12 Million Exposed .env Files Reveal Widespread Security Failures
•February 27, 2026
0
Why It Matters
Exposed secrets let attackers bypass authentication and directly compromise data, highlighting an urgent need for stronger secret governance across development pipelines. The incident demonstrates that misconfigurations, not sophisticated exploits, remain a primary breach vector.
Key Takeaways
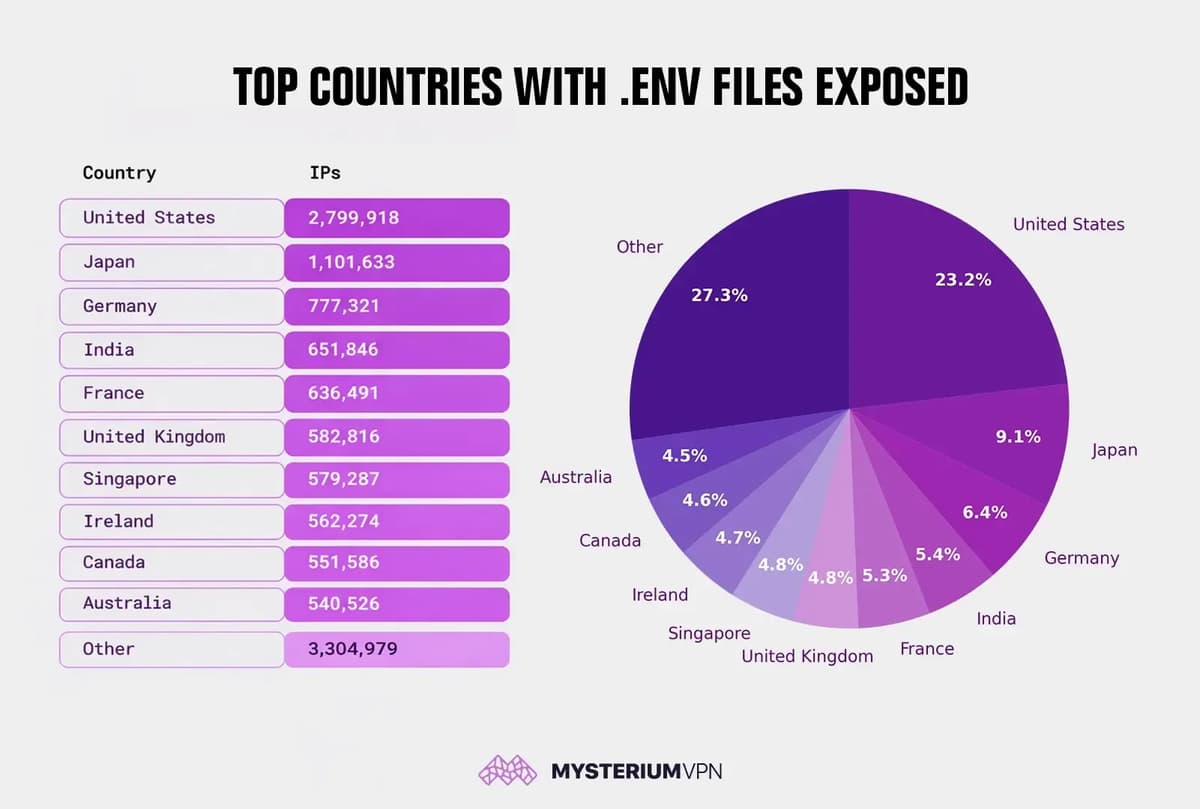
- •12.1M IPs publicly expose .env files worldwide
- •US accounts for 23% of exposed IPs
- •Leaked files contain database passwords, API keys, JWT secrets
- •Misconfigurations stem from missing deny rules and backup files
- •Immediate rotation and secret scanning required after exposure
Pulse Analysis
Environment files (.env) are a staple of modern application deployment, offering a convenient way to inject configuration values such as database URLs, OAuth tokens, and cloud credentials at runtime. Their simplicity, however, becomes a liability when servers inadvertently expose the file through default web roots or misconfigured reverse proxies. Because the files are plain‑text, any attacker who discovers a publicly reachable .env can harvest live secrets without exploiting a vulnerability, effectively turning a configuration mistake into a full‑scale breach vector.
Mysterium VPN’s scan of the public internet revealed 12,088,677 IPs with accessible .env‑style files, a figure that dwarfs previous exposure reports. The United States alone accounts for nearly 2.8 million of those IPs, representing 23 % of the total, while Japan, Germany, India, France and the United Kingdom follow closely. The distribution mirrors the concentration of cloud and hosting footprints, but the uniformity of the mistake—over‑exposed project directories, missing deny rules, and leftover backup files—signals a systemic lapse in operational security rather than a single platform flaw. Attackers can immediately leverage harvested database credentials, API keys, or JWT signing secrets to exfiltrate data, impersonate users, or launch financial fraud.
Mitigating this risk requires a layered approach. Organizations should move secrets out of web‑accessible locations into dedicated secret‑management solutions that enforce audit logging and automated rotation. Server configurations must block hidden files and common backup extensions, while CI/CD pipelines should integrate secret‑scanning tools to catch accidental commits. Finally, adopting short‑lived tokens and least‑privilege access policies reduces the blast radius if a secret does leak. As the Mysterium findings illustrate, treating configuration as a security afterthought invites cheap, high‑impact attacks; proactive secret governance is now a non‑negotiable component of any robust cyber‑defense strategy.
12 Million exposed .env files reveal widespread security failures
0
Comments
Want to join the conversation?
Loading comments...