
Span Cyber Security Arena 2026: Only 10 Days Left to Secure Early Bird Tickets
Span Cyber Security Arena 2026 will be held May 20‑22 in Poreč, Croatia, at the five‑star Pical Resort. The event features three days of conference sessions plus two pre‑conference masterclasses on May 18‑19 for engineers, architects, and consultants. Keynote speakers include BBC cyber‑security reporter Joe Tidy, Windows security expert Sami Laiho, and Trace Labs founder Robert Sell, who will discuss OSINT, social engineering, and insider threats. Early‑bird tickets are available until February 13, after which regular pricing applies.

Open-Source AI Pentesting Tools Are Getting Uncomfortably Good
Open‑source AI pentesting tools are reaching production‑grade performance, with BugTrace‑AI, Shannon, and the Cybersecurity AI Framework (CAI) each demonstrating distinct strengths in a lab test. BugTrace‑AI acts as a low‑noise reconnaissance assistant, flagging likely flaws without launching exploits. Shannon takes...

Where NSA Zero Trust Guidance Aligns with Enterprise Reality
The NSA released Phase One and Phase Two of its Zero Trust Implementation Guidelines, outlining 36 and 41 activities respectively to achieve 30 and 34 distinct capabilities. The guidance builds on earlier Primer and Discovery Phase documents and aligns with...

Pompelmi: Open-Source Secure File Upload Scanning for Node.js
Pompelmi is an open‑source toolkit that adds inline malware scanning to Node.js file‑upload handlers. It inspects files in memory, applying configurable policies on extensions, size, MIME types, and archive contents before any data reaches storage. The library offers pluggable scanning...

What Boards Need to Hear About Cyber Risk, and What They Don’t
Entrust CIO Rishi Kaushal explains how security leaders should brief corporate boards on cyber risk, linking cryptography, certificates, and authentication to tangible business outcomes such as revenue loss, outages, fraud, and regulatory exposure. He demystifies the digital‑trust layer, arguing that...

AI Is Flooding IAM Systems with New Identities
The Cloud Security Alliance reports that AI‑generated identities are being treated like traditional non‑human accounts, exposing them to the same IAM weaknesses such as credential sprawl and unclear ownership. AI systems create and retire identities at unprecedented speed, overwhelming legacy...
Microsoft Sets New Timeline for Sentinel Transition to Defender Portal
Microsoft has postponed the migration of Microsoft Sentinel from the Azure portal to the Microsoft Defender portal, setting a new sunset date of March 31 2027—about nine months later than originally planned. The shift responds to extensive customer and partner feedback requesting...

Arkose Titan Aims to Make Bot, Scraping, and AI Fraud Economically Unviable
Arkose Labs unveiled Arkose Titan, a unified platform that defends against both human‑driven and AI‑powered fraud, scraping, and bot attacks. The solution consolidates bot detection, device and email intelligence, API security, behavioral biometrics, and phishing protection into a single API...
EFF Calls Out Major Tech Companies on Encryption Promises
The Electronic Frontier Foundation (EFF) has launched the "Encrypt It Already" campaign, urging major tech firms to fulfill announced end‑to‑end encryption promises, enable encryption by default, and broaden encrypted storage. The initiative groups demands into three categories—Keep your promises, Defaults...
Apple’s New Privacy Feature Limits How Precisely Carriers Track Your Location
Apple introduced a new privacy setting called Limit Precise Location in iOS 26.3, which reduces the granularity of location data shared with cellular networks. When enabled, carriers can only determine a user’s approximate neighborhood rather than the exact address, while app‑level...

Wearable Tech Adoption Continues as Privacy Worries Grow
Over one billion people now wear fitness trackers that continuously collect health metrics, creating a massive stream of sensitive personal data. A recent Clutch survey shows 74% of users are worried about how this data is handled, while only 58%...

Virtue AI AgentSuite Enables Enterprises to Test and Secure AI Agents
Virtue AI has launched AgentSuite, a multi‑layer security and compliance platform designed for enterprise AI agents. The solution lets organizations test agents, enforce real‑time guardrails, and control tool access while providing full audit trails. IBM research shows 79% of enterprises...

Druva Threat Watch Offers Continuous Threat Monitoring of Backup Data
Druva launches Threat Watch, a zero‑touch, cloud‑native solution that continuously scans backup snapshots for dormant threats and indicators of compromise. The service runs inside Druva’s Data Security Cloud, eliminating the need for extra hardware or agents and delivering near‑real‑time detection...

Conditional Access Enforcement Change Coming to Microsoft Entra
Microsoft announced that starting March 27 2026, Conditional Access policies in Microsoft Entra will be enforced during sign‑ins even when resource exclusions are configured, with a phased rollout through June 2026. The change specifically targets sign‑ins from client applications that request only OIDC...

N-Able Brings AI to Endpoint, Security, and Recovery
N‑able unveiled AI‑enhanced capabilities across its endpoint management, security operations, and data‑protection suite. Leveraging telemetry from over 11 million managed devices and a network of 25,000+ service providers, the company now offers agentic AI that automates scripting, threat detection, and recovery...

Tosi Platform Delivers Unified Connectivity, Visibility, and Security for OT at Scale
Tosi has launched a purpose‑built OT platform that consolidates connectivity, visibility, and security into a single console. The offering includes Tosi Control for fleet management and real‑time status, with Tosi Insight adding traffic analytics and anomaly detection, and a full...

Sumsub’s AI Agent Verification Binds Automation to Verified Human Identity
Sumsub has introduced AI Agent Verification, a new layer that ties AI‑driven automation to a verified human identity through its Know Your Agent framework. The solution detects automated activity, evaluates its risk, and triggers targeted liveness checks when needed, ensuring...

Cside VPN Detection Enables Control of VPN Traffic to Prevent Fraud and Legal Exposure
cside has launched VPN Detection, a solution that identifies and manages traffic routed through virtual private networks. Unlike traditional IP‑list methods, it analyzes network behavior, browser fingerprints, and packet timing across OSI layers three to seven. The tool aims to...

Google Agrees to Pay $135 Million over Android Data Harvesting Claims
Google has agreed to a $135 million settlement to resolve a class action alleging Android devices transmitted system‑service data over cellular networks without user consent. The lawsuit, spanning over five years, claimed background data transfers drained users’ plans starting in November...

A Practical Take on Cyber Resilience for CISOs
Standard Chartered CISO Shebani Baweja explains cyber resilience as an extension of information security focused on recovery, trust, and continuity during severe incidents. She highlights three priority areas: managing third‑party risk, preparing for emerging threats like AI‑driven attacks, and embedding...

ImmuniWeb Reports Double-Digit Growth and Platform Advances
ImmuniWeb reported an all‑time sales record for 2025, maintaining double‑digit year‑over‑year growth while staying profitable. The company rolled out four major AI Platform updates, adding AI‑specific testing for web, mobile, API, LLM vulnerabilities and post‑quantum encryption readiness. Independent ISO 9001 and...

OPNsense 26.1 Brings Updates to Open-Source Firewall Management
OPNsense released version 26.1, code‑named Witty Woodpecker, enhancing firewall management, traffic visibility, and automation interfaces. The update revamps the live firewall log, redesigns the firewall rules UI, and expands API coverage to include Source NAT tagging and Destination NAT port...

Veracode’s Platform Enhancements Help Prevent Software Supply Chain Attacks
Veracode unveiled a suite of platform enhancements for the second half of 2025, highlighted by the launch of Package Firewall, a preventive control that blocks malicious third‑party packages before they enter development environments. The feature integrates with major package managers...
N8n Adds Chat Hub to Centralize AI Access Inside Automation Workflows
n8n launched Chat Hub, a built‑in chat interface that lets users query large language models and trigger workflow agents without exposing workflow logic or credentials. The feature introduces a dedicated Chat role, centralizes model and credential management, and supports both...

McAfee Upgrades Scam Detector to Spot QR Code Scams and Suspicious Messages
McAfee has upgraded its Scam Detector tool to include instant QR‑code safety checks and enhanced detection of suspicious direct messages, even when they contain no links. The update comes as QR‑code scams affect 68 % of recent scanners, with 18 % encountering...

Cloudbrink Adds AI Innovations to Its Platform to Protect Agents, Apps, and Data
Cloudbrink announced new AI‑focused security features that extend its secure connectivity platform to protect AI agents, browser‑based AI services, and custom large language models. The enhancements include a Safe AI BrinkAgent that detects data leaks, a continuously updated definitions database...

Fortinet Expands FortiCNAPP with Network, Data, and Runtime-Aware Risk Prioritization
Fortinet has upgraded its FortiCNAPP platform to incorporate network enforcement, data security posture management, and runtime validation into a single risk‑prioritization workflow. The enhancements enable network‑aware risk scoring, in‑place data sensitivity analysis, and runtime‑informed prioritization, reducing alert fatigue and focusing...

Yubico Extends Hardware Passkey Deployment Options
Yubico has broadened its YubiKey as a Service offering by adding self‑service ordering and a revamped Customer Portal. The new workflow lets employees and partners select YubiKey models, enter shipping details, and receive keys directly in the U.S., Canada or...

Volante’s Multi-Cloud Resiliency Service Keeps Payments Running During Cloud Outages
Volante Technologies has introduced a Multi‑cloud Resiliency Service designed to keep payment processing operational when a primary cloud provider experiences an outage. The solution offers rapid, zero‑data‑loss failover to a secondary cloud environment, eliminating single‑provider dependency for banks and other...

Pondurance RansomSnare Blocks File Encryption and Data Exfiltration
Pondurance has added RansomSnare, a new module to its Managed Detection and Response (MDR) service that halts ransomware the moment it tries to encrypt a file. The capability terminates the malicious process instantly, blocking both encryption and data exfiltration without...
CERT UEFI Parser: Open-Source Tool Exposes UEFI Architecture to Uncover Vulnerabilities
The Software Engineering Institute at Carnegie Mellon University released the CERT UEFI Parser, an open‑source utility that statically parses UEFI firmware binaries and source code into a structured, machine‑readable model. By extracting modules, execution phases, protocols and dependencies, the tool gives...

Why Prevention-First Secrets Security Will Define Enterprise Scale: Learnings From a Leading Telecom
Orange Business discovered that traditional secret detection tools generate massive false positives, leading developers to ignore alerts. By implementing mandatory GitLab pre‑receive hooks and a three‑layer defense, they reduced new secret leaks by 80% while keeping false positives below 5%....

Grammarly and QuillBot Are Among Widely Used Chrome Extensions Facing Serious Privacy Questions
Incogni’s 2026 privacy risk report examined 442 AI‑powered Chrome extensions and found that over half collect user data, often with deep‑level permissions. The study highlighted that scripting and activeTab permissions let extensions read and modify any web page, exposing emails,...
Audits for AI Systems that Keep Changing
ETSI released TS 104 008, a continuous‑auditing based conformity assessment (CABCA) specification for AI systems. It shifts assurance from periodic reviews to ongoing cycles that automatically collect evidence from logs, model parameters, and data samples. The framework operationalizes regulatory requirements into machine‑readable...

Tenable One AI Exposure Delivers Unified Visibility and Governance Across AI, Cloud and SaaS
Tenable has made its Tenable One AI Exposure product generally available, extending the Tenable One Exposure Management Platform to provide unified visibility, discovery, and governance of AI assets across SaaS, cloud, APIs and on‑premises agents. The solution continuously identifies both...

NICE Actimize Insights Network Combats Fraudulent Transfers
NICE Actimize introduced the Actimize Insights Network, a real‑time intelligence platform that aggregates counterparty risk data across financial institutions. The network leverages the company’s fraud and financial‑crime expertise to deliver cross‑channel, millisecond‑level risk signals for authorized push‑payment scams, BEC and...

HackerOne Brings Agentic PTaaS to Continuous, Expert-Validated Pentesting
HackerOne has launched Agentic Pentest as a Service (Agentic PTaaS), a hybrid AI‑human offering that delivers continuous, real‑world exploit validation at enterprise scale. The solution pairs proprietary AI agents with a vetted community of elite pentesters to automate reconnaissance, exploitation and...

Microsoft Brings AI-Powered Investigations to Security Teams
Microsoft has made its Purview Data Security Investigations tool generally available, embedding generative AI to streamline breach, fraud, and content investigations across Microsoft 365. The solution pulls data from emails, Teams, documents, and Copilot, allowing natural‑language searches that group related artifacts...

AWS Adds IPv6 Support to IAM Identity Center Through Dual-Stack Endpoints
Amazon Web Services announced IPv6 support for its IAM Identity Center by introducing dual‑stack endpoints that accept both IPv4 and IPv6 traffic. The new URLs apply to user access portals, administrative APIs, and managed applications, while existing IPv4‑only endpoints continue...

NETSCOUT Adds Wi-Fi 7 Observability and Real-Time SSL Certificate Monitoring
NETSCOUT unveiled new nGeniusONE enhancements that add Wi‑Fi 7 deep packet inspection to its Edge Sensors and introduce real‑time SSL/TLS certificate monitoring. The Wi‑Fi 7 support, backward compatible with Wi‑Fi 6E/6/5, closes observability gaps in remote sites as the market is projected to...

Descope Introduces Dedicated Identity Infrastructure for AI Agents and MCP Ecosystems
Descope has launched an upgraded Agentic Identity Hub that treats AI agents as first‑class identities alongside human users. The platform adds OAuth 2.1, PKCE, DCR, CIMD and tool‑level scopes to MCP servers, letting developers secure agent access with enterprise‑grade policies. It...

When Open Science Meets Real-World Cybersecurity
Fermilab CISO Matthew Kwiatkowski explains how open‑science environments create cybersecurity blind spots when scientists design infrastructure without early security input. He notes that collaboration between IT and researchers reduces risky implementations and that publicly releasable data is often mislabeled, prompting...

Waiting for AI Superintelligence? Don’t Hold Your Breath
AI superintelligence remains a theoretical goal, yet artificial intelligence is already woven into the fabric of enterprise operations, accelerating decision‑making and threat detection. Companies report faster, more accurate alert investigations, but the same speed introduces novel vulnerabilities and operational risks....

Cybersecurity Jobs Available Right Now: January 27, 2026
A wave of cybersecurity openings posted on January 27, 2026 spans senior leadership, engineering, and analyst roles across the United States, Europe, Asia, and the Middle East. Companies such as micro1, Bringg, Oracle, and Snyk are hiring C‑level executives, incident‑response...

Ivanti Expands Neurons Platform with Agentic AI and Autonomous Endpoint Management
Ivanti announced a major upgrade to its Neurons platform, adding Agentic AI‑driven personas to the IT Service Management suite, autonomous endpoint management (AEM) that unifies DEX, UEM and security, and enhanced asset visibility through Discovery. The Agentic AI preview launches...

Upwind Secures $250 Million to Expand Runtime-First Cloud Security for AI Workloads
Upwind announced a $250 million Series B round, bringing total capital to $430 million. The funding, led by Bessemer Venture Partners with participation from Salesforce Ventures and Picture Capital, will accelerate the company’s runtime‑first cloud security platform aimed at AI‑driven workloads. Upwind claims...

Booz Allen’s Vellox Reverser Accelerates Malware Analysis and Threat Intelligence
Booz Allen Hamilton has launched the general availability of Vellox Reverser, an AI‑driven malware reverse‑engineering platform. The solution leverages a resilient agentic AI architecture on AWS Lambda, Bedrock, and Step Functions to automate deep analysis of complex threats. New features...

Stellar Cyber Expands Autonomous SOC Capabilities with Agentic AI
Stellar Cyber unveiled version 6.3, embedding agentic AI to push its Autonomous SOC vision forward. The update automates threat detection, investigation, triage and response across identity, network, endpoint, email and cloud layers, slashing alert fatigue and mean‑time‑to‑respond. New Model Context Protocol...

Quantum Computing Firm IonQ Acquires US Semiconductor Firm SkyWater for $1.8 Billion
IonQ announced a definitive agreement to acquire SkyWater Technology for $35 per share, valuing the semiconductor foundry at roughly $1.8 billion in a cash‑and‑stock transaction. The deal creates a vertically integrated quantum platform that combines IonQ’s fault‑tolerant quantum processors with SkyWater’s...
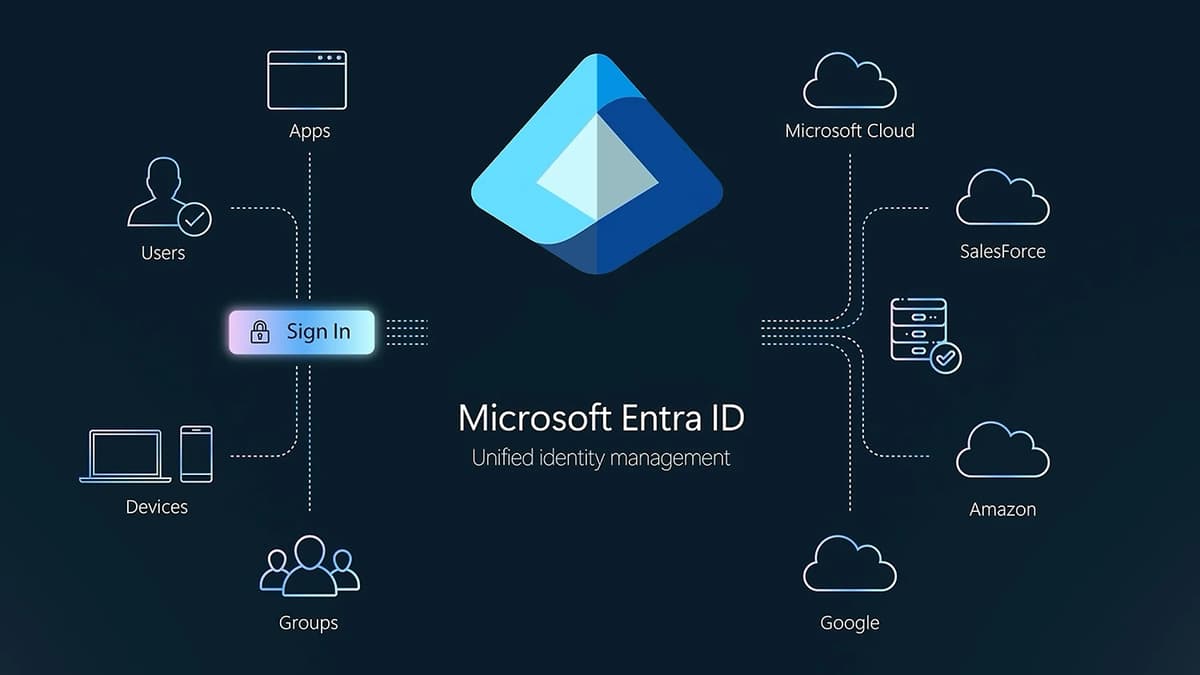
Microsoft Entra ID Will Auto-Enable Passkey Profiles, Synced Passkeys
Microsoft Entra ID will automatically enable passkey profiles and add synced passkey support starting March 2026. The update moves passkey profiles to general availability and introduces a new passkeyType property that lets admins choose device‑bound, synced, or both types of passkeys....