
What Iran Is Learning From Russia’s War and Why the U.S. Should Be Concerned
The article argues that Iran is studying Russia’s four‑year war in Ukraine to extract lessons on military innovation, regime resilience, and security‑state expansion. It notes that Russian adaptations—especially in drone technology and electronic warfare—have been shared with Tehran, giving Iran real‑world data to refine its own weapons. The piece also highlights how Russia’s ability to endure sanctions and bolster internal security challenges the assumption that prolonged conflict will topple authoritarian regimes. Consequently, the United States may face a more capable and entrenched Iranian threat than current deterrence models anticipate.

Copy of Trump’s Cyber Strategy Is a Strong Playbook, but It’s All in the Execution
The White House released a new National Cyber Strategy that structures U.S. cyber policy into six pillars, ranging from offensive capabilities to workforce development. While the document names Russia and China as top adversaries and outlines modernizing steps like zero‑trust...

The Case for Reauthorizing Section 702
Section 702 of the Foreign Intelligence Surveillance Act, a post‑9/11 tool allowing warrant‑less collection of foreign nationals’ communications abroad, is up for reauthorization. NSA veteran Rob Joyce argues the authority is essential for disrupting cyberattacks, thwarting terrorist plots, and monitoring...

Why Australia Needs a National Spy Museum
Australia’s 2025 ASIO Threat Assessment warns of accelerating foreign interference, digital‑enabled domestic threats and a looming espionage surge to 2030. The Bondi Beach attack and ensuing Royal Commission have exposed gaps in public confidence and inter‑agency coordination. In response, the...

America’s AI Strategy Is Fighting the Last War
The article argues that Washington’s AI strategy is modeled on a Cold‑War race with China, emphasizing chip denial and massive AI spending, but it misreads the nature of artificial intelligence competition. China has closed the lead on frontier models to...

America’s Drone Strategy Has a Supply Chain Problem
The Pentagon’s Drone Dominance Program (DDP) seeks to field 30,000 UAVs in Phase I and scale to 150,000 by 2028, but the push for mass production collides with a fragile, NDAA‑compliant supply chain. War with Iran is accelerating demand, potentially exceeding...

Drones Are Changing Warfare And America Isn’t Ready
The United States is confronting a new threat: cheap, swarming drones that can overwhelm traditional air‑defense and missile‑defense systems such as THAAD and Patriot. While the Pentagon is pouring tens of billions of dollars into Counter‑UAS technologies, it is neglecting...

How the Iran War Is Reordering the World, Second and Third-Order Effects
The U.S.-Israeli war against Iran has quickly moved beyond battlefield strikes to generate sweeping second- and third-order effects. Closure of the Strait of Hormuz has cut roughly 20% of global oil flow, sending Brent crude above $120 and triggering stagflationary...

A Declining Demand for Strategic Intelligence? U.S. and Israeli Cases
The article argues that the United States and Israel are increasingly adopting preventive, compellence‑driven campaigns—such as strikes on Iran’s nuclear program and the capture of Venezuela’s Maduro—rather than relying on traditional deterrence. This shift elevates operational and targeting intelligence while...

New Presidential Executive Order Targets Transnational Cybercrime
In March 2026 President Trump signed an Executive Order targeting transnational cybercrime, directing the State, Treasury, War, Homeland Security and Justice departments to produce a coordinated action plan by July. Fraud losses have surged 430% since 2020, with AI‑driven scams...

Why a War in the Middle East Is Hitting Australians at the Petrol Pump
Escalating tensions between Iran and regional rivals are reverberating in Australia as oil markets tighten. Treasury modelling predicts the conflict could lift inflation by about 1.25 percentage points and shave roughly 0.6% off medium‑term GDP growth. Fuel prices may spike...

Why the ‘Day After’ Is The Most Important Day in the Iranian Conflict
The article argues that the day after any U.S. strike on Iran will be decisive because Iran’s theocratic regime, unlike Iraq or Libya, is rooted in ideology and a powerful Revolutionary Guard. The IRGC controls a substantial share of the...

Taking a Stand on Adversaries’ Influence in the Western Hemisphere
On January 3, the United States executed Operation Absolute Resolve, forcing Venezuelan President Nicolás Maduro from power and signaling a decisive push against adversarial influence in the Western Hemisphere. The move dovetails with the Trump‑era Shield of America coalition and a de‑facto...

Iran Exposed a New Reality for U.S. Air Power
Operation Epic Fury marked the first time in a generation that the United States had to fight for air superiority, taking four days to neutralize Iran's integrated air‑defense system (IADS). The campaign combined cyber and space attacks, electronic warfare, SEAD...

How Close the Iran War Came to a Nuclear Disaster
The Iran‑Israel conflict has spilled onto nuclear sites, with Iran’s missiles striking near Israel’s Dimona research center and multiple attacks on Iran’s Bushehr plant and Arak heavy‑water complex. While the Bushehr reactor remained operational and radiation levels stayed stable, the...

Telling China's Story Well: The PRC's Strategic Narrative as an Instrument of National Power
Since President Xi Jinping’s 2013 call to "tell China’s story well," the PRC has built a thirteen‑year strategic narrative program that treats discourse power as a core element of comprehensive national power. The effort is organized around four pillars—Party, Dream,...

The Chalk Mark Still Matters: Russian Espionage Handling in the Modern Era
The article outlines how Russian intelligence continues to rely on classic, low‑tech tradecraft—chalk marks, utility‑pole signals, and dead drops—while integrating modern encrypted communications. It details the RIS’s handling methods, from “tainiki” concealed containers to sophisticated surveillance detection routes used abroad....

Romania Pays the Cyber Price for Backing Ukraine. Where Is the EU?
Romania’s water agency, coal‑power producer and oil‑pipeline operator have suffered ransomware attacks linked to Russian‑aligned groups such as Qilin and Gentlemen, which the country’s top cyber official says are timed with its support for Ukraine. The EU possesses a cyber‑sanctions...

America’s Drone Future
The FAA forecasts that nearly two million drones will operate in U.S. airspace within a few years, yet state and local governments lack affordable, real‑time monitoring solutions. Federal proposals such as Part 108 and expanded JIATF‑401 authority aim to tighten counter‑UAS...

America Is Digitally Fragile — and Our Adversaries Know It
The opinion piece warns that America’s critical infrastructure has become digitally fragile, with adversaries like China embedding persistent footholds in water, energy, telecom and port systems. U.S. cyber strategy remains episodic and reactive, allowing hostile actors to pre‑position capabilities before...

Inside Trump’s Thinking on the Iran War
During a 33‑minute Fox News interview, former President Donald Trump claimed he could cripple Iran’s critical infrastructure within an hour but said the United States is deliberately holding back. He discussed monitoring alleged Iranian sleeper cells, dismissed unverified drone threats...

How GEOINT Can Sustain US Advantages in Africa
Geospatial intelligence (GEOINT) is emerging as a cost‑effective tool for the United States to maintain strategic advantage across Africa. Commercial remote‑sensing satellites now deliver frequent, high‑resolution imagery that monitors infrastructure, mineral extraction, and environmental stress without on‑the‑ground presence. The intelligence...

The Future of War Is Now: What Washington Needs to Hear From the Battlefield
Ukrainian drone operators have demonstrated that low‑cost autonomous systems can outpace NATO battalions, as shown in the Hedgehog wargame. Experts warn that current U.S. doctrine and training are obsolete in the face of rapid drone innovation and mass production in...

After the War and After Putin: Three Potential Succession Scenarios for Russia’s Modern Tsar
The article outlines three possible paths for Vladimir Putin’s succession as the Ukraine war winds down: an intelligence‑driven transition led by senior siloviki, a military‑driven takeover, or an unexpected heir chosen behind the scenes. It highlights the prominence of FSB...

The War’s Next Phase: Five Indicators That Matter Most
General Miller outlines five critical indicators to gauge the next phase of the ongoing conflict: the ability to intercept missiles and cheap Shahed drones, energy flow disruptions and traffic through the Straits of Hormuz, the evolving role of Iraqi and...

The Hormuz Standoff: Global Energy Flow Severs After 'Epic Fury' Strikes
The Strait of Hormuz, a 21‑mile narrow waterway, was shut after a severe incident dubbed “Epic Fury.” The closure halted the transit of roughly 20 million barrels of oil per day, about one‑fifth of global consumption. Heightened tensions between Iran and...

Breaking Down Our "Red October" Moment for AI
The article warns that the Department of War’s rush to embed frontier AI models in national‑security systems mirrors the "Red October" fiasco, where safety mechanisms were disabled and catastrophic failure followed. It argues that without a mission‑aligned, fit‑for‑purpose evaluation framework,...

Purpose-Built or Perilous: Congress Faces a Critical FBI Headquarters Decision
Congress is weighing a pivotal decision on the FBI’s next headquarters as the aging Hoover Building must be replaced. Lawmakers are considering the Ronald Reagan Building, but security experts argue it cannot satisfy Interagency Security Committee Level V standards. The article highlights...

Where Crime and Terror Meet: Australia’s Illicit Tobacco Market
Australian security agencies have linked Iran’s Islamic Revolutionary Guard Corps (IRGC) to two high‑profile firebomb attacks in 2024‑25, exposing a direct crime‑terror nexus. The attacks were facilitated through Australia’s lucrative illicit tobacco market, a $10 billion underground industry driven by the...

Building the Talent Pipeline for America’s Security Future
The opinion piece warns that a shrinking federal workforce is widening talent gaps for U.S. national security. It highlights that government, academia, nonprofits, international bodies, think tanks, and industry all provide viable pathways for young professionals. The author stresses the...

The Cognitive Battlefield Is Now Decisive Terrain
The Pinnacle conference highlighted cognitive warfare as the new decisive terrain, where narrative dominance can outweigh kinetic force. Repeated, low‑level disinformation creates cognitive attrition that erodes public resolve faster than traditional cyber attacks. Decision‑centric, agentic AI and open, modular systems...

Alliances, Ukraine, and China’s Growing Challenge
At the Munich Security Conference, former Defense official Evelyn Farkas warned that the transatlantic alliance’s cohesion is under strain as European partners grow distrustful of U.S. commitments. She urged a clear reaffirmation of American support for NATO and called for...

Inside the High-Stakes U.S. Pressure Campaign on Iran
The Trump administration is deploying a second aircraft carrier, the USS Gerald R. Ford, to join the USS Abraham Lincoln in the Middle East, intensifying pressure on Iran over its nuclear, missile and regional proxy activities. Former intelligence manager Norman...

Confidence, Interoperability, and the Limits of U.S. Decision Systems
The article argues that the United States’ national‑security decision‑making suffers from a systemic confidence illusion: analysts routinely express 80‑90 percent confidence that only materializes at 50‑70 percent accuracy. This mis‑calibration stems not from data scarcity but from institutional architectures that...

A Path to Understanding Autonomy in Defense Technology
The column argues that military autonomy should augment, not replace, commander authority by delegating specific tasks while retaining legal and ethical responsibility. It highlights three pillars—low‑cost, near‑exquisite systems, cross‑vendor interoperability, and a DevOps‑style hardware development model—as essential for trust and...

Standing Up to a Spy: My Run-In with Aldrich Ames
In 1993 a mid‑level CIA analyst refused to approve a Counter‑Narcotics conference in the Caucasus, citing security and logistical risks. The analyst’s objection drew the ire of senior officer Aldrich Ames, who repeatedly confronted him despite the analyst’s credentials. Months later...

Russia’s Foreign Fighter Pipeline: How Moscow Exploits Global Poverty to Feed Ukraine’s Frontlines
Russia is increasingly turning to the Global South to replenish its dwindling ranks in Ukraine, recruiting thousands of migrants with promises of work, money, or citizenship and then sending them to the front lines. Ukrainian intelligence has identified over 18,000...

The Former Head of NSA on the Future of U.S. Cybersecurity
Retired Gen. Paul Nakasone, former NSA director and U.S. Cyber Command commander, discussed his doctrine of persistent engagement, its role in safeguarding recent U.S. elections, and the evolving cyber threat landscape. He highlighted the need for broader public‑private partnerships, a...

Xi Jinping Tightens Grip as China’s Military Purge Deepens
Chinese President Xi Jinping intensified his anti‑corruption and loyalty campaign by dismissing two of the People’s Liberation Army’s top commanders in January 2026. General Zhang Youxia, senior vice‑chairman of the Central Military Commission, and General Liu Zhenli, head of the...
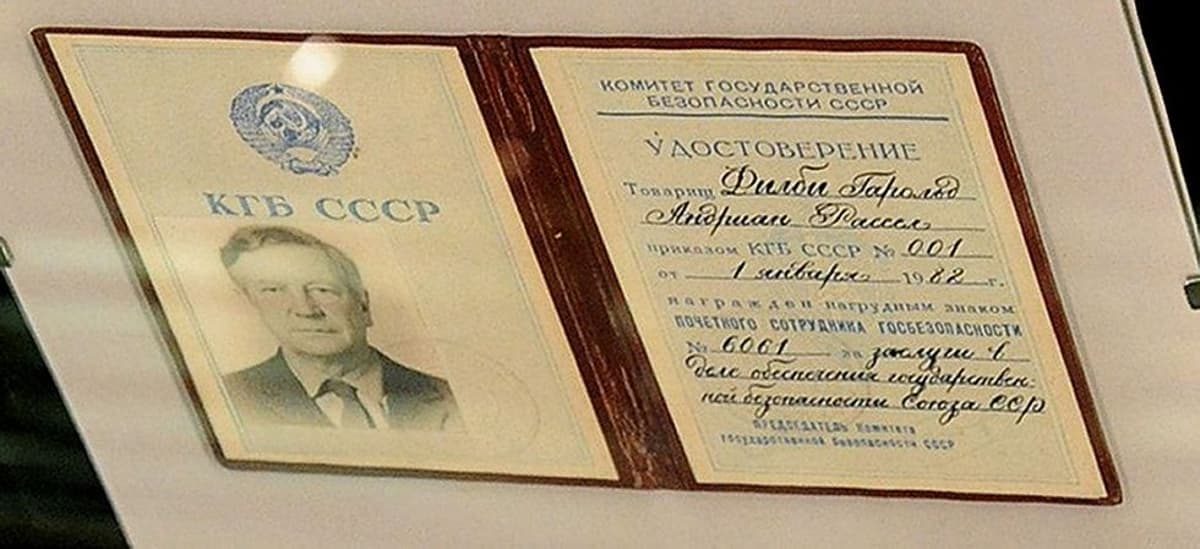
The Kremlin Files: Russian Double Agents and Operational Games
The article explains that Russian intelligence agencies prioritize loyalty to Putin and the regime over national interests, making double‑agent operations—called operational games—their core doctrine. These operations generate fabricated success stories and statistics that feed directly into Kremlin budget justifications. Historical...

Should Western Tech Giants Partner With Pro-Hamas Network Al Jazeera?
Google Cloud has become the primary technology provider for Al Jazeera’s new AI‑driven news engine, “The Core,” which uses generative AI to draft scripts, retrieve archives, and create visualizations. Critics argue the partnership risks amplifying state‑directed, pro‑Hamas content because Al...

Greenland’s Worth a Fight and Russia’s Trying to Start One
Greenland’s position in the GIUK Gap makes it the linchpin for NATO’s ability to detect Russian submarines before they enter the Atlantic, while its Pituffik Space Base hosts critical early‑warning radars for U.S. missile defense. Moscow is exploiting the U.S.‑Europe...

China’s Stunning Military Purge – and What It Means For Taiwan
President Xi Jinping has purged two of the most senior members of the Central Military Commission, General Zhang Youxia and General Liu Zhenli, effectively gutting the PLA's top command. The removals, framed as discipline violations, follow a broader campaign that...

Inside Trump’s New ‘Board of Peace’
President Donald Trump signed the charter for the newly created Board of Peace (BOP) at Davos, positioning himself as its inaugural chairman with sweeping authority over membership, agenda, and dissolution. The charter grants Trump unilateral power to appoint and remove...

They're Coming for Our Kids: How Extremists Target Children Online
Extremist groups are increasingly targeting children on platforms such as Discord, Instagram, Reddit, and gaming chats, turning these digital third spaces into recruitment hubs. In 2024, teenagers accounted for roughly two‑thirds of ISIS‑linked arrests in Europe, and similar patterns are...

The Next FATF Test: Can the West Demand Results From Pakistan?
The Financial Action Task Force will meet in February 2026 to reassess Pakistan after its 2022 removal from the grey list. While Pakistan has introduced anti‑money‑laundering laws and institutional reforms, open‑source evidence shows terrorist groups like Jaish‑e‑Mohammad and Lashkar‑e‑Taiba still...

Loosening the Gordian Knot of Global Terrorism: Why Legitimacy Must Anchor a Counterterrorism Strategy
The 2026 terrorism environment is more hybrid and unpredictable than ever. The author argues that a legitimate U.S. counterterrorism strategy—grounded in legal credibility and international partnership—is essential for the second Trump administration. Past strategies, like the 2018 National Strategy for...

The Kremlin Files: Russia’s Way to the Gray Zone
The article examines Russia’s evolution of gray‑zone or hybrid warfare, focusing on the doctrine of “non‑contact war” and the intelligence‑driven “active measures.” It traces the concept from Soviet‑era sixth‑generation warfare ideas through the writings of generals Slipchenko, Gareev and Gerasimov,...

New Reports Reveal Years of Unaddressed Osprey Safety Risks
New GAO and NAVAIR reviews expose decades‑long safety gaps in the V‑22 Osprey program, highlighting 34 unresolved risks, eight of them catastrophic, and a surge in serious mishaps during 2023‑2024. The reports show that critical component failures—such as hard‑clutch engagement...

The Coast Guard's Mission in the Gray Zone
The opinion piece argues that U.S. defense planning over‑emphasizes expeditionary warfighting while neglecting the Coast Guard’s crucial role in enforcing sovereignty in the gray zone. The Coast Guard uniquely combines law‑enforcement authority, Title 14/10 flexibility, and continuous maritime presence to counter...