Can You Afford the Total Cost of Free Java?
•January 13, 2026
0
Companies Mentioned
Why It Matters
The speed of Java exploits combined with steep regulatory penalties makes the total cost of free Java potentially catastrophic for enterprises.
Key Takeaways
- •Exploit window shrank to five days in 2023
- •GDPR fines reach £1M per day for breaches
- •Azul offers rapid security updates beyond Oracle
- •99.2% of new OpenJDK bugs exploitable without privileges
- •Patch cycles average 60‑150 days, leaving exposure
Pulse Analysis
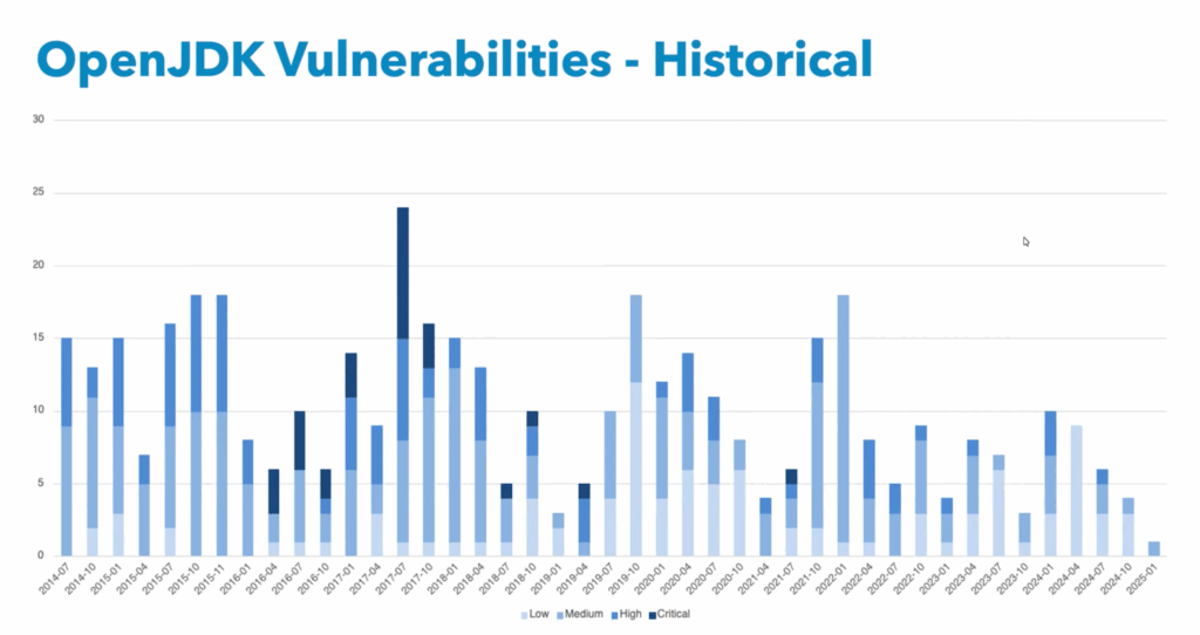
The allure of a zero‑cost Java runtime masks a growing security liability. While Java’s mature ecosystem and built‑in safeguards keep it broadly reliable, recent data shows attackers now exploit disclosed vulnerabilities in as little as five days, with outliers reaching minutes. Enterprises that rely on free distributions must shoulder the entire patching lifecycle, a process that typically stretches two to five months. During this window, 99.2% of new OpenJDK flaws can be weaponized without privileged access, exposing critical applications to rapid compromise.
Beyond the technical risk, regulatory frameworks amplify the financial stakes. In the EMEA region, GDPR mandates breach notification within 72 hours and levies fines up to £1 million per day for non‑compliance. When remediation averages 60 days, a single breach can generate multi‑million‑pound penalties, not to mention reputational damage and customer churn. Companies that underestimate these costs may find the true price of “free” Java far exceeding their budget forecasts.
Mitigation hinges on timely security updates, a capability that most free JVM providers lack. Azul stands out as the only alternative to Oracle offering Critical Set Updates—security‑only patches that can be deployed swiftly without the overhead of full quarterly releases. By investing in a supported Java distribution, organizations align patch cadence with exploit speed, reduce exposure, and safeguard against regulatory fallout, ultimately delivering a lower total cost of ownership than the hidden expenses of unmanaged, free runtimes.
Can You Afford the Total Cost of Free Java?
0
Comments
Want to join the conversation?
Loading comments...