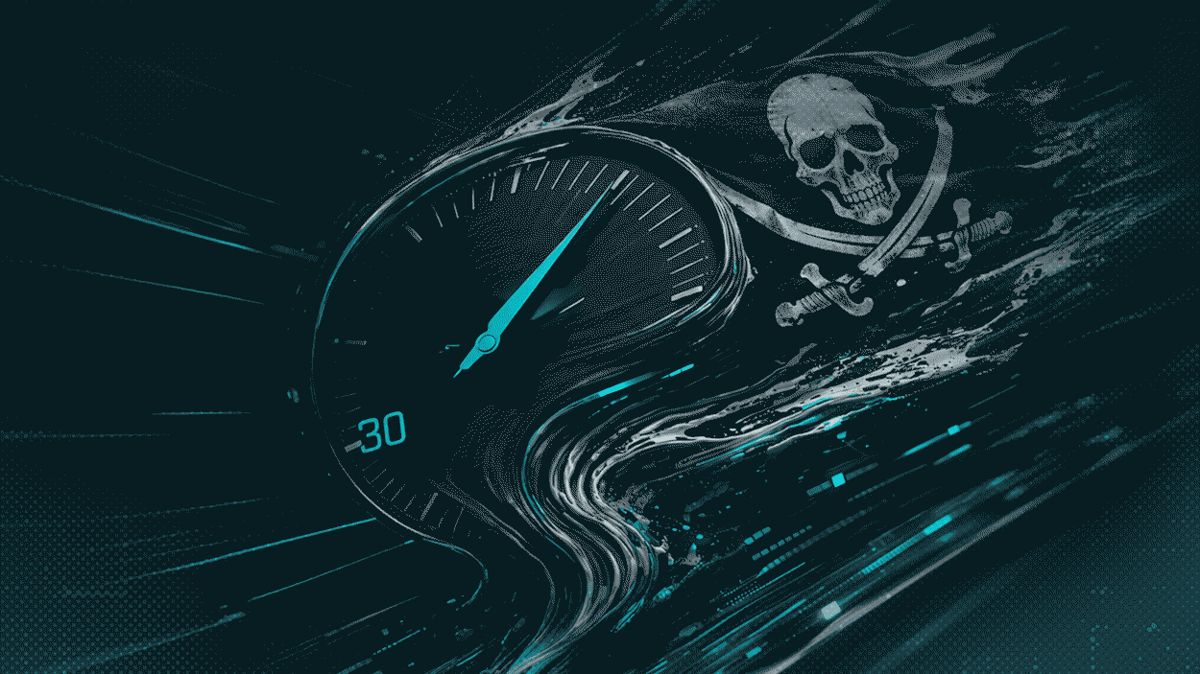
As Breakout Time Accelerates, Prevention-First Cybersecurity Takes Center Stage
Why It Matters
The shrinking breakout window turns brief intrusions into full‑scale breaches, inflating breach costs and regulatory exposure. Organizations that adopt AI‑enabled detection and zero‑trust can limit damage and protect revenue.
Key Takeaways
- •Breakout time now averages 30 minutes, 29% faster than last year
- •80% of RaaS groups offer AI or automation features
- •AI‑driven XDR/MDR can auto‑remediate threats, easing SOC overload
- •Zero‑trust, micro‑segmentation, and MFA reduce lateral movement opportunities
- •Continuous monitoring of edge devices closes gaps between siloed security tools
Pulse Analysis
The cyber‑crime landscape has entered an AI‑augmented era, where threat actors repurpose familiar tactics with machine‑learning speed. Recent industry surveys show that the median lateral‑movement window—often called breakout time—has collapsed to roughly half an hour, a 29% acceleration from the previous year. This compression is driven by AI‑enhanced credential harvesting, automated exploit generation, and sophisticated social‑engineering that can bypass traditional defenses in seconds. As a result, breach costs are soaring, with organizations facing higher remediation expenses and tighter regulatory scrutiny.
For defenders, the traditional “detect‑then‑respond” model is no longer viable. Human analysts cannot keep pace with AI‑generated alerts and the rapid progression of attacks. AI‑powered extended detection and response (XDR) and managed detection and response (MDR) platforms now provide real‑time behavioral analytics, automatically correlating signals across endpoints, networks, and cloud workloads. By clustering alerts and initiating automated containment—such as session termination or host isolation—these solutions free security operations centers to focus on high‑value threat hunting. Unified visibility also bridges the gaps left by siloed point products, ensuring that edge devices and remote‑access tools are monitored alongside core infrastructure.
Adopting a prevention‑first strategy is essential to regain the initiative. Zero‑trust architectures, micro‑segmentation, and phishing‑resistant multi‑factor authentication shrink the attack surface and limit lateral movement. Continuous monitoring of credential usage, AI‑driven script analysis, and dark‑web intelligence further harden defenses. While no single control can stop every breach, layering these measures with AI‑enabled detection creates a resilient security posture capable of countering the accelerating pace of AI‑driven cyber threats.
As breakout time accelerates, prevention-first cybersecurity takes center stage
Comments
Want to join the conversation?
Loading comments...