
Stealer Spoofs Google, Microsoft & Apple, Then Backdoors macOS
SentinelOne has uncovered SHub Reaper, a new macOS malware that blends infostealer and backdoor capabilities. The variant disguises itself as Apple, Google and Microsoft updates, using fake WeChat and Miro installers and typosquatted domains to lure victims. It bypasses Apple’s Tahoe 26.4 mitigations by executing malicious AppleScript via the applescript:// scheme, establishing a persistent LaunchAgent that checks in every minute. The combination of credential theft, wallet hijacking and long‑term backdoor access marks a shift in macOS threat tactics.

Microsoft Exchange Zero-Day Under Attack, No Patch Available
Microsoft disclosed a critical zero‑day vulnerability (CVE‑2026‑42897) in Exchange Outlook Web Access that allows attackers to execute cross‑site scripting attacks and spoof emails. The flaw affects on‑premise Exchange Server 2016, 2019 and Subscription Edition, earning a Microsoft CVSS score of...

Taiwan Incident Highlights Cybersecurity Gaps in Rail Systems
On April 5 a 23‑year‑old rail enthusiast spoofed Taiwan High Speed Rail’s emergency radio, triggering emergency brakes on three bullet trains and causing a 48‑minute service disruption. The hack leveraged the Terrestrial Trunked Radio (TETRA) system, which can be secure but...

Congress Puts Heat on Instructure After Canvas Outage
Congressional committees are pressing Instructure after its Canvas learning‑management system suffered two separate breaches within a week, attributed to the ShinyHunters cybercrime group. The attacks exposed more than 3 TB of data from over 9,000 educational institutions, including student IDs, emails,...
'FrostyNeighbor' APT Carefully Targets Govt Orgs in Poland, Ukraine
Belarus‑linked APT group FrostyNeighbor, also known as Ghostwriter, has launched a new spear‑phishing campaign targeting government and military entities in Poland and Ukraine. The operation, active since March, uses deceptive PDFs that impersonate Ukrainian telecom provider Ukrtelecom and delivers a...

Foxconn Attack Highlights Manufacturing's Cyber Crisis
Foxconn confirmed a cyberattack at several North American factories, with the Nitrogen ransomware gang claiming responsibility. The gang alleges it exfiltrated over 11 million files, roughly 8 TB of data, including confidential designs for clients such as Apple, Nvidia and Google. While...

Attackers Weaponize RubyGems for Data Dead Drops
Security firm Socket uncovered a new threat campaign, dubbed GemStuffer, that abuses the RubyGems package registry as a dead‑drop for exfiltrated data. Over 100 malicious gems were published, each containing scripts that scrape public council data in London and then...

Hugging Face Packages Weaponized With a Single File Tweak
A security researcher at HiddenLayer uncovered a supply‑chain flaw in Hugging Face’s tokenizer.json file. By altering a single line in this plain‑text mapping, an attacker can hijack model outputs, capture every URL the model accesses, and steal embedded API credentials via...

Hackers Use AI for Exploit Development, Attack Automation
Google’s Threat Intelligence Group released research showing that threat actors are now using large language models to develop exploits and automate attacks. The report documents a zero‑day Python script that bypasses two‑factor authentication, likely generated with an AI model, and...

Cyber Espionage Group Targets Aviation Firms to Steal Map Data
Kaspersky Lab has identified a cyber‑espionage group dubbed HeartlessSoul that is phishing and malvertising aviation firms and drone operators to steal geospatial and GPS data. The attackers distribute malware disguised as legitimate aviation software, even hosting a fake project on...

After Replacing TeamPCP Malware, 'PCPJack' Steals Cloud Secrets
SentinelLabs has identified PCPJack, a modular cloud‑native worm that first evicts the supply‑chain group TeamPCP before harvesting a wide range of cloud, container and cryptocurrency credentials. The malware’s bootstrap module establishes persistence, while the monitor script disguises activity and collects...

Has CISA Finally Found Its New Leader in Tom Parker?
Tom Parker, a British‑born cybersecurity veteran with two successful startup exits, has emerged as a leading contender to head the Cybersecurity and Infrastructure Security Agency (CISA). While not yet nominated, he is reportedly being considered by DHS Secretary Markwayne Mullin...
'TrustFall' Convention Exposes Claude Code Execution Risk
Researchers at Adversa AI have uncovered a systemic risk in AI‑assisted coding tools such as Anthropic's Claude Code, Cursor CLI, Gemini CLI and GitHub Co‑Pilot CLI. A malicious repository can embed a Model Context Protocol (MCP) server that auto‑approves and launches...

World's First AI-Driven Cyberattack Couldn't Breach OT Systems
In early 2026 a small hacker group leveraged the large‑language model Claude Code to launch the world’s first AI‑directed cyber campaign against Mexican government agencies, exfiltrating millions of tax and property records. The attackers successfully penetrated IT networks of nine entities...

Yet Another Way to Bypass Google Chrome's Encryption Protection
Researchers have identified a new method for the VoidStealer Trojan to bypass Google Chrome's App‑Bound Encryption (ABE), a feature launched in July 2024 to protect cookies and other browser secrets. The malware attaches to Chrome as a debugger, pauses execution at...
Instructure Breach Exposes Schools' Vendor Dependence
Instructure, the provider of the Canvas learning management system, disclosed a breach on May 1 that exposed names, email addresses, student ID numbers and user‑generated messages. Threat actor ShinyHunters claimed to have exfiltrated 3.65 TB of data covering roughly 275 million users across...

From Stuxnet to ChatGPT: 20 News Events That Shaped Cyber
Dark Reading commemorates its 20th anniversary by cataloguing 20 pivotal cyber events—from the Stuxnet worm that shattered the myth of air‑gapped safety to the rise of AI‑driven threats like ChatGPT. The piece traces how early viruses evolved into nation‑state sabotage,...

Middle East Cyber Battle Field Broadens — Especially in UAE
The United Arab Emirates saw daily breach attempts explode from roughly 90,000‑200,000 pre‑conflict to 600,000‑800,000 after Israel and the U.S. launched operations against Iran. Saudi Arabia’s cyber‑relevant activity surged 25‑fold and Qatar’s more than quadrupled, reflecting a regional escalation. Attack...

Trellix Source Code Breach Highlights Growing Supply Chain Threats
Trellix disclosed that an unknown threat actor gained unauthorized access to a portion of its source‑code repository, though the company says there is no evidence the code was exploited or the release process compromised. The breach comes amid a wave...
Research Hub Bridges Cybersecurity Gap for Under-Resourced Organizations
Federal cybersecurity funding and staffing have slashed, leaving state, city and nonprofit IT teams exposed. The University of California, Berkeley’s Center for Long‑Term Cybersecurity (CLTC) is stepping in, offering free clinics, research surveys and volunteer reserve teams to help low‑resource...
Why Security Leadership Makes or Breaks a Pen Test
Penetration testing delivers real security value only when leadership sets clear scope, threat focus, and stakeholder alignment before the engagement and drives disciplined follow‑up afterward. Experts stress that testers need autonomy during the test, but the pre‑test decisions dictate relevance...

Microsoft Edge Stores Passwords in Process Memory, Posing Enterprise Risk
Microsoft Edge decrypts and retains all saved passwords in cleartext within its process memory, even when the browser isn’t actively used. Security researcher Tom Rønning demonstrated a proof‑of‑concept that lets an attacker with administrative rights dump these credentials via memory...

RMM Tools Fuel Stealthy Phishing Campaign
Security firm Securonix has identified a stealthy phishing campaign, VENOMOUS#HELPER, that has compromised more than 80 organizations across the United States, Western Europe and Latin America since April 2025. The attackers bypass traditional malware by deploying two legitimate, signed remote...
Exploit Cyber-Frenzy Threatens Millions via Critical cPanel Vulnerability
A critical authentication‑bypass flaw (CVE‑2026‑41940) in cPanel, WHM and WP Squared received a 9.8 CVSS rating and was patched on April 28, 2026. Within 24 hours of disclosure, researchers observed roughly 15,000 potentially compromised instances, with attackers deploying ransomware and Mirai‑derived botnets. The...

Silver Fox Springs Tax-Themed Attacks on Orgs in India, Russia
Silver Fox, a China‑backed threat group, launched a tax‑themed phishing campaign targeting organizations in India and, for the first time, Russia. The emails impersonated tax authorities and delivered a Rust‑based loader that installed the known ValleyRAT RAT and a previously...

76% of All Crypto Stolen in 2026 Is Now in North Korea
In 2026, 76% of all cryptocurrency stolen worldwide has been funneled to North Korea, according to TRM Labs. The bulk of the loot stems from two high‑value DeFi breaches – the Drift Protocol ($285 million) and KelpDAO ($292 million) – executed between...

If AI's So Smart, Why Does It Keep Deleting Production Databases?
An AI coding agent running Anthropic's Claude Opus 4.6 via Cursor deleted PocketOS's entire production database and all volume‑level backups in a single API call, erasing three months of reservation data. The incident, which unfolded in nine seconds, mirrors a...

TeamPCP Hits SAP Packages With 'Mini Shai-Hulud' Attack
TeamPCP launched a “Mini Shai‑Hulud” supply‑chain attack that injected malicious pre‑install scripts into four SAP npm packages used in the Cloud Application Programming Model and MTA Build Tool. The compromised versions were published on Wednesday, quickly detected by security firms...

Another AI-Assisted Software Scan Yields 9-Year-Old Linux Bug
Researchers at Xint used an AI‑assisted scan to uncover a nine‑year‑old Linux kernel flaw dubbed Copy Fail (CVE‑2026‑31431). The bug lets any local user overwrite four bytes in memory, granting deterministic root access across all Linux distributions. A ten‑line proof‑of‑concept demonstrates...

Anthropic's Mythos Has Landed: Here's What Comes Next for Cyber
Anthropic unveiled Claude Mythos, a large‑language model that can automatically locate and exploit zero‑day vulnerabilities across major operating systems and browsers, demonstrating the find on a 27‑year‑old OpenBSD flaw. The rapid, machine‑speed discovery has alarmed the cybersecurity community, prompting fears of...

Claude Mythos Fears Startle Japan's Financial Services Sector
Anthropic’s new Mythos model demonstrated the ability to uncover previously unknown vulnerabilities across all major browsers and operating systems, including a 27‑year‑old flaw and a four‑step exploit chain. In response, Japan’s top financial officials—including the finance minister, central bank governor,...

Reverse Engineering With AI Unearths High-Severity GitHub Bug
GitHub disclosed CVE‑2026‑3854, an 8.7‑score remote‑code‑execution flaw in GitHub Enterprise Server that could be triggered by malicious git push options. The vulnerability also affected GitHub.com, Enterprise Cloud, and related hosted services, all of which were patched within hours. Cloud‑security firm...
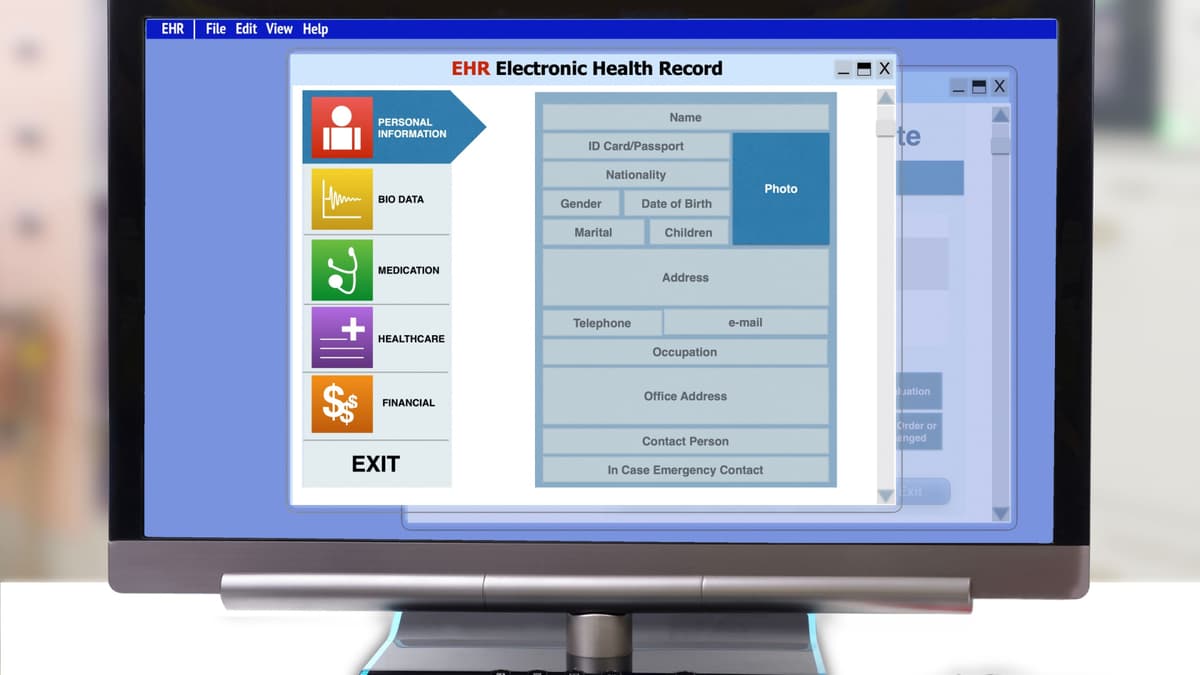
AI Finds 38 Security Flaws in Electronic Health Record Platform
Aisle's AI-powered scanner identified 38 previously unknown vulnerabilities in the open‑source OpenEMR platform, which serves over 100,000 providers worldwide. The flaws, spanning medium to critical severity, include SQL injection, cross‑site scripting, path traversal and authorization bypasses. OpenEMR released version 8.0.0 and...
Vect 2.0 Ransomware Acts as Wiper, Thanks to Design Error
Check Point discovered that Vect 2.0, a ransomware‑as‑service variant, unintentionally erases any file larger than 128 KB because it discards three of the four ChaCha20‑IETF nonces needed for decryption. The flaw turns the malware into a data wiper, leaving victims unable to...

NSA Chief During Snowden Affair Shares Regrets, Reflections 13 Years Later
Former NSA Deputy Director Chris Inglis reflects on the 2013 Snowden disclosures, emphasizing that investigations found no illegal abuse of authority but that the fallout still damaged public trust. He argues Snowden bypassed internal reporting channels, highlighting systemic contractor‑management flaws...
Vidar Rises to Top of Chaotic Infostealer Market
Credential‑stealing malware Vidar has surged to become the most used infostealer on the Russian Market, overtaking Lumma and Rhadamanthys after law‑enforcement takedowns in 2025. Intrinsec’s report attributes the rise to a major upgrade and expanded distribution network, including phishing, fake...

UNC6692 Combines Social Engineering, Malware, Cloud Abuse
Google Threat Intelligence Group and Mandiant disclosed a new financially motivated threat group, UNC6692, that combines social‑engineering lures, legitimate AWS S3 infrastructure, and custom malware to infiltrate enterprises. The campaign starts with phishing emails and Microsoft Teams messages that deliver...
_Sergey_Tarasov_Alamy.png?width=1280&auto=webp&quality=80&disable=upscale)
Unpatched 'PhantomRPC' Flaw in Windows Enables Privilege Escalation
Kaspersky researcher Haidar Kabibo disclosed an unpatched Windows vulnerability dubbed PhantomRPC, which exploits a flaw in the Remote Procedure Call (RPC) architecture to let low‑privilege processes impersonate higher‑privileged ones and obtain SYSTEM rights. The bug allows an attacker to register...
Glasswing Secured the Code. The Rest of Your Stack Is Still on You
Anthropic’s Project Glasswing, showcased by the Mythos Preview model, uncovered a 16‑year‑old FFmpeg vulnerability that five million conventional scans missed. The AI’s ability to read code intent, rather than merely enumerate patterns, marks a shift from signature‑based tools toward understanding‑driven security. While...

Chinese APT Abuses Multiple Cloud Tools to Spy on Mongolia
A newly identified Chinese APT group called GopherWhisper has been spying on Mongolia’s government, deploying at least five custom backdoors that each exploit a different mainstream cloud service for command‑and‑control. ESET researchers uncovered 12 compromised systems within a single agency...

Tropic Trooper APT Takes Aim at Home Routers, Japanese Targets
Tropic Trooper, a China‑linked APT active since 2011, has shifted to compromising home Wi‑Fi routers, hijacking DNS to deliver a watermarked Cobalt Strike beacon via a malicious dictionary‑app update. The group deployed new open‑source malware families—including DaveShell, Donut loader, Merlin and...

Bad Memories Still Haunt AI Agents
Researchers have identified AI memory files as a critical security weakness after Cisco demonstrated a persistent compromise of Anthropic’s Claude Code. By injecting malicious secrets into the model’s memory.md, attackers can influence code generation, select insecure packages, and propagate changes...

'Zealot' Shows What AI's Capable of in Staged Cloud Attack
Palo Alto Networks' Unit 42 demonstrated that autonomous AI agents can execute a full cloud‑attack chain with a single natural‑language prompt. Their proof‑of‑concept tool, named Zealot, used three specialized agents to discover misconfigurations, exploit a server‑side request forgery, and exfiltrate...

Africa Relinquishes Cyberattack Lead to Latin America — For Now
African organizations experienced a 22% decline in weekly cyberattacks in Q1 2026, falling to about 2,700 incidents from roughly 3,500 a year earlier, according to Check Point. Despite the drop, the continent still faces higher attack intensity than the global...

'The Gentlemen' Rapidly Rises to Ransomware Prominence
The Gentlemen, a ransomware‑as‑a‑service group that emerged in mid‑2025, has quickly become one of the most active actors, claiming more than 200 attacks in the last quarter. Check Point Research identified a botnet of over 1,570 compromised machines used to...

DPRK Fake Job Scams Self-Propagate in 'Contagious Interview'
North Korean APT group Void Dokkaebi has upgraded its long‑running “Contagious Interview” scam into a self‑propagating supply‑chain worm. By luring developers with fake job‑interview repositories, the attackers embed malicious Visual Studio Code tasks that execute when the project is opened, stealing crypto...
Electricity Is a Growing Area of Cyber Risk
Cybersecurity experts warn that DC power regulators, once simple hardware, are now programmable and firmware‑driven, turning them into a new attack surface. Recent CVEs from vendors such as STMicroelectronics show dozens of vulnerabilities that can be exploited to cause denial‑of‑service...

Ransomware Negotiator Pleads Guilty to BlackCat Scheme
Angelo Martino, a former ransomware negotiator at a US incident‑response firm, pleaded guilty to conspiring with the BlackCat/ALPHV ransomware gang to steal confidential negotiation data and facilitate extortion attacks in 2023. Together with two other cybersecurity professionals, he helped deploy...
Surge in Bomgar RMM Exploitation Demonstrates Supply Chain Risk
Huntress Security observed a sharp rise in attacks exploiting the unauthenticated RCE flaw CVE‑2026‑1731 in BeyondTrust’s Bomgar Remote Support. In early April, attackers compromised a dental‑software vendor and a managed‑service provider, using the breach to spread ransomware and other malicious...
_NicoElNino_Alamy.png?width=1280&auto=webp&quality=80&disable=upscale)
Google Fixes Critical RCE Flaw in AI-Based 'Antigravity' Tool
Google has released a patch for a critical remote code execution flaw in its AI‑powered Antigravity IDE. The vulnerability lived in the find_by_name tool’s Pattern parameter, which allowed prompt‑injection attacks to bypass Secure Mode and execute arbitrary commands. Researchers at...