Recent Posts

News•Mar 2, 2026
CrowdStrike Warns APAC of Faster, Stealthier Cyberattacks
CrowdStrike’s 2026 Global Threat Report warns that APAC organisations are now facing cyberattacks that move at unprecedented speed, with the average eCrime breakout time shrinking to 29 minutes in 2025. The report highlights a dramatic shift toward malware‑free attacks—82% of detections lacked malicious code—and an 89% surge in AI‑enabled adversaries. Recent breaches such as Australia’s YouX platform, which exposed driver’s licence data, illustrate how identity information fuels synthetic identities and rapid account takeover. Zero‑day exploits also rose 42%, underscoring the need for faster detection and response.
By TechRepublic – Articles

News•Feb 27, 2026
Five Questions to Ask Before Renewing or Expanding Enterprise AI Platforms in 2026
Enterprise AI platform decisions in 2026 are shifting from new deployments to renewals, consolidations, and selective expansions, especially across Asia‑Pacific where cost pressures demand measurable ROI. Leaders must move beyond model accuracy and user adoption, demanding concrete economic proof that...
By TechRepublic – Articles

News•Feb 26, 2026
The Global Fight Over Who Controls Your Data Just Escalated — Here’s What the Numbers Say
U.S. diplomats have been instructed to lobby foreign governments to ease data‑sovereignty and data‑localization rules, arguing that strict regulations hinder American cloud and AI firms. Kiteworks’ 2026 Data Sovereignty Report, based on 286 security professionals across Canada, the Middle East...
By TechRepublic – Articles

News•Feb 23, 2026
Conduent Breach Surges to Over 25M, Could Be Largest in US History
The cyberattack on government services firm Conduent, first disclosed in January 2025, has swelled to affect more than 25 million Americans, making it potentially the largest U.S. data breach on record. Texas alone accounts for 15.4 million impacted residents, while other states...
By TechRepublic – Articles
News•Feb 20, 2026
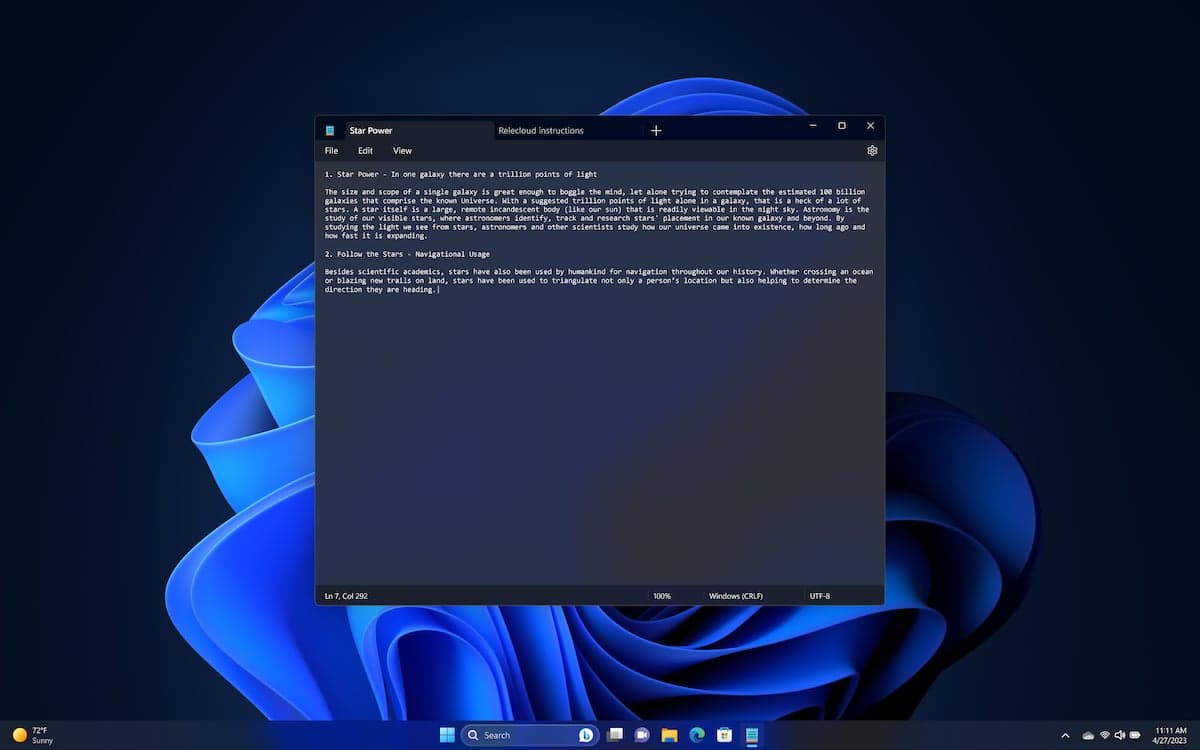
Microsoft: Critical Security Issue Found in Windows Notepad
Microsoft patched a high‑severity vulnerability (CVE‑2026‑20841) in the modern Windows Notepad app that adds Markdown support. The flaw allows remote code execution when a user opens a malicious .md file and clicks a crafted link. The issue affects only the...
By TechRepublic – Articles

News•Feb 17, 2026
Singapore’s AI ROI Reality: High Spend, Hard Returns
AI hype in Singapore masks modest financial returns. Enterprises spend an average S$18.9 million per AI initiative in 2025, yet only 23% achieve the projected ROI. A PwC global CEO survey shows just 12% of CEOs see both cost cuts and...
By TechRepublic – Articles
News•Feb 17, 2026
India’s Cybersecurity Cost Equation
India’s enterprises are boosting cybersecurity spend as multi‑cloud, API‑led ecosystems expand, yet Security Operations Centre (SOC) capacity lags behind. The average data‑breach cost has climbed to ₹22 crore (≈US$2.6 million), highlighting the financial stakes. Tool proliferation generates more alerts, but analyst throughput...
By TechRepublic – Articles

News•Feb 17, 2026
How to Choose a Password Manager for Your Business
Choosing a password manager is now a strategic security decision, not just a convenience tool. While consumer‑focused apps handle basic storage, enterprise‑grade solutions add centralized provisioning, role‑based access, and detailed audit trails. Decision‑makers must evaluate encryption models, zero‑knowledge architecture, MFA...
By TechRepublic – Articles

News•Feb 16, 2026
The Rise of Credential Stuffing Attacks
Credential stuffing attacks are surging as attackers exploit reused passwords harvested from past breaches. The technique is cheap, highly automated, and blends into normal traffic, making detection difficult. Small‑to‑mid‑size businesses, SaaS platforms, and customer‑facing portals are prime targets because they...
By TechRepublic – Articles

News•Feb 16, 2026
Apple Warns macOS Users: Rosetta 2 Support Is Ending Soon
Apple announced that Rosetta 2, the translation layer for Intel‑only apps, will be phased out after macOS 27 and disappear by macOS 28. The upcoming macOS 26.4 beta adds on‑screen warnings for apps still relying on Rosetta, signaling the end of support. This marks...
By TechRepublic – Articles
