1Password Launches Unified Access as a One-Stop Shop for Managing Company Credentials – Say Goodbye to Shadow IT and SaaS Sprawl
•January 13, 2026
0
Companies Mentioned
Why It Matters
Unified Access bridges the gap between identity tools and unmanaged credentials, lowering breach risk while streamlining access for remote and BYOD workforces. It gives security teams full visibility and auditability across the credential landscape, a critical need for modern, distributed enterprises.
Key Takeaways
- •Unified Access merges password manager and SaaS manager.
- •Enables discovery, revocation of credentials across SSO and non‑SSO.
- •Helps mitigate shadow IT and SaaS sprawl risks.
- •Supports compliance with SOC 2, ISO 27001, HIPAA.
- •Available Jan 13 preview for 100‑plus user enterprises.
Pulse Analysis
The rapid adoption of SaaS applications has outpaced traditional identity management, creating pockets of shadow IT where credentials live outside centralized controls. Organizations struggle to inventory these accounts, leading to redundant spend, increased attack surface, and compliance headaches. By consolidating password management and SaaS discovery into a single pane, Unified Access gives security teams a clear map of every credential, whether federated through SSO or stored locally, helping to curb sprawl before it becomes a liability.
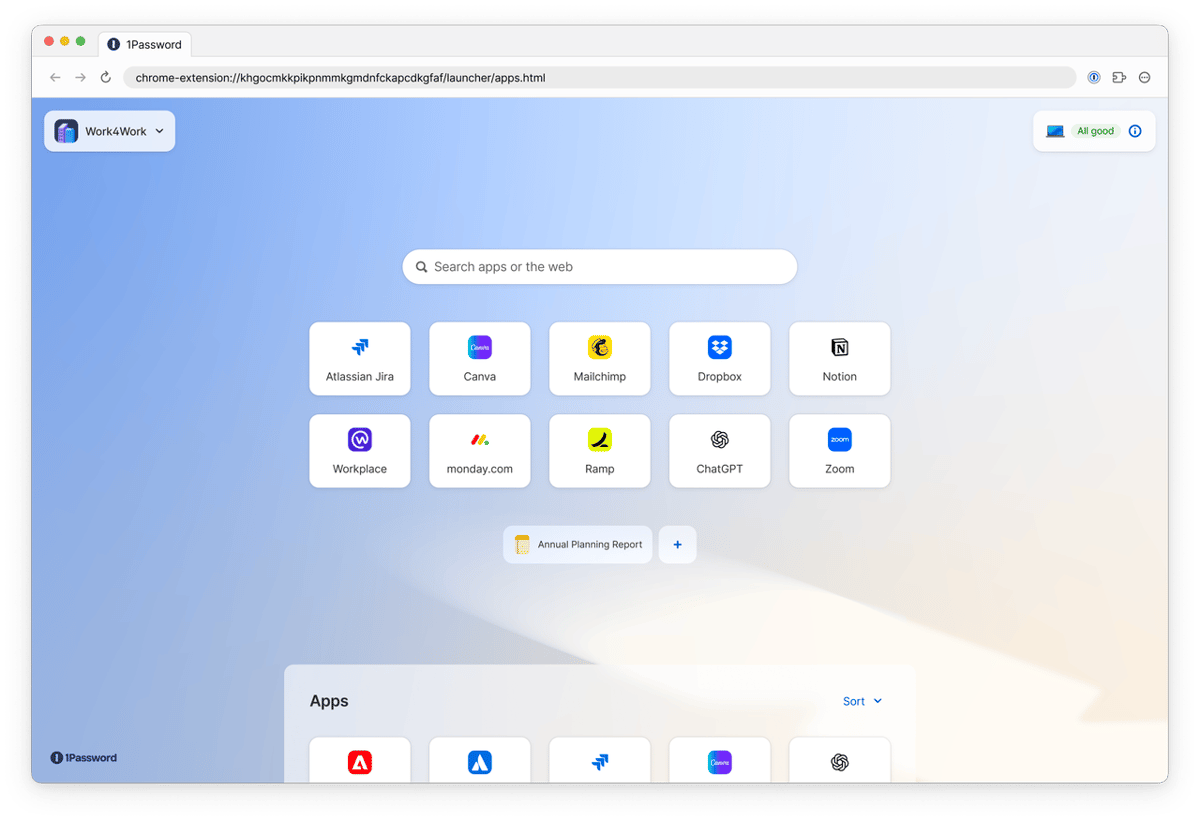
Unified Access operates at the access layer, allowing administrators to scan vaults, provision one‑click app launchers, and instantly revoke rights when roles shift or employees depart. The platform logs each access, rotation, and revocation event, producing audit trails that satisfy SOC 2, ISO 27001, and HIPAA requirements without adding operational overhead. Its app launcher abstracts usernames and passwords, delivering a frictionless experience for end‑users while keeping shared and break‑glass accounts securely vault‑ed. This blend of security and productivity aligns with zero‑trust principles, especially for remote and BYOD environments where device ownership is heterogeneous.
For CISOs, the value proposition is clear: reduced risk exposure, streamlined compliance, and lower total‑cost‑of‑ownership compared to stitching together multiple IAM solutions. As the public preview rolls out to enterprises with 100+ users, the feature signals a shift toward unified credential governance that could become a baseline offering for smaller firms later. Competitors will need to match this integrated approach or risk losing relevance in a market that increasingly demands holistic, device‑agnostic access control.
1Password launches Unified Access as a one-stop shop for managing company credentials – say goodbye to shadow IT and SaaS sprawl
0
Comments
Want to join the conversation?
Loading comments...