
DEF CON
Creator
0 followers
Official channel of the DEF CON hacking conference, featuring recorded talks and presentations from past events ([www.vlogfund.com](https://www.vlogfund.com/en/youtube-channels/defconconference/#:~:text=Image%3A%20DEFCONConference%20,pictures%20from%20past%20conferences%20here)).
Recent Posts
Video•Feb 18, 2026
DEF CON 33 - DisguiseDelimit: Exploiting Synology NAS with Delimiters and Novel Tricks - Ryan Emmon
Ryan Emmens presented at DEF CON 33 a case study on discovering and weaponising an unauthenticated vulnerability in Synology’s DiskStation Manager (DSM) operating system, culminating in a $40,000 Pwn2Own win. By instrumenting the login flow with eBPF tracing and inotify, he uncovered a chain of three CGI‑based processes that write attacker‑controlled data to transient files and inject it as environment variables for a privileged root process. This allowed remote code execution without prior authentication or man‑in‑the‑middle positioning. The research also highlighted Synology’s custom client‑side RSA/AES encryption that obscures login credentials, and demonstrated how Vue.js developer extensions can force the web UI into a debuggable state, bypassing the encryption hurdle and enabling payload injection. With roughly one million public‑facing NAS units, the flaw presents a massive attack surface; organizations must update DSM, disable unnecessary web services, and monitor for anomalous process activity to mitigate the risk of lateral compromise.
By DEF CON
Video•Feb 18, 2026
DEF CON 33 - Browser Extension Clickjacking: One Click and Your Credit Card Is Stolen - Marek Tóth
The DEF CON presentation by Marek Tóth exposed a new class of browser‑extension clickjacking that lets attackers harvest credit‑card and password data with a handful of user clicks. By targeting the manual‑autofill feature of popular password‑manager extensions, the researcher demonstrated...
By DEF CON
Video•Dec 31, 2025
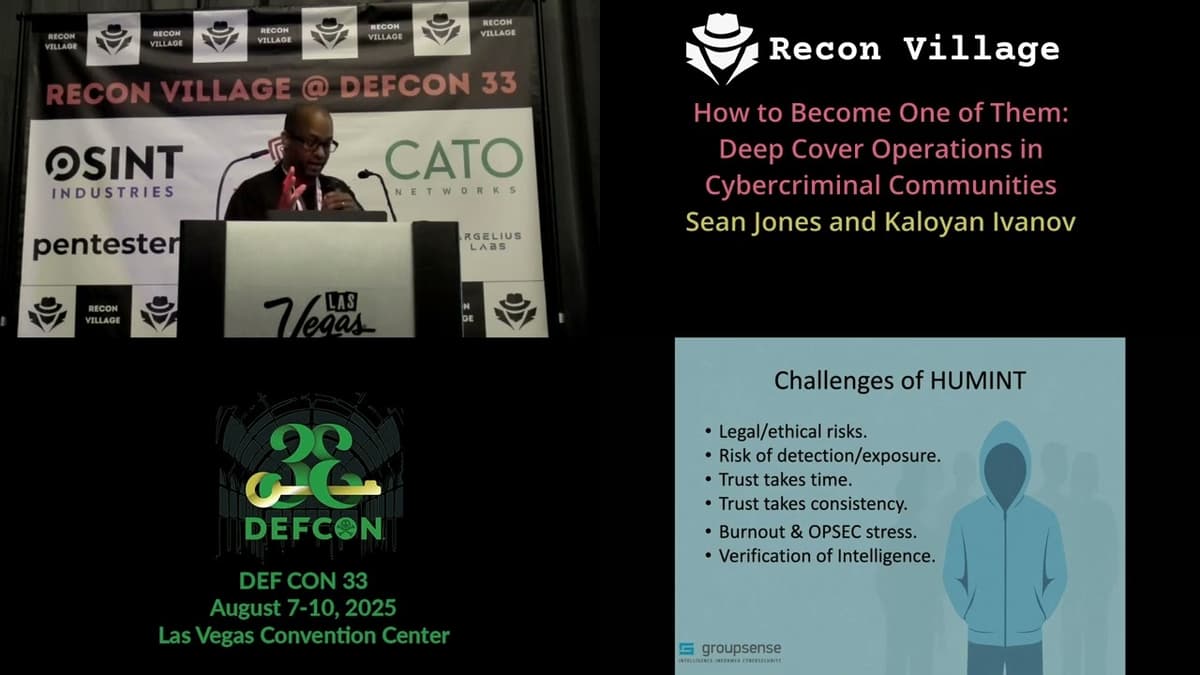
DEF CON 33 Recon Village - How to Become One of Them: Deep Cover Ops - Sean Jones, Kaloyan Ivanov
The DEF CON 33 Recon Village session, led by Sean Jones and Robert Rosio, explored the art and science of deep‑cover operations within cyber‑criminal ecosystems. The presenters argued that human intelligence (HUMINT) remains indispensable, especially when automated scrapers and...
By DEF CON

Video•Dec 31, 2025
DEF CON 33 Recon Village - Autonomous Video Hunter AI Agents for Real Time OSINT - Kevin Dela Rosa
Kevin Dela Rosa presented the Autonomous Video Hunter, an AI‑driven system that extracts real‑time open‑source intelligence from video streams. Built on his startup Cloud Glue, the proof‑of‑concept combines multimodal video processing, large‑language‑model planning, and a suite of vision and audio tools...
By DEF CON

Video•Dec 31, 2025
DEF CON 33 Recon Village - Inside the Shadows Tracking RaaS Groups, Cyber Threats - John Dilgen
John Dilgen, a cyber‑threat intelligence analyst at Reliquest, presented at DEF CON 33’s Recon Village a deep dive titled “Inside the Shadows: Tracking Ransomware‑as‑a‑Service (RaaS) Groups and Evolving Cyber Threats.” He framed the discussion around the staggering $124 billion annual ransomware cost...
By DEF CON