Life Mirrors Art: Ransomware Hits Hospitals on TV & IRL
•February 27, 2026
0
Why It Matters
Ransomware attacks now directly threaten patient care continuity, forcing hospitals to prioritize cyber resilience as a core safety issue. The convergence of media portrayal and real‑world breach amplifies stakeholder urgency to strengthen defenses and response plans.
Key Takeaways
- •HBO's ransomware scene mirrors real hospital disruptions
- •UMMC attack halted operations across 35 clinics
- •Executives often hesitate before shutting down IT systems
- •Clinical downtime plans crucial for patient safety
- •Boards now view cyber risk as patient‑safety issue
Pulse Analysis
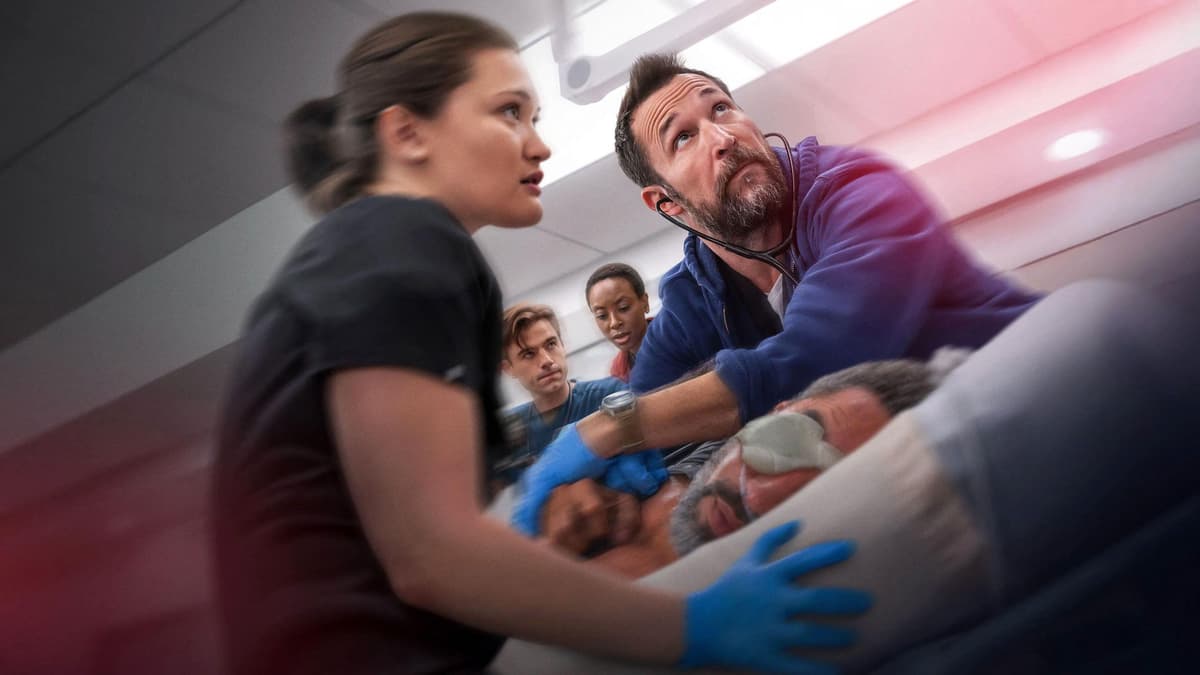
The convergence of fiction and reality this week highlighted how vulnerable health systems remain to ransomware. HBO’s drama ‘The Pitt’ dramatized a hospital’s IT shutdown, showing clinicians reverting to paper charts, fax machines, and memory—a scenario that felt familiar to many CISOs. Within hours of the episode’s broadcast, the University of Mississippi Medical Center confirmed a ransomware breach that disabled its Epic electronic health‑record system across 35 outpatient sites. The synchronicity amplified public awareness, underscoring that cyber‑threats are no longer abstract plot devices but operational crises that can paralyze patient care.
Experts point out that the show got the chaos right but missed key decision‑making nuances. In practice, CEOs rarely pull the plug without consulting IT and security leaders, because an abrupt shutdown can jeopardize life‑saving equipment and delay emergency care. Hospitals therefore invest in clinical resilience plans that map medication dispensing, lab reporting, and patient triage when digital tools fail. Regular tabletop exercises and downtime drills test these protocols, ensuring staff can transition to analog workflows without compromising safety. Such preparedness reduces the financial hit and limits deferred care that often follows a ransomware incident.
The incident has also nudged boardrooms to treat cyber risk as a patient‑safety issue rather than an IT inconvenience. Survey data from Proofpoint shows 70 % of compromised hospitals report care disruptions, prompting executives to demand measurable resilience metrics alongside recovery time objectives. As regulators tighten reporting requirements, hospitals that demonstrate robust credential hygiene, segmented networks, and documented downtime strategies will gain a competitive edge. Investing in continuous monitoring, staff training, and third‑party incident response can transform a potential shutdown into a managed event, preserving trust and revenue.
Life Mirrors Art: Ransomware Hits Hospitals on TV & IRL
0
Comments
Want to join the conversation?
Loading comments...