Cybersecurity Implications of the 2026 Middle East Escalation: When Cloud Infrastructure Becomes a Target
•March 3, 2026
0
Key Takeaways
- •AWS data center hit by kinetic strike in UAE
- •60+ AWS services disrupted across Middle East
- •Hacktivist attacks surged >150 incidents in 72 hours
- •Data residency rules clash with forced cloud migrations
- •Cyber insurance war exclusions face unprecedented test
Summary
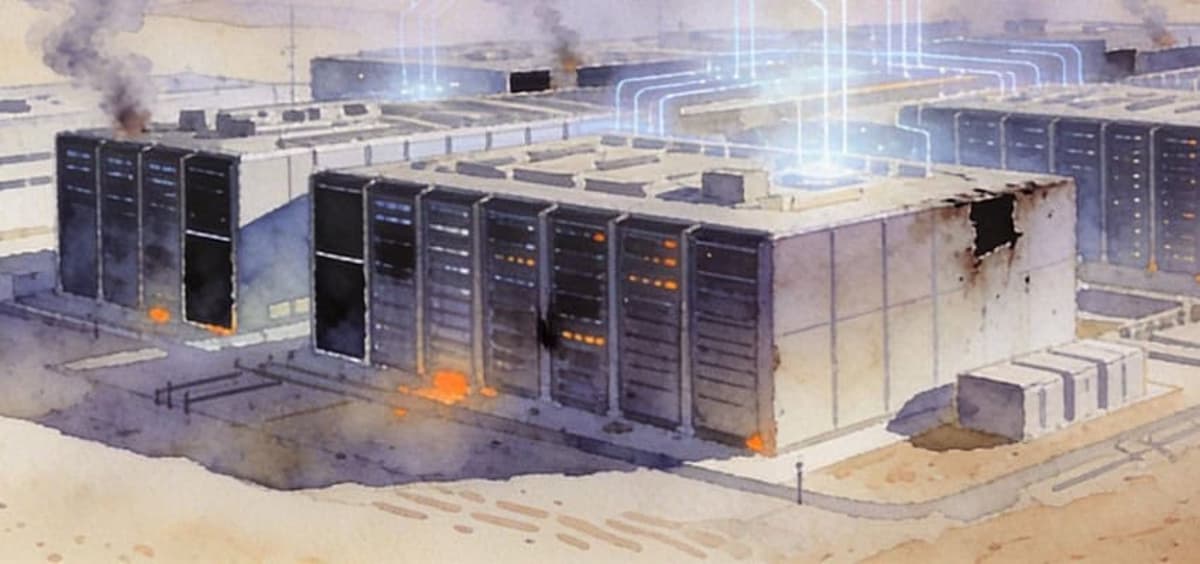
On March 1, 2026, an unidentified projectile struck an AWS data center in the UAE, igniting a fire that knocked out more than 60 services across the Middle East and forced customers to shift workloads to Europe. The physical attack coincided with a massive cyber campaign, with over 150 hacktivist incidents recorded in the first 72 hours and Iranian‑linked actors targeting government, finance and aviation systems. The disruption exposed gaps in data‑residency compliance, business‑continuity planning, and cyber‑insurance coverage, as regulators have yet to issue force‑majeure guidance. Organizations now must reassess cloud footprints, incident‑response triggers, and policy exclusions amid an evolving kinetic‑cyber threat landscape.
Pulse Analysis
The March 1 strike on Amazon Web Services’ ME‑CENTRAL‑1 facility marks the first documented case of a major cloud provider’s hardware being deliberately targeted in an armed conflict. Until now, hyperscale operators have marketed the Gulf as a stable, low‑latency hub for AI workloads, attracting multibillion‑dollar investments from Microsoft, Nvidia and others. The kinetic damage—fire, power loss and water‑logged racks—shattered that narrative, demonstrating that physical proximity to flashpoints creates a tangible risk to compute capacity. Enterprises that based disaster‑recovery plans on regional availability now face a reality where “uptime” is a geopolitical variable, prompting a shift toward multi‑region, cross‑border redundancy.
Simultaneously, a coordinated cyber onslaught erupted, with more than 150 hacktivist incidents logged within the first three days and state‑aligned groups deploying wiper malware and AI‑enhanced phishing. Analysts at Palo Alto Networks’ Unit 42 note that the fragmentation of Iran’s command‑and‑control has spawned autonomous cells, increasing unpredictability and reducing the effectiveness of traditional APT modeling. The rapid activation of these actors underscores the need for security operations centers to treat geopolitical escalations as automatic triggers for heightened monitoring, and to integrate generative‑AI threat‑intel feeds that can keep pace with the speed of modern digital offensives.
The convergence of kinetic and cyber threats also strains existing compliance and insurance frameworks. Data‑residency statutes in the UAE, Saudi Arabia and the EU require personal data to remain within national borders, yet AWS’s emergency recommendation to migrate workloads to Europe creates a legal gray zone with no force‑majeure guidance. Moreover, cyber‑insurance policies are grappling with war‑exclusion clauses that have never been tested against the destruction of third‑party cloud infrastructure. Risk managers must audit policy language, confirm coverage for digital assets, and coordinate with legal teams to document preservation efforts, while governance leaders should redesign backup strategies to span politically stable jurisdictions beyond a single region.
Comments
Want to join the conversation?