Quantum Key Distribution Security Framework Achieves Rigorous Phase-Error Estimation with Correlated Sources
•January 19, 2026
0
Key Takeaways
- •Modulator‑induced pulse correlations previously invalidated proofs
- •Framework folds correlations into overall phase‑error bound
- •Single privacy‑amplification step replaces multiple sub‑key processes
- •Applies to prepare‑and‑measure and interference‑based QKD
- •Improves composable security for real‑world quantum networks
Summary
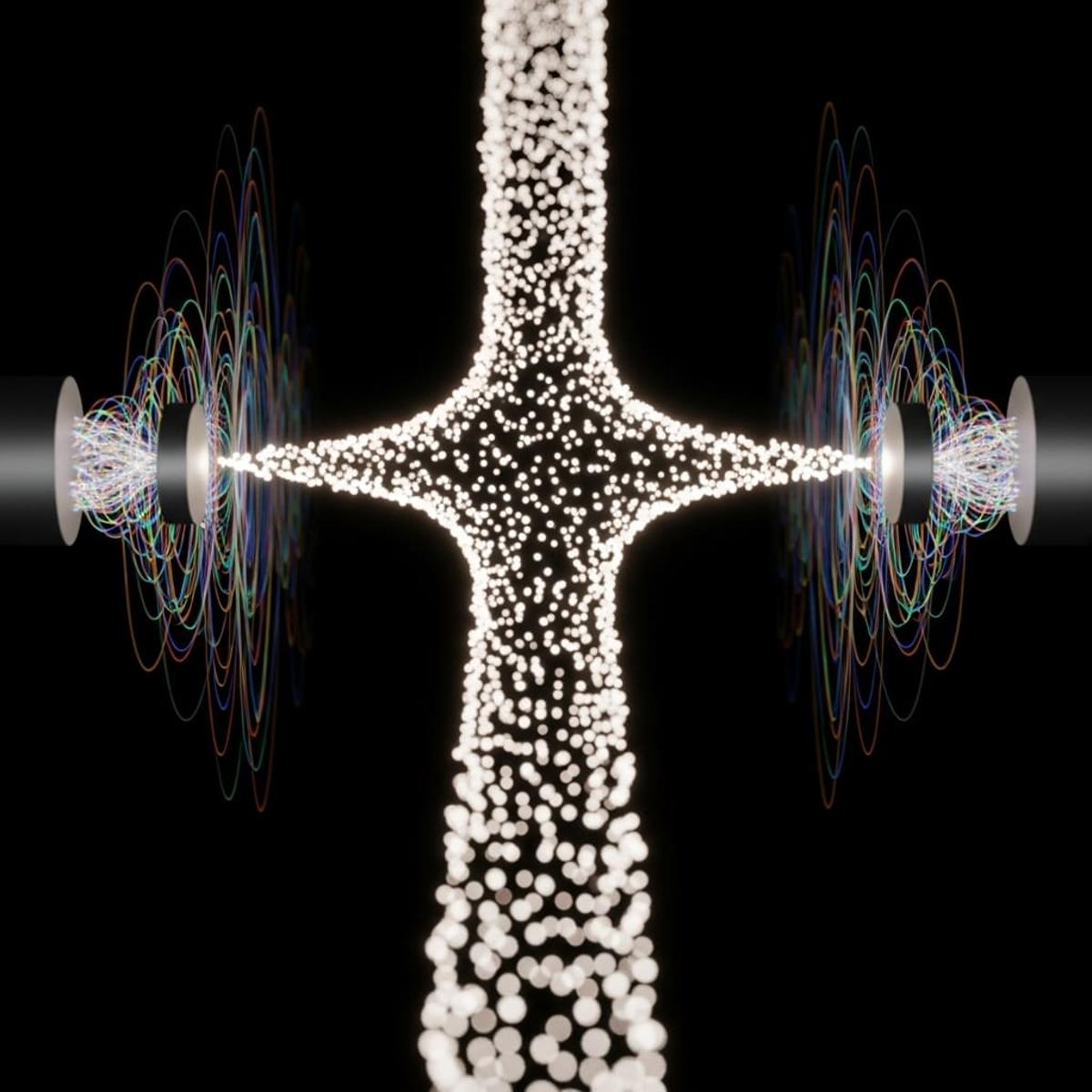
A research team led by Guillermo Currás‑Lorenzo and colleagues has introduced a rigorous mathematical framework that extends phase‑error‑estimation security proofs to quantum key distribution (QKD) systems with correlated pulse sources. The new model directly incorporates encoding correlations caused by practical modulator limitations, allowing a single phase‑error bound to cover the entire sifted key. By eliminating the need for separate privacy‑amplification steps across protocol partitions, the framework simplifies composable security analysis for both prepare‑and‑measure and interference‑based QKD architectures. Experimental validation confirms its applicability to real‑world devices.
Pulse Analysis
Quantum key distribution promises provable security, yet real devices often betray textbook assumptions. In practice, electro‑optic modulators cannot switch instantaneously, creating subtle correlations between consecutive optical pulses. Traditional security proofs, which treat each pulse as independent, become vulnerable, forcing engineers to add ad‑hoc mitigations or accept reduced key rates. Recognizing this mismatch, the new framework treats these temporal dependencies as integral parts of the quantum state, embedding them within the phase‑error estimation that underpins QKD security. By mathematically proving that individual phase‑error bounds can be aggregated even under unbounded correlations, the authors provide a unified, rigorous security metric.
The core of the methodology lies in extending the source‑replacement technique to multi‑round correlated states while preserving the single‑round admissibility conditions required by existing proofs. This enables a single privacy‑amplification operation to secure the entire sifted key, simplifying protocol design and eliminating composability concerns that plagued earlier approaches. Experiments using a prepare‑and‑measure protocol demonstrated that only a modest adjustment to the failure probability is needed to accommodate long‑range dependencies, confirming that the theoretical bound remains tight in realistic settings. Moreover, the framework’s flexibility allows it to be transplanted into interference‑based schemes with untrusted relay nodes, broadening its relevance across the QKD ecosystem.
For the quantum‑communications industry, the breakthrough reduces the engineering overhead associated with mitigating source imperfections, potentially lowering hardware costs and accelerating time‑to‑market for commercial QKD services. It also paves the way for standardized security certifications that reflect actual device behavior, a critical step for regulatory acceptance. Future research may explore extending the approach to other temporally correlated quantum technologies, further solidifying the role of rigorous, implementation‑aware security analysis in the emerging quantum network era.
Comments
Want to join the conversation?