Quantum Computing Advances Cryptographic Algorithms for Data Security , a Doctoral Guide
•January 29, 2026
0
Why It Matters
Quantum computers threaten the foundational RSA and ECC protocols, making rapid adoption of quantum‑resistant algorithms essential for safeguarding global data infrastructures. The guide equips decision‑makers with the technical insight needed to navigate standards, implementation risks, and emerging quantum‑secure technologies.
Key Takeaways
- •Quantum computers break RSA, ECC via Shor’s algorithm.
- •Lattice, code, hash, multivariate, isogeny schemes evaluated.
- •NIST PQC standardization drives industry adoption.
- •QKD protocols like BB84 and Twin‑Field enable secure keys.
- •Implementation hurdles include performance, hardware limits, migration complexity.
Pulse Analysis
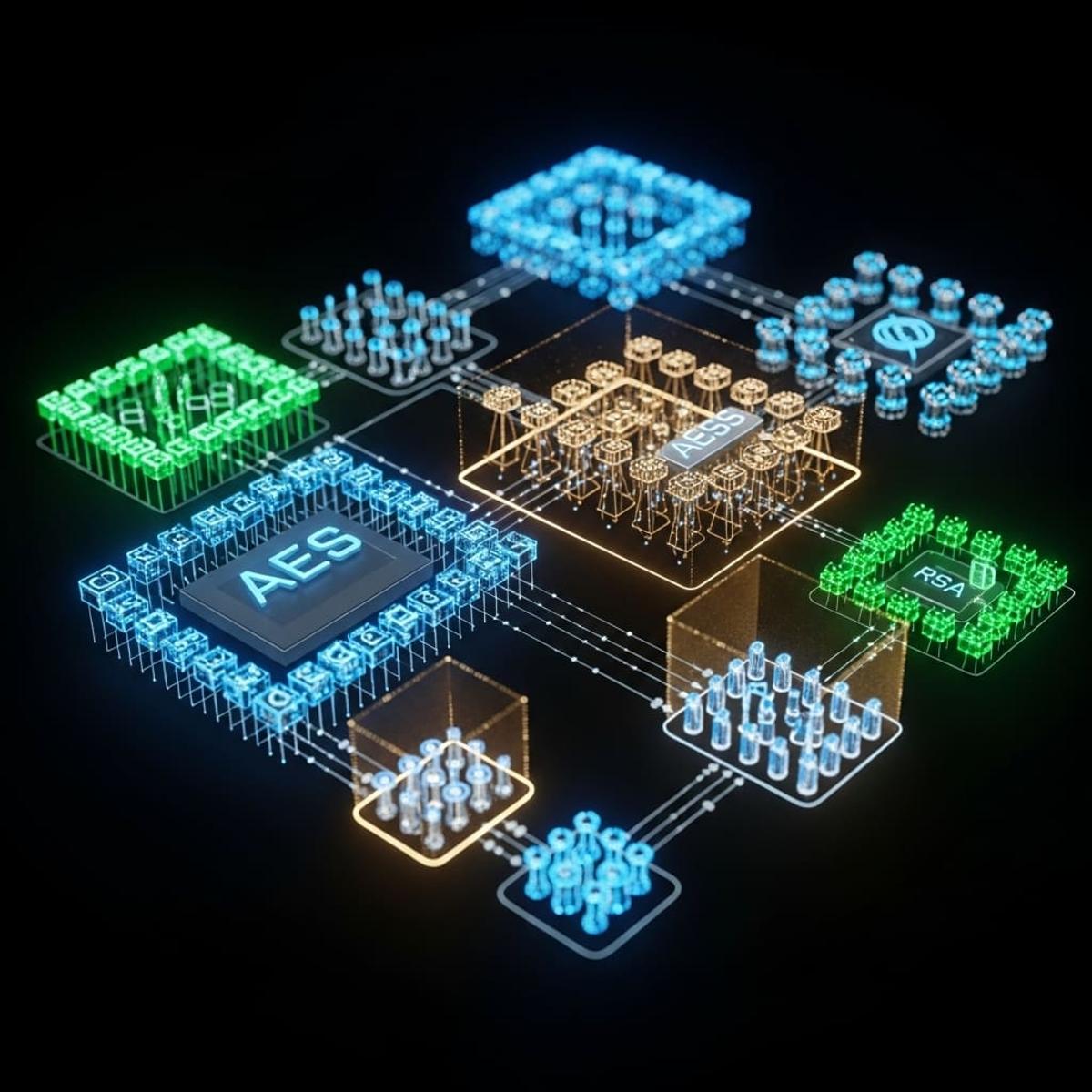
The imminent arrival of scalable quantum computers has turned post‑quantum cryptography from a research curiosity into a business imperative. Classical public‑key systems such as RSA and elliptic‑curve cryptography are vulnerable to Shor’s algorithm, prompting a shift toward lattice‑based, code‑based, hash‑based, multivariate, and isogeny‑based constructions. Each class offers a distinct security‑performance trade‑off, and the guide’s systematic comparison helps enterprises prioritize schemes that align with their latency, bandwidth, and regulatory requirements.
Industry momentum is coalescing around the NIST Post‑Quantum Cryptography standardisation effort, which now defines a shortlist of algorithms ready for deployment. Yet moving from theory to production introduces challenges: constrained IoT devices struggle with larger key sizes, and legacy systems demand hybrid solutions that blend quantum‑resistant primitives with proven symmetric ciphers. The authors’ deep dive into quantum key distribution—covering BB84, MDI‑QKD, and the emerging Twin‑Field protocol—highlights a complementary path for securing key exchange, especially in high‑value sectors like finance and defense. Practical tutorials and performance benchmarks illustrate how to integrate these protocols without sacrificing throughput.
Looking ahead, the guide emphasizes governance and migration strategies as critical success factors. Organizations must develop phased rollouts, invest in tooling that abstracts algorithm selection, and stay agile as NIST finalises its standards. Ongoing research into more efficient lattice constructions, error‑correcting code optimisations, and hardware‑accelerated isogeny calculations promises to reduce overheads and broaden adoption. By framing these technical advances within a clear roadmap, the guide equips leaders to future‑proof their cryptographic infrastructure against the quantum era.
Quantum Computing Advances Cryptographic Algorithms for Data Security , a Doctoral Guide
0
Comments
Want to join the conversation?
Loading comments...