
AWS Now Adds IDs to Security Group Rules
I thought there was a problem with the security group rules created by my bootstrap script initially but there was not. AWS added ids to security group rules which threw me for a loop in my tired state when I initially reviewed this.

Built AWS Batch Environment in 2.5 Weeks, Not Years
What I've Vibe Coded 🤖 In 2.5 Weeks ~ Compared to similar code I tried to implement for years to deploy an AWS environment for running batch jobs (as AI agents or not). How I did it. https://t.co/BlXxVvHagH https://t.co/btfZ0Yw1hK

Understanding Where FIDO2 Passkey Private Bits Reside
Where are the Private Bits of FIDO2 Compliant Passkey Stored? Just because you’re vibe coding doesn’t mean you no longer need to understand how things work. Research for my tool to start a batch job with a Yubikey. https://t.co/GK9IGy1Vi9 https://t.co/5NFLp5P7Oc

Kickstart Secure AI‑Powered Coding with Kiro CLI
All the complicated stuff I do with AI starts here. I still use this method with a few tweaks. Instead of writing a book I publish here. Learn to write good code with AI ~ and secure it. Implement A Simple...

Kiro Token Pricing: Cheap per Token, Costly Overages
This makes no sense: ⁉️ ➡️ Every Kiro plan costs 💲.02 / token. ➡️ So I’m going to barely run out of tokens at the end of the month and overages cost 💲.04 / token. What? ➡️ So to get $.02 per token...

Silencing AI Noise to Build Practical AWS Automation
I’ve started muting all the accounts pushing hot takes on ai 🤖 so I can focus on getting things done. If it’s not contributing towards accomplish something not really helping. Here’s what I’ve gotten done or trying to get done with...

Rust Could Block 80% of Chrome’s Recent Exploits
I asked Google AI mode if rust would have prevented these vulnerabilities out of curiosity. Here’s what it said. 1. The "Hard No" (Prevented by Rust) These categories make up about 80% of your list. In "Safe Rust," the compiler simply won't...

Chrome Update Fixes 26 Remote Code Execution Flaws
Chrome Security Update Patches 26 Vulnerabilities that Enable Attackers to Execute Malicious Code Remotely https://t.co/LgCt5yd3Zb

Avoid Third‑Party DNS Tools Without Customer Approval
I’m sure this works great. I haven’t tried it yet. As a pentester, don’t use this without customer approval because your customers may not want their vulnerability data stored in third party systems. Also they would have to add a...

Attacker Tested Npm Worm Chain with Dummy Payload
Interestingly, the threat actor is said to have swapped out the ICP backdoor payload for a dummy test string ("hello123"), likely to ensure that the entire attack chain is working as intended before adding the malware.

Cryptographer Challenges RustSec Ban on Bug Reports
Cryptographer fights RustSec ban over bug reports • The Register ~ What’s your take? Critical or not? https://t.co/a7d2iTtF6J

Check Your ProtonMail Account Before It Gets Deleted
If you have a @ProtonMail account and haven’t logged in recently better check it. I luckily randomly saw a message. Not really cool to randomly cancel people’s email accounts.

AI Agents Can Leak DNS: Bug or Intentional Abuse?
AI Agent DNS Leaks 🤖 Is this really a bug? Or is it functionality abuse? Because this is how the internet works. You decide. In any case be aware... https://t.co/Fmvxsh8210 https://t.co/uZo5hLB09k

Model's Training Cut‑off Date Misreported versus Paid Version
Asking model repeatedly when it’s training cut off date was and it is telling me April 2025. I asked a number of different types of questions. Claud Opus which I am paying for has a cut off of August 2025....

Anthropic Model Feels Like Reverting to an Older Version
Good idea. Related to someone’s comments about Anthropic models sometimes seeming “dumber” like they switched to an older model. Was feeling this last night.

Identity Isn’t a Perimeter; Real Security Needs Depth
Identity is not the new perimeter. Catchy phrases are not going to make security any easier. Dig deep and learn how to do it right.

AI Tools Amplify Devops Misconfigurations and Workflow Friction
Kiro + Opus 4.6 🤖 Struggling with - cross account lambda layer permissions and recognizing they are needed - CORS issues - maintaining correct variables and ARNs for multi-region deployments - Repeated unbound variables in complex bash scripts - making up variables that don’t exist -...

Choose AI or Deterministic Solutions Based on Accuracy Needs
Questions when starting an AI project: * Do I need a perfectly accurate result every time? ➡️ Use deterministic solution * Is a perfectly accurate result too costly, expensive, or even impossible? ➡️ Use AI to get closer to the result faster...

Use Deterministic Scripts, Not AI, for Meeting Attendee Data
I just saw a post about using AI to query meeting attendees. I personally would never use an AI prompt for that if I needed an accurate result. I don’t think it is the right tool for that problem. It will...

Specialized DNS Proxy Needed for Detecting Beacon
I work up thinking about this and think I’m going to update my agent framework to use traffic inspection proxy that only allows specific domain names for DNS. There are other reasons you might want to do that which I’ve...

Check for “Lzcdrtfxyqiplpd” To Spot GlassWorm Malware
Step Security advises developers who install Python packages directly from GitHub or run cloned repositories to check for signs of compromise by searching their codebase for the marker variable “lzcdrtfxyqiplpd,” an indicator of the GlassWorm malware. Also init.json, i.js

Automated Multi‑Region AWS Environment Deployment Script
So this turned into build an environment to run in. I wrote a script to deploy all the resources with guidance: Tested and deployed so far: Org root user and role Root policies Root permission boundary ou accounts - iam - KMS - dns - jobs - work - backup...

AWS IP Dump Misclassifies Services, Hindering Precise Monitoring
Took a while but modified this script to display all the IP ranges that match in the AWS json IP file for each IP. That way I can monitor which regions and services my system is connecting to. The problem...

Airline CEOs Push Congress to Fund Airport Security
US airline CEOs urge Congress to end standoff, pay airport security officers ~ this cannot be good for security at a time when we really need it. Also people are going to opt not to work for the government if...

AI Code Refactoring Requires Relentless Prompting and Patience
Spent last night refactoring terribly written software 🤖 into manageable pieces and refactoring requirements. Even though the code had a number of correct examples after I got it to deploy a few resources with the correct pattern, the agent continued...

Built Automated Batch Job Framework in Two Weeks
If you followed my journey to try to build a batch job framework (below) for like three years well, here’s what I got done vibe coding 🤖 as a chaperone for naughty AI agents and chatbots in two weeks. To...

Sandbox AI Models Locally to Avoid Security Risks
Trending on GitHub Be careful if running any kind of AI thingamajig on your laptop - put it in a sandbox with strict permissions. I haven’t looked into this in detail. GitHub - microsoft/BitNet: Official inference framework for 1-bit LLMs https://t.co/aPGkm86lnR

AI-Crafted IAM Policies Require Careful Human Review
This AI chatbots 🤖 do while vibe coding: I have a complex bootstrap script to set up an environment for my batch job framework. It needs to create accounts with a role in the root account. And that is all it...

AI Needs Human Oversight, Not Blame for Outages
If you are distressed because AI is causing outages at AWS well… don’t jump to conclusions like everyone did with the whole slew of S3 bucket debacles. Yes there will be problems as people learn how to use this new...

Mac's DNS Glitch Sparks Apple Support Confusion
What are the chances this is really Apple Support? And why is my Mac trying to connect to ip addresses instead Mountain View California right now instead of domain names. Don’t have time for this. 64.233.176.254 @google @apple https://t.co/qsHLJWmhRt

AI Code Isn’t Reliable, but It Speeds Development
You cannot trust code written by AI. But you can still use it to write code faster.

AI-Generated Code Still Fails Critical Security Checks
OMG so much time telling LLMs 🤖to create two lambdas that ALWAYS verify Yubikey before taking actions and after many rounds of bug fixes like wrong database table names for example (would never work) they come up with a...

AI‑Built Tool Cuts AWS Private Network Costs
I’m working on this but got hung up on networking once again The cost to deploy private networks on AWS is prohibitive for small businesses just trying out an idea. My solution is an alternate network for different environments like testing...

AI Coding Agents Can Install Unsafe Tools, Beware
Fun with coding agents. 🤖 Told it to check if a tool was installed and if not install it. Wrote code to use curl to get a common tool from some sketchy GitHub repo instead of using yum on EC2. People not paying...

Detect Reverse Shells with Process‑Network Monitoring Script
A Script To Monitor Application Network Connections 🔒 How would you spot a reverse shell such as was used in Lexus Nexus breach? I vibe coded this script to see parent and child processes with application paths, process names, IPs,...

AWS Secrets Manager Misuse Fueled Lexus Nexus Breach
Lexus Nexus Breach Involving AWS Secrets Manger, RDS, ECS 🔒☁️ Taking a look at the root cause of a breach on AWS, what is actually relevant, and how it may have been prevented https://t.co/Uox6A1LzE9 https://t.co/T7mTvFkZFZ

AI-Generated AWS Scripts Need Human Verification
So here’s a couple of fun things I tried that show how counting on AI 🤖 to do the right thing can go terribly wrong if you are not testing and paying attention. I tested automatically creating some AWS infrastructure scripts...

AWS Model Privacy: Risks of Insider Access and Data Leakage
Although I’m in 🩷 with Kiro CLI and like that AWS makes a copy of the model so your data doesn’t reach the model providers, I want to know more about AWS internal access to such things, customer segregation with...

Build Efficient Multi‑Agent Workflows with Kiro CLI
A Multi-Agent Workflow 🤖 Creating a multi-agent workflow with Kiro CLI (or any other AI tool for that matter) that processes tasks efficiently https://t.co/2gvuZWuBqj https://t.co/pYWOVMmaXe

Isolate Each Kiro CLI Agent in Secure Sandboxes
Securing Kiro CLI Custom AI Agents 🤖 Configuring multiple agents to work with Kiro CLI in individual sandboxes https://t.co/Bt0CxhDK5j https://t.co/Z4WJtwDoms

OAuth Redirect Abuse Fuels Phishing and Malware
OAuth redirection abuse enables phishing and malware delivery | Microsoft Security Blog I just wrote about this type of attack and what you should be asking about authentication processes. Modifying scopes is an authorization issue but it’s related. https://t.co/TucGqHuinb

AI-Powered Lambda Fixes CloudTrail Errors with Bedrock
Querying CloudTrail Errors And Getting AI Recommendations To Fix Them 🤖☁️ Creating a Lambda Function That Uses an AI Prompt with Bedrock and tests Claude and Nova models https://t.co/NQkQbdjudd https://t.co/mnM0kRO5hp

FT Blamed AI; It Was User Misconfiguration Error
We want to address the inaccuracies in the Financial Times' reporting yesterday. The brief service interruption they reported on was the result of user error—specifically misconfigured access controls—not AI as the story claims. https://t.co/0ApCIDNsJT

Know What Security Tools Access Before They Exploit You
Until it hacks everyone’s GitHub accounts and wipes out all their IP. Be careful with tools like this. Make sure you understand what it can access and what it can do. Understand where it is sharing your code and storing...
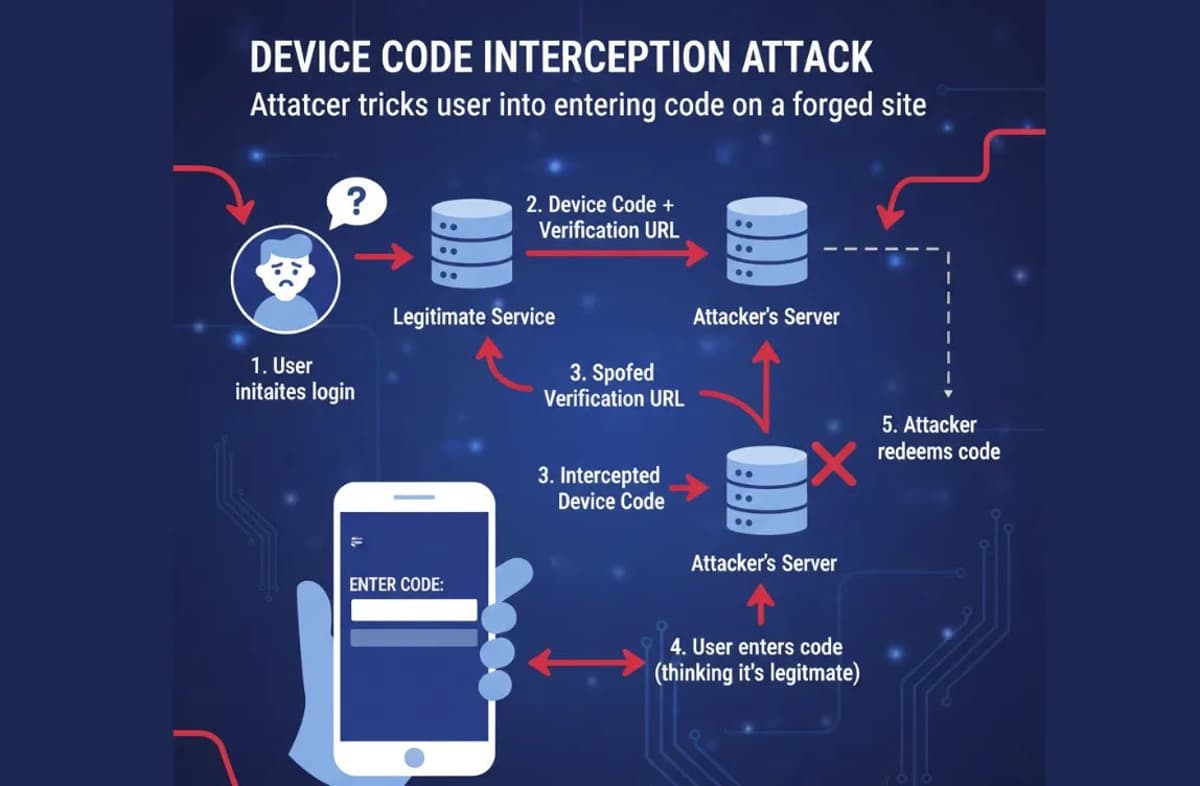
Defense in Depth: Evaluate Auth with Password + Yubikey
Questions to ask when evaluating an authentication mechanism 🔒 Why I still use a password with a Yubikey, not a passkey or a pin Why I dislike the device code flow with a browser How lack of segregation facilitated a Microsoft breach. Defense...

AI Threatens CAPTCHA and Voice Biometrics Authentication
“AI can defeat CAPTCHA systems and analyse voice biometrics to compromise authentication,” [TR: Never trusted voice recognition, it’s too fuzzy to use for auth in my opinion. Infecting memory is an interesting problem.]

AI Chatbots Spot Security Bugs, Not Write Safe Code
Finding Security Bugs in Code With AI Chatbots and Agents 🤖🦊 Although you can't trust code written by an AI chatbot or model you can use one to help you better secure your code https://t.co/mhQJgBlHPe https://t.co/VO48Wro7LJ

Secure AI: Blend Deterministic Controls with Trustworthy Insights
How can a company like @TIBCO win in the age of AI? Was just reading about their current market strategy and risk. I was involved with a TIBCO project while implementing a tax solution at a Fortune 1000 company. Focus...

Ask the Problem First, Then Match Tools
This is an interesting thread. Everyone is suggesting tools to solve the problem. I’d start by asking more about the data and the questions the customer is trying to answer or problems they are trying to solve first before recommending...
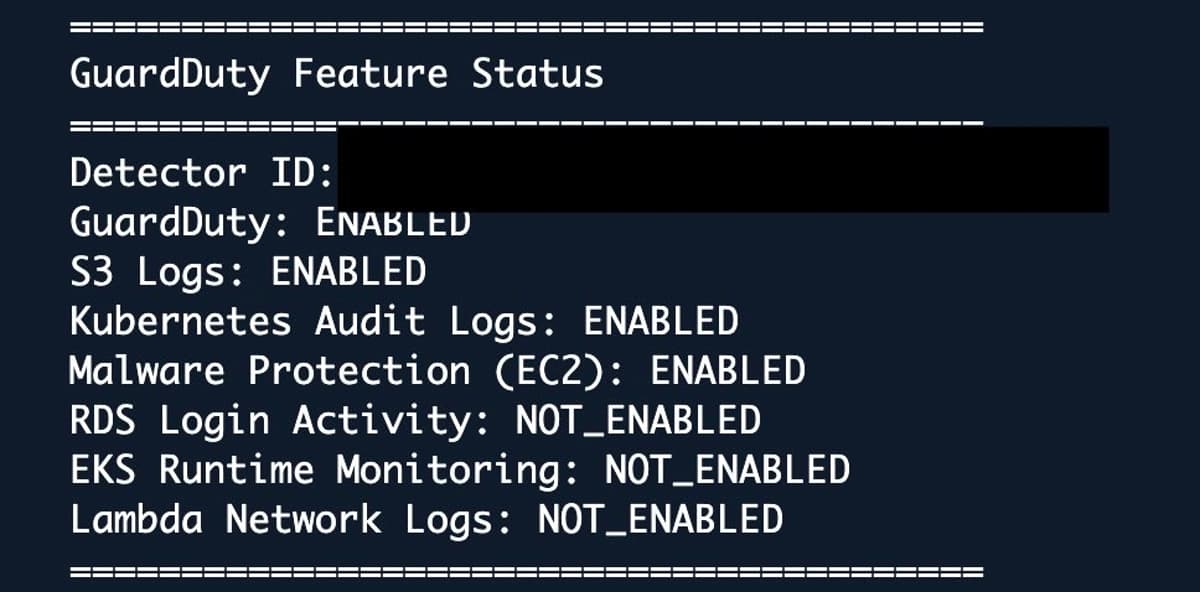
Automated GuardDuty Feature Audit and Enablement in Hours
Vibe coded 🤖 a script to list which AWS GuardDuty features are enabled in minutes. Took 15-30 minutes to correct it. The script to enable disabled features, sub features, and create an s3 malware scan plan took about two hours. See blog...