
Open Fibre Data Standard and the Visibility Gap in Network Resilience
The Open Fibre Data Standard (OFDS) proposes a unified, machine‑readable schema to map terrestrial fibre routes, nodes, and ownership, addressing the chronic visibility gap that hampered resilience assessments after New Zealand’s Cyclone Gabrielle. Discussions at NZNOG 2026 highlighted how fragmented, outdated maps prevent operators from identifying shared risks and true path diversity. By standardising data, OFDS enables cross‑operator analysis, helping pinpoint single points of failure and improve backup planning. The article outlines a pragmatic, incremental adoption roadmap for operators, regulators, and researchers.

Are Data Centres Moving to DC Power?
Data centre operators are revisiting direct‑current (DC) power as a way to trim energy costs for AI‑intensive workloads. By moving the AC‑to‑DC conversion from each server to a larger rack‑level supply, facilities can capture 10‑15% savings on total power budgets....

Repairing the RPKIViews H1 2026 Archives
RPKIViews repaired its H1 2026 archives after discovering a CCR ordering bug in older rpki‑client versions. Using a new rpkitouch repair feature, the team reprocessed 110 rpkispools, handling 190,601 CCRs and over 19 million RPKI objects. The effort compressed the dataset from...

The Invisible Hand: Regaining Control of Service Quality From Outsourced Satellite Networks
Mobile network operators are increasingly leasing Low Earth Orbit satellite capacity from satellite network operators to fill coverage gaps, but the lack of direct control creates a trust gap and makes service‑level enforcement difficult. Researchers at Tsinghua University introduced Ripple,...
ReAct: Reflection Attack Mitigation for Asymmetric Routing
ReAct is a new mitigation framework for amplified reflection DDoS attacks that works even when traffic follows asymmetric routes. It leverages programmable data‑plane devices such as Intel Tofino switches and Nvidia Bluefield‑3 smart NICs to match request and response transaction IDs using...
![[Podcast] CIDR Inside](/cdn-cgi/image/width=1200,quality=75,format=auto,fit=cover/https://blog.apnic.net/wp-content/uploads/2026/04/CIDR_FT.jpg)
[Podcast] CIDR Inside
In the latest episode of APNIC’s PING podcast, chief scientist Geoff Huston revisits the origins of Classless Inter‑Domain Routing (CIDR) and the two‑decade‑old CIDR Report that monitors routing announcements. He explains how CIDR shattered the rigid Class A‑C model, enabling flexible...
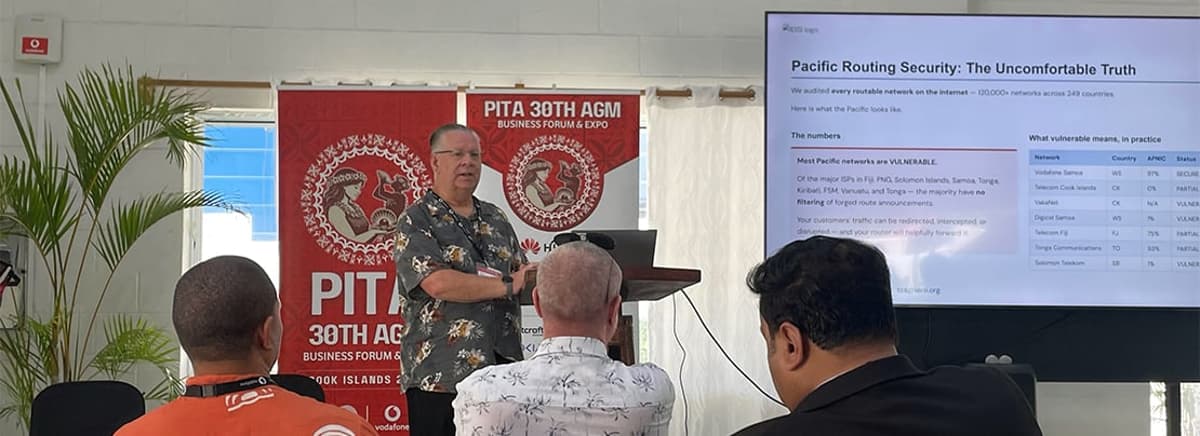
Pacific Routing Security Sets a Deadline
At the APNIC Sub‑Regional Forum during PITA 30 in Rarotonga, routing‑security chair Terry Sweetser asked Pacific telco leaders whether they filter forged BGP announcements. The discussion revealed widespread uncertainty, with only 49 of 116 regional ASNs showing any protection and many...
Google Hits 50% IPv6
Google announced that half of its global traffic now arrives over IPv6, marking a symbolic milestone for the next‑generation Internet protocol. The 50 % figure reflects rapid growth but does not instantly resolve lingering technical and operational gaps. Industry observers note...
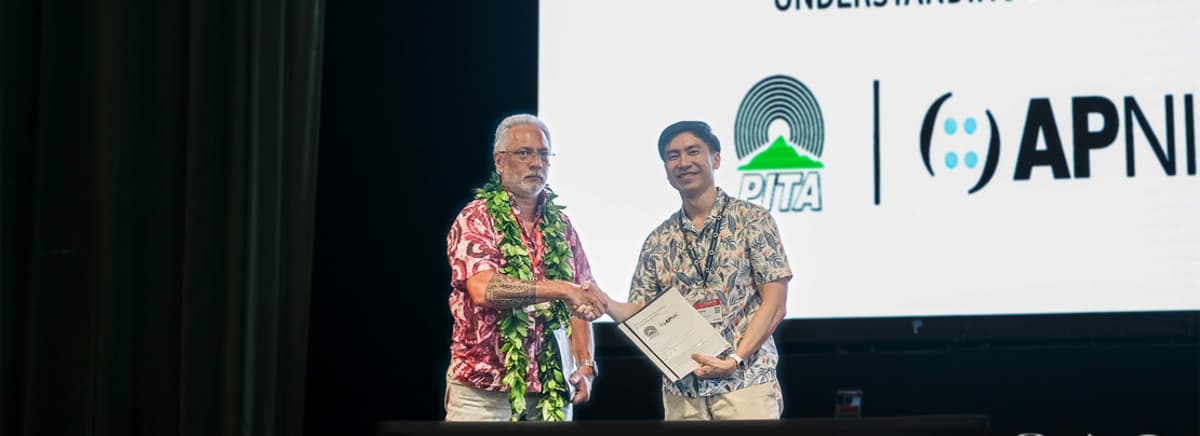
APNIC and PITA Renew MoU to Strengthen Cooperation in the Pacific
APNIC and the Pacific Islands Telecommunications Association (PITA) have renewed their Memorandum of Understanding, updating a partnership first signed in 2002. The refreshed agreement, signed at PITA 30 in the Cook Islands, emphasizes joint training, capacity building, and the launch of...

Revocation of X.509 Certificates
Recent measurements reveal two critical trends in X.509 certificate revocation. A SIGCOMM ’25 paper proposes publishing only revoked serial numbers as DNSSEC‑signed TXT records, leveraging NSEC and aggressive negative caching to achieve roughly 99.8% cache‑hit rates, with Let’s Encrypt’s 612 million...

Strengthening Your Network Security with APNIC’s Products and Tools
APNIC held a webinar in late March 2026 on strengthening network security, drawing 211 participants. The session highlighted the evolution from traditional IRR to cryptographic solutions like RPKI ROAs and the upcoming ASPA for path validation. It also showcased APNIC’s...
![[Podcast] IP Networking in Deep Space](/cdn-cgi/image/width=1200,quality=75,format=auto,fit=cover/https://blog.apnic.net/wp-content/uploads/2026/04/PIA14761.jpg)
[Podcast] IP Networking in Deep Space
Marc Blanchet of Viagenie discussed extending Internet Protocol beyond low‑Earth orbit, targeting the Moon, asteroid belt and interplanetary missions. Using Linux TUN, TC‑NETEM and 64‑bit delay modeling, his team can simulate round‑trip times of hours, revealing TCP’s limitations in deep‑space environments....

Exploring the Blind Spot of IXPs Route Servers
Route servers at large IXPs filter BGP updates using a two‑stage process—RPKI validation followed by IRR‑based prefix whitelists derived from AS‑SET objects. The article reveals that AS‑SET expansion discards the origin‑ASN relationship, creating a blind spot where invalid announcements can...

Connecting the Pacific: Infrastructure, Operations, and Regional Cooperation
The Pacific region is witnessing incremental but meaningful upgrades to its Internet ecosystem, highlighted by new submarine‑cable projects such as Google’s Bulikula system, the VAKA cable to Tuvalu, and upcoming Hawaiki Nui 1 and Adamasia cables. Local Internet Exchange Points are slowly...

Setting up Akvorado: A NetFlow Analyser for Your IPv6-First Network
Terry Sweetser details how to deploy Akvorado, an open‑source NetFlow/IPFIX collector, on a modest SOHO server using Docker Compose. The guide walks through enabling SNMP on a router, configuring NetFlow v9 export, and launching the Akvorado stack with ClickHouse and...