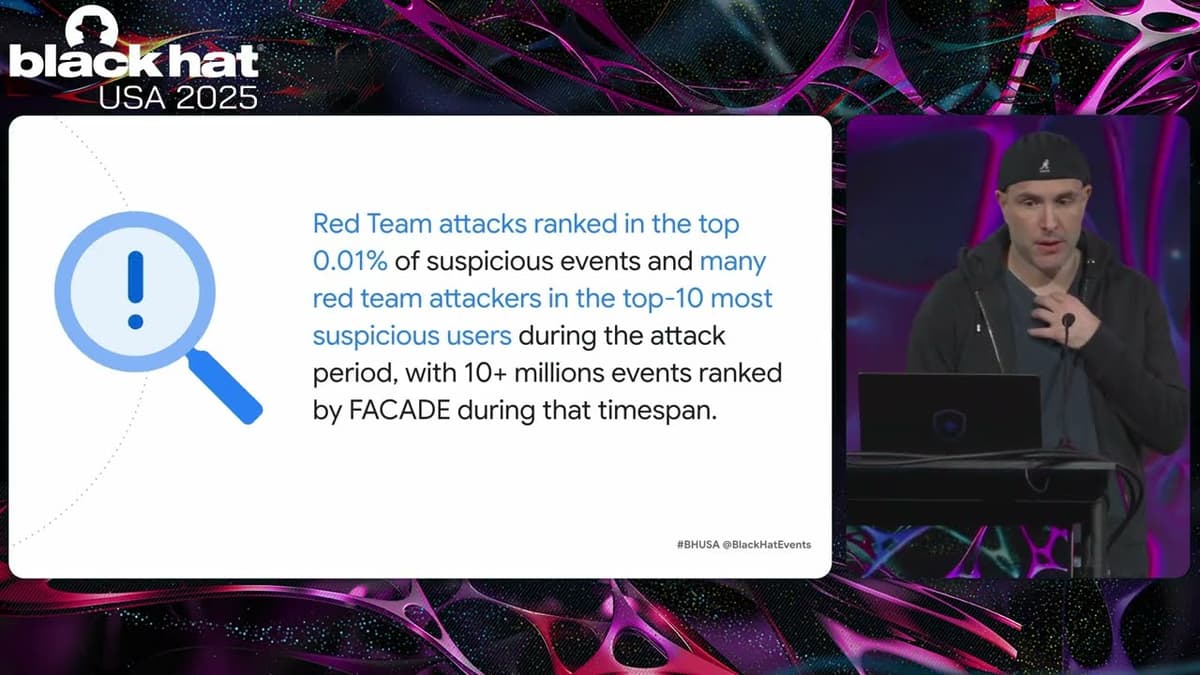
Black Hat USA 2025 | FACADE: High-Precision Insider Threat Detection Using Contrastive Learning
Google unveiled Facade, a self‑supervised AI system that detects insider threats by analyzing contextual patterns in corporate logs. Leveraging contrastive learning on exclusively benign data, Facade achieves unprecedented accuracy, reporting false‑positive rates below 0.01% and as low as 0.0003% for...
By Black Hat

Video•Feb 23, 2026
Black Hat USA 2025 | Breaking Out of The AI Cage: Pwning AI Providers with NVIDIA Vulnerabilities
Researchers from Wiz uncovered a critical vulnerability in the NVIDIA Container Toolkit, the software that isolates AI workloads on NVIDIA hardware. The flaw permits a container escape to the host OS, potentially compromising entire Kubernetes clusters and exposing cross‑tenant data....
By Black Hat

Video•Feb 23, 2026
Black Hat USA 2025 | Autonomous Timeline Analysis and Threat Hunting: An AI Agent for Timesketch
At Black Hat USA 2025, Google engineers unveiled an AI‑powered agent that autonomously performs digital forensic timeline analysis and threat hunting within Timesketch. The system ingests heterogeneous log streams, reconstructs attack chains, and surfaces compromise evidence without relying on pre‑written...
By Black Hat
Video•Feb 22, 2026
Black Hat USA 2025 | Vaulted Severance: Your Secrets Are Now Outies
The Black Hat USA 2025 talk, titled “Vaulted Severance: Your Secrets Are Now Outies,” examined critical weaknesses in modern secret‑management systems, using HashiCorp Vault as a case study. The presenters, from SIATA, framed the discussion around how vaults serve as...
By Black Hat
Video•Feb 20, 2026
Black Hat USA 2025 | Exploiting DNS for Stealthy User Tracking
The Black Hat USA 2025 presentation by Bitdefender researchers Yangabella and Yan Pedrian revealed how DNS traffic from smartphones can be weaponized to create persistent, cross‑network device fingerprints. By acting as a curious DNS resolver, they collected 985 million DNS events...
By Black Hat

Video•Feb 20, 2026
Black Hat USA 2025 | From Prompts to Pwns: Exploiting and Securing AI Agents
The Black Hat USA 2025 session titled “From Prompts to Pwns” examined how modern AI agents—especially those powered by large language models—can be both powerful assistants and vulnerable attack surfaces. Speakers Becca and Rich from NVIDIA’s AI Red Team introduced a three‑tier...
By Black Hat