Recent Posts
News•Feb 27, 2026
Life Mirrors Art: Ransomware Hits Hospitals on TV & IRL
The recent episode of HBO’s drama "The Pitt" portrayed a hospital’s IT systems being shut down by ransomware, forcing clinicians to revert to paper‑based processes. Hours later, the University of Mississippi Medical Center confirmed a real ransomware breach that crippled its Epic electronic health‑record system across 35 clinics. Experts praised the show’s realistic depiction of operational chaos but noted inaccuracies in executive decision‑making. The incident underscores the growing operational and patient‑safety risks ransomware poses to healthcare providers.
By Dark Reading

News•Feb 27, 2026
The Case for Why Better Breach Transparency Matters
Cybersecurity experts Adam Shostack and Adrian Sanabria argue for greater breach transparency at RSA Conference. They highlight that current practices treat incidents as legal liabilities, limiting shared learning. The speakers propose structured feedback loops similar to aviation and medicine. Without...
By Dark Reading

News•Feb 26, 2026
Marquis V. SonicWall Lawsuit Ups the Breach Blame Game
Fintech firm Marquis, which serves over 700 banks, filed a lawsuit against firewall vendor SonicWall after a ransomware breach exposed client data for roughly 780,000 individuals. SonicWall later disclosed that a breach of its own firewall configuration backups affected all...
By Dark Reading

News•Feb 25, 2026
PCI Council Says Threats to Payments Systems Are Speeding Up
The PCI Security Standards Council published its inaugural 2025 annual report, the first since its 2006 founding, outlining a surge in payment‑system threats and the council’s expanding role. The report highlights accelerated attacks leveraging AI, ransomware incidents such as BridgePay,...
By Dark Reading

News•Feb 25, 2026
Why 'Call This Number' TOAD Emails Beat Gateways
Researchers at StrongestLayer analyzed about 5,000 phishing emails that evaded secure email gateways between December 2025 and early 2026. They found that telephone‑oriented attack delivery (TOAD), which consists solely of a phone number, represented roughly 28 % of all bypasses and...
By Dark Reading
.jpg?width=1280&auto=webp&quality=80&disable=upscale)
News•Feb 25, 2026
'Richter Scale' Model Measures Magnitude of OT Cyber Incidents
The Operational Technology Incident (OTI) Impact Score, unveiled at the S4x26 conference, offers a Richter‑scale‑style metric for gauging OT cyber‑attack consequences. It combines severity, reach, and duration into a single figure, with assessments delivered via an online portal within 12...
By Dark Reading

News•Feb 23, 2026
More Than Dashboards: AI Decisions Must Be Provable
Enterprise leaders are demanding proof of what AI systems actually did, not just what they were designed to do or what dashboards report. As AI moves into regulated, high‑risk environments, boards and auditors expect decision‑level evidence for each action. The...
By Dark Reading
_roibu_Alamy.jpg?width=1280&auto=webp&quality=80&disable=upscale)
News•Feb 23, 2026
Iran's MuddyWater Targets Orgs With Fresh Malware as Tensions Mount
Iran‑linked APT MuddyWater has escalated its campaign, dubbed Operation Olalampo, against organizations in the Middle East and Africa. The group continues to rely on spear‑phishing but also began exploiting public‑facing servers, delivering several previously unseen malware strains such as the...
By Dark Reading

News•Feb 23, 2026
Enigma Cipher Device Still Holds Secrets for Cyber Pros
The Enigma cipher machine, originally built in 1918 and later adapted by the Nazis, saw only a few hundred surviving units out of an estimated 35,000‑40,000 produced. Historian‑turned‑cybersecurity expert Marc Sachs will discuss the device’s historic failures at RSAC 2026, highlighting...
By Dark Reading
News•Feb 23, 2026
600+ FortiGate Devices Hacked by AI-Armed Amateur
A financially motivated, Russian‑speaking threat actor used generative AI services to compromise more than 600 Fortinet FortiGate firewalls worldwide between January and February. The campaign avoided exploiting software vulnerabilities, instead leveraging exposed management ports and reused credentials with single‑factor authentication,...
By Dark Reading

News•Feb 20, 2026
Latin America's Cyber Maturity Lags Threat Landscape
Intel 471’s 2025 report shows Latin America’s cyber‑maturity is improving but the region faces a rapidly intensifying threat landscape. Ransomware incidents jumped 78% year‑over‑year, with more than 450 breaches recorded, while Brazil alone accounted for 30% of ransomware and extortion attacks....
By Dark Reading
News•Feb 19, 2026
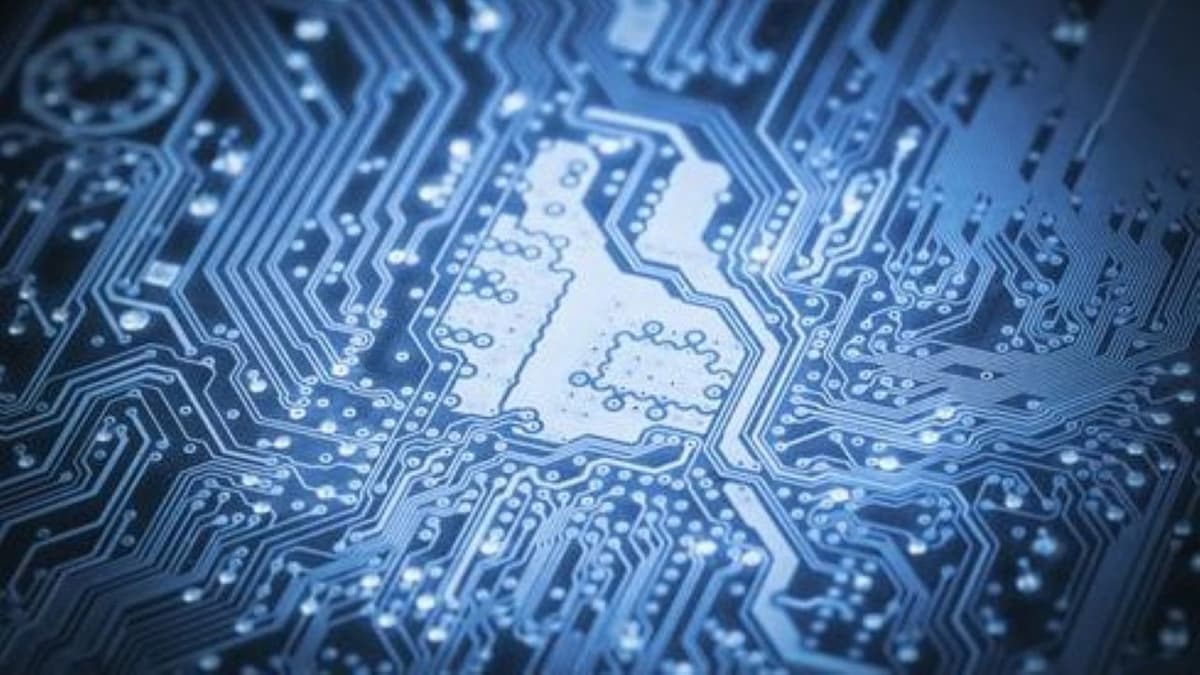
Emerging Chiplet Designs Spark Fresh Cybersecurity Challenges
Chiplet technology is reshaping semiconductor design by allowing modular, mix‑and‑match silicon components, accelerating AI data‑center and autonomous‑vehicle development. However, the distributed manufacturing model creates new supply‑chain vulnerabilities, as a single compromised chiplet can introduce hardware Trojans that affect entire systems....
By Dark Reading
News•Feb 19, 2026
Supply Chain Attack Secretly Installs OpenClaw for Cline Users
Dark Reading reported that the npm package for Cline version 2.3.0 was compromised, causing it to silently download the OpenClaw tool during an eight‑hour window. The breach stemmed from a prompt‑injection flaw that allowed an attacker to steal release tokens and...
By Dark Reading

News•Feb 19, 2026
Connected and Compromised: When IoT Devices Turn Into Threats
The proliferation of consumer and enterprise IoT devices continues unchecked, yet most lack basic security controls such as passwords and encryption. Research presented by Mattia Epifani at RSAC 2026 shows that devices—from Amazon Echo to smart refrigerators—store unprotected audio, credentials, and personal...
By Dark Reading

News•Feb 19, 2026
More Than 40% of South Africans Were Scammed in 2025
South Africa experienced a staggering 77% scam victimization rate in the 12 months to early 2025, with 42% of adults losing money, averaging $130 per incident. GASA estimates scammers extracted roughly $2.3 billion from over 17.5 million South Africans, equating to about...
By Dark Reading