CVE-2025-64328 Exploitation Impacts 900 Sangoma FreePBX Instances
•March 1, 2026
0
Why It Matters
The breach demonstrates how unpatched VoIP management platforms can become a foothold for large‑scale intrusion, threatening business communications and data integrity. Prompt remediation and monitoring are now essential for any organization using FreePBX.
Key Takeaways
- •About 900 FreePBX servers host EncystPHP web shells
- •CVE‑2025‑64328 scores 8.6, fixed in v17.0.3
- •Threat group INJ3CTOR3 linked to the campaign
- •CISA added the flaw to its KEV catalog
- •400 compromised instances located in the United States
Pulse Analysis
FreePBX, the open‑source management layer for Asterisk VoIP systems, became the target of a large‑scale intrusion after a post‑authentication command‑injection flaw was disclosed as CVE‑2025‑64328. The vulnerability resides in the Endpoint Manager’s filestore module, allowing an authenticated user to execute arbitrary shell commands via the testconnection function. With a CVSS rating of 8.6, the bug affects versions 17.0.2.36 through 17.0.3‑1, and was patched in version 17.0.3. Exploiting this weakness gives attackers asterisk‑level privileges, opening a direct path to the underlying operating system.
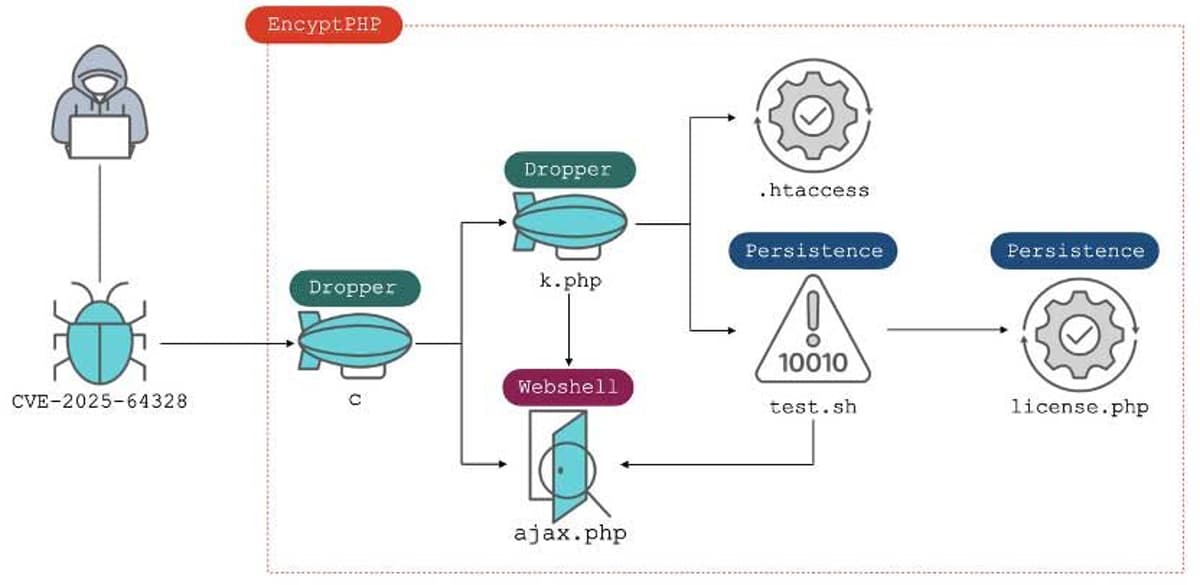
Threat actors identified as the INJ3CTOR3 group weaponized the flaw by delivering a custom PHP web shell dubbed EncystPHP. The dropper, fetched from the malicious domain crm.razatelefonia.pro, installs persistence mechanisms such as a root‑level user, SSH key injection, and port‑22 exposure, while simultaneously erasing logs, removing competing shells, and harvesting database credentials. Shadowserver’s monitoring now shows roughly 900 compromised FreePBX instances across the United States, Brazil, Canada, several European nations, and other regions, illustrating the campaign’s broad geographic reach.
The ongoing infections underscore the critical need for rapid patch deployment and continuous monitoring of VoIP infrastructure. Organizations running FreePBX should upgrade to version 17.0.3 or later, audit for unauthorized web shells, and enforce strong authentication for administrative interfaces. Inclusion of CVE‑2025‑64328 in the U.S. CISA Known Exploited Vulnerabilities catalog signals heightened regulatory attention and may trigger compliance requirements for affected entities. Proactive threat‑intelligence sharing, as demonstrated by Shadowserver and national cyber agencies, remains essential to mitigate similar supply‑chain attacks in the telecom sector.
CVE-2025-64328 exploitation impacts 900 Sangoma FreePBX instances
0
Comments
Want to join the conversation?
Loading comments...