Geekery: Bookending the COROS Security Debacle of 2025
•March 3, 2026
0
Key Takeaways
- •Half a dozen critical Bluetooth flaws discovered
- •Vulnerabilities affected all COROS watch models
- •Fixes required extensive firmware and architecture updates
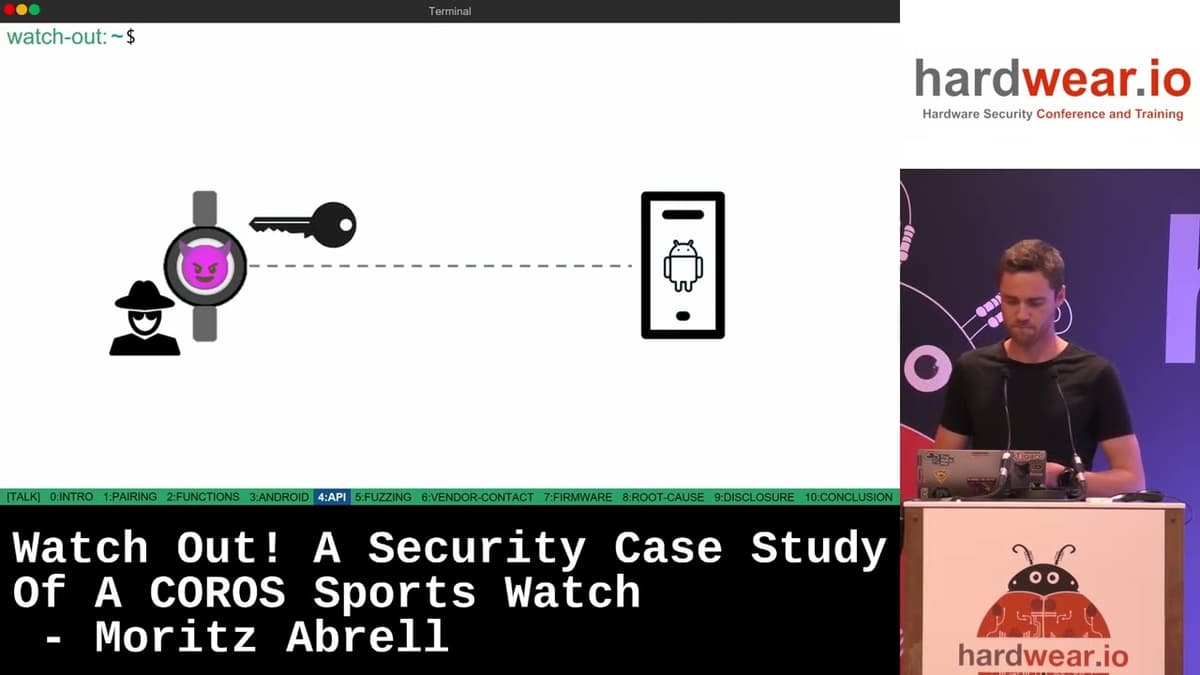
- •Researcher Moritz Abrell presented full remediation timeline
- •Incident highlights IoT security challenges for wearables
Summary
Last summer, COROS disclosed a series of severe Bluetooth security vulnerabilities affecting every model in its smartwatch lineup. Initially downplayed, the company pivoted quickly, implementing extensive firmware patches and architectural overhauls across all devices. Security researcher Moritz Abrell documented the full discovery and remediation process in a conference talk and detailed blog post. COROS now provides a public matrix linking each watch to the specific fixes applied.
Pulse Analysis
The COROS security breach of 2025 sent ripples through the wearable technology sector, revealing how deeply embedded Bluetooth vulnerabilities can compromise user data and device integrity. By exposing flaws that spanned every product tier—from entry‑level fitness trackers to premium multisport watches—COROS highlighted a systemic risk common to many IoT devices. Analysts note that such widespread exposure can erode consumer confidence, prompting heightened scrutiny from regulators and investors alike.
In response, COROS launched an aggressive remediation campaign, rolling out firmware updates that rewired core communication protocols and fortified encryption layers. The company’s public vulnerability matrix offered granular visibility, mapping each watch model to its corresponding patch schedule. This level of transparency, coupled with rapid deployment, helped mitigate potential exploitation and restored a measure of trust among early adopters. Industry observers credit the turnaround to the pressure exerted by independent researcher Moritz Abrell, whose detailed analysis and conference presentation accelerated internal decision‑making.
Beyond COROS, the incident serves as a broader lesson for the IoT ecosystem: proactive security testing and swift patch cycles are no longer optional. Wearable manufacturers must embed security by design, allocate dedicated resources for vulnerability research, and maintain open communication channels with the security community. As the market for connected health devices expands, firms that prioritize these practices will likely gain a competitive edge, while those that lag risk regulatory penalties and brand damage.
Comments
Want to join the conversation?