
35,000 Users Targeted in Phishing Campaign in Just Two Days
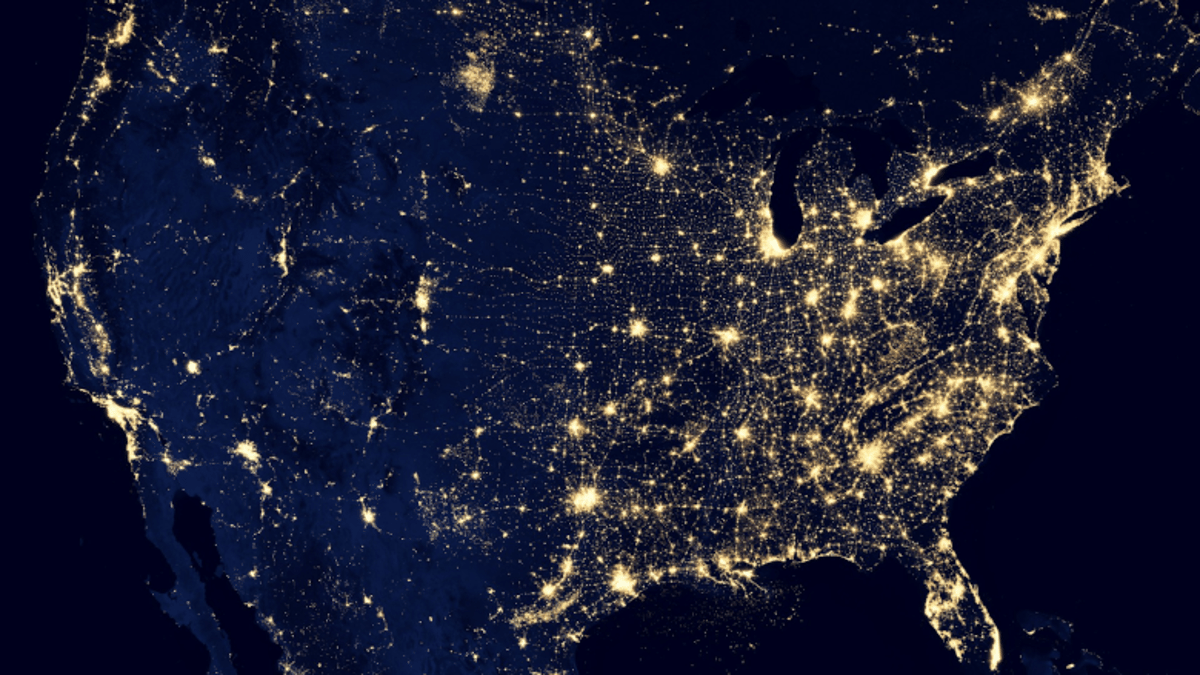
Between April 14 and 16, a sophisticated phishing operation hit more than 35,000 users across 13,000 organizations in 26 countries, with 92% of victims located in the United States. The campaign masqueraded as compliance‑related communications, using organization‑specific details and encrypted‑looking attachments to lure recipients. Targeted sectors included healthcare, financial services, professional services, and technology, reflecting attackers’ focus on high‑value data. Security leaders warn that AI‑generated content is sharpening the realism of such attacks, turning phishing into a behavioral and identity‑centric threat.

Exclusive: What the Celebrity Stalkerware Breach Means for Executive Protection
Cybersecurity researcher Jeremiah Fowler uncovered a publicly accessible database containing 86,859 screenshots taken from a celebrity’s device, exposing personal communications, invoices, and identification data. The leak appears tied to stalkerware used by an individual targeting a European entrepreneur‑media figure, and...

The Coming Wave of Large-Scale Al-Enabled Cyberattacks
Artificial intelligence is reshaping cyber offense as quickly as it empowers defenders, giving attackers tools to automate phishing, deep‑fakes, and large‑scale reconnaissance. Experts warn that the first truly massive AI‑enabled cyberattack will likely be a coordinated, machine‑speed campaign targeting multiple...

The Browser Blind Spot Your Privacy Program Is Missing
Privacy programs have matured with data mapping, consent platforms, and vendor risk assessments, yet they overlook a critical exposure point: the web browser. Third‑party JavaScript runs on 92% of sites, capturing keystrokes, form inputs, and navigation data before any server‑side...
New Research: AI-Driven Cybercrime Led to a 389% Increase in Ransomware Victims
FortiGuard Labs' 2026 Global Threat Landscape Report reveals AI‑driven cybercrime has propelled ransomware victims up 389% year‑over‑year. While brute‑force attempts fell 22% due to more precise targeting, exploitation attempts rose 25.5%, indicating attackers are leveraging AI tools such as FraudGPT,...
Ransomware Responsible for 90% of Manufacturing Cyber Losses
New claims analysis shows ransomware accounts for 90% of financial losses in manufacturing, even though it represents only 12% of incident volume. Phishing and transfer fraud make up 30% of claims, while MFA misconfigurations cause 26% of total losses. The...

Less Than 10% of Higher Education Has No Intention of Adopting AI
Ellucian’s latest AI survey shows that two‑thirds of U.S. higher‑education institutions now use artificial intelligence, up from 49% a year ago, while only 7% have no intention to adopt it. Eighty‑eight percent expect AI usage to rise over the next...
What the Medtronic Breach Means for Security Experts
Medtronic confirmed a breach of its corporate IT systems, with hacker group ShinyHunters taking credit. The company said the intrusion did not affect manufacturing, product distribution, financial reporting, patient safety, or its ability to meet patient needs. Security experts highlighted...

Why Energy Infrastructure Is Cybersecurity’s Next Frontier
The energy sector’s rapid shift toward electrification, renewables, and digital grid modernization is dramatically expanding its cyber‑attack surface. Traditional, perimeter‑based security models are being replaced by a sprawling network of distributed assets—solar inverters, smart meters, storage units, and IoT sensors—that...

What Claude and OpenClaw Vulnerabilities Reveal About AI Agents
Security researchers at Oasis disclosed two critical vulnerability chains affecting Anthropic's Claude and the open‑source OpenClaw AI agents. In both cases a single manipulated input—whether a crafted search‑ad link or a malicious website—allowed an attacker to hijack the agent and...

Security Leaders Discuss the Claude Mythos Breach
Security leaders reacted to reports that Anthropic’s Claude Mythos AI model was accessed without authorization. The breach stemmed from a simple credential guess and a third‑party vendor path, exposing weaknesses in supply‑chain and perimeter controls. Experts warn that AI models are...
Operationally Ineffective: Putting CVEs in a Chokehold with Privilege Disruption
The Mythos Preview leverages AI to accelerate vulnerability discovery, turning roughly 33,000 privilege‑path dependent CVEs from dormant assets into cheap, weaponizable exploits—estimated at about $2,000 per attack. These CVEs, which account for 70% of confirmed weaponized flaws, undermine traditional patch‑and‑remediate...

How Should Effective AI Red Teams Operate?
Enterprises are rapidly deploying large language models into critical workflows, but traditional security testing fails to capture AI‑specific vulnerabilities. Dr. Peter Garraghan explains that AI red teaming must go beyond simple prompt refusal tests, emulating real adversaries and probing iterative...
The Security Metric That’s Failing You
Security teams have let patch‑rate metrics become the de‑facto strategy, but clean patch reports hide far greater risks such as misconfigurations, stale permissions, and legacy network segments. The window for exploiting a disclosed vulnerability has collapsed from weeks to roughly...
US Security Agency Leverages Claude Mythos Despite Pentagon Blacklist
The National Security Agency has begun using Anthropic’s new Claude Mythos Preview model despite a Pentagon‑issued supply‑chain risk designation on the company. Mythos, announced on April 7, is a general‑purpose LLM tuned for cyber‑exploit identification and is currently being rolled out under the...

Vercel Breach Originated From an Employee’s AI Tool
Vercel confirmed a data breach after an employee used the consumer AI service Context.ai with corporate credentials. The tool gave attackers access to the employee’s Google Workspace account, which they leveraged to enter limited Vercel internal environments. The company says...
58% of Organizations Spend Over 10 Hours a Month Securing AI-Generated Code
A Cloudsmith report reveals that 58% of organizations devote more than ten hours each month to validating and securing AI‑generated code, with 8% spending over forty hours. The study also shows 44% of respondents have suffered security incidents linked to...
Top 3 Cyber Insurance Incident Claims
Cowbell’s 2026 Claims Report shows data breaches (33.5%), cybercrime (31.8%) and extortion (18.3%) dominate cyber‑insurance claims. Meanwhile, AM Best notes U.S. cyber premiums slipped to $9.14 B while claim frequency jumped 40%, signaling a loss‑heavy environment despite lower premium volume. Industry experts...
What Are Security Experts Saying About OpenAI’s GPT-5.4-Cyber?
OpenAI has launched GPT‑5.4‑Cyber, a defensive‑oriented AI model, and is scaling its Trusted Access for Cyber (TAC) program to thousands of verified individual defenders and hundreds of critical‑infrastructure groups. Unlike Anthropic’s Claude Mythos, which remains limited to a handful of...

What “The Pitt” Gets Right About Ransomware and What Hospitals Can’t Afford to Ignore
The TV drama *The Pitt* dramatizes a ransomware attack that mirrors real‑world hospital incidents, showing how systems can be restored while operational chaos persists. The piece highlights that credential abuse accounts for 22% of healthcare breaches, leading to prolonged downtime,...

Democratized Software, Democratized Risk: Who’s Accountable When Everyone Codes?
AI‑driven coding tools are letting non‑technical teams create software without traditional developer resources, accelerating delivery and cutting costs. However, this democratization creates governance gaps that can expose organizations to security, compliance, and accountability risks. The article advises IT leaders to...

Venice Hydraulic Pump System Hacked, Hackers Claim Power to Create Floods
A hacker group identifying as “Infrastructure Destruction Squad” or “Dark Engine” claims to have breached Venice’s hydraulic pump system that protects Piazza San Marco, asserting it can open floodgates. The group says it stole administrative credentials for the flood‑risk management...

Pro-Iranian Actor Claims L.A. Metro Cyberattack
Last month, Los Angeles Metro shut down portions of its network after detecting a cyber intrusion, and it is still working to restore services. Intelligence from Dataminr attributes the attack to a pro‑Iranian hacktivist group called Ababil of Minab, which...

3 Quantum Realities to Confront This World Quantum Day
World Quantum Day highlighted the accelerating timeline toward a post‑quantum future, with industry leaders warning that waiting for certainty will delay critical migration. Experts emphasized that the operational risk lies in how long it takes to identify dependencies, prioritize remediation,...

Top Secret Clearance Holder Charged With Leaking Classified National Defense Information
The FBI arrested Courtney Williams, a former Special Military Unit member with a Top Secret/Sensitive Compartmented Information clearance, and charged her with leaking classified national‑defense information. Prosecutors allege that between 2022 and 2025 she provided secret data to a journalist via 10 hours...

Ransomware Response: How Businesses Regain Control Under Pressure
Ransomware attacks now hinge on speed, forcing executives to make high‑stakes decisions within hours. The article outlines how the crisis expands from a technical breach to an enterprise‑wide challenge involving legal, financial, and reputational risks. It stresses that pre‑emptive controls—isolated...

Breach of FBI Surveillance System Considered a “Major Incident,” Security Experts Weigh In
The FBI confirmed a breach of its Digital Collection System Network (DCSNet), labeling it a “major incident” under the Federal Information Security Modernization Act. Attackers accessed the system through a compromised vendor ISP, bypassing the agency’s own defenses. Federal officials...

10 Data Security Stories to Know About (March 2026)
March 2026 saw a wave of data‑security incidents spanning municipal ransomware, high‑profile corporate breaches, and controversial law‑enforcement data purchases. A ransomware attack forced Foster City, California to declare a state of emergency, while a Verizon‑authorized retailer exposed over 6.3 million customer...

Breaking Down “The Mosaic Effect”
Artificial intelligence is accelerating the "mosaic effect," where separate, permissible data points are combined to reveal sensitive insights. The effect, originally noted in intelligence work, now emerges in seconds as AI correlates thousands of low‑risk records, threatening compliance in regulated...

The AI Efficacy Asymmetry Problem
Over the past 18 months AI labs have released protocols and models—Anthropic’s Model Context Protocol and Claude Opus 4.6—that let large language models interact directly with browsers, APIs and command‑line tools, turning them into autonomous agents. Both attackers and defenders have integrated...

3.7M Records Exposed, Many Belonging to Sears Home Services
Cybersecurity researcher Jeremiah Fowler uncovered three publicly exposed databases containing 3.7 million records tied to Sears Home Services' AI virtual assistant. The leak includes audio recordings, call transcriptions, and chat logs, revealing names, contact details, service information, and extended recordings up...

Taming the Threat Beast: Building a Threat-Led Cybersecurity Program
A threat‑led cybersecurity program shifts focus from sheer data volume to relevance, enabling organizations to prioritize the threats that truly affect their business. The piece cites a Google Cloud study showing 61 % of security professionals feel overwhelmed by threat feeds...

8M Confidential Crime Tips Hacked, Compromised
A hacker group calling itself Internet Yiff Machine says it breached P3 Global Intel, a tip‑intelligence platform owned by Navigate360, exposing over eight million confidential crime tips—about 93 GB of data. The leaked dataset reportedly contains plaintext records, contradicting P3’s claims...

Threat Actors Target the Entire Retail Supply Chain
Black Kite’s 2026 report warns that threat actors now view wholesalers and retailers as a single, highly interconnected organization, exposing the entire retail supply chain to systemic cyber risk. Over 70% of major retailers, nearly 60% of wholesalers, and more...

GuardDog Telehealth Accesses Sensitive Medical Records Under False Pretenses
GuardDog Telehealth admitted to accessing patient medical records under false pretenses, claiming treatment needs while actually selling the data to law firms. The lawsuit, supported by Epic and Health Gorilla, alleges the use of sham providers to request records from...

Fear of Surveillance Leads to Increased VPN Use
A new PasswordManager survey shows that 36% of U.S. adults now use virtual private networks, making VPNs mainstream. Privacy concerns dominate, with 35% of users seeking to hide activity from the government and 65% aiming to block advertiser tracking. A...

Document Protection: Why Hybrid Storage Is the Future of Security
Companies are increasingly leveraging AI, which boosts productivity but also escalates sophisticated cyber threats. Digital document storage provides speed and collaboration, yet its exposure to breaches forces a security rethink. Experts recommend a hybrid model that keeps regularly accessed files...

Cracking Cyber’s Talent Gap Challenge
Rob Lee argues that the cybersecurity talent gap is less about a lack of candidates and more about outdated hiring practices and misaligned role definitions. Companies often demand senior experience for junior positions and narrow technical criteria, sidelining adaptable talent...

AI Security and Forensic Accounting: Protecting Financial Systems in an Automated World
Artificial intelligence is reshaping both security operations and financial processes, but the rapid automation of accounting, payments, and vendor management is expanding the attack surface for AI‑enabled fraud. Threat actors now use AI to craft convincing phishing attacks, impersonate executives,...
The Great Security Culture Shift: Building a Proactive Defense in an Era of Advanced Threats and Social Engineering
The article highlights a surge in DLL side‑loading attacks delivered through LinkedIn Messenger, where malicious PDFs bypass traditional endpoint defenses. It reveals that 66% of malware infections occur on devices already equipped with endpoint protection, exposing gaps in reactive security...

Would You Trust an AI Pentester to Work Solo?
Security leaders face mounting pressure to outpace threats while accelerating AI adoption, yet only 36% are satisfied with current pentesting providers. AI‑powered pentesting promises unprecedented speed and scale, scanning massive codebases in minutes, but it falls short on contextual judgment,...

Brian Harrell — Top Cybersecurity Leaders 2026
Brian Harrell, former DHS Assistant Secretary and current Chief Security Officer at Avangrid Energy, is highlighted as a top cybersecurity leader for 2026. He oversees a converged security portfolio that includes IT/OT cyber, physical security, privacy, fire protection, and business...

Dr. Bryan Stoker — Top Cybersecurity Leaders 2026
Dr. Bryan Stoker, a third‑degree Taekwondo black belt and former NSA senior leader, has become Chief Technology Officer at Dispersive Holdings. He spent over 40 years at the NSA and three years as USCYBERCOM J2 technical director, where he built...

Why Security Teams Can No Longer Ignore Recruitment Fraud
Recruitment fraud is emerging as a critical enterprise security threat, driven by AI‑powered social engineering that can convincingly impersonate recruiters and hiring workflows. Labor market volatility, highlighted by 1.17 million U.S. job cuts in 2025, has amplified the urgency and exposure...

4 Data Security Incidents to Know About (February 2026)
February 2026 saw four notable data security incidents. Inadequate redactions of the Jeffrey Epstein files exposed roughly 100 victims, including personal contacts and nude images. Updates to the 2024 Conduent breach revealed secondary leaks affecting customers such as Volvo Group North America...
Harvest Now, Decrypt Later: Preparing for the Quantum Hangover
Quantum‑era risk is no longer a distant theory; adversaries are already harvesting encrypted data to decrypt later when quantum computers mature. This "harvest‑now, decrypt‑later" model threatens long‑life information across government, finance, healthcare and private‑sector IP. CEOs must shift focus from...

How AI Could Impact Tax Season Security This Year
The IRS Criminal Investigation report shows tax‑related financial crimes hit $4.5 billion in FY 2025, a 111.8 % jump from the prior year, signaling heightened risk this tax season. Cybercriminals are leveraging generative AI to produce hyper‑personalized phishing, deepfake voice and video scams,...

AI-Generated Image-Based Harm Is Becoming a Security Issue — Organizations Must Prepare
AI‑generated image‑based harm is emerging as a fast‑moving security threat that targets students, employees and the public, causing immediate reputational and emotional damage. Existing moderation tools and legal frameworks struggle to keep pace with synthetic imagery that can be created...

Human-Related Security Risks Rose 90% in 2025
A KnowBe4 report reveals human‑related security incidents surged 90% in 2025, driven largely by social‑engineering attacks and employee error. Email‑based threats grew 57%, with 64% of organizations hit by external attacks exploiting staff inboxes. Human mistakes affected 90% of firms,...

41% of Organizations Have Hired a Fake Candidate
A GetReal Security survey reveals that 41 % of IT, cybersecurity, risk and fraud leaders admit their firms have hired and onboarded a fraudulent candidate, underscoring AI‑driven identity attacks’ real‑world impact. The same study shows 88 % of organizations encounter deep‑fake or...