Exposure Assessment Platforms Signal a Shift in Focus
•January 21, 2026
0
Companies Mentioned
Gartner
Why It Matters
EAPs consolidate fragmented alerts into actionable attack‑path insights, dramatically improving risk reduction and operational efficiency for security teams.
Key Takeaways
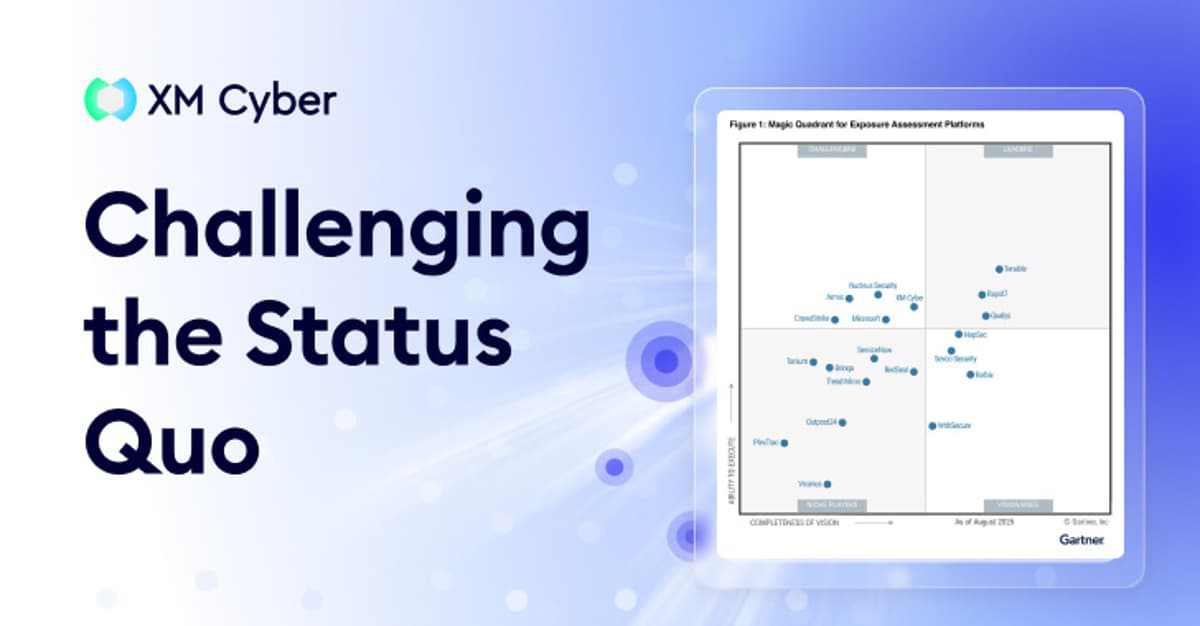
- •Gartner launches Exposure Assessment Platforms category.
- •EAPs replace traditional vulnerability management with CTEM.
- •74% exposures are dead ends, wasting remediation effort.
- •Projected 30% downtime reduction by 2027.
- •Platforms integrate risk‑informed prioritization across environments.
Pulse Analysis
The security industry has long wrestled with the sheer volume of vulnerability data, a problem Gartner now addresses by carving out a dedicated Exposure Assessment Platforms (EAP) category. Traditional vulnerability management treats flaws as isolated tickets, ignoring how they interconnect across cloud, on‑prem, and identity layers. By framing security as Continuous Threat Exposure Management, Gartner acknowledges that risk is a dynamic, path‑based phenomenon rather than a static list of CVEs. This conceptual shift aligns research with how sophisticated attackers chain misconfigurations, privileged accounts, and unpatched software to reach critical assets.
EAPs differentiate themselves through four core capabilities: continuous, cross‑environment discovery; context‑driven prioritization that weighs asset importance, exploitability, and lateral‑movement potential; seamless integration with existing ticketing and orchestration tools; and lifecycle tracking that monitors exposure remediation over time. By mapping real‑world attack paths, these platforms transform raw alerts into a unified risk graph, allowing SOC analysts to focus on the 26 % of exposures that truly threaten business processes. Vendors that built exposure modeling into their DNA, such as XM Cyber, outperform legacy players merely adding exposure features to legacy scanners.
For enterprises, the business payoff is tangible. Gartner’s projection of a 30 % reduction in unplanned downtime by 2027 translates into higher service availability, lower incident response costs, and reclaimed analyst bandwidth. Organizations that adopt EAPs can replace noisy, low‑value alerts with prioritized, actionable remediation plans, directly linking security effort to revenue‑protecting outcomes. As the market matures, the competitive edge will belong to platforms that deliver accurate attack‑path visibility while integrating smoothly into existing security workflows, making exposure assessment a cornerstone of modern cyber‑risk management.
Exposure Assessment Platforms Signal a Shift in Focus
0
Comments
Want to join the conversation?
Loading comments...