BetaNews
A leading online source of technology news and analysis

GenAI Data Policy Violations More than Doubled in 2025
GenAI‑related data policy violations more than doubled in 2025, with organizations now averaging 223 incidents per month and the top 25 percent facing 2,100 monthly breaches. User‑generated prompts surged 500 percent to 18,000 per organization, while regulated‑data uploads account for 54 percent of violations. Netskope Threat Labs reports that 47 percent of employees still use personal, unmanaged GenAI accounts despite broader corporate tool adoption. Nine‑in‑ten firms now block at least one GenAI application, reflecting tighter enforcement as usage expands.

Amazon Rolls Out Its Alexa+ AI Assistant to the Web
Amazon announced that its Alexa+ AI assistant is now available via any web browser, initially through an Early Access program at Alexa.com. The web version mirrors the device‑based experience, handling shopping, calendar management, document analysis and smart‑home control. By decoupling...
![Why 'Slow AI' Is Holding Back Enterprise Deployments [Q&A]](https://hixhlmpcokxhartfkpyi.supabase.co/storage/v1/render/image/public/images/thumbnails/fbfd0ed9cfccdbd34af24df287140d4b.webp?width=1200&resize=contain&quality=75)
Why 'Slow AI' Is Holding Back Enterprise Deployments [Q&A]
Enterprises are hitting a hidden bottleneck dubbed “slow AI,” where outdated, complex networks impede the rapid rollout of AI workloads. AI’s massive data throughput, ultra‑low latency, and hybrid‑cloud demands expose gaps in legacy network capacity, visibility, and security. Companies often...

Resecurity Says Security Breach Was Nothing More than Hackers Duped by a Honeypot
Resecurity disclosed that a recent breach claim was a honeypot trap, not a genuine data loss. The Scattered Lapsus$ Hunters (SLH) group boasted access to internal systems, but only interacted with synthetic accounts populated with fake consumer and payment records....
![Generative AI: Closing the Developer Gap and Redefining the Software Moat [Q&A]](https://hixhlmpcokxhartfkpyi.supabase.co/storage/v1/render/image/public/images/thumbnails/14576053824f0ed38bdc211ea3ffa9a8.webp?width=1200&resize=contain&quality=75)
Generative AI: Closing the Developer Gap and Redefining the Software Moat [Q&A]
Generative AI is rapidly closing the long‑standing developer shortage by automating repetitive coding tasks and empowering citizen developers, allowing enterprises to clear backlogs and accelerate delivery. At the same time, the same productivity boost is eroding traditional technological moats built...
![Why Keeping Old Customer Records Could Cost Millions [Q&A]](https://hixhlmpcokxhartfkpyi.supabase.co/storage/v1/render/image/public/images/thumbnails/de2cb970de6f40b6d4d6496dff588ce3.webp?width=1200&resize=contain&quality=75)
Why Keeping Old Customer Records Could Cost Millions [Q&A]
Companies that retain outdated customer records face amplified breach costs and reputational damage, as legacy data expands the attack surface. Regulators such as the EU’s GDPR have levied multi‑million‑dollar fines on firms that hoard unnecessary personal information. Data minimization—collecting only...

Maturing ID Wallets, Investment for Compliance and Confidential AI -- Privacy Predictions for 2026
Industry leaders predict that digital identity wallets will move from pilots to global scaling by 2026, anchored by the EU Digital Identity (EUDI) regulation and expanding support in Apple and Google wallets. Companies will boost spending on privacy, compliance and...
![AI Video Tools and How They’re Changing Business Communication [Q&A]](https://hixhlmpcokxhartfkpyi.supabase.co/storage/v1/render/image/public/images/thumbnails/6ab6f686913f489f6e6e0b26927a4252.webp?width=1200&resize=contain&quality=75)
AI Video Tools and How They’re Changing Business Communication [Q&A]
AI video tools are reshaping business communication by slashing production time and cost, enabling richer, on‑demand content. CraftStory’s CEO Victor Erukhimov explains how their platform generates long‑form videos through segmented diffusion and high‑frame‑rate data, delivering a one‑minute video in about...

Nissan Confirms Customer Data Was Involved in Red Hat Security Breach
Japanese automaker Nissan confirmed that a security breach at its software partner Red Hat exposed personal data of roughly 21,000 customers in Fukuoka. The leaked information includes names, addresses, phone numbers and partial email addresses, but no financial or credit‑card details....

Foxit PDF Editor Gains New Collaboration Safeguards and AI Features
Foxit released PDF Editor v2025.3 for Windows and Mac, adding privacy‑focused collaboration safeguards and a suite of AI tools. The update introduces region‑specific consent prompts, audit‑logged consent data, and automatic anonymization for users who decline. Integration with Microsoft Sensitivity Labels...
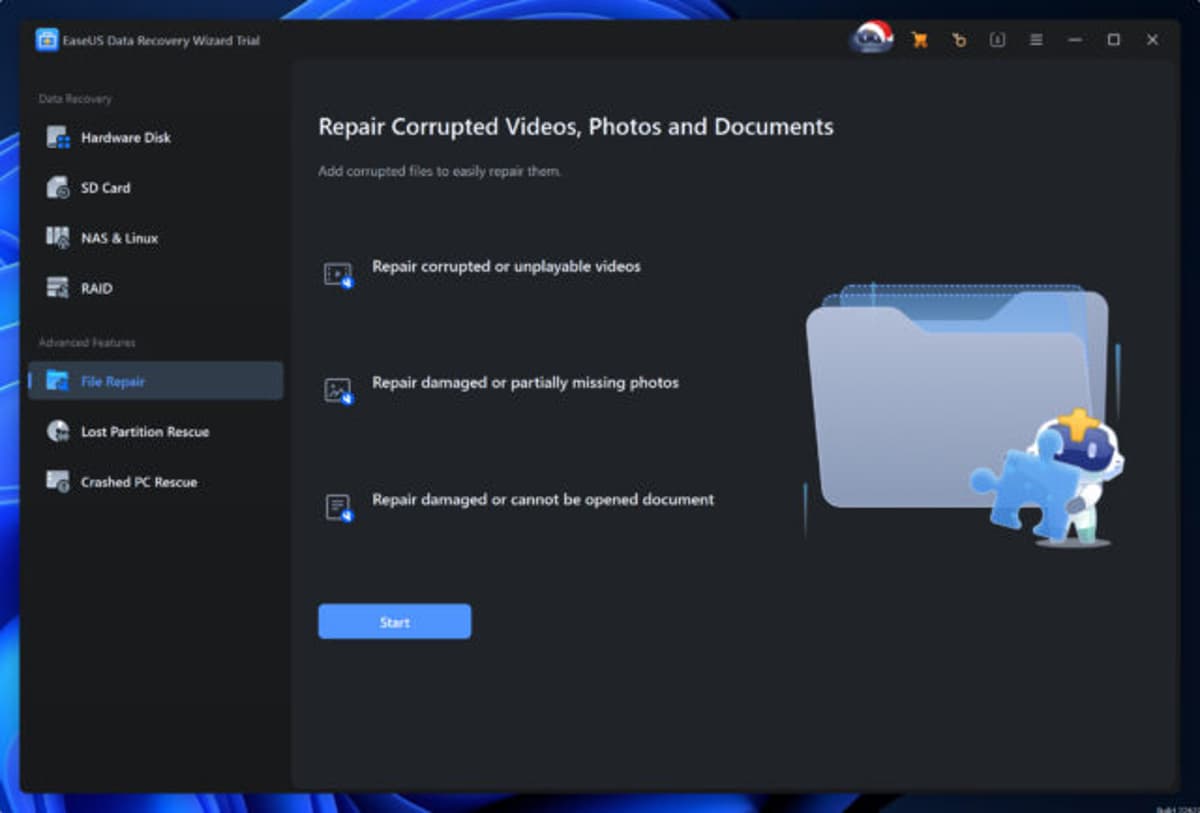
EaseUS Adds Fragmented File Recovery Tech to Data Recovery Wizard
EaseUS released Data Recovery Wizard 20.1.0, adding a SmartSector Rebuild (SSR) engine that targets fragmented files on heavily used removable storage. The SSR technology analyzes data signatures, metadata, and block proximity to reconstruct files that standard tools miss. EaseUS claims up...

NordProtect Rolls Out Expanded Monitoring Features for Identity Theft Detection
NordProtect, Nord Security’s identity‑theft protection service, has added expanded monitoring capabilities to detect fraud earlier. The upgrade includes credit monitoring across all three major bureaus, short‑term loan tracking, and comprehensive financial‑account alerts. Users also receive a TransUnion credit‑lock feature and...
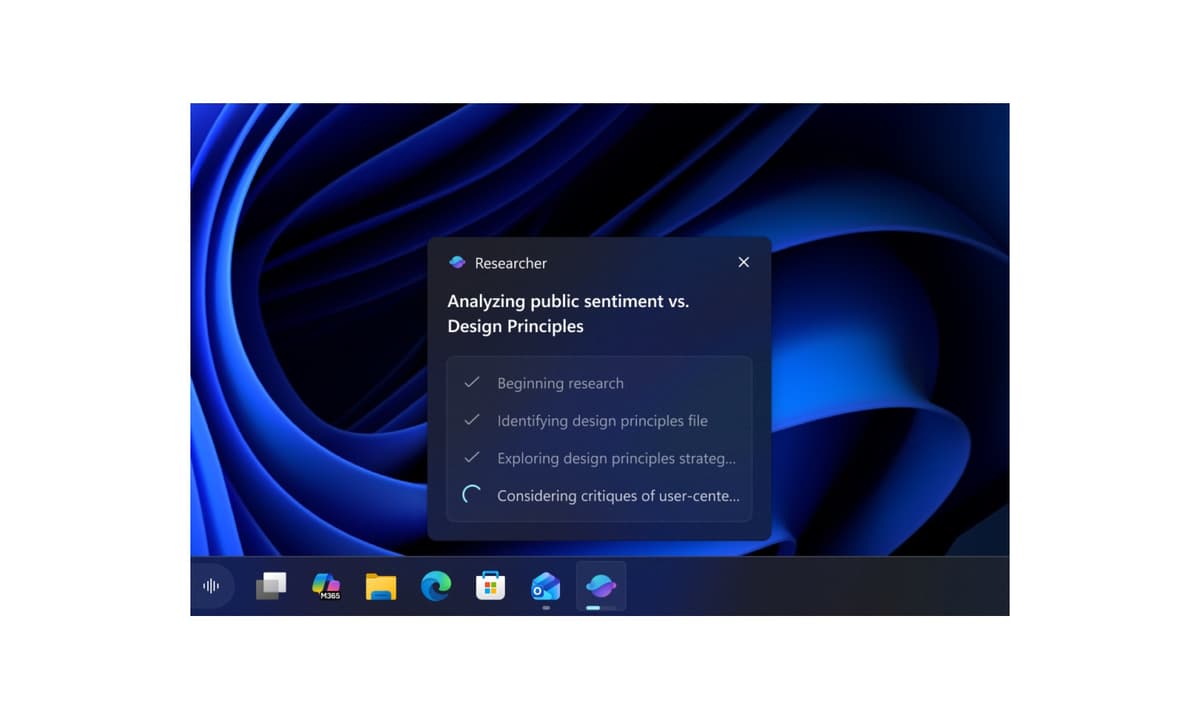
Microsoft Brings Ask Copilot and Agents to the Windows 11 Taskbar for Business Users
Microsoft released Windows 11 Insider Preview Build 26220.7523, adding Ask Copilot and AI Agents directly to the taskbar for commercial users. The opt‑in feature integrates Microsoft 365 Copilot, contextual Work IQ data, and voice or text interaction in a single click. Agents can be invoked via...

Cloudflare's Impact Report for 2025 Reveals How Elections, Journalism, and Nonprofits Faced Rising Online Threats
Cloudflare’s 2025 Impact Report highlights how its security suite shielded more than 3,000 public‑interest sites, including journalists, NGOs, and election infrastructure, from a staggering 9.9 billion cyber‑attacks each month. The Athenian Project protected 441 election‑related properties, blocking 200 million DDoS attacks across...