
Unpatched TOTOLINK EX200 Flaw Enables Root-Level Telnet Access, CERT/CC Warns
On Jan 6 2026, CERT/CC disclosed CVE‑2025‑65606 affecting the TOTOLINK EX200 range extender. An authenticated attacker can upload a malformed firmware file that forces the device into an error state, automatically launching an unauthenticated root‑level telnet service. The telnet console provides full system control, enabling configuration tampering, arbitrary command execution, and potential lateral movement across the network. TOTOLINK has not issued a patch and the product is officially end‑of‑life, leaving users to rely on network isolation and replacement.
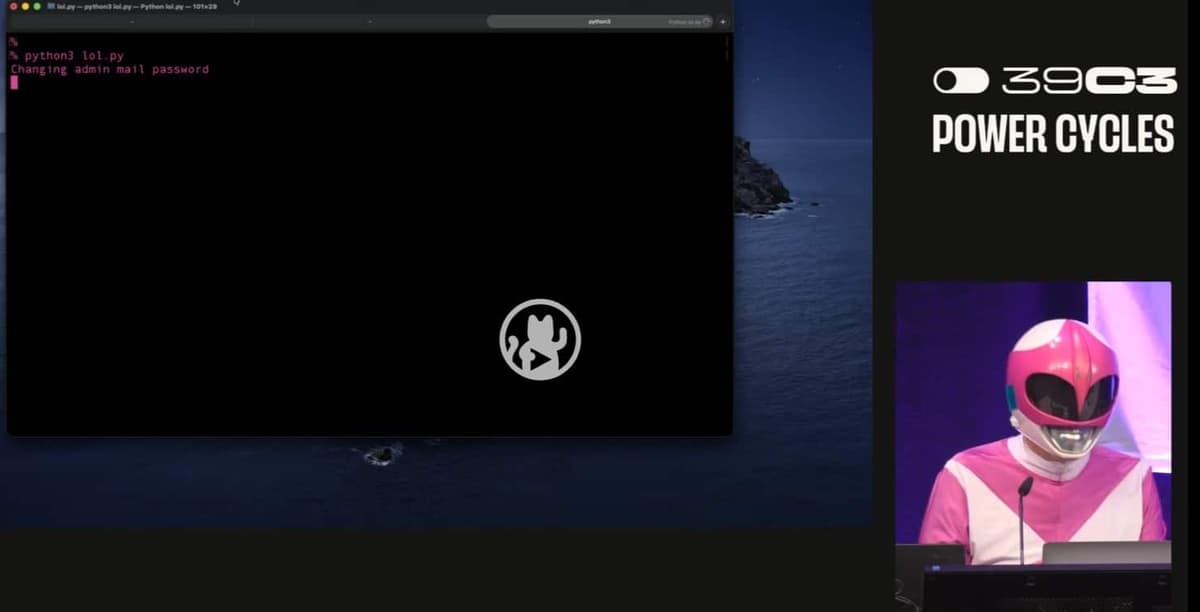
Hacktivist Exposes and Deletes White Supremacist Websites Live at Conference
At the Chaos Communication Congress in Hamburg, hacktivist Martha Root publicly deleted three white‑supremacist sites—WhiteDate, WhiteChild and WhiteDeal—while the audience cheered. The live takedown was accompanied by the release of data on more than 6,000 users from the dating platform,...

What Is a Proxy Server? A Complete Guide to Types, Uses, and Benefits
A proxy server acts as an intermediary between client devices and the Internet, forwarding requests, filtering data, and returning responses. The guide distinguishes forward proxies, which protect users by masking IPs, enforcing policies, caching content, and inspecting traffic, from reverse...
Critical N8n Vulnerability Allows Arbitrary Command Execution (CVE-2025-68668)
A critical vulnerability (CVE‑2025‑68668) in n8n’s Python Code Node lets authenticated users bypass the sandbox and execute arbitrary system commands. The flaw affects all n8n versions from 1.0.0 up to, but not including, 2.0.0 and carries a CVSS score of...