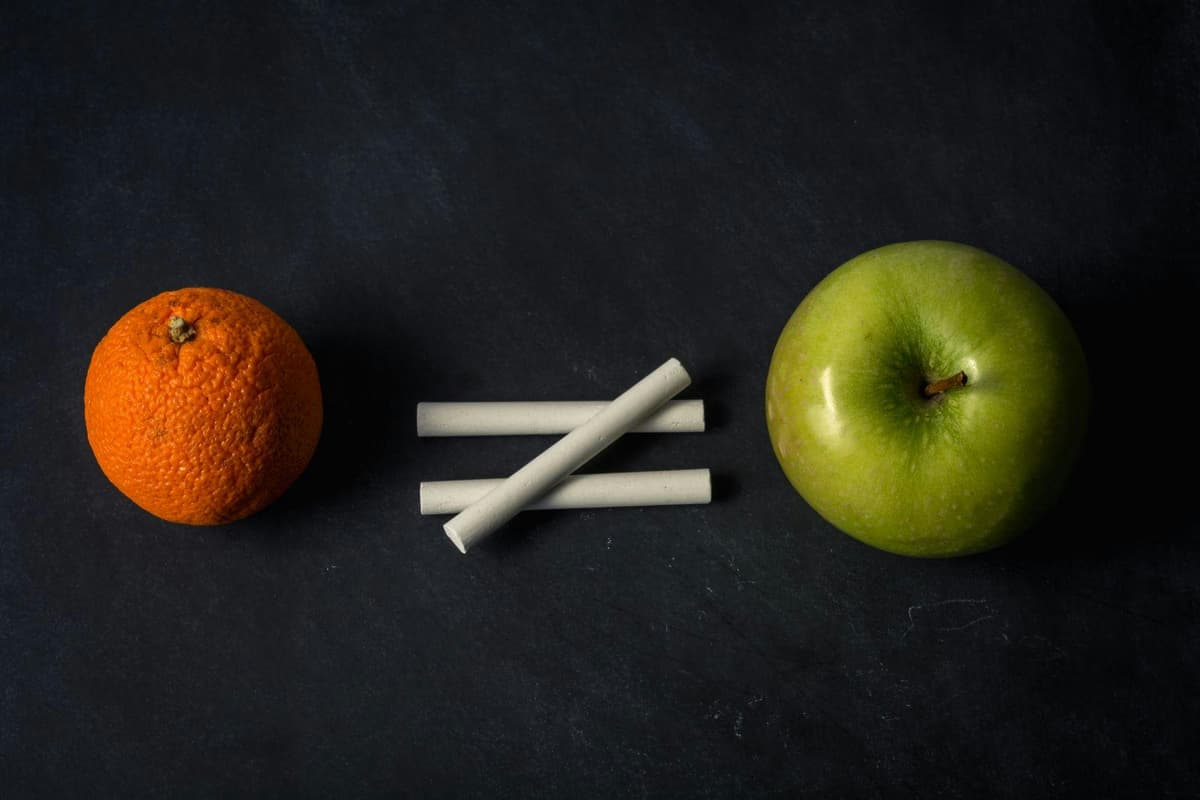
Control System Cyber Incidents and Network Breaches Are “Apples and Oranges”
•February 26, 2026
0
Why It Matters
Without a unified definition, organizations mis‑measure risk, allocate resources inefficiently, and regulators lack accurate visibility into OT‑related threats.
Key Takeaways
- •Network breaches focus on data loss, not physical impact
- •Control‑system incidents affect safety, equipment, environment
- •Verizon report omits OT‑specific cyber events
- •Divergent definitions hinder cross‑industry incident comparison
- •Unified taxonomy and training needed for accurate reporting
Pulse Analysis
The divide between IT network security and industrial control system (ICS) security stems from their core objectives. IT teams prioritize confidentiality and data integrity, tracking ransomware, phishing and other breaches that compromise information assets. In contrast, OT professionals safeguard availability and safety of physical processes, where a cyber event can trigger equipment failure, environmental spills, or even injuries. This divergent focus reshapes what each group classifies as a "cyber incident," leading to inconsistent reporting across the enterprise.
The 2025 Verizon Data Breach Report illustrates the reporting gap. Its tables enumerate incidents and data breaches by industry, yet they omit the millions of control‑system events that affect process continuity, as shown in Weiss's own database. For sectors like utilities, manufacturing and transportation, the omitted OT incidents often involve loss of control, equipment damage or environmental harm—outcomes that traditional breach metrics simply do not capture. Consequently, stakeholders relying on Verizon data may underestimate the true cyber‑risk exposure of critical infrastructure.
Bridging this apples‑to‑oranges comparison requires a common cyber‑incident definition that spans both network and control domains. Industry bodies and regulators should mandate unified taxonomy, while organizations must invest in OT‑specific cyber‑incident training for both IT and engineering staff. Aligning metrics enables more accurate risk assessments, informs better budget allocations, and supports compliance with emerging resilience standards. Ultimately, a shared language empowers companies to protect both data and physical assets against the evolving threat landscape.
Control system cyber incidents and network breaches are “apples and oranges”
0
Comments
Want to join the conversation?
Loading comments...